►
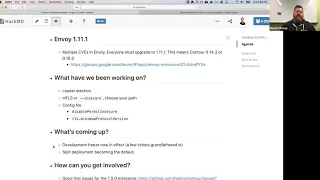
From YouTube: Contour Community Meeting - August 27, 2019
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
A
So
if
you
miss
anything,
you
can
always
watch
it
later
and
if
you
have
any
questions,
please
feel
free
to
just
unmute
yourself
and
speak
up
or
if
your
mic
isn't
working
today
or
if
you're,
in
the
location
that
where
it
doesn't
work,
just
type
out
your
your
questions
in
the
chat
and
I'll
race.
It
I'm
gonna,
share
my
screen
here
and
gonna
share
the
agenda,
so
everyone
can
see
it
get
a
bunch
of
stuff
they
want
to
talk
about
today.
A
So
the
first
thing
is
envoy:
one
11.1
which
dave
is
gonna
cover,
then
we're
gonna,
look
at
what
we've
been
working
on.
What's
coming
up
here
and
I'm
gonna
go
through
a
bunch
of
good
first
issues
for
the
1.00
milestone.
So
if
you
are
looking
to
get
involved,
if
you
are
looking
for
issues,
that
would
be
a
good
first
issue
for
you.
This
is
definitely
the
place
for
that.
So
with
that
Dave
you
wanna
want
to
take
it
all
over
here.
Sure.
B
What
can
everybody
so
before
we
get
into?
What's
happened
in
previous
release
and
what's
coming
up,
there's
an
important
kind
of
PSA,
which
is
we
have
to
talk
about
the
DHCP
vulnerabilities
that
were
just
going
in
envoy
and
to
be
fair,
not
just
on
boy,
looks
like
Netflix
sat
down
on
how
to
look
at
the
HTTP
specification
like
there
are
some
ambiguities
here,
I
wonder
what
would
happen
if
I
sent
a
random
server
on
the
internet,
this
packet,
and
so
this
set
of
HTTP
vulnerabilities,
affect
pretty
much
every
implementation
out.
B
There
goes
on
boys,
I
haven't
checked
in
Jake's,
I'm,
sure
sure
everybody
was
doing
HTTP
to
has
been
scrambling.
What
this
means
for
us
as
envoy
business
is
that's.
The
only
shipping
version
of
envoy
that
contains
these
fixes
is
over
$1
Evan
dot
one
they
have
not
backed
got
them
to
one
or
ten
or
any
earlier
version.
You
must
upgrade
period.
B
Now
we
we
maintain
a
fairly
strong
coincidence
between
humble
releases
and
controversies,
and
so
in
concert
with
the
Envoy
developers.
We
have
one
dot,
11th
or
12th
and
or
end
so
many
Sony
releases
zero
to
14.2
and
zero
to
15.
So,
honestly,
you
should
just
up
create
a
zero
to
fifteen.
Why
stay
on
the
old
bastard
come
to
the
new
stuff,
but
the
key
the
key
here
is
that,
unfortunately,
you
don't
have
a
choice
to
not
upgrade
envoy.
If
not
backported,
this
fix,
you
must
upgrade.
That's
that's
just
the
deal
of
the
game.
B
This
is
open
source.
So
are
there
any
questions
around
around
that
around
what
the
issues
are
about?
How
does
that
impact
contour?
You
can
feel
free
to
ask
in
terms
of
how
this
affects
contour
is
like
its
component.
In
the
good
name
structure,
we
don't
expose
HTTP
to
HTTPS
I'd
world,
the
only
port
we
exposes
for
just
the
health
check
and
you
debug
in
your
stats
in
traditional
stuff.
We
do
inside
pasta
the
listening
port.
The
service
is
connected
to
the
Envoy
which
is
connected
to
the
outside
world.
B
So
this
this
is
an
issue
that
affects
envoy
I've,
put
a
link
in
in
the
show
notes
to
the
Envoy
release
notes.
Just
like
a
lawyer:
I
am
NOT
a
security
security,
white
hat,
so
I
will
not
pretend
to
interpret
these
things
for
you.
You
should
read
the
on
the
CB
s
yourself
into
turn
from
your
own
level,
30
and
exposure,
but
the
straight
up
version
is:
this
is
a
pretty
serious.
It
affected
all
the
HTTP
HTTP
implementations.
You
need
to
upgrade
ok
here.
B
A
A
B
C
B
B
This
is
using
v2
TLS.
We
have
a
job
that
generates
all
the
certificates
for
you
and
we
set
up
contour
and
envoy
to
use
those
certificate.
If
Achatz
of
our
secrets,
it
all
works,
pretty
seamlessly
the
got.
The
goal
of
this
is
the
eighth.
The
end
goal,
which
we'll
come
back
to
in
the
you-know-what
coming
up
is
that
we
want
to
make
what
we
call
the
split
deployment
splitting
contour
into
the
contour
and
envoy
pods
into
their
own
life
cycles.
The
key
to
that
is
being
able
to
secure
that
their
traffic
between
it.
B
B
This
is
this
is
a
breaking
change
that
your
deployment,
if
you
don't
have
this
flag
contour
and
you
just
instead
of
ringing
our
upgrade
document,
it's
gone,
I
mean
an
avenue
to
deployment
and
gone
from
0
14
is
here
are
15,
it's
not
gonna
start
up.
There's
going
to
be
very
clear
message.
It
says
you
need
to
breathe
and
provide
TLS
credentials
or
use
insecure.
B
The
the
reason
for
this
is
that
in
secure
mode
is
kind
of
in
it's
name,
not
the
one
we
want
you
to
use.
You
would
only
use
this
if
you
were
Co
deploying
your
pods,
your
contour,
your
voice,
in
kind
of
like
a
little
kind
cluster,
or
something
like
that
for
the
real
world
you
either
should
you
should
be
using
mutual
TLS
between
your
services
to
secure
and
authenticate
that
connection
and
also
like,
if
you
yeah,
so
that's
that's
page.
We
go
now
in
real
world.
B
So,
with
over
the
last
couple
of
releases,
we've
been
moving
towards
that
third
position.
So
that's
a
that's
the
the
important
change
there.
It's
we
made
it
very,
very
explicit,
like
there's,
no
way
that
you
could
just
kind
of
edit
your
edit,
your
image
version
and
be
like
mean
since
you're
working
and
then
oh
I
was
accidentally
working
in
secure
mode.
I
didn't
realize
that
by
making
this
explicit,
you
have
to
provide
TLS
key
material
or
explicitly
pass
in
the
contour
serve
insecure.
B
You
have
to
choose
at
that
point,
so
there
is
no
way
that
you
can
accidentally
fall
into
an
unexpected,
like
you
choose
at
this
point,
Nick
I'm
gonna
hand
over
to
you
now
to
talk
about
leader
election
that
landed
in
0.15,
how
it
applies
to
this
split
deployment
and
possibly
finish
up
a
little
bit
like
where
it's
gonna
go
in
the
next
release.
Joe.
D
D
So
there's
another
piece
of
work
to
change
this
leader
election
models,
one
more
like
that.
Api
server,
where
you
can
have
each
contour
can
be
basically
a
read
replica
and
one
contour
will
be
like
that
as
the
as
the
boss
and
that
boss
will
be
the
one
that
is,
that
does
the
writing,
and
so
that's
sort
of
forthcoming
I'm
hoping
to
learn
that
in
being
one
but
we'll
see
how
again.
E
Hi
can
I
ask
a
question:
yeah,
absolutely
I,
I
work
at
the
big
institution
that
Josh
Wausau
and
Alexander
Brander
working
at
and
whenever
I
see
leader
election
I
sort
of
you
know
panic
a
little
bit
just
in
terms
of
what
that
means
running
a
leader
election
system,
and
so
is
do
I.
Think
about
this,
like
a
leader
election
system
in
terms
of
a
traditional
zookeeper,
or
is
this
like,
backed
by
a
tee
day
like
what's
actually
doing
the
consensus
out
of
this
or
am
I
thinking
of
this
the
wrong
way.
You're.
B
D
Functionally
what
it
does
is
it
uses
annotations
on
a
on
a
carpet
currently
there's
annotations
and
a
config
map
as
the
sort
of
locking
mechanism,
all
of
them
all
of
the
instances.
Watch
the
company
map,
the
annotation
says
which
one's
the
leader
that
one
becomes
the
leader
and
there's
a
bunch
of
stuff
the
easy
go
to
make
it
apply.
Okay,.
E
B
B
B
B
You
opt
into
a
leader,
enable
leader
election
in
the
future,
we're
going
to
hope
to
make
that
make
that
default,
see
we
either
change
that
default
or
just
check
change
that
suits
a
disabled
leader
election,
or
we
just
turn
it
on
when
it
when
it
seems
reasonable
the
they
got
the
offer
at
the
moment.
We
only
have
by
only
exposing
the
GOP
support
on
the
leader
contour.
That
causes
all
the
envoys
to
follow
that
one
and
they
get
their
configuration.
B
Each
of
them
get
the
same
configuration
we
are,
we
are
probably
going
to
move
as
we
evolved,
evolve.
The
direction
to
the
model,
where
only
the
leader
has
the
authority
to
drive
back
status.
So
it's
a
consistent
status
stream,
but
we
may
choose
to
as
the
API
server
does.
If
actually
have
read-only
followers
I'm,
not
gonna
use
the
S
word,
that's
not
appropriate,
so
that
will
that
will
let
a
rather
than
every
everybody
dogpiling
in
one
contour
their
potential.
Potentially,
you
can
spread
the
load
across
many.
B
B
Good
work
we'll
move
on
then
on
the
next
date.
On
let's
talk
about
is
the
config
file.
We
added
we
added
a
configuration
file
in
0.14.
The
goal
of
that
is
to
capture
configuration
changes
which
aren't
at
the
route
or
virtual
host
level.
Obviously
we
all
know
about
the
rat
level
like
what
service
load
balancer,
bla
bla.
The
virtual
host
is
effectually
that
the
TLS
properties
things
like
that,
but
there
probably
needs
to
be
a
layer
above
that
a
kind
of
administrator
level
of
four.
You
know
in
the
scope
of
four,
this
canto
installation.
B
These
things
apply,
and
so
that
was
why
we
created
the
configuration
file
now
in
in
0:14
it
was
mute,
but
in
zero
15
we've
added
a
few
few
configuration
properties
which
fit
into
this
cluster
I
was
gonna,
say
clucks.
The
word
lets
me:
have
one
conference
tour,
but
so
the
installation
wide
the
properties
for
this
installation
I
haven't
talked
to
about
this
before
state.
But
would
you
would
you
feel
okay,
talking
about
the
Royal
disabled,
mint
and
secure
and
mint
protocol
version?
Okay,
otherwise,
I
can
do
it.
E
C
Awesome
yeah,
so
the
destroyer
announced
that
they
haven't
not
familiar,
there's
a
way
that
if
you
specify
TLS
secrets
on
an
on
an
ingress
route
by
default,
we
kind
of
like
follow
good
standards.
So
the
idea
is:
if
we
see
that
your
you
want
to
present
certificates
on
a
listener,
then
we'll
assume
that
you're
gonna
want
TLS
right.
C
So
a
lot
of
other
ingress
resources
require
you
to
annotate
your
ingress
resource
and
say
hey
when
I
receive
a
request
over
a
plain
HTTP,
then
force
or
301
redirect
back
to
this,
your
employee
so
ingress,
what
kind
of
takes
it
as
if,
when
we
see
that
secure
that
secret
on
that
ingress
route,
we're
gonna
assume
you
want.
You
know
a
TLS
end
point.
So
we'll
automatically
do
that,
so
you
don't
have
to
annotate
or
set
that
configuration.
C
So
when
a
request
comes
again
on
insecure,
will
this
automatically
redirect,
but
there
are
times
where
you
might
want
to
actually
serve
both
endpoints
serve
the
plain
HTTP,
as
well
as
the
secure
listener.
So
in
the
ingress
route,
there's
a
way
you
can
specify
hey
I
have
these
routes,
but
for
this
specific
path,
let
me
let
this
sole
serve
an
insecure
path.
C
So
if
an
administrator
wanted
to
require
that
301
redirect
everywhere,
usually
still
had
the
ability
to
set
that
on
their
route,
so
basically
they
could
override
kind
of
what
an
administrator
with
one.
So
now,
if
you
set
this
disabled
permit
insecure
in
the
config
file
users,
if
they
try
and
set
that
on
their
ingress
routes,
I,
don't
look
it'll,
get
disabled
or
ignored
in
thrown
away.
So
that's
that
disable
permit
insecure.
The
same
thing
kind
of
follows
for
the
the
TLS
min
protocol.
C
B
B
We
kind
of
put
that
off
for
the
moment
by
saying.
Well,
let's
just
do
it
gives
people
the
A+,
but
we
figure
that
there'll
be
another
place,
that
we
need
to
put
other
tailor
stuff,
and
so
that's
why
it's
in
its
its
own
key,
but
in
protocol
version
basically
lets
you
raise
the
minimum
from
1.1,
which
is
that
which
is
the
default
up
and
also
prevents
users
from
raising
below
that
from
from
lowering
it
below
that.
E
Have
any
feedback
on
this?
No,
this
is
great
I
mean
we
want
to
be
able
to
set
both
of
these
at
the
cost
a
little.
So
in
order
for
us
to
host
any
sort
of
any
sort
of
application,
the
subject
regulatory
stuff-
we
have
an
internal
name
called
critical
application
framework
or
any
sort
of
you
know
future
PCI
Sox
compliant
any
of
that
sort
of
stuff.
We
need
to
specify
and
enforce
a
non
tangible
minimum,
TLS
version
so
which
is
one
point
two,
so
this.
E
E
B
It's
the
standard,
concrete
map
gears
mounted
as
a
volume,
and
it
matters
the
file
in
the
volume
and
it's
made
available.
You
know
such
comfy
comfy
mo
that
that
classic
part
of
the
reason
why
we
added
a
configuration
file
that
so,
but
behind
the
scenes,
some
configuration
that
there
is
a
there's,
a
hierarchy,
configuration
file
to
environment
variables
to
flag
specified
directly.
That's
the
that's
always
the
hierarchy.
B
We
could
have
added
minimum
protocol
version
or
disable
commit
insecure
as
flags
as
flags
on
the
deployment
part
of
the
part
of
the
problem.
There
is
that
we
would
have
that
meant
that
every
all
the
deployment
would
change.
At
the
same
time
like,
like
you,
change
an
inspector,
the
deployment
potentially
using
a
comfy
file
that
you
stage
stage
that,
as
in
you,
want
to
change
change,
the
config
map
bump
one
of
the
pods,
he
will
get
rebuilt,
hopefully
the
same
spec,
but
the
most
important.
The
there
obably
different
ways
ways
are
doing.
B
We
did
expect
that
almost
all
all
big
shops
would
have
some
kind
of
ansible,
the
helmet
templating,
which
is
their
way
of
building
they're
part
of
their
deployment
parts.
So
yes,
young
lady,
complete
map
was
not
the
not
go
the
the
worst
thing,
but
the
the
real
clincher
was.
There
are
some
things
that
we
can't
really
express
well
in
CLI
flags,
one
of
the
one
of
the
when
we
get
to
what's
going
up
next
one
of
the
grandfather
noon
tickets
is
the
ability
to
do
Jason,
walking
and
expressing
the
Jason
logging
format.
B
String
is
like
a
bunch
of
see.
A
lot
of
flags
would
just
be
just
just
be
just
a
disaster
she'll,
quoting
so
right.
That
was
the
main
reason
why
we
created
a
common
pigfarts.
We
put
put
that
in,
but
it's
it's
always
a
question
of
to
put
in
a
config
file.
Should
we
have
a
flag?
Should
we
do
it,
as
both
some
have
some
have
both
like,
for
example,
you
can
specify
that
the
location
of
your
coop
config
at
both
the
config
level
and
the
flag
level
yeah.
E
You
know
oh
I'll
check
it.
Our
team
in
India
is
doing
most
of
this
work
and
we
I
know
we're
trying
to
get
to
0.15,
so
I'll
check
with
him,
but
I
I
think
is
it
currently
is
I.
Think
it's
like
a
bit.
If
there's
any
reason
for
us
to
have
concern
there,
I'll
make
sure
I'll
get
back
to
you
back
to
you.
Do.
B
The
way
we
built
it
is
very,
very
cheap
to
move
to
move
or
kind
of
allow
things
to
be
set
in
multiple
locations
and
there's
a
world
of
Latin
priests.
It's
like
it
doesn't
change
on
a
per
flight
level.
Toys,
config
file
environment,
variable
flag
on
this
flag
on
the
command
line.
That
always
is
the
Waker,
so
it's
written
is
very
cheap
for
us
to
change
and
almost
said
the
other
said
so
trivial,
but
I've
gotta
say
that
costing
more
than
we
yell
at
me,
but
it
is.
B
We
built
this
in
such
a
way
that
you
use
not
a
major
major
engine
undertaking
to
make
these
little
moves.
Like
all
that,
it's
oh,
we
need
a
flag
to
override
the
config
file.
Easy
just
raise
ticket
okay,
we're
kind
of
halfway
through
there,
so
maybe
I'm
a
Hannah,
bicurious
and
I
guess
we'll
talk
about
what's
coming
up
in
the
future
of
contour
yeah.
A
B
The
use
case
that
we
have
in
mind
so
turns
out
I
need
to
step
back
a
little
bit
and
say
the
goal
is
to
move
to
split
deployment
and
just
to
define
what
split
deployment
mean
means
for
our
seers
contours
live
in
a
deployment
your
classic
deployment
envoy
is
live
in
a
diamond
set.
There
is
no
value
in
having
more
than
one
envoy
running
per
host.
That's
not
the
way
you
scale
them
out,
and
that
also
opens
the
door
very
easily
to
host
networking.
B
B
You
probably
don't
want
to
bounce
it
every
time
you
change
your
contour
company
to
pick
up
a
new
configuration
change,
so
the
goal
that
we're
working
at
over
the
last
couple
of
releases
separate
them
into
different
pods
that
it's
different
in
two
different
sets
of
pods,
so
they
have
different
lifetimes
now
that
interviewed.
That
means.
Well,
how
are
you
going
to
communicate
it
across
and
if
they're
not
sharing
the
same
localhost
networking
you
need
to
secure
that
traffic.
B
So
it
answer
the
question
of
where
does
insecure
fit
in
it
would
only
be
in
the
cases
where
you
had
chosen
to
deploy
them.
Co-Located
you're
like
well
they're,
just
talking
of
a
loopback.
They
don't
need
me.
They
don't
need
to
encrypt
their
communication.
No
one
else
can
talk
over
localhost
we're
fine.
With
that
we
will.
B
We
were
in
the
process
of
updating
the
deployment
manifests
and
we're
basically
going
to
get
to
a
set
a
stage
where,
instead
of
the
four
and
think
it
was
five
last
last
time
we've
been
so
then
whittling
them
down
there
just
to
split
deployment
and
development
or
localhost,
or
something
like
that.
So
if
you-
and
that
would
not
include
any
replicas,
it's
just
one
contour
one
envoy
in
a
pod-
they
go
so
there
that's
suitable
for
of
if
you're,
if
you're
in
small
cluster
you're
doing
a
kind
deployment.
B
A
B
So
the
last
thing
you
want
is
for
us
to
have
a
replica
set
of
three
three
contours
and
two
envoys
which
are
all
going
to
be
stuff
from
Thor
under
the
one
machine
that
that's
ago,
we
realized
that
the
split
deployment
model
can't
scale
all
the
way
down
like
like
this.
We
want
to
have
a
reasonable
number
of
replicas
and
a
reasonable
number
of
both
the
hope,
the
daemon
set
and
the
deployment.
So
we
realized
that
there's
a
limit.
B
E
Actually,
I
have
one
more
question,
so
just
it's
related
to
the
to
the
shutdown
stuff
and
demon
suits
versus
deployments.
So
you
might
be
aware,
we've
we've
got
a,
we
think,
there's
a
larger
networking
issue
that
has
to
do
with
us
repaving
some
of
our
clusters
and
we
get
into
an
RPR
issue
and
I
think
we're
going
to
switch
to
a
deployment
deployment
versus
demon
set.
I
know,
there's
been
some
work
on
in
terms
of
the
shutdown
and
seek
term.
B
Okay,
so
preference
that
super
quickly,
we
we
are
going
to
give
examples
with
a
diamond
set,
sophisticated
users.
We
say
they're
just
exams
like
they're,
just
starting
points
that
you
can,
because
we
can't
possibly
document
all
the
different
all
the
different
ways
to
add
cloud
providers,
as
well
as
the
infinite
set
of
they're
middle
of
the
postures.
So
the
point
versus
team
set
for
your
homeboys
is
very
much
a
matter
of
personal
choice:
okay,
they
they
they
both
well
in
terms
of
shut
down.
B
One
one
thing
that
we
did
fix
in
in
the
manifest
for
0
to
50:
the
way
that
when
in
the
pre
shutdown
hook
that
kubernetes
uses,
we
change,
we
say
to
envoy
change
your
health
state.
There's
a
curl
you
can
make
to
the
admin
interface.
It
says,
make
make
your
health
checks
file
so
that,
in
the
hope
that
that
will
be
out
of
for
the
upstream
load
balancer.
B
If
you
have
work
in
terms
of
cleanly
shutting
down
envoy.
This
is
something
that
then
we're
developers
don't
seem
it.
Maybe
I
should
pass
this
to
make,
but
it's
something
that
the
on
board
developers
don't
seem
to
be
really
on
board
with
they're,
usually
like
or
stop
giving
a
traffic.
Don't
ask
it
to
reject
traffic.
Maybe
I
mean
it
could
speak
more
about
this
cuz
I'm
thinking
it
this
recently
yeah.
D
The
other
thing
that
happens
is
that
when
you
tell
it
to
start
draining
envoy
will
set
its
health
end
point
will
start
returning
unhealthy.
So
that
means
that,
as
far
as
kubernetes
is
concerned,
it
will
be
removed
from
load,
balancers
and
stuff,
like
that,
any
load,
balancer
health
check,
so
that
health
check
in
convoy
will
notice
that
that
Envoy
is
now
unhealthy
and
will
stop
sending
traffic
to
it.
So
the
idea
is
that
you
you're
kind
of
draining
by
using
the
up
the
next
level
upstream
load
balancer
in
the
kubernetes
case.
D
That's
the
service
object
in
the
in
the
case
that
you're
using
like
some
other
sort
of
networking
and
you
go
directly
to
the
on
words.
That'll,
be
your
next
hop
upstream
load
balancer
and
the
the
thing
that
we
added
with
the
C
term
is
related,
but
slightly
different.
That's
actually
for
contour,
not
for
on
word,
and
that's
a
basically,
if,
oh,
that
does
for
contour.
D
That
means
that
when
you
send
a
C
term,
it
will
cleanly
shut
down
all
of
the
different
threads
that
go
to
sorry,
that
that
contour
is
running
not
not
just
wet,
not
just
so
that
had
to
be
how
killed
and
did
the
idea
that
that
alone,
us
also
let
us
simulate
sort
of
this
thesis
failed.
You
know
in
a
weird
way
kind
of
things
make
sense.
B
B
This
means
that
this
means
we
have
to
focus
on
a
set
of
features.
We're
really
hoping
to
get
the
development
milestone,
that
zero
to
fifteen,
be
our
last
develop
milestone
a
few
things
that
have
slipped
over
and
grandfathered
into
beta
one,
but
the
the
key
takeaway
is
that
from
now
until
the
first
beta,
which
is
September
20th,
we
might
do
one
or
two
release
candidates.
We
are
looking
to
stabilize
that
set
of
features.
B
Maybe
she
was
caught
after
101,
but
but
after
100,
but
we
have
to
draw
a
line
in
the
sound
of
things
that
we
can
get
done
for
wonder
Oh
rather
than
continuing
to
like
let
let
leave
leave,
leave
the
boat
at
the
dock,
so
that'sthat's
much
simpler,
very
much
in
in
in
polishing
and
working
in
working
on
polishing.
The
current
features
that
we
have
for
for
our
wonderful
release.
B
What
how?
How
will
this,
what
what
am
I
trying
to
say,
rather
than
playing
feature
bingo,
we
really
want
to
look
at
how
a
particular
enhancement
allow
people
to
use
contour
in
a
way
they
probably
can't
I'm
some
good
examples
that
are
having
a
better
story,
around
authentication,
potentially
having
better
story
around
ipv6
non,
really
owns
ipv6
at
the
moment.
Don't
don't
get--don't
over
index
too
much
on
that?
Maybe
the
ipv6
story
isn't
super
important
I.
B
Think
that's
really
kind
of
regional
thing,
depending
where
you
are
in
the
world
ipv6
seems
to
be
be
kind
of
culturally
specific,
but
that
those
the
kind
of
things
are
looking
at
rather
than
rather
than
attacking
various
tackling
things
like.
Oh
I,
can't
put
an
ipv6
address
in
here,
we'll
look
more
holistically
and
say,
and
so
should
we
put
some
resources
on
making
that
pv6
story
better.
Should
we
put
some
resources
on
having
more
comprehensive
answer
to
how
Dawei
orth
indicate?
B
Way,
we're
looking,
but
that's
that's
after
November,
but
the
big,
the
the
big
push
for
next
to
the
next
two
months
or
so
is
on
finishing
the
finishing
the
better
one
backlog
and
going
through
polishing
up
what
we
we'd
be
happy
to
call
on
one
to
over
lease,
but
before
I
get
into
the
the
next
book
point.
The
one
thing
that
we
are
eating
in
that
very
I'm
pushing
is
that
we
we're
gonna
set
the
splits
upon
it
becomes
the
default
for
anyone
who's
running
contour.
B
B
We
call
the
default,
because
it's
the
one
that
you
just
copy
and
paste
what's
going
to
happen,
is
that
we're
going
to
push
people
to
if
you're,
installing
contour
are
you're
going
to
be
installing
in
this
split
one
node,
because
that
is
the
most.
That
is
the
most
reasonable
one
that
we
think
that
contour
should
be
deploying
in
the
old
model
of
just
everything.
Everything
in
two
containers
in
one
pod
was
very
simple
to
get
going
two
years
ago
when
this
project
started,
but
realistically,
if
you're
using
this
thing
in
anger,
you
want
to
have.
B
So
that's
the
that's
the
the
big
plan
that
we're
going
to
it
by
some
specific
stuff
we're
going
to
continue
to
work
on
to
make
that
split
deployment
story,
the
one
that
we
go
out
with
in
one
day,
because
we
think
that
this
is
the
this
is
I
had
to
pull
myself
back
from
saying
the
right
way.
But
this
is
certainly
a
strong
recommendation
for,
if
you
just
want
to
play
con
contour
get
started
with
it.
B
This
is
this
is
a
way
that's
going
to
work
for
you
very
well,
so
those
are
the
those
need
kind
of
what's
what's
what's
coming
up,
what's
coming,
ups
I
want
to
pass
over
for
the
people
watching
at
home.
How,
potentially,
can
you
get
involved
here?
We,
we
have
a
bunch
of
a
bunch
of
issues
that
we
we
tak
quote.
We
would
call
them
Help,
Wanted
or
good
first
issue,
Help
Wanted.
A
good
first
issue
are
not
mostly
synonyms
but
help
wonder
it
is
if
someone
has
particular
set
of
skills
in
that
area.
B
Good
first
issue
is,
as
it
says,
a
good
first
issue.
There
usually
good
first
issues
usually
are
more
well
specified.
For
example,
we
have
one
says
when
go
one:
a
Thirteen's
released
upgrades
to
go
under
thirteen.
That's
just
a
bit
of
copying
copying,
replacing
making
sure
that
the
doctor
binaries
are
in
the
right
place
and
I
kind
of
just
since
I'm,
assuming
mechanical
translation,
the
help-wanted
ones
are
that
are
not
labeled.
Good
first
issue
potentially
have
a
little
bit
more
analysis.
That
needs
to
be
done
like
need
to
still
need
to
talk
about.
B
Well,
exactly
how
do
we
we
want
to
have
this
at
this
feature
or
fix
this
particular
limitation,
but
it's
not
entirely
clear
how
to
do
it,
but
for
both
these
issues?
These
are
ways
if
you're
looking
to
get
involved
in
a
project
you're
looking
to
contribute.
This
is
the
best.
This
is
one
of
the
best
ways
to
start
so,
there's
a
link,
there's
a
link
in
the
show
notes
that
will
take
you.
Take
you
straight
to
it
yeah
this
is
for
bid.
This
is
for
beta
1.
B
I
can
probably
update
that
to
be
across
all
the
almost
milestones
that
we
have
about,
but
just
just
on
that
I'm
contribution,
I
say
with
my
open
source
out
fully
on
he's
not
just
about
code.
He
is
about
bug.
Reports
is
about
experience,
report
is
about
typos
and
the
documentation
zit
is
about
beating
us
up
in
slack
when
things
that
we
say
are
not
clear.
Contribution
is
a
much
broader
scope
than
just
I
sent
some
code.
B
Don't
do
that?
The
don't
think
that,
just
because
you're
not
experienced
go
developer
or
you
don't
have
experience
in
this
project
that
there's
nothing
that
you
can't
contribute,
that
is
completely
false.
Use
use
of
this
product
like
telling
us
how
it
worked
for
you
or
fail
to
work
for
you
in
anger,
is
as
valuable
as
what
more
valuable
dense
than
code
like
we
can
type
code
all
day,
but
you,
you
need
to
give
us
your
feedback
about
how
the
product
is
not
working
for
you,
and
that
is.
B
That
is
definitely
contribution
that
we
want
to
hear.
You
can
come
find
us
in
slack.
You
can
raise
issues
you
can
come
up.
You
can
I
almost
simply
had
a
man
in
this.
We
don't
because
I
got
rid
of
it,
but
you
can.
If
you
can't,
you
can
speak
up
in
this
in
this
chat
and
let
us
know,
and
with
15
15
minutes
and
change.
This
is
probably
the
it's
probably
the
time
to
do
that.
To
open
the
floor,
for
feedback
for
discussion,
questions
yeah.
A
I
just
want
to
just
want
to
reiterate
what
Dave
said
here.
It's
really
important
that
we
understand
all
your
use
cases
as
well,
so
we
do
have
an
issue.
It's
issued
1269,
if
you
want
to
add
in
your
use
case
there
or
if
you
would
rather
just
chat
with
us
about
your
use
case.
It's
super
important
for
us
on
the
team
in
the
the
community
to
understand
how
contour
is
being
used.
So
please
add
your
voice
here.
It
means
a
lot
to
us.
E
Hey
yeah,
so
I
feel
like
I'm
monopolizing,
the
coal,
but
I'll
raise
one
other
one,
because
I've
been
encouraged
to
do
so
by
josh,
josh
raza.
So
so
one
of
the
one
of
the
things
we've
got
plans,
obviously
beyond
contour
or
envoi,
and
and
we're
a
relevant
shop
which
I
guess
is
fairly
common
in
an
enterprise
land.
So
it's
always
been
a
battle
to
try
and
compile
and
boy
and
roll
seven.
E
But
we're
successfully
doing
that
now
and
so
one
of
the
things
that
Matt
Klein
raised
a
while
ago,
Matt
being
the
creator
of
them
boy
is-
and
there
is
an
open
issue
on
this-
is
the
kitchen
sink
nature
of
the
employee
images.
So
today,
I'm
always
built
with
every
extension
compiled
and
so
and
I've
got
a
color
coded
list
here
that
I
think
I
sort
of
dazzled,
Josh
and
Alex
weeds.
E
But
if
you
look
at
what
the
list
of
extensions
that
we
think
that
contour
uses
it's
a
very
small
number
that
we
know
for
sure
we're
currently
used
today,
there
are
some
that
we
believe
are
coming
down
the
pipe.
So
that
includes
things
like
cause
external
orphan.
These
are
the
things
which
are
features
that
are
captured
in
the
issues
list,
but
then
there's
a
whole
bunch
of
crap.
That
is
not
needed.
Hot
restart,
a
lot
of
the
GRP
see
breach
stuff
back
and
forward
thrift.
E
Zookeeper
extensions,
hystrix,
stats,
stats,
D
data
dog
go
on
and
on
wide
separate,
so
there's
a
whole
bunch
of
stuff
compiled
in
so
our
question
to
them
was:
would
you
support
us
running
our
own
mm
boy,
compiling
boy
with
all
that
stuff
can
compile
out,
but
tag
to
a
1
dot?
11.1
I
think
the
answer
was
no
and
it's
it's
not
a
deal
breaker,
but
I
just
want
to
put
that
out
there
at
some
point,
we'll
probably
want
to
get
to
bring
our
own
invoice.
E
B
Version
I
I
hear
you,
oh
the
the
feature
set
that
continents
from
envoy
is
very
small
and
honestly,
it's
not
changing
at
this
point.
The
the
changes
are
like.
Was
it
like
a
double-double,
which
is
some
Chinese
RPC
yeah
I
mean
that
those
those
things
are
great
but
they're
not
particularly
relevant
to
us
in
terms
of
like,
like
the
official
will
you
we
support
their
that's
where
the
discussion
we
should
have
off
off
this
call,
but
the.
B
B
Okay,
two
things
that
was
it
one.
One
part
of
the
reason
one
thing
at
intervals,
but
deployment
is
that
it
gives
us
the
ability
to
run
those
two
containers
in
different
service
accounts,
so
contouring
the
ability
to
watch
secrets,
ba-ba-ba-ba
envoy,
doesn't
make
any
of
that.
So
part
of
the
reason
for
splitting
that
out
and
one
of
the
things
that
Joe
has
been
pushing
me
for
a
long
time
is:
can
we
make
all
the
way
around
with
no
service
account?
Can
we
give
it
no
permissions
to
talk
to
the
API
at
all?
B
This
is
kind
of
like
like
a
double
Underpants
thing
of
somewhere.
Has
this
big
surface
area
to
all
these
extensions?
Can
we
can
we
mitigate
what
happens
if
if
it
gets,
if
it
gets
exploded,
the
other
one
about
the
coming
back
to
your
your
own,
your
own
envoy,
one
thing
that
compiling
on
boy
is
a
big
job,
I've
no
masterhood
successfully,
and
we
I
think
we
get
a
lot
of
loss
in
this
team
from
not
taking
the
ownership.
I
was
building
and
shipping
our
own
an
envoy.
Oh,
maybe
that's
not.
B
Mean
I
know
just
to
cut
you
off,
but
the
the
setting
to
be
compiled.
You
know
out
of
envoy,
like
it
either
works
or
doesn't
like
I'm
always
gonna
say
that
when
you
remove
an
extension,
you
literally
cut
off
an
arm
of
the
GOP,
see
that
the
message
it
translates
into
just
like
this
extension
isn't
enabled
Owen.
B
B
The
reason
why
one
reason
why
we
need
them
to
be
in
such
close
thing
is
that
like
they
will
check,
though
Britain
like
freaks
out
between
envoy
1.8
and
1.9,
they
totally
checked
like
there
was
no
backwards
compatibility
between
the
chair
PC.
So
you
we're
forcing
this
mode
of
this
particular
contour
words
with
that
particular
version
or
envoy.
This
later
version
one.
We
require
sisterly
devotion
of
contour.
B
B
E
Guess
what
what
would
be
interesting
and
I'm
happy
to
do
this
for
any
sort
of
essentially
I?
Think
it's
a
good
idea
or
any
sort
of
forum
Josh
others
are
suggesting
gear
up
and
may
even
just
be
a
docker
thing
it
to
be
interesting,
like
I've,
taken
a
stab
at
what
I
believe
is
actually
required,
either
now
or
potentially
in
the
future
and
is
never
required.
It'll
be
interesting.
Just
to
get.
E
You
know
the
core
team
to
cast
an
eye
over
that
and
see
if
I'm,
missing
anything
and
then
I'd
be
happy
to
do
some
testing.
Like
you
know,
we
we
we
can
sort
of
roll
that
into
an
engineering
environment,
will
build
it
based
on
an
employee
one
11.1
tag
and
make
sure
it
matches
their
the
contour
version
as
well,
but
just
just
someone
and
I
over
that
list
of
extensions
we
compiled
out
would
be
helpful
as
a
starting
thing
and
we
can
do.
B
B
The
we
should
just
yeah,
but
that's
the
that
seems
completely
reasonable.
Oh
one
other
thing,
one
other
thing
that
is
going
on
is
there
is
a
it's:
it's
not
a
fork.
It's
a
separate
branch
of
envoy
that
is
building
against
open
its
Isola,
I've,
been
boringness
or
so
so
I
think
any
perhaps
one
of
the
one
of
the
and
that
will
then
create
a
separate
flavor
of
envoy
this.
This
has
been
terminates
on
what
projects
slash
open,
SSL,
open,
that's
the
github
I
think.
B
But
some
some
people
believe
that
opener
self-contained
magic,
Phipps
compliance
magic
which
allows
them
to
comply
with
Phipps
things
either
taking
a
position
at,
but
perhaps
there
there
is.
That
opens
the
door
for
a
discussion
of
using
ongoing
the
load.
Balancer
story
we
need
instead
of
extensions.
Can
we
play
some
spin
of
it
for
that,
like
we
have
so
many
different
spins
of
it
already
for
the
different
base
images
it's
built
on.
Can
we
just
have
one
more
something?
E
Yeah
and
obviously
there's
companies
like
Tetris,
so
they
didn't
in
getting
into
this
get
invoice
sort
of
game
as
well,
and
maybe
you
can
go
through
a
checkbox,
but
that
still
wouldn't
work
for
us,
but
in
theory
they
could
maybe
put
out
different
different
builds.
The
other
thing
as
I
went
through
this
analysis.
I
actually
need
to
go
back
to
the
end
boy,
guys
and
I
plan
on
doing
this
I
plan
on
raising
an
issue,
because
there
are
some
extensions
which
are
in
the
extension
list
that
you
can
compile
out.
E
B
E
C
E
B
B
We
just
point
you
very
close
very
strongly
to
an
image
over
there,
a
docker
hub
Lum,
so
it
seems
reasonable,
like
the
I'm
sure
you
understand
that,
like
like
in
our
released
once
we
have
to
make
it
as
simple
as
part
I
literally
understand
in
reality,
with
with
sophisticated
deployments.
You
know
that
we
can
speak
about
things
we
require,
rather
than
just
names
and.
B
B
B
Other
than
I'll
correct
that
link
to
be
a
little
it
be
points
to
the
current
milestone,
because
one
of
the
one
of
the
things
things
is
we
contributions
in
the
current
milestone
is
the
important
more
like
a
contribution
that
we're
not
planning
on
working
for
a
couple
of
months.
It's
a
bit
deflating
for
everybody.
B
So
definitely
when
you
go
to
github,
the
label
be
good
first
issue
and
labels
I
think
they're,
even
like
the
thinking
API
integrates
with
that
very
well
like
it
says
you
know
looking
to
contribute,
try
these
labels
and
pretty
sure
it
says
that
on
the
PR
interface
or
on
the
on
the
issue
interface.
But
those
are
because
he
standards
that
we
follow.
So
we
were
many
very
issues,
especially
the
longer
the
longer
running
ones
are
not
what
I
classifies
as
good
fit
issues
like
they.
B
They
either
have
a
lot
of
back-and-forth
in
a
very
easy
to
follow.
What
the
what
the
history
thing
is.
They
can
be
very
nerdy
indeed,
indeed,
technical,
but
they're,
not
great
issues
to
start
with,
but
for
things
that
for
things
that
I
do
recognize
our
good
ways
to
get
started,
contributing
to
the
project
we
label
them
as
such
and
I
kind
of
suggest
to
the
rest
of
the
people
on
it.
Saying
hey,
don't
put
your
time
into
that?
We.
You
know
that.
B
B
This
is
this
is
always
the
battle
with
every
open-source
project,
the
velocity
versus
completeness
but
I'm,
pretty
proud
about
contributing
contributing
doctor,
like
I,
told
you
how
to
get
started
and
in
terms
of
being
able
to
contribute
like
get
the
code,
build
the
code
and
do
it.
We
are
we
a
lot
of
time
and
effort
into
that
into
that
process.
We
we
feel
it's
pretty
it's
pretty
smooth,
so
it's
Michael
and
I
joked
about
how
hard
it
was
to
build
to
do
it
on
boy
from
scratch.
B
I,
don't
think
our
project
applies
to
that
like
we,
we
it's
the
department
making
the
changes
about
changing
the
code,
not
about
the
the
pantomime
of
building
and
pushing
the
release
and
making
sure
you've
done
it
correctly.
We
put
a
lot
of
time
into
our
PR
process,
so
we
could
work
that
we
submit
to
everybody.
A
A
Alright,
then
I
think
we're
we're
gonna
close
it
up.
I
want
to
thank
everyone
from
the
contour
team
for
for
being
here
and
explaining
all
the
work
that
goes
into
contour.
Thank
you.
So
much
and
I
want
to
thank
the
community
members
and
I
want
to
call
out
Michael
here
for
the
great
questions
today.
So
thank
you
so
much
for
being
here
and
with
that
yeah
I'm
gonna
end
the
call,
thank
you
everyone
and
have
a
fantastic
week
thanks.
