►
From YouTube: vSphere Integrated Containers Networking Overview
Description
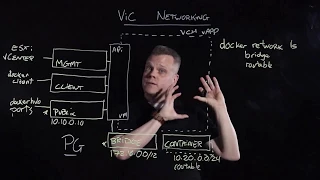
In this lightboard talk, Patrick Daigle provides an overview of the networking concepts for vSphere Integrated Containers.
Download VMware vSphere Integrated Containers (VIC) for free here: https://my.vmware.com/en/web/vmware/details?downloadGroup=VIC110&productId=614&rPId=15884
For more information see the VIC product page: https://www.vmware.com/products/vsphere/integrated-containers.html
A
Hi,
my
name
is
Patrick
tags,
I'm,
a
Technical
Marketing
Architect
with
VMware,
and
today
I'm
going
to
talk
to
you
about
Vick
networking
concepts
or
vSphere
integrated
containers,
networking
concepts
so
with
vSphere
integrated
containers.
We
start
with
this
virtual
container
host
construct
and
the
way
this
works
is
we
actually
wrap
this
inside
of
a
V
app,
which
gives
us
a
resource
pool
for
resource
management
perspective
and
that
inside
of
that
V
app,
we
provisioned
one
VM
and
that
acts
as
your
docker
API
endpoint.
A
So,
with
these
four
integrated
containers,
we
provide
you
with
a
consumption
model
where
you
can
use
docker
commands
to
consume
vSphere
resources,
and
we
provision
these
docker
images
as
VM
inside
of
this
V,
app
that
we
just
created.
So
when
you
think
about
creating
this
container
host,
what
we're
doing
really
is
we're
mapping
that
these
sphere
resources
that
we
want
to
provide
through
the
docker
consumption
model,
so
in
particular
today
we're
going
to
talk
about
the
networking
constructs
and
the
networking
resources
that
we
are
mapping
to
that
docker
interface.
A
A
So
this
will
be
used
for
connection
to
the
Internet,
to
download
from
docker
hub,
for
example,
or
to
expose
ports
that
are
running
inside
of
your
containers.
This
can
be
configured
with
either
DHCP
or
static.
Ip
address
the
second
network
that
you
need
to
provision
as
part
of
your
container
host
is
this
bridge
network.
Now
this
bridge
network
is
a
private
network
that
needs
to
be
isolated
and
that
needs
to
be
unique
to
each
container
host.
A
The
reason
is
that
we're
really
mimicking
here,
the
bridge
network-
that's
present
in
docker
that
allows
containers
to
talk
to
one
another
and
that
allowed
containers
to
talk
to
the
container
host.
So
we
want
this
to
be
private.
We
want
this
to
be
isolated
and
we
want
this
to
be
unique.
Per
container
host.
This
network
uses
a
fixed
network
scope
of
172
dot,
16.0
/
12.
The
addresses
are
assigned
by
the
container
host
as
you
instantiate
the
container
VMs.
A
So
that's
it
for
the
two
mandatory
networks
you
need
to
create
for
the
container
host.
So
now
we're
going
to
talk
about
the
three
remaining
networks
that
are
optional,
so
the
first
one
is
a
client
network.
So
if
you
decide
that
you
want
to
isolate
the
docker
client
traffic
from
the
public
network
traffic,
you
can
do
so
leveraging
this
client
network.
Now,
like
the
public
network,
this
client
network
can
use
both
DHCP
or
a
static
IP.
The
third
network
we
talk
about
here
is
the
management
network
in
a
typical
vSphere
production
environment.
A
The
management
network
is
segmented
because
this
is
used
to
communicate
with
your
vSphere
resources,
like
your
ESXi
hosts
or
your
vCenter
server.
So
in
a
typical
vSphere,
Enterprise
production
environment,
this
network
will
be
segmented
out,
so
we
allow
you
to
segment
it
out
as
well
when
you
provision
the
VCH.
A
Lastly,
we're
going
to
talk
about
this
container
network
here
this
container
network
is
a
user
defined
network
that
you
can
use
to
connect
your
container
VMs
directly
to
a
routable
network.
Now
this
is
something
that's
not
possible
in
the
regular
docker
world.
It
is
something
that's
unique
to
Vic,
because
we're
provisioning
these
docker
images
as
VMs.
You
can
actually
connect
these
VMs
directly
to
a
port
group
and
I'm,
going
to
give
you
an
example
of
how
that
works.
For
now.
A
One
thing
to
realize
here,
that's
very
important
is
that
each
of
these
networks
is
actually
backed
by
a
vSphere
port
group.
Now
this
board
group
can
be
either
via
network
distributed,
switch
port
group
or
an
nsx
logical,
switch
port
group,
but
because
this
is
backed
by
an
actual
vSphere
port
group,
you
get
a
lot
of
increased
visibility
into
what's
happening
in
terms
of
the
network
flows
between
all
of
these
networks.
A
So
any
network
flow
monitoring
tool
that
you
have
in
place
today,
like
view
realize
Network
insight
or
other
will
Ematic
automatically
apply
here
and
allow
you
to
see
all
the
network
flows
between
your
container
VMs
and
your
container
host
and
the
external
world.
This
also
means
that
I
can
apply
security
policies
now
on
each
of
these
port
groups
and
on
each
of
these
individual
container
VMs
that
I'm
going
to
provision
inside
of
this
container
host.
A
A
Ls
I'm
going
to
get
two
networks
defined,
namely
my
bridge
network
and
my
routable
network
again.
Remember
we're
mapping
vSphere
resources
into
this
docker
API
for
consumption.
So
when
I
do
dr.,
Network
LS
I
see
these
two
networks
that
I'm
at
when
I
created
my
container
house.
What
does
this
look
like
if
I
want
to
run
an
actual
docker
image?
We'll
do
two
examples
here.
A
So
what
happens?
I
run
this
locker
command.
The
doctor
command
runs
through
the
doctor
client
network
to
reach
the
API.
My
VCH
will
check
its
image
cache
to
see
if
it
has
this
httpd
image
present.
If
it
doesn't
have
it
it's
going
to
go
out
to
the
internet
on
the
public
network
to
fetch
it,
and
then
it's
going
to
talk
to
my
V
Center
on
the
management
network
to
create
my
containers.
A
Vm
so,
like
I,
said
we're
provisioning,
these
docker
images
as
VMs,
so
each
image
gets
its
own
VM,
the
container
in
it's
a
container
VM.
That's
very
lightweight,
that's
running
a
very
slim
Linux
kernel,
and
it's
running
only
my
httpd
process.
Now,
because
I
didn't
specify
a
network
here,
this
container
VM
will
actually
get
connected
to
the
bridge
network,
so
will
get
assigned
an
IP
from
this
scope
here.
A
A
A
A
A
So
in
conclusion,
I've
walked
through
all
of
the
different
networks
that
you
can
provision.
With
these
four
integrated
containers.
We
looked
at
these
three
networks
that
you
can
configure
in
terms
of
enabling
the
container
host
operations
we've
looked
at
the
two
different
types
of
networks
that
you
need
to
configure
in
terms
of
leveraging
container
networking
and
I've.
Given
you
examples
of
how
to
instantiate
those
using
docker
commands
and
how
these
map
now
into
actual
vSphere
come.
A
The
other
thing
we
talked
about
is
the
benefits
of
running
containers
as
VM
they're,
now,
first
class
citizens
in
your
vSphere
environment.
So
you
can
get
full
visibility
into
these
network
flows.
Now,
if
you're
running
a
network
flow
monitoring
tool-
and
you
can
apply
security
to
these
individual
container
because
they're
running
as
VMs
now,
you
can
apply
securities
to
this
individual
container
VMs
and
you
can
even
apply
micro
segmentation
if
you're
running
NSX
with
that.
Thank
you
for
listening
and
have
a
nice
day.
