►
From YouTube: Contour Demo - Ingress Controller
Description
In this demo, Xiao Hu Gao is showing how to use Contour to configure Kubernetes Ingress in multiple different use cases.
Check out Contour here: https://projectcontour.io
A
Hi
welcome
to
this
demo.
My
name
is
Jeff
Gould
ow
today,
I
will
demonstrate
how
you
can
use
contour
as
an
inker
controller
for
your
food,
nice
clothes.
Let's
first
talk
about
what
contour
is
contour
is
a
open-source
project
started
by
vmware
firmly
helped
you
at
a
high
level.
Contour
is
a
ingress
controller
for
kubernetes
that
works
by
deploying
the
Envoy
proxy
as
a
reverse
proxy.
A
A
load
balancer
and
the
goal
behind
contour
is
to
expand
upon
the
functionality
of
the
existing
ingress
api
to
allow
for
a
richer
user
experience,
as
well
as
solving
some
of
the
shortcomings
in
the
original
ingress
design.
Contour
introduces
a
new
ink
REST
API,
making
an
english
route
which
is
implemented.
There
are
custom
resource
definition.
Please
refer
to
the
contour
pickup
site
for
details
on
the
latest
feature
and
how
you
can
contribute
to
this
great
project.
A
Now,
let's
talk
about
sound
the
benefits
of
contour,
so
contour
leverages
envoy
for
data
point
traffic
for
tea,
as
most
of
you
already
know
on
what
is
designed
by
lift
to
solve
some
of
the
performance
challenges
required
to
scale
a
large
distributed
application
typically
distributed.
Applications
are
dynamic
and
constantly
scales
up
and
down,
so
real-time
programmability
is
a
must
to
scale
a
distributed
app
by
leveraging
contour
for
control
and
envoy.
As
data
plane.
A
You
can
make
real-time
updates
to
ingress
and
be
assured
that
established
TCP
sessions
were
never
reset
as
a
result
of
a
changing
application
pattern.
Count-O
also
scales
extremely
well
vmware,
along
with
our
customers,
have
performed
up
to
millions
of
concurrent
connections
in
quest
controller
is
the
aggregation
point
for
application.
Traffic
in
out
of
a
company's
cluster
are
typically
shared
by
multiple
development
teams.
When
the
challenge
is
in
a
multi-tenant
environment
is
a
lack
of
coordination.
A
Count
or
leverage
is
a
concept
delegation
to
safely
support
ingress
in
a
multi
team,
kubernetes
environment,
the
state.
This
delegation
capability
also
allows
the
admin
to
maintain
ownership
of
ingress
domain
secrets
or
TLS
certificates
required
to
secure
on
traffic
termination
within
a
admin
controlled
namespace,
while
giving
control
or
delegate
how
back
in
traffic
are
redirected
to
a
specific
development
team.
Counter
also
simplifies
the
configuration
required
for
some
of
the
more
advanced
use
cases
such
as
low
balancing
strategies
or
service
rating.
A
Traditional
ingress
controllers
often
use
annotation
to
enable
path
rewrite
to
support
those
use
cases
with
contour.
You
can
leverage
the
same
delegation
framework
to
control
how
much
traffic
are
routed
to
which
service
based
on
administrative
policies.
I
will
talk
more
about
that
when
I
do
the
Bluegreen
upgrade
and
also
service
rating
demonstration.
A
So
why
is
delegation
so
critical
for
ingress,
where
I
found
the
shortcomings
of
existing
ingress
solution?
Let's
take
a
look
at
this
through
the
example
I
have
here
in
a
multi
team
environment
I'll
have
two
teams
team
a
and
Team
B.
They
may
both
both
be
hosting
a
blog
site
using
Beamer
calm
as
the
host
team,
a
wants
to
use
service
a
which
may
be
press
team
B.
Maybe
wanna
use
service
B,
which
could
be
a
completely
different
application
packet
you're,
both
ingress
controllers
are
applied,
which
service
is
active.
A
A
Let's
see
how
contours
of
this
problem
contour
leverage
the
concept
delegation
to
safely
satisfy
ingress
in
a
multi
team
environment
in
a
kubernetes
cluster.
This
delegation
capability
is
implemented
in
the
form
of
a
English
Rossier
D.
So
the
main
concept
behind
this
English
Rossi
Rd
is
really
modeled
after
the
concept
how
things
work
in
DNS.
So
what
we
have
here
is
we
have
this
route
English
route,
which
has
authority
over
Reaumur
calm,
and
we
can
pass
this
Authority
over
to
other
folks
within
the
cluster.
So
this
example
here
Timmy
has
authority
of
the
American
/blog.
A
Now,
if
Team
B
comes
along
and
creates
an
ingress
route
of
the
scene,
very
calm
/blog,
because
the
Ron
has
already
been
delegated
to
team
a
it
will
be
rejected
since
team
a
has
already
been
delegated
to
it,
they
already
using
it.
The
concept
of
delegation
also
allows
you
to
isolate
secrets
and
serious
search
to
a
specific
namespace
we
talked
about
before.
So
instead
of
copying
your
TRS
search
into
team
evening
space,
you
can
keep
those
certs
and
is
within
a
am
control
main
space
for
centralized
management.
A
A
We
need
to
account,
for
we
will
create
a
dolphin
II,
the
water
balancer
from
anything
wears
on
English
traffic,
when
the
user
will
flow
from
the
internet
to
yellow
balancer
and
a
little
bit
nicer
for
Special
Envoy
in
an
unwary
bridge
proxy
traffic
to
the
backend
and
at
high
level
card
room
can
be
thought
of
as
a
translator
of
:
easy
objects
to
a
Envoy
configuration
contour,
watches
the
who
needs
a
green
grass
and
translates
them
into
JSON
format
and
serves
up
to
envoy
intern
on
pointers
west,
which
is
working.
No
traffic.
A
Counter
works
in
a
live
demo
here:
I
have
a
domain
define
using
a
file
as
the
accordion
s
and
I've
delegated
a
root
domain
to
ta-ta
have
English
ratified,
aroused
the
root
/
internal
servers
running
intimately
in
space
on
port
101
I
am
going
to
now
apply
the
inverse
Raj
mo.
You
can
see
that
the
root
domain
is
active
and
valid
in
TM.
A
and
I
can
navigate
to
teammates
photo
leaving
a
hostname
defined
in
English
route
was
from
the
browser.
A
Let's
now
switched
timbi
timbi
I'm
gonna
create
an
English
round
match
to
the
same
blue
hat
in
TM
Spees
namespace.
Once
we
apply
the
mo,
we
can
see
that
this
English
crowd
has
been
rejected
and
it's
considered
as
orphan,
because
this
pad
has
not
been
delegated
to
team
beat.
The
traffic
will
continue
to
route
to
teammate
uninterrupted.
A
Once
you
save
and
apply
the
mo,
you
can
verify
that
Team
B
stage
is
not
active,
switch
over
to
a
team
age
main
space.
It
was
the
analogy.
Maze
English
rock
is
being
orphaned
status
and
it's
no
longer
being
delegated
to
you
switch
over
to
team
these
memories.
You
will
see
now
the
ingress
role
is
active
with
him.
B
now
I'm
going
to
show
you
two
more
advanced
scenarios
of
using
ingress
route
and
the
delegation
to
implement
blue
green
upgrade
and
upstream
waiting
waiting.
A
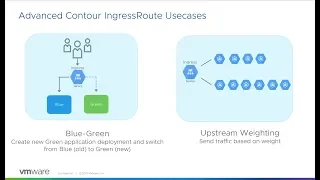
Let's
first
look
at
the
blue,
bring
up
great
team,
a
has
just
developed
a
version
two
of
the
service,
and
they
would
like
to
switch
over
from
version
one
to
version
two
which
is
almost
zero
downtime.
Looking
at
the
existing
ingress
demo,
production
servers
is
delegated
to
blue,
which
is
set
to
version
one
of
the
software
version.
A
A
You
can
see
that
changes
take
effect
almost
immediately
now
the
diploma
is
valid
and
the
blue
tip
for
me
is
orphaned.
We
switch
over
to
of
a
web
console.
Now
you
can
see
that
application
is
running
on
version
2.
Let's
take
a
look
at
our
last
demo:
option
waiting
to
the
blue-green
updates.
I
can
route
a
small
percentage
of
traffic
to
my
new
service
by
assigning
weights
to
version
1
and
version
2
of
my
software
based
on
user
feedback.
I
can
run
more
and
more
traffic
to
version
2
and
eventually
switch
over
everyone.
A
Looking
into
the
yellow
version
1
in
version,
2
of
my
service
are
both
listed
under
the
English
world
and
the
50%
of
the
traffic
are
assigned
to
version
1
and
the
remaining
50%
I
go
to
version.
Once
you
apply
the
mo,
you
can
use
the
standard
cube
CTL
commands
to
validate
the
traffic
week.
Quick
note:
the
traffic
percentages
are
completely
arbitrary.
It's
perfectly
ok
to
use
different
combinations
and
I
can
validate
for
my
browser
to
the
traffic
are
being
distributed
evenly
across
implants.
