►
Description
In this video, we show you how to correctly configure vSphere Integrated Containers Registry, Docker Engine and VIC Engine to securely pull and push images.
vSphere Integrated Containers registry provides certificate-based authentication out of the box and we explain how to combine roles, certificates, users and projects to achieve the business goals you need.
For more information please visit the vSphere Integrated Containers (VIC) product page:
https://www.vmware.com/products/vsphere/integrated-containers.html
A
Hi
there
in
this
video
I'm
going
to
show
you
how
to
configure
Vic
registry
and
docker
engine
to
talk
to
each
other
securely
so
that
they
can
pull
and
push
images
to
projects
in
big
registry
I'm,
also
going
to
show
you
how
to
then
take
those
images
from
Vic
registry
and
deploy
them
to
a
virtual
container
housed
in
vSphere.
So
quite
a
few
things
to
cover,
but
hopefully
it'll
be
really
useful
information
to
help
you
get
getting
started
with
the
basics
of
setting
up
this
kind
of
authentication.
A
So
I
have
a
completely
clean
install
of
Vic
registry
here
and
I
have
a
completely
clean
couple
of
docker
hosts
right
here,
regular
docker
host.
So
let's
get
started.
The
very
first
thing
I
need
to
do
is
to
download
the
root
certificate
for
this
registry.
The
root
certificate
is
the
certificate
that's
going
to
be
used
by
the
docker
engines
to
authenticate
with
this
registry.
So
it's
been
downloaded
to
my
downloads
folder,
and
here
it
is
what
I
need
to
do
is
get
this
onto
one
of
these
docker
hosts.
A
Let's
pick
this
one
as
simplest
way
for
me
to
do.
This
is
just
to
cut
and
paste
it.
You
can
use
SCP.
Whatever
means
you
prefer.
So
the
important
question
is:
where
does
docker
engine
expect
this
certificate
to
live?
Well,
it
expects
it
to
be
in
Etsy,
docker
and
a
folder
in
here
called
certs
dot
d,
and
in
this
top
D
folder.
You
need
a
subfolder
that
matches
the
IP
address
of
the
Vic
registry.
A
Okay,
hopefully
I've
done
that
correctly.
There's
my
certificate
that
I'm,
hopefully
going
to
use
to
authenticate
with
so
the
way
that
you
authenticate
from
docker
engine
and
you'll,
see
sorry
if
I
type
docker
info
with
my
snap
fingers.
This
is
the
docker
I'm
using
so
now
that
I've
created
my
certificate,
I
should
be
able
to
authenticate
with
the
registry.
So
if
we
type
docker
login,
which
is
the
means
for
authentication
and
adds
the
registry
IP
address,
that's
already
prompting
me
for
my
username,
because
I've
tried
this
once
already
put
in
the
password.
A
A
A
Okay,
so
I'm
now
a
user
I'm
not
going
to
set
myself
as
an
administrator.
So
now
back
in
my
docker
engine,
I
should
be
able
to
login
successfully
and
I
can
array
so
I've
logged
in
now.
What
can
I
do
now
that
I'm
logged
in
well?
Can
I
push
images
to
this
registry
now?
Well,
no
because
I
actually
need
to
create
a
project
to
push
an
image
too.
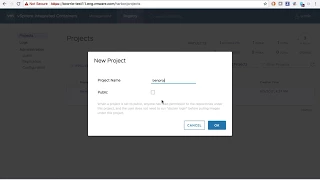
So,
let's
create
a
project
I'm
going
to
call
this
project
been
prod.
A
I
am
going
to
make
it
public
for
now
now,
just
to
be
clear,
a
public
project
is
a
project
that
a
user
doesn't
have
to
be
a
member
of
in
order
to
pull
images
from
it
and
we'll
see
it
a
little
bit
more
detail
about
that
later
on.
So
for
now,
I'm
going
to
make
this
public
so
I've
made
a
project.
So
I
should
now
be
able
to
push
an
image
the
project.
So,
let's,
let's
create
an
image
I'm
going
to
create
an
image
from
scratch.
A
Okay,
so
if
we
build
this,
call
it
test.
Okay,
it's
going
to
pull
down
the
Debian
image
from
docker
hub.
It's
going
to
run
the
command
to
actually
just
create
the
file
on
the
file
system
there
it
is
so
we
can
now
test
that
by
doing
docker,
run
I
t-test
and
there's
my
hello
world
file
on
the
file
system.
It's
a
good
that
works,
so
I've
now
created
an
image
which
we
can
see
in
docker
images.
Now.
The
next
question
is:
how
do
I
push
this
to
the
registry
and
the
project
that
I
just
created?
A
Well,
you
need
to
tag
the
image,
so
docker
tag
is
the
way
we
do
this
I'm
going
to
tag
this
image,
firstly
with
the
IP
address
or
the
address
of
the
the
registry
and
then
going
to
specify
the
project
which
is
been
proj,
I'm,
going
to
still
call
it
test,
I'm
going
to
specify
a
version.
So
it's
a
v1
okay,
so
this
will
tag
that
if
we
type
docker
images
we'll
see
the
tag
image
so
now,
if
I
go
to,
if
I
do
docker
push
and
take
this
same
all
right.
So
it's
not
happy.
A
So
why
is
it
not
happy?
What
have
I
not
done?
Well,
the
key
thing
to
remember
is
that,
in
order
to
actually
push
to
a
project,
you
need
to
be
a
member
of
that
project
and
you
need
to
have
the
right
role
to
be
able
to
push
so
I'm,
going
to
add
myself
as
a
member-
and
you
see
here
that
there
are
a
few
different
roles
that
I
can
be
in
order
to
push
I
need
to
be
an
admin
or
a
developer,
so
I'm
going
to
make
myself
a
developer
thumbs
up
there.
A
We
should
be
good
so
now
now
good
I
can
push
now.
I
ran
through
this
demo
a
few
times
ahead
of
time.
The
layer
already
exists
in
there
for
some
reason,
but
who
cares
it's
pushed
correctly?
If
we
go
there,
we
go
it's.
The
log
is
showing
that
I
just
pushed
to
this
repository.
If
we
go
to
to
here
we'll
see
yeah
there
is,
there
is,
but
I
just
pushed
so
that's
great.
So
now
that
I've
pushed
let's
go
into
a
completely
different
docker
host
and
look
at
how
I
might
actually
pull
that
image.
A
So
the
first
thing
I'm
going
to
do
is
I'm
going
to
just
try
pulling
it.
So,
let's
just
get
this
a
image
name
run.
It.
Ok!
Is
this
going
to
work?
It's
not
going
to
work,
even
though
my
project
is
public.
You
remember
I
configure
my
project.
If
we
look
at
the
project,
see
I
configured
my
project
to
be
public
I
can't
pull
it
without
authenticating
and
that's
because
we've
set
this
registry
up
by
default
to
only
work
with
a
secure,
authenticated
connection.
A
So,
even
though
the
project
is
public,
I
still
can't
pull
or
run
did
that
image
without
authenticating.
So
actually,
let's
create
a
new
user.
Let's
go
to
users:
let's
create
a
guest
user.
It's
like,
let's
create
a
George
user
George.
Is
my
colleague
George
that
it's
not
Georgia
via
mobile
combat,
doesn't
matter
George,
let's
call
him
Curious,
George
you'll,
love
that
all
right,
so
we've
now
created
a
George
user.
So
if
I
go
to
this
second,
so
remember
this
is
a
completely
different
docker
house.
The
one
we
were
previously
in
was
this
one.
A
This
is
a
completely
different
docker
host.
So
if
I
do
docker
login
ten
more
one
868
eighty
two
and
type
George
and
type,
my
password
okay,
what
are
we
doing
wrong
here?
Well,
remember:
I!
Need
that
certificate
on
every
single
docker
host
that
I
want
to
authenticate,
so
I
actually
have
to
go
back
over
here.
What
I'm
going
to
do
is
fast-forward
to
the
point
of
which
status
certificate
is
already
created,
so
the
magic
of
video
okay,
so
we've
created
our
certificate
in
the
same
way
as
we
did
on
the
last
docker
host.
A
I
should
now
be
able
to
log
in
as
George
hooray,
I'm
George,
so
you'll
find
that
scary
go
to
the
projects
now
now
remember.
George
is
not
a
member
of
this
project,
but
it
is
a
public
project,
so
I
should
be
able
to
run
actually
just
make
it
a
private
project.
Let's
make
it
fail
first.
So
if
we
look
at
the
projects,
let's
make
this
project
private.
A
So
if
I
do
docker
run
there,
we
go
okay,
so
we're
now
Ascenta
cated,
but
I
don't
have
the
ability
to
pull,
because
because
the
project
is
private,
I'm,
not
a
member
of
the
project.
So
the
two
ways
to
solve
that
are
to
either
go
to
projects
and,
as
me
add
me
as
a
as
a
guest.
So
we
can
do
that
if
we
go
to
the
project
and
add.
A
George
as
a
guest,
so
George
can
now
pull,
but
he
can't
push
and
the
same
thing
would
have
happened
if
I'd
made
that
project
public.
So
this
is
just
a
little
bit
of
information
about
the
various
roles,
the
various
different
means
of
authenticating,
so
the
final
thing
I'm
going
to
do
is
I'm
actually
going
to
show
you
how
to
run
this
exact
same
image
but
using
a
virtual
container
house.
So
those
of
you
who've
seen
my
recent
video
on
how
to
download
and
install
Vick
at
a
VCH
may
well
be
familiar
with
this
command
line.
A
Big
machine
create
command
with
some
arguments.
Now.
This
is
the
command
line
to
install
a
virtual
container
house
to
my
vSphere
cluster.
With
all
of
the
arguments,
we
all
noticed,
I've
added
an
argument
on
to
the
end
here:
registry
CA
and
pointing
to
my
certificate,
the
one
that
I
downloaded
from
SiC
registry
earlier.
A
So
let's
install
this
virtual
container
host
and
let's
try
to
deploy
that
exact
same
image
to
it.
Now
you'll
see
loaded
registry
CA
from
the
location
there,
that's
verifying
that
it's
picked
up
that
certificate
and
it's
associating
it
with
this
virtual
container
house
so
that
we
can
authenticate
with
vim
registry.
So
the
next
thing
I
need
to
do
is
to
point
my
docker
client
at
the
VCH
which,
as
you
can
see,
we
with
this
is
successful.
Okay,
so
let's
try
authenticating
I'll.
A
A
Now
it's
going
to
create
VM
decays
from
that
image.
On
the
data
store
that
I've
specified
it's
a
little
bit
slower
than
the
overlay
file
system,
one
that
looks,
but
it's
not
horrendously
slow
and
then
it
should
run
the
image
and
the
way
that
we
can
double
check.
That
is,
we
can
have
a
look
on
the
file
system
and
see
if
our
hello
world
file
is
there
so
there
it
is.
So
let's
do
an
LS
there.
