►
From YouTube: WEBRTC WG F2F meeting June 2019
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
B
B
B
B
You
Eric,
basically,
all
we
need
to
do
is
to
note
the
decisions
that
we
make
and
the
meeting
is
being
recorded.
So
we
can
move
on
okay,
so
we've
got
one
issue:
one
PR
on
web:
it's
the
ice,
some
discussion
on
a
media
capture
issue
from
UN
a
few
things
on
in
the
use
cases
and
then
we'll
get
to
web
RTC
PC
for
the
rest
of
the
meeting.
B
Well,
I
can
maybe
try
to
do
it
slide
his
slide.
It's
not
very
big.
Basically
peter
has
put
together
a
PR
on
initial
flex.
Ice
methods
and
attributes.
I
haven't
gotten
feedback
from
developers
yet,
but
the
big
question
he
has
is
whether
anyone's
interested
in
implementing
any
part
of
it
any
thoughts
from
anyone
in
the
audience.
A
A
A
B
B
F
So
I'm
just
trying
to
understand
what
this
might
do
for
a
development
I,
you
might
be
able
to
say,
hey
I,
don't
like
the
look
of
that
v6
address.
Let's
just
not
nominate
it
is
that
the
sort
of
logic
that
you
might
apply,
because
it's
to
do
with
your
app
or
some
behavior
I'm,
trying
to
work
out
why
how
this
level
of
granularity
gets
useful
just
to
be
useful,
yeah.
B
F
B
B
So
you
want
to
a
candidate
involving
a
turn
server
a
relay
candidate
which
you
can
bring
up
immediately,
but
it
wouldn't
necessarily
be
the
ultimate
candidate
so
might
want
to
find
something
else,
that's
less
expensive,
but
you
want
to
bring
up
that
that
turn
candidate
immediately
and
as
an
example,
you
want
to
keep
it
as
a
as
an
alternative
so
that
you
can
always
fall
back
to
it
if
the
other
one,
the
other
candidate,
fails.
Oh.
B
F
B
Know
it
one
of
the
things
that
can
give
you
is
the
ability
to
maintain
a
connection
through
interface
changes,
because
you
can
use
turn
mobility
and
keep
that
turn
candidate
alive,
even
as
you
move
around
and
then
search
for
less
expensive
candidates
as
they
come
in
and
out.
Okay,
but
well
I
I
mean
I.
Think
one
thing
is
to
tie
the
end,
be
used
cases
to
things
that
might
need
this,
which
some
of
which
we'll
talk
about
later,
okay,
so
I
think
we
have
our
next
steps
on
this
one.
G
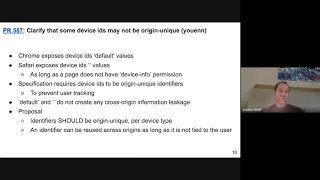
Okay,
so
the
first
PR
is
to
no
knowledge
in
the
spec,
but
some
implementations
are
using
device
IDs,
which
are
not
origin,
unique.
The
best
chrome
that
has
the
default
value
for
device
ID,
which
is
not
all
unique
and
Safari,
also
exposed
the
empty
string
device
ID
value
in
Internet
when
calling
a
pneumatic
devices.
As
long
as
a
page
has
not
vice
information.
G
But
clearly
some
value
is
like
default
and
I'm
teaspoon
do
not
create
any
cross
origin
information
leakage.
So
there's
no
issue
with
user
tracking
for
those
values.
So
the
proposal
here
is
to
relax
a
little
bit
the
stack
so
that
we
we
say
that
device
IDs
should
be
for
a
generic,
at
least
for
device
type
and.
G
G
G
So
this
is
specific
to
Safari,
but
we
were
using
the
empty
string
for
device
IDs
and
help
a
sufferer
is
facing
the
empty
string
on
a
vitality
constraint
as
if
the
constraint
is
not
specified.
So
if
you
are
saying,
but
about
an
exact
device
ID
containing
with
the
empty
string,
we
do
not
look
at
it
and
we
we
provide
you
your
stream
with
basically
the
first
matching
device.
G
My
understanding
is
that
this
pattern
might
be
useful
in
some
cases
like
at
least
in
Firefox,
for
instance,
the
first
apparently
the
first
audio,
the
first
device
that
is
listing
in
univille
devices
list
is
the
default
system
one.
So
some
applications
might
use
that
to
actually
pick
the
default
one
and
we
do
not
want
to
break
them.
So
that's
why
we're
doing
that.
So
the
proposal
in
VCR
is
to
interpret
the
empty
string
as
if
the
constraint
is
not
specified.
G
So
it's
very
similar
to
the
existing
case
in
the
spec,
where
an
empty
array
is
considered
as
as
if
the
constraint
is
not
specified,
of
course,
only
apply
to
downstream
constrain
so
which
means
facing
more.
Besides
no
device,
a
group
ID
currently
in
suffer
implementation.
We
are
only
implementing
that
for
device
ID,
but
we
we
would
update
our
implementation
for
all
four
bullets,
so
the
PR
that
is
written
595
is
specific
to
Vianca
spec
value.
G
G
G
Does
it
which
implementation,
chrome,
Chrome
and
Firefox
so
I
think
I
meant
Firefox,
do
not
provide
the
empty
string
device
ID.
So
in
practice
it
might
it
might
not
happen,
but
it's
true
that
if
you
craft
getusermedia
and
you
pass
on
a
pass,
an
empty
string
device
ID,
probably
Firefox
and
ohm-
will
fail.
So
it
would
require
changes
to
firefox
and
chrome
to
align
with
it.
I
haven't
done
the
test
there,
but
I
would
guess
that's
for
many
buckets.
I
H
E
A
A
A
F
I
G
I
G
A
D
On
once
you
do
get
used
to
media,
then
you
stop
using
empty
string
in
numerate
devices
right
device
change.
Could
it
be
true
to
say
that
you
know
the
the
getusermedia
algorithm
matches
because
device
ID
empties
being
matched
matches
at
the
time
of
the
call,
and
then
it's
a
device
change
or
does
the
device
change
mean?
We
should
over-constrained
well.
I
D
G
I
H
Yeah,
I
think
I
think
the
spec
doesn't
even
have
the
concept
of
a
full
device.
So
I
think
that,
with
a
fiery,
all
devices
are
empty
string
before
so,
though,
if
all
of
them
were
exposed
with
with
empty
stream,
means
that
if
you
pass
empty
string,
any
of
those
devices
that
you
use
would
match.
So
how.
I
G
D
F
G
G
J
B
B
B
F
G
G
B
C
B
Well,
I
think
it's
trying
to
say
that
that
you
could
potentially
get
some
information
about.
What's
being
said
through
those
things,
so
you
gotta,
you
know,
have
to
encrypt
it
to
the
so.
The
media
server
wouldn't
get
it.
Although
it's
not
clear,
I
assume
it's
I'm
assume
it
means
end-to-end
encrypted,
but
it
doesn't
say
that
I
get.
J
J
K
B
B
A
A
F
B
B
F
B
F
B
B
A
L
M
B
C
B
C
A
B
A
A
So
this
is
this:
this
is
really
relevant
when
either
you
have
a
media
server
for
from
a
third
party,
or
you
have
an
architecture
where
you,
where
you
assume
that
you
can
detect
any
shenanigans
from
the
JavaScript
on
your
bra
in
your
browser.
But
you
cannot
detect
shenanigans
down
on
the
media
server
so.
B
J
J
K
B
A
So
we
have
I
think
we
basically
have
that.
Yes,
these
are
two
valid
use
cases
and
the
description
needs
to
be
high-level
enough,
that
we
know
we
can
easily
see
what
we
are,
what
the
security
requirements
were
imposing
are,
and
you
need.
We
need
a
victim
volunteer.
It's
actually
massage
needs
to
be
high
level
enough.
A
B
F
G
But
we
we
are
not
trying
to
hide,
for
instance,
when
user
I
typing
on
the
keyboard
and
exchanging
text,
messages
which
are
which
might
have
the
same
kind
of
privacy
information.
So
it's
in
there
there's
some
unbalanced
and
there.
The
additional
concern
I
mean
habits
that
I
don't
know
any
native
app
where
there
is
this
difference
between.
G
The
trust
you
have
and
the
fact
that
yeah
can
we
be
given,
but
the
native
app
will
not
have
access
to
the
camera
excellent,
weird
ways.
So
it's
it's
somehow
a
new
concept
I
understand
that
it's
the
web,
it's
Pacific,
where
I'm
still
concerned
how
it
would
actually
work
in
in
practice
and
web
solutions
right.
J
A
E
B
B
I
B
B
A
It's
easier,
five
is
minor
one.
It
is
that
when
I
was
reading
through
this
okay,
the
ability,
impulsive
bandwidth
limit
across
all
mesh
n
put
limits
the
build
the
perfect
cues
that
can
affect
audio
quality
or
perceived
latency
and
again,
no,
it
doesn't
I
mean
imposing
a
bandwidth
limit,
is
in
imposing
bandwidth
limits.
So
if
you
want
to
come
effect
audio,
they
call
the
end
proper
see
latency
said
say
that
you
want
to
have
a
fear
or
useful
control,
Oh
management
of
all
their
calls
and
latency
yeah.
K
B
A
O
Okay,
great
thanks
for
having
me
here
so
hi,
everybody
I'm
for
us
I'll
briefly
introduce
myself
so
I
I've
used
the
data
channel
in
the
past
for
various
innovative
use
cases
I.
Think
in
2013,
I
started
a
company
called
peer
CDN,
which
was
using
the
data
channel
to
implement
next
generation
CDN.
The
idea
was
to
do
efficient,
peer-to-peer
delivery
of
static
website
content,
and
then
we
were
acquired
by
Yahoo
in
2015
and
then
in
2014
I
started
web
torrent,
which
is
an
open
source
project
to
make
the
BitTorrent
protocol
work
in
the
browser.
O
It
also
used
that
a
channel
as
the
transport
and
web
torrent
has
millions
of
of
monthly
users
now
so
anyway.
Thank
you,
I
just
wanted
to
say
thank
you
for
having
me
here
and
to
describe
this
this
DHT
use
case.
So
I
thought
it
would
be
useful
to
start
with
an
overview
of
what
a
DHT
is
just
so
everybody
is
on
the
same
page,
to
understand
the
use
case
better.
O
So
the
idea
is,
the
HT
provides
a
way
for
millions
of
computers
to
self-organize
into
a
network,
so
the
computers
can
communicate
with
other
ones
in
the
network
and
ideally
share
resources
in
some
way,
and
they
do
this
without
the
use
of
a
central
registry
so
because
of
the
the
the
fact
that
it
doesn't
use
the
central
registry
in
any
way.
This
is
used
in
nearly
every
decentralized
protocol,
from
the
torrent
to
ipfs
to
that
aetherium
I
think
bitcoin
uses
something
similar
and
it's
it's
it's.
O
It
finds
its
way
into
basically
any
distributed
data
store,
and
you
know,
there's
just
a
lot
of
examples
of
this
I
think
there's
even
more
than
I
listed
here.
I
could
pee
free
net
coral,
Apache
Cassandra
and
even
some
Oracle
products
actually
use
dhts
as
well,
so
I
mean
I'm
a
little
biased
but
I
think
it's
a
very
beautiful
idea
in
computer
science
and
so
I
think,
if
you're
interested
to
learn
more,
you
can
read
the
academic
paper
about
it
here
that
I
linked,
but
basically
the
key.
O
The
key
abstraction
that
it
provides
to
all
these
various
applications
is
that
you
can
look
up
a
key
and
get
the
value
that's
associated
with
that
key,
and
you
can
do
it
without
it
appears
having
any
central
way
of
coordinating
and
despite
the
fact
that
there's
no
central
coordination,
it's
extremely
efficient,
so
you
can
do
it
in
log
n
time.
Where
n
is
the
number
of
peers
in
the
network?
So
could
I
go
to
the
next
slide?
O
So
there's
I
don't
want
to
get
too
much
into
the
details,
because
it's
quite
a
long
topic,
but
I
just
wanted
to
talk
a
little
bit
about
the
properties
of
Kedah
melia,
which
is
the
most
popular
way
that
people
use
dhts.
So
you
see
here,
this
is
just
sort
of
a
visual
representation
of
how
you
iteratively
look
up.
O
The
key
are
looking
for
in
the
network,
so
the
idea
is
that
every
peer
maintains
a
routing
table
which
is
basically
contact
information
for
other
peers
in
the
network
and
then
the
the
data
they're
looking
for
the
key
they're
looking
for
might
be
on
some
peer
who
they
don't
know
how
to
contact
directly.
But
what
they'll
do
is
they'll
contact
the
closest
peer,
so
there's
the
notion
of
closeness.
O
Every
peer
has
an
ID
and
you
can
be
sort
of
you
can
be
close
to
data
or
far
away
from
data,
and
so
I
will
ask
the
closest
peers
that
I
know
of
like
hey.
Do
you
have
this
data
that
I
want,
and
if
the
peer
does
they'll
provide
it
to
me,
but
most
likely
they
won't
have
it,
but
they
will
be
able
to
tell
me
about
peers
that
they
know
that
are
closer
to
the
data,
and
you
can
structure
the
network
such
that
you
can
in
a
very
small
number
of
hops.
O
You
can
find
the
data
that
you're
looking
for
so
in
the
network
of
10
million
peers.
You
can
actually
get
to
the
the
peer
that
has
the
data
that
you
want
and
in
roughly
20
hops,
and
this
is
because
of
the
login
efficiency
that
I
described
earlier.
So
in
general,
there's
like
three
sort
of
RPC
messages
that
you
would
send
in
such
a
system.
So
you
would
ask
appear
to
store
a
key,
a
value
pair
for
you.
There's
then
there's
fine
mode,
which
is
basically
saying.
O
Please
give
me
information
about
the
K
closest
peers
to
the
ID
that
I'm
looking
for
and
in
the
normal
way.
This
is
used.
It's
often
just
an
IP
address
and
a
port,
because
this
is
the
this
is
what
you
need
to
contact
the
peer.
Obviously,
in
WebRTC
it's
going
to
be
different
than
that,
and
then
lastly,
find
value
is
basically
a
way
of
saying
it's
similar
to
find
note.
O
If
you
have
a
pre-configured
signaling
server
and
all
the
browser's
involves
no
to
connect
over
HTTP
or
a
WebSocket
to
to
such
a
signaling
server,
and
obviously
this
is
a
good
fit
for
applications
like
hangouts
or
Skype
or
or
something
like
that,
where,
where
WebRTC
is
basically
being
used
to
avoid
sending
large
amounts
of
video
data
through
a
central
server.
But
it's
a
poor
fit
for
a
distributed
application
that
wants
to
avoid
centralized
signaling
entirely
so
with
WebRTC.
O
I
can't
maintain
very
many
connections
at
the
same
time,
and
my
my
routing
table
then
is
becomes
a
lot
less
useful,
so
yeah
I,
just
amplified
again
likely
peers
must
remain
actively
connected
to
any
peer
that
they
wish
to.
Let
other
peers
know
about,
because
there's
no
way
that
I
can
get
an
offer
from
a
peer
disconnect
from
them
and
then
later
use
that
offer
to
reconnect
to
them.
O
So
these
are
the
requirements
that
we
came
up
with
to
sort
of
fix
this.
This
issue
for
this
use
case,
so
the
number
one
requirement
is
the
one
at
the
top.
That
is
the
most
important
one
and
all
the
rest
are
nice-to-haves,
but
the
number
the
number
one
requirement
here
is
listen
or
multiplex,
and
the
concept
is
that
an
application
must
be
able
to
create
long,
lasting
signaling
data,
so
signaling
data
which
I
can
generate
and
have
it
lasts
more
than
the
ideally
more
than
the
the
duration
of
the
the
NAT.
O
You
know
hole
punching
timeouts
if
that
makes
sense,
and
furthermore,
that
I
should
be
able
to
share
this
signaling
data
one
time
and
have
multiple
incoming
peers
use
that
signaling
data
to
connect.
So
this
this
idea
is
that
that
the
offer
the
WebRTC
offer
can
be
stored,
sort
of
over
a
little
bit
of
longer
a
term
in
someone's
routing
table,
and
so
they
should
be
able
to
then
provide
that
just
to
another
peer
and
the
peer
can
use
that
to
to
connect.
C
O
That's
a
great
question,
so
I
I
think
at
the
bare
minimum
it
would
be
the
most
important.
The
most
important
feature
is
to
be
able
to
accept
multiple
incoming
peer
connections
with
one
offer
so
timewise
like,
even
if
it
was
only
the
same
constraints
that
WebRTC
has
today,
in
other
words
like
roughly
60
seconds
or
so
this
would
still
be
very,
very
useful
for
the
DHD
use
case.
O
Obviously,
if
I
make
it
last
last
longer
or
something
like
ten
minutes
would
be
very,
very
useful,
because
now
we
don't
need
to
update
our
routing
tables
so
often
right,
but
at
the
bare
minimum.
It's
it's
important
to
be
able
to
generate
this
signaling
data
share
it
with
many
people
and
then
have
those
people
connect
to
us
without
needing
to
forward
an
answer
to
us.
O
So
I
don't
know
if
that
makes
sense
to
people,
but
the
concept
is
it's
sort
of
like
an
asynchronous
offer
answer
and
then,
in
that
situation,
mm-hmm
right.
So
the
interactivity
is
a
big
problem,
because
it
requires
that
the
peers
are
all
connected
to
each
other
and
be
able
to
forward
these
these
offers
and
answers
along.
Maybe
Leonard
can
jump
in
here,
if
I'm
not
being
clear
so.
M
The
idea
I
had
for
this
requirement
is
to
basically
have
something
like.
Oh,
it
is
house
where
you
have
some
kind
of
asynchronous
sync
signaling.
We
don't
depend
on
having
an
offer
before
you
can
send
an
answer,
so
you
have
basically
you
post
your
signaling
data,
which
could
be
it
could
look
like
what
OTC
offers
at
the
moment.
Your
posting
data
once
and
multiple
peers
can
use
it
to
connect
to
you
and
one
example.
One
idea
I
have
two
to
keep
the
net
whole
openness
to
just
continuously.
F
Think
we
don't
I,
don't
think
we
need
to
solve
it
here.
I
think
it's
clear
that
to
me
this
is
kind
of
interesting
space
and
useful
for,
for
other
use.
Cases
actually
like
I,
had
a
requirement.
That
was
quite
like
this,
where
I
want
two
devices
that
are
on
on
a
home
Wi-Fi
to
talk
to
each
other,
but
the
Nets
gone
down.
So
I
can't
see
the
signaling
server
anymore,
but
I
am
they
just
talk
to
each
other?
F
They
know
each
other's
the
last
set
and
in
theory
they
should
be
able
to
reconnect,
but
they
can't
because
they
need
to
reach
out
to
a
signaling
server,
which
will
then
drop
out
of
the
equation
three
seconds
later.
So
there
are
a
bunch
of
interesting
uses
for
this
technology.
I
kind
of
feel
it'd
be
nice
not
to
solve
them
all
here.
That
makes
sense.
I.
M
M
F
I'm
not
like
again
I
would
sort
of
push
back
on
accepting
other
populations.
Is
it's
like
almost
a
solution,
rather
than
like
what
you
really
want
is
some
kind
of
persistent
signaling,
unlike
how
it
what
it
does
with
that,
what
the
behavior
is
is
is
I
think
we
could
still
like
iterate
on
so
I
wouldn't
want
to
put
that
into
the
requirements,
because
I
don't
think
it's
a
requirement.
F
A
Then
that's
certainly
doable
when
I'm
also
thinking
that
it's
actually
been
done.
So
that
way
we
have
pretty
much
all
the
API
is
needed
in
in
the
ice
in
the
ice
transport,
tray,
API
and
well,
except
connected
today
to
them
at
the
moment.
You're,
basically
saying
that
this
is
data
channels
right
well,.
K
O
O
You
know
in
a
way
where
I
can
save
their
offering
I
I
mean,
maybe
it
doesn't
have
to
do
with
saving
offers
or
signaling
data.
That's
again
an
implementation
detail,
but
it's
a
some
extent.
We
can't
get
away
from
a
little
bit
of
implementation
detail
in
the
sense
that
if
we
want
to
be
able
to
create
certain
Network
topologies,
there's
I
need
to
be
able
to
describe
like
requirements.
I
have
for
the
way
I
can
connect.
O
It
appears
right
so
I
want
to
be
able
to
disconnect
from
somebody
and
then
connect
to
them
again
later
five
minutes
from
now.
Right.
That's
that's!
That's
I!
Think!
That's!
That's
not
really
getting
too
much
into
implementation.
That's
talking
about
a
requirement
for
type
of
application
to
be
built.
Yes,.
O
Right
the
use
case
for
worker
threads
is
that
you
can
it's
really.
It's
quite
would
enable
a
lot
of
really
quite
interesting
use
cases.
You
could
imagine
a
service
worker
that
sits
there
intercepting
all
kinds
of
HTTP
requests
and
then,
instead
of
letting
those
go
out
to
the
server
it
handles
them
with
WebRTC
data
channel
instead,
which
is
extremely
powerful
idea.
A
No
way
what
what
way,
what
we
have
with
data
channels
is
that
and
they're
much
more
loosely
tied
tied
to
the
concept
of
variation,
but
they
we're
getting
into
into
implementation
again.
So
the
the
basic
requirement
is
that
you,
you
should
be
able
to
know
about
peers
and
then
connect
to
them
without
having
to
involve
the
third,
that's
singling
in
server
in
order
to
connect
to
them.
O
If
you
try
to
create
more
than
a
few
dozen
and
but
I
also
think
the
protocol
just
overall
the
protocol,
some
protocol
decisions
make
it
hard
to
implement
WebRTC
efficiently
and
in
a
in
a
sort
of
way
that
even
the
best
implementations
might
not
be
able
to
get
passed.
So,
ideally,
we
would
be
thinking
about
how
to
support
a
case
where
the
browser
can
have
say:
I,
don't
know
fifty
connections,
you
know
and
have
that
be
a
lightweight
a
lightweight
abstraction,
I'd.
A
O
E
O
Hundred
would
be
better
I
mean
so
so
in
existing
the
HTS
that
are
used
in
all
the
various
projects.
I
mentioned
earlier.
The
number
that
the
number
of
nodes
in
a
routing
table
can
get
up
to
close
to
a
thousand
nodes
and
in
those
use
cases
there
in
those
implementations,
they're
just
storing
IP
addresses
and
ports
for
every
peer
and
their.
So
it's
very
it's
lightweight
like
to
store
a
thousand
IP
addresses
and
ports.
O
It's
like
storing
a
thousand
strings,
it's
nothing
and
though
they're
not
even
actively
connected
to
those
nodes
right
because
they're
using
UDP,
so
they
can
just
fire
off
a
packet
to
that
to
that
port
anytime.
They
want
to
so
so
the
the
end
with
twenty
million
nodes
in
a
lot
of
these
networks,
you'll
see
you
end
up
having
a
routing
table
of
roughly
yeah
a
couple
hundred
or
a
thousand
entries
in
your
in
your
routing
table,
so
yeah
I
think,
let's
say
hundreds
would
be
good.
So.
A
M
O
M
Aspects
of
it
as
well,
one
of
them,
is
the
it
basically
goes
back
to
listener
multiplex,
where,
if
you
do
create
multiple
equations
now
you
allocate
a
lot
of
sockets
and
a
lot
of
ports,
and
that
is
an
issue
and
the
other
one
is
also
part
of
efficiencies.
If
you
have
a
lot
of
background
noise,
when
you
have
peerconnection
it's
going
on
many
Pico
nations,.
B
O
Okay
and
then
this
this
last
requirement
here
is
quite
a
long
shot,
and
it's
probably
going
to
be
controversial
so
but
I
just
we
just
had
to
throw
it
in
here,
just
just
to
get
people
thinking.
But
the
idea
here
is
to
have
connections
which
are
offer
offers
which
are
persistent
across
like
restarts
of
the
browser.
O
And
this
this
is
not
strictly
required,
but
this
this
would
obviously
it
would
be
really
nice
to
be
able
to
to
restart
the
browser
and
have
the
routing
table
that
I
I
saved
from
six
hours
ago
still
be
useful
to
get
me
connected
to
peers
without
having
to
to
go
and
talk
to
a
central
server
to
get
reconnected
to
the
network.
So,
to
avoid
that
initial
bootstrapping
step
for
you
or
you
ask
a
central
server
to
give
you
a
couple
of
peers
to
get
you
going,
I
think.
A
A
A
A
M
B
B
H
H
O
I
mean
one
one
example
you
could
imagine
is
ipfs.
This
is
a
global
file
system.
The
idea
is
I
know
a
piece
of
content
that
I
want.
I
know
the
hash
of
that
content
and
I
need
to
find
who
in
the
world
has
the
content.
So
this
is
in
a
you,
know,
opposite
of
in
a
way
from
like
a
URL
works
with
the
URL
I,
say:
I
know
the
server
I
want
to
talk
to
and
I
ask
it
for
a
specific
resource,
by
name
and
so
in
the
IP
FS,
or
this
sort
of
decentralized
model.
O
Here,
I'm,
saying
I
know
the
content.
I
want
and
I
don't
care
who
I
get
it
from
just
anyone
who
has
it?
Please,
you
know,
give
it
to
me
and
then
I'll
verify
that
I
got
the
correct
content
by
checking
by
hashing
it
and
checking
that
it
matches
what
I
expect
so
being
able
to
use
the
DHT
to
find
people
or
defined
contents,
and
you
know
being
able
to
store
the
sort
of
where
the
key
is
the
contents
hash
and
the
value
is
the
content
itself.
That's
like
one
very
common
use
case.
O
Yes,
exactly
so
I
could
visit
a
website
and
that
website
could
load
over
a
network
like
this.
The
website.
Could
you
know
that,
in
the
background,
it's
fetching
resources
from
this
distributed
network
and
and
in
some
cases
the
content
isn't
available
anywhere
else.
So,
if
I
want
to
access
that,
I
need
to
access
it
on
ipfs
or
on
that
or
on
BitTorrent
or
wherever
the
content,
lives
and
I
want
to
be
able
to
to
do
that,
to
do
that
over
WebRTC.
M
Okay,
so
I
I
made
progress
to
try
solve
the
problem
of
well,
basically
having
a
solution
to
for
use-cases
I
can't
use
getusermedia
to
access
I
call
them
the
best
available
mode
and
the
default
mode.
So
the
status
quo
is
that
without
without
get
user
media,
you
usually
have
IP
handy
mode,
greater
or
equal
than
2,
and
for
terminology
I'm
calling
this
default
mode
and
with
getusermedia
you
usually
have
a
peer
handling.
One
and
I
call
that
the
best
available
mode.
So
the
problem
with
that
is
that
not
all
use
cases
can
use
getusermedia.
M
We
have
received
only
media
use
case,
they
turn
on
use
cases
and
they
obviously
can't
ask
for
camera
access.
So,
and
these
are
often
innovative
local
network
use
cases
which
makes
well,
they
could
very
much
use
IP
heading
mode,
one
because
they
operate
on
local
networks.
More
often
so
I
also
see
that
default
mode
and
the
best
available
mode.
They
are
diverging
further.
For
example,
in
Odyssey
B
am
DNS
whose
candidate
obfuscation
is
now
going
to
to
be
employed
as
far
as
I
can
see
and
yeah.
M
So
I
I
made
a
proposal
to
add
the
direct
connection
permission.
It's
a
new
permission
to
the
permission
API
and
out
of
the
well
section
that
that
says,
basically
media
devices
camera
a
microphone.
They
may
also
implicitly
grant
their
connection
that
a
starting
point,
then,
is
an
additional
API
for
web
body
CPC,
which
basically
extend
extends
the
our
TCP
connection
in
two
ways.
It's
on
one
static
method
and
one
new
event.
M
M
It
can
do
that
at
any
time,
but
ideally
it
should
do
that
with
providing
context
and
a
half
I
did
a
couple
of
examples:
how
to
provide
context
in
in
the
pull
request,
and
then
the
application
can
register
connection
upgradeable
event.
So
this
is
a
point
where
it
gets
a
little
bit
tricky,
but
so
the
API
has
been
API
has
been
developed
in
a
way
that
allows
to
allows
user
agents
to
experiment.
M
So
basically,
what
happens
now
is
that
there's
some
mechanism
going
on
that
at
some
point
may
or
may
not
grant
a
direct
connection
permission
in
whatever
user
into
whatever
way
the
browser
wants
to
other
user
agent
wants
to
notify
this
request
and
the
connection
upgradeable
event
fires.
If
and
only
if
the
mode
has
been
upgraded,
it's
the
best
available
mode.
So
as
it
is
a
static
method,
it
would
apply
to
all
peer
connections
of
the
current
realm
and
since,
as
I
mentioned,
that
getusermedia
may
implicitly
grant
this
connection
this
permission.
O
M
Sorry
so
providing
context
is
something
important,
I
think
so,
for
some
use
case
may
make
sense
to
do
this
when
the
chosen
Kendrell
pit
is
not
host
a
host
or
hostess.
Something
voice
and
video
conference
may
make
sense
to
call
this
method
when
joining
a
session
or
a
room.
But
you
only
intend
to
listen.
You
don't
intend
to
share
you
come
in
joining
this
conference,
but
not
you
know
not
going
to
present
anything
and
for
data
transmission.
This
could
be
used
when,
for
example,
when
having
selected
a
file
to
sent
to
the
other
peer.
M
So
as
a
nice
side
effect
of
this
API
process
that
implicitly
grant
direct
connection
permission
would
now
also
grant.
It
would
not
also
trigger
the
the
connection
of
gradable
event,
so
that
would
be
a
clear
indication
to
the
application
that
it
can
do
a
nice
restart
and
they
would
actually
do
have
a
positive
effect
or
it
could
be,
could
have
a
positive
effect.
The
connection.
M
Yeah
and
also
there
is
no
don't
gripe
mechanism
in
this
progress
so
because
doesn't
really
make
sense
to
ground
down
great
anything.
If
you
have
already
leaked
basically
leaked
their
hosts
candidates
because
they
are
already
known
at
this
point
of
the
application.
So
don't
grading
will
only
be
effective
for
future
peer
connections.
Okay,
next
slide,
please.
M
So
the
the
probably
the
the
most
pressing
issue
here
is:
how
is
this
being
reflected
in
the
user
interface?
How
does
the
user
experience
look
like
and,
like
I
said,
this
API
is
tailored
to
encourage
the
direct
connection
permission
being
granted
without
having
to
rely
on
the
prompt.
So
this
gives
you
eye
designers
room
for
experimentation
on
the
right
side.
We
see
an
example.
M
How
I
would
envision
it
for
sound
will
be
used
in
Firefox,
which
is
something
I
talked
about
with
young
Eva,
so
it
could
be,
for
example,
move
to
the
side
panel,
and
then
there
would
be
an
icon
representing
re.
You
could
activate.
You
could
grant
a
permission
here
to
have
a
more
direct
connection
and
then
there's
a
small
question
mark
that
could,
for
example,
explain
what
is
a
direct
connection.
M
A
You
have
a
static
method
on
an
event
which
kind
of
separate
separates
the
the
thing
into
two
piece:
two
pieces
right.
So
why?
And
in
particular
you
use
of
static
means
that
you
are
assuming
that
you
have
exactly
the
same
very
like
connection
interest
for
all
for
all
pair
connections
inside
inside
the
context.
It's.
M
A
peer
connection
is
something
reflected
in
the
UI,
so
so
it
wouldn't
be
clear
which
peer
connection
am
I,
know
granting
a
direct
connection,
a
direct
connection
permission
and
the
event
is
about
I
mean
the
alternative
would
have
been
to
make
it
a
promise
and
I
have
chosen
to
not
do
this.
After
long
discussion
with
ya
neva
to
support
lose
support,
this
not
being
a
prompt,
so
they
should
really
encourage
implementers
to
not
make
it
a
prompt
but
to
me
to
experiment
making
it
somewhere,
something
that
isn't
that.
M
How
would
a
call
it
doesn't
have
a
direct
effect,
for
example,
it
could
be
that
this
thing
yeah
shown
on
the
right.
The
example
is
always
visible
and
message
doesn't
do
anything
in
in
the
in
the
browser,
because
the
browser
always
shows
it
it's.
You
know
it's,
it's
always
on
the
side,
but
it
could
be
an
indication
for
the
browser
to
you
know
show
this
icon
on
the
sides
to
visualize
that
there
is
some
something
in
the
user
can
do
something
the
user
can
grant
may
be.
Young
Eva
can
also
comment
on
that.
I
I
think
the
makes
a
good
point
that
we
could
make
the
method
part
of
a
peer
connection
object
and
then
maybe
the
event
would
only
fire
for
that
peer
connection.
I
think
the
point
of
a
static
method
was
that
this
is
really
about
permission.
So
it
applies
to
the
whole
page,
and
you
might
want
to
call
this
before
you
create
a
peer
connection
object.
I
If
you
have
more
trust,
if
more
Trust
has
identified,
you
can
get
an
event
fired
on
you
that
you
can
then
do
a
nice
restart
and
improve
your
connection.
So
I
think
we
can
always
work
on
the
details
from
the
PR,
but
you
know
there's
a
general
sense
of
the
room.
Do
people
think
this
is
a
good
way
to
go
this.
G
That's
that
I
think
it's
worth.
We
should
tackle
in
Murdoch's
env,
not
not
now
the
idea
of
being
burnt,
and
so
on
that
that's
nice.
If
we
find
good
heuristics
that
are
good
cases
where
we
are
actually
changing
dynamically
during
the
lifetime
of
a
page.
We
we
don't
have
that
right
now
in
browser
implementations,
except
for
get
user
media
and
applications
can
already
do
that.
So
I
think
we
should
live.
Please
show
your
page
there
and
try
to
work.
B
A
The
reason
I'm
asking
is
that,
if
I
remember
the
mission
spec
correctly,
which
is
far
from
obvious,
then
you
already
have
the
ability
to
register
for
a
notification
when
permission
changes,
I
forget
exactly
what
well
what
is
called
but
I.
Think
that
when
you
get
when
you've,
you
flipped
I
connections
from
from
this
allowed
to
allowed,
you
are
able
to
get
to
get
an
event,
so
that
part
of
the
spec
might
actually
not
be
not
need
to
be
an
if
it
ties
to
the
permission.
Spec.
G
If
you
implicitly
grant
direct
connection
whether
in
to
deny
direct
connection
chronicles,
does
it
mean
that
you
will
know
provide
any
candidates
at
all,
so
is
it
like
something
like
disabling
the
whole,
whoever
TCP
connection
feature
or
not?
Now
a
lot
of
things
like
that
that
were
that
we
need
to
define
and
discuss
and
yeah
it's
it's
really
to
me.
It's
really
exploratory
work
right
now,
I
think.
I
M
I
G
L
F
Think
one
thing
we
maybe
could
do
in
the
timescale
coming
back
to
something
UN
said
was
that
in
theory
we
could
be
gathering
some
metrics
and
heuristics
about
like
where
this
might
have
helped
and
I
don't
know
if,
if
any
of
the
browser
vendors
are
in
a
position
to
to
generate
stats
or
comments
on
that,
but
I
think
it
would
be
read
that
would
be
a
nice
use
of
time
is
to
get
a
sense
of
of
just
how
many
times
this
would
have
helped.
Is
that
something
that
we
think
we
could
generate
somehow.
M
B
M
Basically,
I
filed
these
before
I
started
working
on
the
PR,
so
I
thought
this
would
be
useful
for
every
CPC,
because
the
connection
upgradeable
event
is
something
that
is
currently
missing.
The
application
doesn't
know
when
it
can
do
a
nice,
we
start,
and
it
would
actually
it
may
benefit
from
it.
So
this
is
what
the
connection
upgradeable
event
is
is
about,
and
then
there,
of
course,
is
a
method
that
would
provide
it
in
any
case
neutral
light.
B
M
A
B
I
B
What
I'm
thinking
is
and
I
don't
know
how
it
works
for
the
IGF
meeting,
but
we
can
do
one
and
another
interim
in
July.
Okay,
so
probably
we
all
sent
out
a
doodle
right
away,
so
we
can
have
this
be
the
focus
of
the
next
interim
emigrate:
okay,
early
July,
yeah
early
July,
okay,
good!
Thank
you!
Everybody
all.
