►
From YouTube: Antrea Community Meeting 07/19/2021
Description
Antrea Community Meeting, July 19th 2021
A
A
B
First,
the
motivation,
the
the
target
of
this
design
is
to
remove
the
kuby
proxy.
If,
if
the
copy
proxy
is
removed,
a
lot
of
cpu
circles
and
memories
can
be
sealed,
we
need
we
don't
need
to
handle.
A
lot
of
applicable
interest
is
that
we
may
account
a
lot
of
os
flows
in
current
design.
The
service
can
be
only
supported
fully
when
the
client
is
from
the
port.
If
the
client
is
from
remote
host,
android
proxy
has
to
need
the
help
of
kubi
proxy
to
redirect
the
service
traffic
into
entry
gateway.
B
B
B
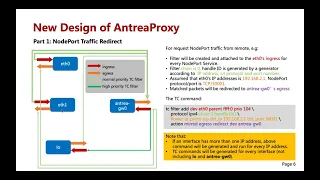
What
here
is
a
new
design?
Okay,
I'll
introduce
the
new
design
in
two
parts.
The
first
part
is
the
linux
is
how
to
redirect
remote
and
localhost
service
traffic
to
actually
gateway
directly
without
passing
through
and
to
proxy,
and
how
to
make
the
response.
Traffic
back
to
the
client
and
the
new
design
used
linux
tc
to
handle
the
node
power
and
load
balance
traffic
from
remote
clients
and
for
for
non-power
traffic
from
localhost
link.
Tc
is
used
for
load
balance.
Traffic
from
local
hosts
and
new
design
use
can
leave
roots
to
handle
it.
B
B
Oh,
oh
sorry,
and
this
part
this
the
second
part,
and
the
second
part
is
os
pipeline.
I
think
this
part
can
be
used
in
links
as
well
as
windows,
and
there
are
three
main
reasons:
first,
how
to
do
smart
for
source
traffic,
the
second
one,
how
to
handle
the
destination
mac
address
of
the
response,
traffic
and
the
third
one
compatible
with
the
lag
city
plan.
B
I'll
introduce
the
new
design,
the
first
part
take
notepad,
for
example,
okay
for
request,
notepad
track
notepad
traffic
from
remote
client.
First,
a
filter
will
create
another
test
to
the
field.
Take
it
as
an
eagle
example
we'll
attach
the
two
eth0s
in
grass
for
every
node
pulsar
is
here
we
take
so
and
one
and
that's
the
definition
part
by
default.
The
filter
will
be
will
be
put
on
train
0..
The
handle
id
is
generated
by
generator
according
to
notepad
ip
address
layer,
4
protocol
and
the
node
part
number.
B
B
B
B
B
B
B
Okay,
that's
for
sub
chain
is
where
the
second
layer
filters
locate
one
node
pod
is
created
the
filter.
The
filter
will
be
created
and
attached
to
the
sub
chain.
The
filter
matches
the
packets
according
to
the
to
the
source.
Part
under
the
action
is
to
redirect
the
mass
response
traffic
to
the
interface,
where
it's
requested
traffic
from
if
the
substring
is
full
go
back.
B
B
B
B
B
Okay,
next
for
response
traffic
for
response
traffic,
it
has
two
directions:
one
for
actually
conjugate
wave.
This
traffic
is
traffic.
This
request
is
from
kubernetes
node
and
the
one
for
default.
Router
interface,
this
request
the
traffic
is
from
a
remote
client
and
then
we
should
add
a
higher
priority
filter
to
match
to
match.
The
traffic
would
request
the
traffic
from
country
gateway,
and
then
we
can
bypass
bypass
the
traffic
back
to
and
to
get
away
and
the
left
traffic
traffic
is
for
the
photo
before
the
road.
B
Next
for
cluster
cluster
ip
for
cluster
ip
is
only
used.
It's
only.
This
client
can
be
from
part
of
kubernetes
node
here
used
for
kubernetes
node,
world
class,
ips
drive,
class
ip
is
created,
and
if
there
is
no
a
cluster
ip
so
far,
ok,
then
the
unlinked
router
will
be
created
for
the
class
type.
Another
prefix
is
32,
that's
the
longest
one
longest
mask
for
root.
Okay!
Well
then,
unlike
this
one
add
a
new
add
a
new
class
ip,
then
a
new
unlinked
router
will
be
generated
and
we
can
replace
the
old
one.
B
B
B
B
B
B
B
B
B
B
B
B
B
B
This
data
is
reply,
the
track
tracker
and
the
service
traffic
it
will
be.
The
master
package
will
be
sent
to
70
75
the
70
file.
The
70
file
is
a
new
username
table,
and
this
table
this
table
is
how
mentioned
this
table
before
a
table
certified
and
the
generated
learn
flow
is
located
at
the
table.
70
file,
the
first,
the
first
packet
of
a
remote
client,
will
trigger
a
flow
at
the
table.
70,
and
this
flow
is
used
to
set
destination.
Mac,
address,
output,
interface
and
output,
output.
B
B
B
B
B
B
Okay,
the
next
for
her
for
helping
traffic,
the
the
astronaut
does
not
append
to
as
the
happy
address
of
astronaut
can't
be
attributed
to
it,
because
the
anti-gateway
will
drop
drop
will
drop
the
package
if
its
destination
is
so.
This
source
address
should
be
a
different
one.
Here
we
we
use
our
watch
service
versus
ip
address
to
to
do
to
do
it.
B
B
A
D
B
Yes,
but
how
investigated
some
possible?
Actually,
I
think
I
think
it
may
it's
not
so
so
worthy
to
do
it
I
can
I
can.
I
can
use
a
link
to
tc
filter
to
do
some
tool
to
add
a
mark
to
this
kind
of
mark,
but
that
will
introduce
another
drone
to
tc
filters.
The
current
design
of
the
currently
designed
for
tc
filters
is
stateless
and
that
if
the
distributors
introduce
stateful,
I
think
that
will
that
will
if
and
that
that
will
make
a
effect
effect
to
the
performance.
E
B
B
B
C
E
E
B
C
B
C
B
C
B
F
I
do
have
a
quick
question
if
cornell
doesn't
mind,
I'm
looking
at
the
the
road
number
17
and
18
18
here
I
was
not
noticing
that
if
the
client
part
is
from
the
remote
node
and
depending
on
the
external
traffic
policy,
we
may
or
may
not
need
s-nets
in
two
different
cases.
I'm
I
might
miss
when
you
present
it,
but
could
you
explain
a
little
bit
on
why
that
is
the
case.
F
A
A
A
Time,
okay,
I
have
two
very
simple
questions,
mostly
as
usual
because
of
my
ignorance,
so
considering
these
few
use
cases
that
at
the
moment
we
are
not
supporting,
is
this
affecting
in
any
way
conformance
tests?
I
mean:
is
there
any
conformance
test
that
explicitly
verifies
if
no
deporter
node
for
traffic
works
with
external
traffic
policy,
local
in
our
cases
or
is
conformant
conformance
tests
are
still
passing
fine.
B
A
Our
load
balancer,
no
sorry,
I
meant
something
different
I
mean.
If
now
we
replace
q
proxy,
we
completely
proceed
with
entria
proxy
will
the
conformance
test,
like
you
know,
the
cncf
conformance
conformance
tests
that
we
already
executed
in
our
ci
will
they'll
still
pass,
or
will
there
be
any
conformance
tests?
That
might
start
not
passing
because
of
these
use
cases
that
we
are
not
supporting
at
the
moment
or.
B
A
B
B
B
A
A
B
A
Yes,
yes,
I
mean
you,
you
mentioned
that
there
were
some
for
ipv6.
You
found
some
upstream
issues
that
were
preventing
you
for
implementing
design
for
defining
a
solution
for
ipv6.
I
was
just
curious
if
those
issues
were
already
tracked
in
the
kubernetes
community
or
whether
these
there
was
no
one.
Looking
at
those
issues
at
the
moment.
B
B
A
A
B
The
next
one
is
how
to
remove
how
to
remove
cookie
proxy
totally.
The
current
design
is
that
we
use
the
endpoint
of
kuber
api
server
to
fast,
fast,
faster
service
or
other
other
information
from
kobe
api
server,
and
this
is
not.
This
is
not
perfect
because
reflects
the
information
from
only
the
api
server.
B
A
A
A
A
And
it
appears
that
it's
really
all
for
today,
so
I
would
like
to
thank
again
hong
leon
for
this
presentation.
Thank
again,
everyone
for
attending
this
meeting
and
and
well.
The
only
thing
left
to
do
is
to
is
to
say,
wish
everyone
a
good
afternoon
a
good
evening
or
a
good
day
and
we'll
talk
again,
we'll
meet
again
in
two
weeks
time,
thanks
everyone
for
joining
and
have
a
good
one
thanks.
