►
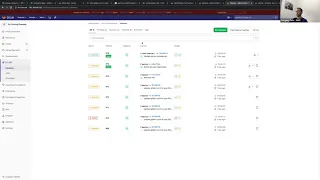
From YouTube: Coverage Guided Fuzzing Demo
Description
A early walk through of coverage guided fuzzing
A
Alright,
so
here
we
have
a
little
fuzzy
example
where
we
have
I
will
walk
again
from
from
the
beginning
from
the
beginning.
So
we
have
a
box
again
through
the
beginning
and
I
show
also
the
the
project
itself
and
the
false
targets.
David
I
think
you
saw
saw
it
as
well,
but
I'll
just
start
from
the
beginning,
so
I'll
walk
through
this
quickly.
A
A
A
A
Okay,
so
this
is
standard
github
CI
ya
know
so,
as
we
include
as
we
are
using
any
other
security
feature
and
give
them,
including
the
template
like
including
SAS,
template
or
desc.
We
included
coverage
fuzzing
channel
and
once
we
include
that
we
need
to
yeah
once
we
include
that.
Actually,
this
adds
yeah
sorry.
So
we
need
to
include
that
and
we
need
to
add
another
stage,
fuzzing
stage
which
will
be,
which
will
will
run
after
tests
stage
and
for
each
pausing
function
fast
test.
A
B
A
A
A
Here
we
can
use
it
any
image
that
we
use
for
from
the
build
project,
but
we
are
hosting
several
handy
images
at
this
wrapper.
This
is
public
repo.
It
does
not
hold
any
source
code,
it
just
holds
releases
of
our
CLI
to
like
binary
releases
and
also
it
holds
any
quite
a
few
handy,
docker
images
with
which
includes
several
fuzzing
engines,
because
it
takes
a
lot
of
steps
to
usually
to
install
like
leaked
files
are
all
LLVM,
so
either
the
user
has
those
images
already
or
if
you
can
use
our
images.
C
A
A
A
A
So
here
we
have,
we
also
have
the
version
of
the
father,
so
we
can,
in
the
future,
will
be
able
to
also
to
reproduce
everything
again.
So
here
we
have
the
just
the
test
cases
that
were
generated-
and
here
we
have
the
crashes
the
crash
horse
is
so
I
think
this
is
something
that
you
already
saw
in
the
previous
version,
and
now
we
have
balls
because
we
have
the
GL
coverage
report
as
an
output,
and
we
so
now
we
support
it
on
the
get
love
back
and
rails.
So
this
is
also
parsed
in
this
screen.
A
We
have
a
new
report,
type
of
coverage
fuzzing.
So
again,
this
is
just
initial
logic
that
we
added
in
the
merge
request
that
I
talked
about
last
meeting
and
we
will
add
more
more
details
here.
But
the
current
current
detail
screen
and
how
the
j-jason
covered
in
Jason's
report
is,
is
a
parse,
so
we
can
see
the
scanner
provided
it
slipped
buzzer.
A
Maybe
we
need
to
change
it
to
a
more
accurate,
because
this
is
like
Wasley
father
and
not
see
Sifu
school
sleep
buzzer,
the
scanner
type
is
coverage
fuzzing
severity,
our
CLI
else
also
to
classify
severity
for
some
crashes.
I
didn't
pour
this
part
of
the
code
yet,
but
I'll
do
that
in
the
next
version,
so
we'll
have
also
severity
for
some
of
the
crashes.
We
have
a
crash
state
here
and
we
have
the
also
the
crash
type,
which
is
index
south
of
French,
which
is
exactly
the
the
bug
that
that
happened
in
our
example.
A
To
the
like,
artifact
screens,
we
have
also
they
will
have
also
the
button
here
for
the
MVC,
which
is
available,
and
some
of
the
issues
for
the
MVC
will
have
a
button
here,
so
so
I
need
the
user
can
download
the
whole
artifacts
in
one
click
and
I
think
in
the
future.
Currently,
currently,
we
only
parse
the
report,
but
in
the
next
larger
quest
in
the
next
version.
A
A
A
A
I'll
push
this
change
is
that
what
we
decided
is
that
in
the
regression
we
will
also
run
short,
fuzzing
Accession,
so
actually
it
would
also
find
the
same
crash
and
unless,
unless
we
fix
I'll
open
another
I'll
push
this
change
and
open
another
of
marriage
requests
with
with
the
fix,
so
you
will
see
that
there
is
no.
You
know
yeah.
A
C
C
D
Yeah,
that
was
the
question.
Is
that
it's
good
to
see
it
on
the
pipeline
view,
but
usually
people
would
look
at
it
here
right,
because
you've
opened
up
a
merge
request.
You
push
code
into
Co
got
scan,
it
says,
need
to
be
there
for
next
week's
customer
advisory
board.
It's
more
of
a
question
that
can
I
go
there
to
show
that
if
it's
there
and
it
sounds
like
what
you're
saying
Seth
is
that
implementation
is
TBD,
so
it
shows
up
in
the
security
merge
request.
Widget,
that's
fair.
C
D
What
they're
doing
is
they're
updating
it
to
be
more
accurate,
like
did
displaying?
What
is
the
actual
state
so
like
in
the
case
of
the
video
that
Marcel
made
is
there's
like
200
Varner
abilities
detected,
but
really
there's
not
200.
That
count
includes
everything
else
is
it
has
been
previously
fixed,
but
they
never
merged
down
to
two
master.
So
it
couldn't
tell
you
the
delta
to
say
there
were
only
two
new
ones.
Instead
of
two
hundred
mm-hmm.
C
D
D
B
We
get
the
yeah
once
we
get
the
buzz
findings,
integrate
with
sandal
and
vulnerabilities
I,
believe
the
widget
information
will
start
being
displayed
because
that
widget
is
being
driven
off
of
all
the
stand
and
vulnerabilities
is
my
understanding,
so
it
should
show
up
as
part
of
the
widget
and
the
security
dashboard
all
at
the
same
time.
Okay,
but
that's
the
part
we
haven't
done
yet
yeah.
C
D
D
D
A
D
I
just
say
it's
a
Sam's
positioning
in
his
upcoming
blog,
the
settings
put
on
the
home
on
the
Direction
page
really
talks
about
like
this
finds
things.
Traditional
scanners,
don't
fine,
which
I
think
we
all
agree
is
the
case
of
fuzzing,
but
to
kind
of
show
that
in
a
quick
demo
to
someone,
if
we
add
in
the
SAS
template
SAS
would
run
I,
don't
think
SAS
is
gonna,
find
the
error
that
you're
finding
of
getting
in
the
names
like
you
can
see
your
access
and
find
it.
A
Okay
sounds
good,
okay,
yeah
and
now
so
sander
I
replicated
in
the
environment
and
they
move
the
GCP
demo.
So
long
I'll
send
the
link
in
the
channel
as
well
together.
Then
then,
let
me
know
either
if
you
want
to
record
it
with
with
your
own
rhythm
and
voice,
then
hey.
If
you
want
to
like
me
to
record
it.
