►
From YouTube: IETF103-HOSTSPEAKERSERIES-20181108-1245
Description
HOSTSPEAKERSERIES meeting session at IETF103
2018/11/08 1245
https://datatracker.ietf.org/meeting/103/proceedings/
A
Okay,
so
it's
almost
time,
thank
you,
everyone
for
coming
we're
going
to
start
the
technical
technology
session.
Today
we
are
very
fortunate
to
get
our
chief
architect
for
our
carrier
business
unit
to
talk
about
technology
and
how
he
has
been
instrumental
in
bringing
our
revenue
to
pass
the
hundred
billion
mark
last
year
so
we're.
Fortunately,
that's
welcome
to
Utah.
B
Good
afternoon,
everyone
so
and
I'm
aware
eagle-eyed
to
have
opportunity
to
make
a
prize
and
prize
in
the
presentation
about
our
ideas
and
some
practice
in
network
architecture.
Evolution
also
because
response
for
the
product
and
the
solution,
architects
design
so
always
think
we
feel
during
in
the
recent
years.
We
the
network
world,
faced
a
great
challenge,
so
I
think
I
hope
my
sharing
will
be
will
be
benefit
and
helpful
for
ITF
to
to
let
us
to
face
the
challenge
together.
So,
okay,
that
I
begin
so.
B
During
during
the
past,
several
decades,
IETF
and
engineering
made
a
great
contribution
for
the
networking
in
the
world.
So
currently
the
IP
network
has
already
covered
almost
covered
all
of
the
world
and
become
very
important
infrastructure
for
the
information
world.
So
more
and
more
application
and
the
services
rely
on
the
network
infrastructure
such
as
a
cloud
in
the
night
and
the
in
the
future,
maybe
the
IOT
so
on
a
country.
So
this
application
rely
on
network
on
our
country,
so
the
network
faced
the
great
challenges
for
new
requirement,
so
so
full
of
I
P
Network.
B
B
B
So
this
means,
but
at
the
same
time
the
revenue
increase
is
very
slow,
so
list
means
it
is
difficult
for
carrier
to
invest
continuously
for
the
network
list,
the
first.
So
the
reason
for
for
the
all
pacts
increase
I
always
think,
maybe
maybe
the
maybe
the
low
maintenance
efficiency,
because
we
think
is
the
major
reason,
is
the
current
reason
that
telecom
network
maintenance
depends
on
the
human
experience
where
heavily
so
this
list
is
the
creature
challenge
so
how
to
solve
this
child
challenges.
B
I
think
we
need
to
think
about
system
architecture
in
our
nation,
so
we
we,
we
think
of
mom
autonomous
network,
will
be
the
future
of
the
network
architect
so
before
to
think
about
autonomous
Network,
where
we
make
a
deep
starting
about
the
current
network
of
OTT
and
telco
network,
so
the
right
side,
other
the
left
side.
The
left
center
is
a
typical
as
a
typical
cloud
network
in
front
architect.
So
we,
the
right
side,
is
a
typical
network
architecture
of
the
telco.
B
B
So
the
services
is
realized
by
the
software
it
is
easy
to
is,
it
is
easy
to
deploy
with
is
the
change
of
the
workload
and
application,
so
at
the
same,
at
the
same
time,
there
is
a
very
clearly
boundary
of
cloud
services
at
a
network,
operation
layer
so
and
all
of
this
process
are
realized
by
the
software
to
realize
the
automation,
but
for
the
can
call
telco
network.
So
currently
the
transport
and
and
natural
services
in
general
converged
in
dedicated
hardware,
so
it
is
difficult
to
get
up
for
for
network
transport
and
network
services
independently.
B
We
will,
as
we
know
when,
when
we
developed
the
product,
we
know
the
network
services
and
the
network
transport
rely
on
different
process.
Different
hardware
features,
so
within
one
boss,
it
is
difficult
to
to
scale
up
independently,
so
the
second,
the
second
difference
is
so
currently
for
katako
network.
There
are
services
and
my
current
system
a
sterile
system
so
understood.
For
example,
there
are
a
lot
of
network
services
and
the
management
system
for
access
network
for
metro
network
for
for
for,
for
example,
for
the
core
network.
B
So,
at
the
same
time
as
a
boundary
of
the
network,
services
and
network
operation
is
not
very
clear,
so
in
some
area
maybe
they
realize
that
the
service
system
will
talk
with
the
device
directly,
for
example,
maybe
some
use
case
some
OSS
system
talks
a
success
note
directly
so,
but
for
other
for
more
for
more,
for
other
scenario
may
be
the
service.
The
services
platform
will
talk
of
its
network
with
with
the
operation
team
with
the
people
so
here,
so
we,
this
list
means
a
lot
of
work
should
be
done
by
menu
by
people.
B
B
The
over
picture
over
the
value
of
the
goal
of
the
network,
so
I
think
the
the
final
target
is
increased,
the
revenue
and
the
decreased
TCO,
but
here
there
are
three
three
major
value
of
provocation,
so
that
is
that
is,
that
is
a
better
customer
experience,
a
higher
operation,
efficiency
and
open
the
programmability
for
operation
vision.
I
think
zero
torch
operation
is
a
target,
so
maybe
in
the
future
we
need
as
sofala
for
the
hurtful
target.
B
We
need
to
make
the
mark
easy
and
simple
and
the
we
need
to
solve
the
challenge
of
continuously
service
provisioning
for
the
network.
Currently,
it
is
difficult
to
continues
country
the
delivery
of
the
service
on
network
in
general
for
talent,
telco
carrier.
They
have
a
change
window
for
the
network
modification
and
another.
Another
challenge
is
how
to
make
mitigate,
make
rotation
from
the
legacy
and
network,
so
in
January.
If
currently,
for
the
customer
follow
a
telco
players.
B
B
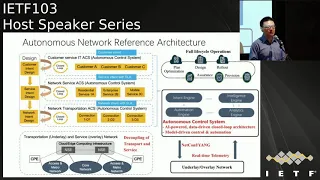
So
this
is
a
general
idea
of
the
autonomous
networks,
reference
architecture,
so
the
right
side.
So
for
the
network
itself,
we
think
maybe
we
think.
Maybe
we
need
to
be
copying.
The
transport
and
network
services
function
completely
so
because
so
for
network
transport,
they
are
net.
Network
transport
is
focused
answer,
not
the
bandwidth
increase,
the
bandwidth
utilization
and
the
SRA
guaranteed,
but
for
our
so
this
means
it's
a
transport
made
a
focused
on
the
physical
infrastructure,
but
for
network
services.
In
fact,
it
focused
on
the
user
and
the
subscriber
itself
an
application.
B
So
this
means
for
user
and
the
for
server
for
user
for
tenant.
The
most
important
feature
is:
do
you?
Could
you
deploy
the
services,
charity,
flexible,
yeah
and
have
a
have
a
boot
and
they
can
guarantee
the
service.
Experience
looks
a
customer
we
can
found.
The
logic
is
different
for
a
transport
and
under
services,
so
listen
to
why
we
sing
wheezing
in
the
future.
B
The
network,
the
copying
of
transport
and
the
services
are
very
important
and
maybe
in
a
future,
based
on
the
based
on
the
hardware
and
silicon
technology,
progress
racing,
maybe
for
the
transport
network,
it
will
be
more
reliant
on
the
on
the
dedicate
hardware
in
the
chip
side,
but
for
the
network
services.
It's
more
rely
on
the
software
based
on
the
general-purpose
computing
capability.
So
this
is
the
fuller,
fuller
network,
hardware
or
network
itself
for
a
network
services
and
the
management
system.
We
think.
B
System
so-
and
it's
very
important,
so
this
means
we
need.
We
need
to
establish
a
common
platform
for
network
operation
and
a
common
network
service
platform
for
services,
so
in
one
hand
we
can-
and
we
can
so
based
on
its
platform.
I
think
it
is
easy
to.
Maybe
it
is
benefited
to
to
deploy
the
network
transport
and
a
network
services
end
to
end
and
all
of
this
and
all
of
this
system
should
be,
should
execute
by
software.
B
So
this
is
a
left-side,
so
how
to
realize
this
network
management
and
a
network
services
platform
recalls
autonomous
control
system.
The
right
side
is
the
general
idea
of
less
octant
I.
Think
we've
seen
this.
This
ACL
system
should
be
consists
of
the
four
major
engines.
The
intended
engine,
autonomy,
automation,
automation,
engine
elastic
engine
and
intelligent
engine
and
all
of
search
engine
should
be
work.
Work
in
the
closed
loop
model.
This
musica
it
can
realize
our
Thomas
in
each
layer.
B
B
It
realized
very
a
decoupling
between
the
network
transport
and
the
network
services,
but
in
general
they
have
a
how
to
say
it
can
it
cannot
realize,
though
agnostic
so
for
examples
of
the
excellent
so
so
this
is
the
way
we
think.
Maybe
we
currently
are
we
full
of
that
protocol
evolution.
We
think,
maybe
is
the
four
winds.
Three
principles
are
important.
The
first
is
the
natural
service,
air
transportation
technology
ignore
Aeronautics
majorly
and
it
can
be
replaced
independently
means
may
be
replaced
the
whole
evolution
independently.
B
The
second
is
very
various
transportation,
which
different
technology
can
be
choose
for.
The
specific
service
later
I
will
share
a
use
case
of,
as
divine
is
the
typical
a
scenario
for
a
second.
As
for
a
second
principle
and
a
third
days,
multiple
candle
services
can
be
supported
by
responding
transporting
transported
technology.
I
think
we've
seen.
Maybe
this
this
principle
are
very
important
for
a
protocol
evolution.
B
For
a
transport
for
a
transport
layer-
or
we
think,
maybe
in
the
future,
the
the
target
of
the
of
the
of
the
list
layer
how
to
guarantee
the
capacity
girls
and
the
resource
utilization
this
reasonable
cost.
The
second
is
how
to
visibility
and
a
guarantee
ice
array
of
services.
The
third
is
how
to
achieve
always
on
on
delay.
So.
B
Places
this
is
to
realize
to
retrieve
it
to
realize
this
target
we
need
to
think
about.
We
think
some
some
something
need
to
sing
us
think
about
the
first.
We
need
to
simplify
the
protocol
system
and
to
realize
two
supports
and
to
end
our
babies
next
slide.
Okay,
so
this
slide
show
some
so
our
some
ideas
about
about
the
protocol
evolution.
The
first
days
are
similar
similes
so
because,
currently
the
services
other
the
transportation
function
realized
rely
on
the
hop
hop
by
home,
configuration
and
and
then
later.
B
This
is
why
it
is
difficult
for
for
telco
to
pro
Wilders
the
the
services
to
the
customer
very
quickly,
and
the
second
is
the
currently.
The
protocol
is
very
complex,
so
it
is
difficult
to
maintenance
and
and
also
difficult
to
realize,
the
automation,
because
if
we
realize
the
automation
Network,
if
we
have
two
theories,
all
kinds
of
the
protocol
and
all
cancels
a
lot
of
scenario,
it
is
very
difficult
so
and
another
so
idea.
I
think
we
are
wasting.
B
Maybe
this
technology
can
be
used
for
follow
all
kinds
of
a
scenario
sooner
from
access
to
make
sure
and
to
call
why
we
think
about
think
about
this,
because
we
think
currently,
the
telecom
network
is
how
to
say,
is
a
hierarchy
and
layer,
aggregation
network
from
access
measure
and
to
call
and
they
and
the
connect
to
the
internet.
But
in
the
future
we
think
with
cloud
with
a
cloud
become
more
and
more
popular
and
recently
edge
computing.
It
is
also
become
aware
or
become
more
popular.
We
seen
in
the
future.
B
The
underlay
transport
network
should
be
a
basic
infrastructure
to
connect
his
Marty
cloud.
This
means
the
the
traffic
traffic
pattern
will
be
changed
and
the
network,
how
the
same
just
like
fabric,
can
support
all
kinds
of
traffic
among
the
dinner
cloud
cloud,
so
listen
to
the
what
we've
seen,
maybe
in
the
future.
The
idea
is
that
the
underlay
transport
transport
transport
network
should
be
a
flight
in
network
can
provide
very
big
bandwidth
and
the
scale
up
or
scale
out
very
easily.
This
is
the
basic
idea
to
think
about
transport
transport
network
and
follow.
Follow
overlay.
B
Network
I
will
share
two
use
cases.
We
are
to
use
his
it
to
to
understand
the
requirement
of
this
network.
The
first
one
is
to
is
to
establish
the
cloud-based
overlay
and
network
for
the
customer,
so
we
we
we
did
during
the
past
two
years.
We
developed
our
way
to
analyst
network
based
on
our
public
cloud.
Visa
cooperative
is
a
France
Telecom,
their
telecom
and
China
Telecom.
So
the
idea
is,
we
hope
to
deploy.
B
The
target
is
for
the
customer
one
point:
access
for
a
global
network.
This
means,
if
the
customer
access
network
we
can,
we
can
deploy
so
were
to
virtualized
network
based
on
the
cloud
infrastructure
and
to
realize
the
globe
Global
connection
for
the
customer
work
quickly.
So
listen!
It
is
a
second,
so
service,
provisioning
in
minutes
and
adult
encourages
in
second.
Currently,
if
you
just
rely
on
telco
cloth,
it
is
difficult
to
realize
its
target.
So
this
is
a
this
is
what
what
we
are.
This
is
the
target
weight
developed.
B
This
is
network,
so,
besides
the
traditional
way
knife
such
as
a
DVR
and
every
piece,
the
Gateway
we
we
added
some
to
a
new
being
us
one
is
a
VPN
gateway.
Well,
another
is
X
gateway
between
gateway
is
used
to
as
access
point
to
all
kinds
of
a
tool
to
the
customer,
while
the
wells
are
different
to
technology,
such
as
the
leased
line
mayor
peers,
if
you
know,
is
a
clip
here
so
as
gateway
is
used
to
interconnect
waste.
B
This
is
a
different,
different
datacenter.
So
this
is
the
basic
solution
follow
for
the
overlay
virtualized
network.
So
when
we
develop
the
lease
it
way
now
here
is
there
is
a
more
detailed
information
about
how
to
realize
the
services
requirement
so
to
full
a
customer
access
the
access
its
center
and
access.
They
are
their
own
VPC
in
a
coalition
or
in
a
remote
position
and
based
on
this
network.
It
is
also
can
support
the
customer
connect
to
the
network
welder
cloud.
B
So,
but
when
we
develop
today's
component,
such
as
the
week
III
and
ask
it
we
we've,
we
found
a
lot
of
challenges,
never
faced
before.
For
example,
the
first
use
of
capacity
so
because
this
is
it
we
and
the
week
we
will
connect
a
lot
of
customer.
So
the
here
the
capacity
is
not
as
a
challenge
in
not
it's
not
the
boundaries,
it
is
control.
B
B
So
this
means
and
at
same
time
we
at
the
same
time
we
need
to
add
a
feature
easily,
because
the
way
we
were
supposed
to
I
psi,
we
were
suppose
I
said
VP
and
we
were
supposed
MPs
and
in
future
we
need
to
add
some
more
and
more
feature.
This
is
a
second
so
because
of
the
because
of
the
because
of
the
the
capacity
and
the
performance
requirement
or
the
traditional
network
network
product
available.
B
Reliability
cannot
satisfy
the
traditional
networks,
justice
supposed
to
one
plus
one
control
plan
and
as
a
backup,
but
waiting
to
support
this
natural
wasting
m2m
model
should
be
supported.
So
there
are
a
lot
of
technology
should
be
should
be
should
be
solved.
Clearly
is
a
typical
example
is,
as
we
know
currently,
the
PGP
can
actually
rely
on
the
P
TCP,
but
when
we,
when
we
realize
that
when
we
realize
the
network
function
on
a
server,
we
know
the
Arabic,
the
reliability
of
the
server
is
not
fair
in
January.
B
Server
will
be,
will
be
done
so
currently
do
you
for
the
BGP
rely
on
the
TCP.
It
is
a
great
challenge
to
realize
the
high
availability,
for
example,
and
to
end
a
model
for
control
plan
soul.
It
means
we
need
to
win
you
to
run
several
control
plan
at
the
same
time,
and
maybe
you
and
that
may
be
select-
is
the
best
best
result
of
different
control
plan
and
in
the
future
we
hope
we
can
upgrade
the
the
control
plan.
How
to
say.
B
Individually
and
maybe
raising
the
different
version
of
the
software,
so
listen,
all
of
this
feature
rely
on
the
BGP
connection.
The
robust
of
each
bit
connection
may
be.
Currently
we
use
some
software
technology
of
our
complex
software
so
for
technology
to
solve
this
issue,
but
we
think,
maybe,
if
we
think
about
the
the
the
evolution
look
at
the
BGP,
maybe
is
it
better.
So
here
is
just
an
example
full
of
full
of
a
mess.
B
That's
why
so
another
another
use,
kisser
Estevan
so
currently,
as
the
divine
is
a
very
hot
topic
in
the
industry,
so
the
I
think
it.
In
fact,
it
is
the
overlay
network
based
on
the
based
on
the
internet
and
and
maybe
based
on
at
the
same
time,
based
on
static
or
leased
line
network
for
enterprise.
So
well
when
we
develop
a
solution
and
cooperate
with
Teleco
customer,
we
found
as
a
following
following
requirement.
B
So
in
the
first
scale,
because
in
January's
are
thousands
of
thousands
of
site
for
the
enterprise,
so
the
scale
is
very
important,
so
the
second
is
is
how
to
say
advanced
editing.
Technology
is
necessary
in
general
for
the
sd1,
because
they
are
maybe
they
are
in
general.
They
are
several
eternal
to
to
transport
reservist,
for
example,
one
is
a
amperes
another
internet
so
how
to
how
to
select
the
celebrity
from
the
channel
so
not
based
on
the
service
experience
based
on
the
policy.
B
So
this
is
is
the
very
key
feature
for
lies,
dy
and
another
important.
Seeing
is
security
because
we
deployed
the
network
on
the
Internet.
The
security
consideration
and
the
deployment
are
very
important,
just
as
the
third
challenge
is
both
the
policy
network
policy,
because
when
we
deploys
a
weenus
so
dynamically,
so
how
to
guarantees
the
policy
consistent.
It
is
another
challenge.
All
of
these
things.
B
In
fact,
different
vendor
have
a
have
a
different,
innovative
ideas
to
solve
these
challenges,
but
currently,
almost
all
those
all
of
this
solution
are
based
on
the
pre
pre
material
of
a
protector.
A
perfect
solution,
for
example,
is
banned
by
the
BGP,
so
we
hope,
maybe
idea
can
can,
can
do
more
contributing
in
in
this
area,
because
if
so,
this
means
in
the
future,
it
can
help
to
realize
into
working
with
the
different
vendors
as
divine
solution.
So
this
is
a
this
is
the
second
use
case
about
the
overlay.
Network.
B
Ok,
so
next
topic
about
about
about
the
autonomous
network
list
is
to
realize
the
automation,
so
I
think
to
realize
automation
the
the
basis
and
the
fundamental
issues
is
model,
so
we
think,
maybe
in
the
future,
at
least
that
there
are.
There
are
three
levels
model
that
the
network
device
Network
element
model,
so
the
the
network
model
and
network
service
model
so
yeah,
because
all
our
software
software
automation
rely
on
the
model,
so
we
think
model
definition,
it's
very,
very
important
to
to
to
realize
the
automation,
and
so
this
is
the
okay.
B
So
currently
there
HF
has
already
has
already
made
a
lot
of
has
already
established
the
workgroup
and
draft
for
the
model.
Definition
at
the
same
time,
in
the
industry
there
are,
there
are
a
lot
of
organization
and
vendors
and
a
customer
to
define
their
own
young
model,
for
example,
open
config,
for
example,
as
a
cisco
and
the
huawei
will
has
already
released
as
their
as
their
their
private
model.
B
So
I
think
I
think
we
think
we
think
IDF
is
very
important
to
lead
all
of
this
all
of
this
organization
and
and
the
players
to
define
the
relative
standard
model.
It
is
very
important
for
the
industry,
so
this
is
a
okay.
This
is
about
a
young
model,
so
the
last
last
very
important,
very
important
design
is
about
the
holistic
and
intelligent
of
the
other
autonomous
and
network.
So
we
can
here
is:
is
a
use
Kies
about
to
composer
to
show
the
challenges
for
the
autonomous
network
so
and
in
general,
currently
the
the
root
cause.
B
So
how
to
say
the
network
should
be
I
should
have
thought
can
influence
the
services
deployed
on
the
network,
but
yeah,
but
as
a
as
as
there
are
different
world.
So
in
general,
for
a
network
operation,
the
the
fault
can
be
caused
by
Harrow
configuration.
The
the
park
of
hardware
installed
we're
at
the
software
so
but
I
think
butter
for
our
services.
They
don't
care
about
these
issues.
They
care
about
service
experience,
so
yeah
the
policy
can
be,
can
be
execute
correctly.
B
So
theory,
there
is
no
correlation
correlation
between
the
network
fault
and
the
services,
experience
and
fault.
Currently
this
is
the
list
of
the
major
challenge
for
the
network
network,
the
operation
and
the
folder
and
the
customer.
So
we
think
why
the
reason
reason
for
that.
The
first
is
the
lack
of
data
full
of
thought
because
and
analysis.
So
the
second
T
is
so
it
is
a.
It
is
a
lack
of
lack
office,
of
mechanics
to
our
wowza
application
or
service
experience
so
and
the
majority
of
failure
are
detect.
Pasi
passively.
B
This
means
may
be
driven
by
the
complain
of
the
end
customer.
Those
may
be
customers
say:
oh
I
cannot
access
Internet.
Oh,
my
video
quality
is
very
bad,
but
currently
we
can
currently,
then
network
operation
cannot
found
these
issues
proactively.
This
is
the
third
is
lack
of
the
capability
to
correlated
to
the
issues
between
the
network
and
application.
So
all
of
this
how
to
solve
this
challenges,
I
think
the
basis
telemetry
is
very
important.
B
We
need
to
change
the
traditional
network,
maintain
a
network
status
clauncher
and
make
mechanism
to
the
future
so
from
the
polling
polling
based
polling
based
and
the
folks
on
that
device.
The
stators
expand
to
the
telemetry,
based
focusing
on
real-time
status
of
the
network
and
for
from
expand
from
static
topology
based
focused
on
device
linked
to
the
dynamic
past,
based
focused
on
application
flows
and
extend
from.
B
The
just
expand
from
and
focus
on,
the
management
tool,
not
only
management
plan,
but
also
control
plan
and
the
forwarding
plan
so
and
at
the
same
time
were
based
on
this
data.
We
can
correlate,
we
can
establish
correlation
between
the
network
status
and
the
services
theatres.
It
is
benefit
for
the
full
analysis
and
may
be
nice
tab
for
the
intelligent
of
network.
B
The
full
stack
full
of
network
analysis
and
the
intelligent
based
on
this
chart.
Maybe
we
can
we
can
we
can.
We
can
understand
the
issues
we
mentioned
and
more,
while
so
from
the
bottom
or
bottom
up
are
wasting
as
they
are
at
least
the
three
layers
for
the
network
analysis
and
the
intelligent
in
the
future.
The
bottom
line
is,
is
a
network
device
itself
so
in
in
here?
So
we
think
we
need
to
expand.
B
We
need
to
strengthen
the
data
collection
capability,
not
only
focused
on
the
management,
but
also
includes
control
plan
and
a
data
plan.
This
means
the
challenges
list
means
we
need
to
developed
some
new
protocols
and
the
format
and
Mechanics
for
this
for
different
data
collection,
for
example,
for
data
plan,
the
the
the
volume
of
data
is
very,
very
huge.
Maybe
we
need
to
you
to
design
some
new
mechanics
to
talk,
lattices
data
so
above
the
network
is
a
collect,
collect
there,
so,
basically
on
clerk
layer
it
can
adopt
to
a
different
interface
to
network.
B
So
I
think
the
interface
between
the
planter
and
and
the
network
are
very
important
so
in
here.
If,
if
ITF
can
lead
to
define
the
relative
standard
protocol
and
and
the
encoding
and
the
format
for
a
data
full
of
full
of
basic
lecture
well,
it
is
very
very
benefit
for
the
industry
above
the
clutter,
so
we've
seen
we
missing
may
be
there
yeah.
It
is
necessary
to
deploy
two
layers
analysis.
Why
is
the
online
online
analysis
near
to
the
network
itself,
and
that
may
be
another?
B
Is
the
offline
offline
analyzes
data
system
mainly
used
for
training
and
studying?
So
this
is
a
so
it's
fuller,
fuller,
fuller,
fuller
online,
and
this
is
platform
a
it
will
pro
pro.
While
the
data
leak
can
gather
all
kinds
of
data
and
share
the
data
folder
for
the
for
the
network
of
my
tenants,
so
it
is
very
important
to
solve
the
silho
system
maintenance
issues.
So
this
is
the
this
is
the
basic
architecture.
B
The
next
area
I
will
share
a
use
case
to
to
about
about
the
network,
intelligent
realization
what
is
which
is
basic
model
and
what
is
a
challenge.
So
this
this
story
has
very
interesting:
it's
not
related
ways
protocol,
it's,
it
is
really.
It
is
about
physical
network,
so
full
of
pong,
a
physical
pong
access
network.
So
for
FTTH.
We
know
as
carlo
that
the
telco
vendor
will
provide
a
very
huge
in
a
large
scale.
B
Passive
optical
network,
Tula,
Tula
customer
to
the
altitude,
a
home
gateway,
so
to
maintain
is
listen.
Network
is
very,
very
challenge
so
because
it
is
it's
a
passive
network
how
to
how
to
how
to
found
or
localities
of
photos
in
that
Network
and
aware,
is
the
fault
occurred.
It
is
very
difficult
because
it's
a
passive
network
and
there's
a
situation
as
the
environment
is
very,
very
complexed,
so
the
scissors
issues
is
not
only
the
broke
broken,
but
also,
maybe
some
how
to
say.
B
Maybe
some
the
quality
is
decreased,
for
example,
maybe
for
fiber,
if
all
over
bending
the
fiber,
maybe
the
the
quality
will
be
decreased
of
not
broken,
maybe
if
the
connector
is
losing
its
also.
The
similar
situation
is
a
very
complex,
so
the
second
is
why
we
need
to
we
need
to
locate
is
the
accurate
position
of
the
fault,
because
all
of
these
issues
should
be
should
be
solved
by
by
by
bagpipe
on
site
engineering
workload.
So
it
is
a
great
challenge,
so
a
paste
wait
one.
B
When
we
faced
this
challenge,
we
we
use
the
big
data
technology,
so
collect
a
lot
of
data
from
Allah,
auntie
and
and
ort,
and
extract
the
feature
of
this
data
and
training
the
model
for
a
training.
The
model,
training
efforts
paid
model
so
realize.
So
currently
we
achieved
a
really
good
result
with
reduce
the
40%
of
total
as
the
resist
and
and
the
increase.
The
prediction
prediction
of
the
fault
80%,
but
we
basically
list
the
good
good
hand.
The
other
hand
is
with
the
left
side.
B
Well,
the
left
left
part
under
so
to
realize
this
realized
analysis
and
the
prediction
we
have
to
collected
a
huge
of
data
so
here
is-
is
really
sample
for
a
10k
access
access
customer
for
one
week
we
have
to.
We
have
to
collect
more
than
six
terabyte
data
to
analyze
and
and
analyzes.
It
is
a
great
cost
for
data
transportation
and
the
data
storage
in
a
data
process,
so
the
challenges.
So
this
means
big
data
cannot
solve
everything,
especially
with
the
condition
of
the
cost.
B
So
this
means
we
sync
the
domain
knowledge
introduced
to
and
to
improve
the
process
that
data
data
addresses
efficiency
is
very,
very
important.
So
this
is
the
use
keys
to
share
these
the
use
case,
because
we
think
maybe
we
can
so
for
routing,
for
routing
issues,
analysis
and
and
and
troubleshooting
for
routing
issues,
and
maybe
in
the
future,
to
predict
the
routing
issues.
B
It
is
very,
very
important
for
the
IP
network,
so
this
is
the
big
problem
from
the
birth
of
the
IP
technology:
how
to
how
to
detect
the
failure
of
the
routing,
how
to
predict
the
failure
of
the
role
team?
Maybe
we
can
we
can
introduce
the
new
technology,
the
data
analyst
technology,
fuller
for
this
error,
but
we
think
we
think
the
domain
knowledge
is
very,
very
important
to
just
rely
on
the
generic
Big
Data
technology.
I.
Don't
think
it
can
achieve
a
very
good
result.
B
Okay.
So
that's
the
last
part
about
security.
I'll
security
is
a
very
important,
especially
in
recent
in
recent.
A
lot
of
organization
in
the
country
and
people
are
Sync
concert.
Secure
is
a
big
challenge
for
the
network
forest
OSHA
and
follow
for
the
word
so,
but
I
think
we.
We
need
to
work
together
to
solve
these
challenges,
so
we
cannot.
We
cannot
let
the
security
issues
to
prevent
Network
into
working
for
a
global
network.
B
So
currently,
as
though
IETF
has
already
developed
a
lot
of
security
protocol,
almost
almost
related
to
all
aspects
of
the
security
from
ossification
to
the
encryption
for
the
under
full
integration,
all
and
a
lot
of
Technology
and
and
in
the
future,
the
network,
the
IP
network,
or
should
the
pillar
should
be
a
in
front
of
superior
fundamental
for
all
kinds
of
networks
such
as
a
Phi
which
is
show
such
a
IOT
so
for
different
network.
So
maybe
there
are
some
different
consideration
about
the
network
security.
How
to
adopt
this
technology
tuesday's
solution.
B
I
suggest
that
maybe
ITF
can
work
more
close
with
other
osteo
without
organization
to
to
to
solve
the
challenge.
Okay,
we
we
talk
about
or
talk
a
lot
about
the
architect
in
a
technology
about
the
autonomous
network.
Frankly,
speaking,
I
think
we
think
it
is
a
long
journey
to
achieve
the
autonomous
network
we
just
in
the
in
initial
state,
so
based
on
our
we
think
so,
just
like
saw
on
automatic
driver.
We
try
to.
B
We
try
to
define
the
maturity
level,
a
suggestion
to
evaluating,
to
evaluate
the
autonomous
network
from
the
level
zero
to
the
level
files.
There
are
some
detail,
information
about
it,
but
even
a
summarized
doesn't
like
a
human
being
I
see
in
wheezing.
We
think
they
are.
There
are
three
to
a
capability
habilis,
a
very
important
to
the
first
in
the
hunt
to
execute
that
do
something,
and
the
second
is
the
AIA
or
a
year
to
gather
information
of
the
world
and
the
first
third,
a
ISM,
and
so
we
we
use
this.
B
These
ideas
to
think
about
the
autonomous
and
network
to
maybe
is
the
inner
inner
universe,
the
freest
who
realize
the
automation
and
the
next
step,
maybe
which
I've
realized
we
can
I
mean
we
can
have
a
more
or
have
a
have,
a
most
strong
Cal
ability
to
a
while,
the
environment
and
the
based
on
the
autumn
execution
and
their
Wireless
of
the
network.
We
can
establish
the
intelligent
to
realize
the
closed-loop
and
in
the
to
realize
the
autonomous
and
that
were
in
the
future.
Ok,
this
is
this
is
ok.
B
The
last
part
is
a
summarized
about
about
my
presentation:
I
think.
Maybe
there
are
three.
What
I
mentioned
is
three
thoughts,
so
the
major
topic.
The
first
is
d
copying,
network
transportation
and
services.
So
a
second
is
D
carving
the
network
operation
and
the
service
IT
system.
The
third
is
the
closed-loop
control
to
realize
the
autonomous
and
the
AI
in
in
a
network.
So
I
always
think
there
are
a
lot
of
what
we
need
to
do
to
realize.
The
the
autonomous
network,
thanks
samsaya.
