►
From YouTube: IETF103-SECDISPATCH-20181106-1610
Description
SECDISPATCH meeting session at IETF103
2018/11/06 1610
https://datatracker.ietf.org/meeting/103/proceedings/
C
Okay,
sorry,
all
right,
we
are
gonna
get
started
so
welcome.
This
is
sec.
Dispatch
folks
will
be
trickling
in
my
name.
Is
roman
janae?
Do
I
co-chair
with
Richard
Barnes
that,
unfortunately
couldn't
be
with
us
here
today?
This
is
the
note
well.
This
is
hopefully
not
the
first
time
that
you
have
heard
this.
It
applies.
If
you
have
any
questions.
C
C
God,
oh
thanks
Mona.
We
appreciate
it
all
right
so
just
to
level
set
if
you're
new
to
the
dispatch
process.
This
is
intended
to
help
triage
security
work
and
give
a
sense
to
those
with
drafts
about
where
they
could
potentially
take
that
work.
Their
key
ground
rules
for
the
dispatch
process
is
that
the
outcome
of
speaking
here
is
a
recommendation
about
what
the
next
step
should
be.
We
do
not
adopt
any
drafts
and
what
possible
outcomes
are.
We
might
recommend.
Hey,
go
talk
to
this
working
group.
We
may
recommend
to
spin
up
another
working
group.
C
We
may
recommend
that
the
NAD
should
sponsor
this.
If
the
ad
is,
of
course
agree
or
perhaps
the
feedback
is
that
this
is
not
an
area
of
work
that
the
ITF
should
be
focused
on
and
so
I
would
ask.
Is
we
have
the
presentations?
I
mean
two
things
as
you
come
up
to
the
mic?
First,
you
know.
If
you
have,
you
know
if
you
have
a
comment
or
kind
of
want
to
discuss
something
by
all
means.
C
C
C
C
E
Will
I
will
tell
you
about
my
proposal
named
the
certificate
limitation
profile,
which
is
application
level
amendment
to
current
trust
model?
Well,
just
a
brief
description
of
current
US
model.
Oh
Kevin
pick
a
trust
model
we
have
set
of
trusted
C's.
We
have
two
mechanisms
of
revocation
or
even
four
of
chicken
certificate
status,
cereal
and
CSP
and
anyway
we
have
say
Drive
and
revocation.
E
Google
versus
Symantec
demonstrated
us
that
say,
driven
revocation
is
not
enough,
at
least
in
case
when
we
have
big
sales
and
I.
Think
everybody
can
imagine
what
happens
if
we
find
that,
let's
encrypt
misbehaves
so
anyway,
we
need
the
possibility
to
protect
from
misbehavior
of
big
C's,
which
is
better
than
just
remove
the
root
from
the
grass
roots.
E
For
now,
application
can
do
the
following
things:
application
can
specify
a
specific
set
of
trusted
roots
application
can
ensure
serial
or
a
CSP
validation,
and
those
should
decide.
What
are
they
to
do
if
the
OCSP
server
is
unavailable
and
if
we
need
to
provide
some
limitations,
we
have
to
hard
code,
it
I
propose
the
solution.
Names
LP,
which
is
a
list
of
certificates
with
a
specified
limitation.
The
list
itself
is
distributed
with
or
by
the
specific
application.
E
Here
is
the
proposal
initial
list
of
limitation.
It's
rather
simple.
We
can.
We
can
limit
the
time
from
when
we
stopped
trusting
the
maximum
time
officiants
by
by
this.
So
let's
say
we
can
limit
value,
see
max
validity.
For
example,
if
the
original
certificates
was
expected
to
be
valid
for
two
years,
we
can
limit
it
for
just
one
year.
E
E
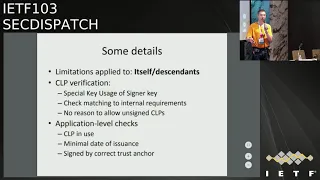
The
process
of
verification
I
think
should
include
insurance
that
the
SLP
is
sent
by
a
certificate
with
a
separate
TK
usage.
We
should
check
that
we
use
a
COP
from
by
the
source
and
well,
if
we
have
a
local
cell
P
I,
don't
think
that
it
makes
sense
to
allow
unsigned
selfies
it
should
be
configured
the
application.
The
application
that
you
sell
P
should
make
minimal
checks
that
Co
P
is
in
used
by
the
configuration
that
sale.
E
P
is
not
older
than
this
or
that
date,
and
that
it's
correctly
signed
when
we
verify
the
certificates
using
cell
P.
There
are
many
more
changes
to
the
current
process.
We
anyway
should
build
a
chain
of
trust.
We
process
the
chain
of
trust,
but
at
each
step
we
check
whether
limitations
are
applied
and
behave
according
to
the
limitations,
as
I
said,
though,
anyway,
we
have
a
way
of
dealing
with
limitations,
at
least
in
Chrome
and
Mozilla.
E
F
G
So
this
is
your
interesting
to
hear
god.
It
seems
like
there's,
perhaps
a
few
different
things
in
here-
that
we
might
want
to
talk
about
differently.
So
one
would
be
a
data
model
in
terms
of
sorry
I'm,
Ben
kata,
so
the
first
thing
would
be
a
data
model
for
thinking
about
what
sorts
of
non-binary
limitations
you
want
to
put
on
a
certificate
interesting.
This
is
through
your
date.
G
E
E
Well
and
the
second
and
the
one
more
questions
I
definitely
got.
The
from
your
set
of
questions
is
a
model
of
distribution.
I
think
that
it
is,
as
mostly
I
expect,
the
source
of
selfies
browsers
I
think
that
new
versions
of
cell
peace
can
be
deliberate,
with
browsers,
update
or
just
downloaded
from
browser
sites.
I
I
It
was
advantageous
to
have
something
like
this,
but
having
the
the
leaf
nodes
revoked
in
this
fashion
turns
out
to
be
rather
inefficient
because
there's
just
a
lot
of
bits,
it's
a
phenomenal
number
of
bits
and
so
device
something
that
will
be
coming
out
sometime
soon
that
that
compresses
them
considerably
I
think
you
have
to
think
about
the
size
considerations
involved
here.
Clients
that
are
looking
to
do
this
sort
of
validation-
probably
don't
want
to
download
the
entire
CT
database
in
order
to
to
make
their
decisions,
and
so
that's
that's
a
little
challenging.
I
The
other
comment
that
I
got
up
to
say
was
that
the
the
correct
trust
anchor
is
very
difficult
to
identify
in
this
context.
For
us,
we
make
the
list
and
we
use
their
own
distribution
mechanisms
to
get
the
the
list
down
to
two
end
points,
and
those
end
points
verify
that
we
have
a
signature
that
we
we
put
a
lot
all
that
stuff
and
verified
in
the
end
points,
but
talking
about
a
generic
system
would
be
would
be
quite
challenging.
Yeah
I
agree
it.
I
There
suspect
that
the
that
the
way
you
would
probably
operate
one
of
these
services
is
you
would
have
a
server
that
runs
for
your
application,
that
that
pulls
from
various
sources.
All
this
this
this
data,
so
maybe,
for
instance,
Mozilla's
maintaining
servers,
I,
think
they're
publicly
so
accessible.
You
would
pull
them.
The
Zillow
list
sign
that
for
your
own
application
and
then
push
it
down
to
the
application
yourself.
I
E
C
J
There
is
no
Phyllis
plus
I'm,
risking
to
repeat
hood.
Other
people
have
already
said
it
before,
but
my
main
problem
with
this
approach
is
that
it's
probably
creates
chicken
and
egg
problem,
because
you
are
trying
to
limit
trust
answers
with
another.
Just
anxious
google
sign
CTL,
so
you
are
creating
an
agency
that
controls
what
she
is
current
application
trust
so
who
will
control?
Vc?
Oh
okay,.
E
I
think
that
at
the
worst
case,
the
application
developer
can
just
resign.
The
cell
just
resigned
the
selfies
with
their
own
K,
which
is
hard-coded
in
the
application.
It's
the
worst
case,
and
anyway,
we
already
have
the
problem
of
chicken
and
egg
here,
because
it's
common
to
all
the
apk
system,
I,
don't
think
it
makes
the
situation
worse.
K
K
L
Feel
like
there's
a
lot
of
things
that
leverage
off
the
browser's
decisions
like
I.
Think
if
you
look
at
a
lot
of
Linux
distributions,
they're
Etsy,
whatever
the
directory
that
has
all
the
CAE
roots,
is
basically
mirrored
from
whatever
fire,
whatever
Mozilla
has
done
most
recently,
because
they
trust
Mozilla's
policy.
But
of
course
they
can't
make
any
decisions
beyond
the
binary
and
out
of
that
see
a
list.
So
if
they
think
the
goal
here,
I
agree,
the
goal
is
to
be
able
to
model
more.
D
C
C
M
It's
a
fairly
straightforward
draft,
just
adding
some
voids
and
sn1.
So
if
people
think
I
should
go
there,
it
shouldn't
be
too
much
work.
I've
already
actually
stolen.
Most
of
the
text
from
someone
now
I
forget
who
Sean
I
think
from
his
previous
RSC's.
So
next
slide
please.
So
this
is
adding
HSS
X,
MSS
and
XMS
SMT.
These
were
chosen
because
they've
already
progressed
through
CF
RG,
or
at
least
mostly
progressed
through
CF
RG,
and
also
we've
had
interest
in
actually
deploying
them
from
some
of
our
partners.
M
M
So
some
potential
use
cases
for
these
signatures.
An
x.509,
not
such
a
good
idea
to
use
it
in
end
entity,
cert
speak
is
mandating.
Managing
state
is
heard,
and
if
you
fail
to
manage
your
state
correctly,
you
could
inadvertently
reuse
signatures,
causing
an
attacker
to
be
able
to
forge
signatures
fairly
easily
as
CA
certs
and
interactive
protocols.
It's
an
okay
idea.
You
have
an
HSM
already
to
manage
state.
M
The
only
slight
disadvantages
that
signature
size
is
larger,
so
it's
an
okay
option.
If
you
can
live
with
that
larger
signature
size,
the
best
use
case
would
be
for
say
certain
non
interactive
protocols
and
code
signing
certs,
and
this
is
where
we've
seen
the
interest
for
these
algorithms.
You
have
an
HSM
to
manage
state
and
the
signature
size
is
not
so
much
of
an
issue,
and
in
this
case
these
algorithms
are
ready
to
deploy
now
for
long
live
search
such
as
in
IOT
or
automotive
next
slide.
M
J
K
N
H
C
O
B
B
P
Q
C
The
process
is
to
hear
from
the
floor,
so
the
the
options
appear
to
be
that
we
need
something
to
describe
the
parameters
for
lamps
to
take
the
work
they're,
given
how
the
Charter
is
written.
There
needs
to
be
a
commitment
to
we
heard
at
least
two.
Yes,
you
know
one
yes
and
one
probably
eventually
kind
of
an
implementation.
I,
don't
know
whether
that's
enough
to
recharter
kind
of
the
group
and
then
the
alternative
beyond
that
would
be
a
needy,
sponsored
kind
of
document
or
screen,
while.
C
P
C
M
R
R
But
I
will
briefly
talk
about
the
word
draft
so
background
is
we
had
like
lots
of
thoughts
of
security
incidents
during
past
like
few
years
about
sexy,
including
the
loss
of
the
assets
and
especially
in
the
last
eight
year,
is
like
random
dub,
not
a
J's
around
a
hot
area
which
suffered
a
lot
about
security
incidents
which
Cohen
suffered
it,
which
caused
a
loss
of
assets
and
yeah.
This
is
where
stopped
major
incident.
R
We
have
we
there's
lots
of
extends
past
few
years
and
why
we
here
why
I
am
here
is
like
we
wanted
to
build
the
base
document
for
clipped
asset
custodians
Whittaker,
which
is
we
call
the
Bitcoin
exchange,
were
sort
of
things
and
for
the
best
security
security
best
practices.
At
this
moment
some
organization
makes
and
documents,
but
we
don't
have
any
open
documents
at
this
moment.
R
Right
now-
and
the
second
reason
is
that
we
have
like
a
instant
happens
like
quarries
or
the
law
enforcement,
have
some
investigation
investigations,
but
not
like
the
lessons
from
those
instant
is
not
pick
up,
be
public,
so
there's
a
little
bit
difficulty
with
shares
and
nourish
shares,
resins
from
that
those
instance.
So
so
the
why
we
here
is
like
we
were.
We
were
trying
to
make
documents
about,
not
we're
not
making
the
regulations
because
we're
not
up,
though
we're
not.
This
is
a
not.
R
This
is
a
ITF
is
not
the
price
to
make
the
regulations,
but
we
can
tell
like
this
is
how
we
think
to
secure
the
could
create
asset
cassadines
and
also
we
can.
We
may
tell
like
it
is
the
kind
of
guidelines
and
also
that
one
important
thing
is
like
we
want
to
open
that
document,
so
everyone
can
use
and
free
everyone
can
comment
and
no,
there
is
no
dependency
with
like
some
countries
and
economics.
So
that's
why
that's
a
weird
proposing
document
here.
R
But
there
is
no
solid
definition
at
this
moment,
so
in
me
it
may
be
useful
for
the
define
here
and
we
people
can
use
it
and
there's
another
things
like
security
controls
or
the
objectives
and
and
also
the
security
analyst
and
I
resist
those
are
actually
coming
from
the
is
Otis
and
27001
based
things,
but
there's
still
we
have.
We
need
to
add
some
information
on
this,
so
we
put
some
information
here
and
to
the
our
draft
as
well.
So
this
is
kind
of
that.
R
R
So
we
need
to
think
about
while
we
deal
with
those
key
management
and
here's
a
discussion,
but
what
we
want
to
get
information
from
here
so
that
the
first
one
is
ITF
is
the
right
price
to
discuss
those
issues
and
if
so,
we
want
to
where
the
right
place
and
if
not,
is
there
any
price
you
know?
Is
there
any
prey
is
a
good
for
good
to
have
such
discussions.
S
S
The
broker
would
interface
between
the
end-user,
no
in
the
exchange
and
and
do
things
like
protect
the
users
money
ensure
that
it's
still
there
as
you're
transacting.
So
if
something
happens
at
the
with
the
cryptocurrency
and
there's
a
theft
or
whatever
you
you're
protected
in
some
way,
so
you're
not
talking
about
that.
No
we
are
just.
Can
you
explain
a
little
bit
more
because
then
I
have
a
gap
still,
okay,.
R
So
we
are
just
like
we
are
just
defining
what
kind
of
feature
the
functions
is
could
be
required
for
those
to
meet,
builds
the
crypto
currency
exchanges,
and
we
discussed
like
that.
How
is
it
like
this
is
Erica
we,
this
is
the
press,
that's
this
store
the
public
private
keys,
and
we
may
we
made
this.
We
were
discussing
this
may
be
a
list.
R
We
need
to
think
about
how
we
need
to
think
about
the
risk
and
how
do
we
deal
with
it
and
we
don't
need
we
don't
like
your
questions
like
out
like
the
brokers
and
customers.
Api
is
those
things
like
should
be
here,
but
we
don't
have
a
discussion.
We
don't
discuss
this,
for
this
part,
is
that
clear
yeah
I
mean.
C
T
R
U
Script
approach:
could
you
please
a
little
bit
to
the
slide
waves
as
a
question
about
I
saw
and
or
some
other
installations,
so
actually
in
I
saw
in
technical
committee
307
in
study
group,
seven
more
or
less
relevant
work
is
going
on,
so
just
for
information
that
relevant
work
is
already
done
and
technical
committee
217
I
saw
was
created
to
address
such
issues.
Okay,.
U
V
So
a
lot
of
the
protocols
involved
in
this
that
you
would
like
us
to
discuss
and
have
best
common
practice
for
art
designed
outside
the
IETF
and
no
one
in
the
IETF
actually
probably
knows
these
protocols.
So
in
that
sense,
I
think
this
is
not
the
right
place
to
discuss
it.
I
think
it's
here.
Your
initiative
is
really
good.
I
really
wish.
V
You
know,
there's
a
standard
document
that
all
the
exchanges
can
use
and
like
how
should
I
do
this
so
that
it
don't
lose
millions
of
other
people's
money,
but
I
honestly,
don't
think
that
the
IETF
is
the
place
for
that,
because
we
actually
don't
know
these
protocols.
In
fact,
when
you
say
crypto,
we
think
about
something
completely
different.
I
know
what
you
do.
V
W
So
I
feel
like
there
is
probably
some
work
here
to
be
done.
There's
probably
a
useful
technical
problem
to
be
solved,
but
I
think
there's
there's
a
lot
of.
At
least
it's
not
clear
to
me
right
now,
kind
of
where
the
boundary
is
between
technical
work,
that
we
were
doing
an
organization
like
this
and
the
policy
works
goes
Louis.
I,
though,
think
the
dress
is
helpful
and
then
starting
to
flush
that
out
I
mean
maybe
it
might
require
a
round
or
two
more
discussion
to
really
hardened
that
boundary
up.
That's
a
Paul's
point
about
expertise.
W
You
know
the
the
IETF
as
a
community
is
not
a
fixed
thing.
One
of
the
things
that
I
think
I
would
want
to
see
as
a
prerequisite
to
get
starting
work
here
is
that
the
community
that
would
be
involved
in
this?
So
perhaps
some
people
currently
fulfilling
this
role
in
the
in
the
blockchain
ecosystem,
we're
paying
attention
to
this
we're
involved
we're
contributing
and
I
think
that
community,
if
you
had
the
active
stakeholders
involved
and
I,
think
if
you
could
bring.
W
W
S
W
S
Kathleen
we're
all
ready
again
so
I'm
just
responding
to
Paul
and
that
I
do
think
that
there
could
be
something
very
useful
here
and
I.
Don't
think
we
should
shy
away
from
this
area
of
work.
If
you
look
at
what's
going
on
in
in
the
blockchain
world
they're
trying
to
recreate
our
protocols
and
in
some
cases,
they're
not
doing
a
great
job,
so
I
think
you
know
if,
if
those
are
to
take
hold
in
some
shape
or
form
us
having
collaboration
and
expanding
work
in
the
space,
is
a
smart
thing
to
do.
Okay
and.
V
V
Guess
the
last
two
people,
sorry
like
I,
said
I
do
think
there
is
value
I'm,
not
sure
if
I
gave
the
best
place,
because
we
try
to
look
at
assistants
in
general
and
the
protocols
that
we
that
we
describe
and
know
about
like.
If
we,
if
the
decentralized
research
group
that's
doing,
things
now
comes
up
with
a
protocol
that
goes
into
the
ITF
and
I
think
we
should
definitely
have
a
document
like
this
for
that
protocol,
but
I
find
it
a
little
bit
difficult
to
have
something.
That
is
really
something
very
specific.
V
It's
the
same,
if
you
would
say
like
if
the
voting
machine
people
would
come
here
and
say
we
have
got,
we
have
this
policy
on
how
to
protect
voting
machines.
It's
a
really
good
idea,
but
we
have
general
security
and
we
have
the
protocols
that
are
used,
and
we
can
make
statements
about
that.
But
it's.
M
C
Okay,
so
to
summarize
the
gist
of
it,
it
would
appear
that
there's
no
organic
place
in
which
to
kind
of
take
this
work.
So
typically,
next
steps
are,
if
you
think,
there's
a
bigger
body
work
around
that
to
try
to
build
well,
I'm
sure
kind
of
around
that
and
perhaps
propose
come
up
off
and
with
that
be
able
to
demonstrate
hey,
there's
a
community
of
folks
there's
a
community
of
interest
and
perhaps
talk
about.
Is
there
more
or
less
kind
of
work
to
do
here?
W
B
Call
that
area
director
so
I
think
I
mean
I
mean
it's
okay
with
Mike
LED
here,
but
I
think
I
speak
for
our
general
policy,
which
is
if
it
would
help
you
have
a
mailing
list,
discuss
this.
We
can
make
one
for
you,
so
I,
don't
know
if
that
helps
you
or
not.
But
if
you'd
like
that
email
us
and
we
can
take
care
of
it
I
any.
K
X
X
So
if
we
look
at
the
network
architecture
here
is
a
device
and
an
access
point
and
then
a
triple
a
server.
So,
like
radio
server
that
controls
access
to
this
local
network-
and
we
generally
think
that
there
will
be
a
remote,
Triple,
A
server
that
actually
implements
the
EAP
noob
server
side,
because
it
needs
a
user
interface
and
we
don't
need
any
software
changes
here
on
the
local
network,
but
only
to
that
server
and
to
the
device
and
then
the
device
me
it
has
no
identity.
So
how
does
it
talk
to
the
application
server?
X
Well,
it
uses
this
fixed
I
know
most
identity,
loop
at
EAP,
don't
know
got
net
and
that
the
local
people,
a
server,
has
to
route
to
the
server
that
implements
EAP
noob
and
for
that
network.
And
then
the
device
is
able
to
talk
with
the
authentication
server,
and
that's
the
trick
here
in
the
design
that
since
we
can
talk
over
EAP,
we
can
have
inbound
communication
before
the
device
is
registered.
X
It's
key
exchange
over
the
invention
and
then
the
outer
band
message
that
authenticates
this
with
the
hash
of
the
easy
th
parameters
and,
additionally
with
send
the
secret
knowledge
that
is
then
used
again
for
authenticating
the
key
exchange
at
the
the
key
confirmation
step.
So
these
are
the
steps
and
not
for
attaching
a
device
to
the
network,
and
then,
after
this
we
create
a
persistent
association
between
the
device
and
the
authentication
server
and
in
the
future
connections
that
will
be
used
for
tricking
and
reconnecting
with
the
witne
on
Caesar,
with
the
EC
dat
and
future.
X
X
The
assumptions
we
wanted
to
make
about
the
out-of-band
channel
here.
Well,
we
wanted
to
make
minimal
assumptions
about
the
main
channel.
So
just
one
message
in
either
direction
should
be
enough
either
from
server
to
the
device
or
device
the
server
and
the
outer
band
channel
is
assumed
to
provide
either
secrecy
or
integrity
for
the
outer
band
methods.
X
But
if
one
fails,
the
protocol
will
still
survive
those
who
under
security
protocol
design,
will
not
believe
that
and
that's
why
there
is
this
note
that
in
the
case,
if
their
message
has
no
secrecy,
the
other
band
methods-
someone
can
see,
for
example,
the
QR
code
and
spy
on
it.
Then
there
is
this
catch
that
the
user
must
note.
X
The
failure
of
the
other
endpoint
to
accept
the
received
message,
and
if
it
does
not
accept
it,
then
the
user
must
go
and
reset
the
other
endpoint
that
is
sending
out
open
message
and
remove
that
created
Association
from
the
another
security
goal
here
and
which
we
have
Lee
recently
spent
a
lot
of
time
on.
Is
this
resistance
to
the
now
serviced
by
money,
men
in
the
middle
that
occurs?
That
becomes
a
problem
because
we
don't
have
like
this
long-term
credentials
to
fall
back
to,
and
we
absolutely
do
not
want
to
go
to
this.
X
X
X
Authentication
server
or
the
cloud
interface
for
that
and
then
logs
in
and
that
approves
the
device
to
be
attached
to
the
wireless
network
and
also
is
it's
now
register
as
Alice's
device
on
the
authentication
server
for
application
purposes,
and
the
protocol
here
in
the
background
happens
well
here,
the
device.
Does
this
initial
parties
in
the
eighth's
exchange
with
the
authentication
server
here,
the
outer
bandmates,
it
authenticates
it
in
the
two
ways,
and
then
we
have
the
key
confirmation
stack
again
in
band.
X
Okay,
so
I
wanted
to
show
some
details
about
the
security
design,
but
obviously
I
won't
be
able
to
go
through
this
all.
But
so
one
thing
is
that
the
the
outer
band
message
we
wanted
that
to
be
small.
So
it
basically
has
this
two
important
with
sada
Lubin,
whom
so
Ananse
secret
norms
and
in
the
house
of
the
key
exchange
in
van
key
exchange,
and
they
can
be
formatted
as,
for
example,
as
a
URL
and
then
put
into
a
cure
code
or
in
depth
tag
that
is
dynamically
changing.
X
Maybe
every
few
minutes
when
the
nonce
is
chains
and
the
noob
is
the
part
that
needs
confidentiality
and
Huub
is
the
part
that
needs
integrity
in
the
handshake.
And
one
of
those
is
enough
to
rule
for
security
for
identifiers.
Since
the
device
doesn't
really
have
any,
we
don't
we
don't
register
any
identifier.
We
can't
trust
any
identifiers
that
the
device
presents
us
like
MAC
addresses
and
therefore
we
need
to
avoid
attacks
like
identifiers
squatting,
and
the
solution
here
is
that
the
server
allocates
the
new
peer
identifier
for
the
for
the
peer
in
the
initial
exchange.
X
B
Happens
if
I
take
the
if
I
take
them,
if
I,
if
I
take
the
identifiers
from
another
device
and
display
it
on
my
screen
and
then
and
so
so.
The
scenario
here
is
there
like
two
devices
in
the
room
and
and
I
take
the
identifiers
from
from
a
device
and
the
the
user
thinks
the
the
user
is
attempting
to
pair
with
me.
X
I'm,
the
attacker,
the
Cure,
so
the
because
the
device
has
no
identity.
It's
the
physical
access
to
the
device
that
identifies
the
device
so
certainly
well.
The
user
does
need
to
not
choose
the
right
device
and
the
the
way
it
we've
implemented.
It
is
there's
a
reset
button
on
the
device
and-
and
you
need
to
do
like
hard
reset
or
when
you
take
the
device
out
of
the
box.
It's
powered
up
and.
H
X
H
X
B
And
I
understand
the
use,
but
the
user.
Do
you
so
scenario?
Maybe
I'm
not
quite
following
your,
but
the
the
devices
are
both
an
imprinting
mode
and
the
attacker
takes
the
QR
code
from
a
from
device
from
legitimate
device
displays
the
his
own
display
the
at
and
at
that
point
the
user
actually
is
connecting
to
the
legitimate
device,
but
thinks
is,
can
attacker
correct.
B
X
X
Y
X
B
X
X
B
W
X
It's
kind
of
whether
it's
a
problem
or
not.
This
isn't
difficult
to
define,
because,
if
I
think
of
like,
if
we
formalized
attack
model,
is
not
going
to
be
a
problem
because
that
attacker,
you
know,
if
that
other
device
is
just
now
Park
I
know
part
of
the
attackers
I'm
using
a
dishonest
device
to
connect
and
that
dishonest
device
may
use
whatever
means
of
communication
a
ones
do
the.
B
Usual
scenario
is
the
next
thing
that
the
user
does.
The
problem
is
that
the
toe
so
I
like
again
I,
have
no
I,
don't
understand
what
you're
using
model
is,
but
you
but
I'm,
assuming
the
light
that
user
is
looking
at
the
device
and
has
like
instructions
on
the
screen
right
and
it
says,
do
like
XY
and
Z
right
so
IQ.
B
It's
looking
at
on
his
device
and
so
he's
he's
he's
sending
you
the
that
is
anything
he
knows
of
the
mouse,
a
nose
mierqi
keep
pressing,
and
so
he
simulates
he
sends
you
on
his
own
screen
things
that
appear
to
be
simulated
events,
because
he
can
like
see
their
device
to
see
what
it's
doing
right,
but
instead,
what
he's
doing
is
guiding
you
through,
like
you
know,
miss
configuring,
the
honest
device
and
so
on,
and
because
the
problem
is
that
the
user
thinks
is
connecting
to
this
device.
The
Ashley
Adonis
device.
G
H
G
And
you
can
also
have
issues
you
know
when
you've
done
the
unit
on
occasion
and
then
the
user
goes
to.
You
know,
label
the
device
that
they
just
registered
in
some
database
and
they
mislabeled
the
device,
so
they've
actually
registered
the
Hans
device,
but
they
think
that
it
they
associated
with
dishonest
device.
It's
not
the
name
that
these
are
prong
mismatches
and
depending
what
the
user
can
do
with
the
device
that
could
have
problems
for
them.
I'm
less
sure
that
I
understand
exactly
the
scenario
you're
describing
about
I'm.
G
I
I
I
H
Z
Soto
satellite
image
here
so
right
now,
an
emu.
We
don't
have
any
charter
items
to
do
something
like
this.
The
other
sort
of
issue
here
is
this
is
a
particular
solution
and,
and
there's
this
kind
of
device,
enrollment
or
registration
problem
is
being
discussed
in
a
number
of
different
types
of
craft
like
there
was
I,
think
a
brewski
and
some
other
things
they're,
not
exactly
the
same,
but
they're
related
and
before
I
think
we
would
want
to
take
on
the
work.
Z
Z
Registration
code,
QR
code
or
whatever
it
is,
then
then
you
wouldn't
be
able
to
use
this
mechanism
as
far
as
I
can
tell
so.
There
may
be
some
devices
that
would
be
locked
out
that
that
wouldn't
be
able
to
use
this
mechanism
that
maybe
people
care
about
so
I
think
there's
needs
to
be
kind
of
more
definition
around
the
problem.
Space.
Z
Y
W
So
I
have
been
made
aware
by
another
email
participant
there's
a
meeting
to
discuss
these
various
onboarding
questions
this
evening
at
6:00
8:00
in
same
room
where,
let's
see
I
guess
opposite
of
eg
is
meeting
right
now
it's
something
tight
that
I
can't
pronounce,
but
it's
down
on
the
second
floor,
I
think
so
it
sounds
like
I.
Think
Joe
is
probably
right.
There's
some
ambiguity
right
now
around
the
specific
use
case
and
whether
this
makes
sense
to
work
on
I
think.
Hopefully
that
meant
there
might
be
a
little
bit
more
clarity
on
that.
W
Z
Think
it
could
be
it
kind
of
depends
if,
if
there
may
be
another
possibility
would
be
if
there
was
a
place
where
this
kind
of
device
enrollment
was.
If
there
was
a
working
group
or
or
a
community
that
supported
that,
but
EMU
certainly
could
be
if
I,
but
I,
think
we'd
really
want
to
make
sure
we
knew
what
use
case
we
were
trying
to
solve
because
they're
all
so
we
could
ration
a
lot
and
could
be
difficult.
C
O
Cable
labs
and
I
just
want
to
talk
about.
You
know
the
this
approach
of
providing
provisioning
devices
using
it
mechanisms.
This
is
something
that
you
know
in
the
mo
working
real,
quick
we
started
to
discuss.
We
discuss
a
little
bit
seems
that
recharter
might
be
needed
or
not
I,
don't
know.
Probably
not,
but
I
would
say.
Definitely
emo
would
be
one
of
those
places,
and
one
of
the
things
that
I
wanted
to
say
is
that
we
see
this
happening.
O
You
know
trying
to
use
it
to
provision
some
form
of
credentials
for
devices
happening
in
many
different
ecosystems,
and
you
know
if
you
guys
are
interested
come
to
the
6
p.m.
there
will
be
an
interesting
discussion,
but
definitely
I
would
say.
Maybe
you
know
could
be
a
good
place
to
do
it.
I
wouldn't
say
that
you
know
it
could
be
like
other
working
group.
Probably
it's
not
it's
very
deeply
related
this
one.
So
I
would
support
yeah,
especially
to
email.
P
Y
Again,
this
is
a
cheap
method,
so
I
think
it.
It
makes
sense
to
have
it
anymore
because
there's
where
the
expertise
is
other
methods
that
may
use
heap
in
certain
ways
with
you
know
other
protocols
or
our
tie
to
other
technologies
that
we
can
figure
out
but
I,
don't
see
any
reason
why
they
should
not
be
taken
up
by
emo.
Again,
I
am
caught
her,
so
I'm,
not
not
saying
as
a
chair.
W
All
right
thanks
for
those
comments,
so
is
it
given
all
that
I
think
I
propose.
We
consider
this
provisionally
dispatch
to
EMU
pending
the
discussion
tonight
about
requirements,
so
any
further
discussion
about
what
kind
of
where
to
do.
This
work
right,
where
the
design
of
this
work
should
be
a
matter
for
the
email
working
group
to
figure
out
its
image.
W
Z
AA
Final
word:
yep
DC's,
research,
India,
so
well.
I,
don't
want
to
really
comment
on
whether
you
should
do
this
work
or
which
working
group
should
do
this
work,
but
coming
from
a
developing
economy,
I
think
solution
like
this
will
help
many
of
the
startup
ecosystem
that
we
have
back
in
developing
countries
like
India
I,
know
many
people
who
have
innovative
solutions,
but
the
handling
the
security
stack
and
all
these
things
are
creating
a
bit
of
overhead.
AA
This
kind
of
outer
band
the
technique
using
standardized
systems
is
something
probably
the
people
would
love
and
would
be
popular.
That
is
my
hunch.
They
are
the
only
thing
that
concerns
me
is
per
device,
cost
that
that
is
something
that
we
have
to
scale
and
we
have
to
kind
of
check
I'm
talking,
particularly
from
a
very
implementation
and
marketing
point
of
view,
so
I
I
do
have
full
support
for
this
work.
Thank
you.
C
Q
Accuracy,
eh
and
the
problem
was
demand.
Validation
is
that
it
basically
kind
of
goes
towards
a
proxy,
so
it
validates
that
the
IP
address
that
you
can
do
something
on
the
IP
address.
The
domain
name
is
pointing
to,
for
example,
or
that
you
have
access
to
a
certain
mail
aggress,
and
there
are
several
problems
we
stumbled
about,
for
example,
IP
use
after
free
attacks.
Q
If
you
have
somebody
who
sets
up
the
service
if,
for
example,
Amazon
ec2
points
a
DNS
name
there,
and
then
it's
like
well
I,
don't
use
that
service
anymore
throws
away
the
service,
it
doesn't
delete
the
DNS
record,
then
somebody
else
can
grab
that
IP
address
actually
get
a
certificate
and,
depending
on
what
domain
is
actually
pointing
there,
which
sub
domain
can
actually
cause
a
lot
of
mayhem.
So
uber
got
hit
by
this.
Quite
recently,
all
the
authority
and
his
folks
had
one
of
their
web
RTC
endpoints
hit
by
this.
Q
What
you
can
also
do
is
you
can
do
forced
on
path
attacks,
so
you
do
a
normal
monkey
in
the
middle.
If
you
happen
to
just
be
on
the
path
or
you
do
an
EP
attack
to
force
somebody
to
route
by
you,
which
then
allows
you
to
do
the
same
thing
again,
there's
also
DNS
cache
poisoning.
If
you
can
poison
the
cache
of
the
CA
to
hold
a
record
pointing
somewhere
else,
an
IP
address
you
control,
you
can
get
a
certificate.
Q
There
was
recently
an
attack
where
you
over
variety
additional
section
of
DNS
responses,
it's
quite
academic
and
theoretical,
because
you
have
to
reduce
him
to
you
to
64
byte,
but
they
somewhat
have
a
point
similar
to
that.
If
you
have,
you
know
surfs
tail
going
on,
you
can
actually
force
a
situation
which
is
similar
to
the
first
problem
by
tossing,
authoritative
server.
Q
So
against
use
of
the
free
attacks,
you
could
start
requiring
TLS
a
records
to
be
present,
especially
if,
like
the
requests
are
coming
from
Amazon,
ec2
or
well
any
other
of
the
big
cloud
providers,
you
could
do
proof
of
prior
ownership
based
validation,
which
is
not
really
there,
but
doing
that
would
be
an
option
spiking
that
for
forced
on
path
attacks
like
all
of
the
above
already
helped.
But
in
addition,
you
could
also
do
a
multiband
touch.
Q
Point
validation
or
you
could
say
like
ok
if
we
are
seeing
attack
at
the
IP
at
this
subnet,
from
which
we
see
the
request
and
one
of
the
BGP
monitoring
services.
We
just
don't
issue
until
that's
over
and
for
DNS
for
notary
there's.
Also,
some
practical
considerations
like
checking
for
small
MTU
packets
and
ignoring
them
chasing
additional
sections
yourself,
validating
DNS
egg,
which
is
well
to
give
them
anyway
and
not
using
surf
from
cache
or
actually
even
serve
stale.
Q
However,
others
are
missing
and
if
you
have
something
like,
for
example,
surf
stale
surf,
stale
I
contacted
see.
Also,
you
will
probably
also
come
the
resistance
security
considerations
now,
but
then
you
have
all
these
recommendations
all
over
the
place
in
different.
There
are
some
different
parts
and
what
this
basically
leads
to
is
people
reading
them
or
people
not
reading
them.
All.
If
you
miss
one,
you
might
have
a
problem
for
your
CA
a
little
bit
on
the
history
of
the
whole
thing.
Q
So
we
had
a
first
paper
on
this
in
2018
in
February,
we
presented
it
at
the
ACMA
working
group
at
ITF
102,
where
we're
told
like
a
cape.
You
can
present
all
along
drop
us
a
draft.
We
sent
a
draft
roughly
two
weeks
three
weeks
four
weeks
ago
and
after
a
male
discussion,
because
people
were
especially
concerned
that
this
is
not
protocol
specific,
but
more.
Like
an
operational
idea
for
like
how
to
run
a
CA,
this
was
moved
to
SEC
dispatch.
F
Q
Because
I
didn't
quite
follow
that,
so
the
comments
were
more
general
like
this
is
about
how
to
operate
a
CA
or
like
operate.
Resolvers
operate
services,
if
you're
a
CA
and
not
about
likes
a
specific
acne
protocol,
it
was
actually
like
actually
a
relatively
short
email
exchange,
which
ended
with
Richard
I.
Think
hitting
up.
You
ask
him
whether
we
could
have
it
here.
So
there
was
not
that
much
discussion.
It
was
more
like
okay.
This
should
be
dispatched
first,
yeah
I
think.
W
The
upshot
is
Richard
burns
again
is
that
did
the
attacks
like
the
BGP
and
dynastic
layer
attacks
apply
very
broad
and
then
actually
all
three
of
the
classes
of
problem
that
you
apply
to
other
methods
of
issuing
certificates?
Besides
acting
all
the
manual
stuff
that
exists
is
pre,
active
yeah
I
mean
it's
a
minority
in
the
web
now,
but
yeah
and
so
I
think
the
idea,
if
you're
going
to
do
the
document
like
this
would
be
to
have
something
that
you
could.
W
Using
an
automated
protocol
like
a
key,
that's
a
I
think
there
could
be
some
utility
here.
It's
you
know
the
see
a
browser
forum
working
a
validation
working
group
could
use
this
as
some
inputs
of
their
consideration,
of
what
validation
methods
to
accept
I.
Think
for
me,
this
probably
looks
like
an
ad
sponsored
draft,
because
it
is
so
so
informational
so
like
it
would
benefit
from
some
discussion
on
site.
W
What
I
think
might
be
interesting
to
discuss
attack
me
if
you
you're
up
for
doing
some
additional
work
is
to
look
at
some
some
mitigations,
especially
the
first
problem
you
know
to
use
after
free.
There
are
some
protocol
updates
there
that
that
could
be
used
to
address
that
problem.
I
think
they
would.
Q
That
that
would
actually
be
another
thing
you
could
do
like
the
proof
of
Pirozhki
ownership,
but
technically
technically.
The
problem
already
goes
away.
If
you
require
TLS
era
codes
to
be
present,
which
then
moves
somewhat
closer
to
the
DNS
challenge,
but
should
be
depending
on
whether
you're
regenerating
key
material
on
every
reissue
of
a
certificate
only
be
a
one-time
setup.
Instead
of
updating
the
challenge
in
DNS,
okay,
yeah
I.
K
Shawn
Turner,
so
we
do
have
this
RFC
that
was
written
long
ago
called
RF,
these
RC
3647,
which
is
certificate
policy
and
certificate.
Following
this
policy
framework,
which
tells
you
about
how
to
write
policies
for
writing
your
CA
and
how
the
CA
is
they'll
run
its
say
how
they
do
it.
If
these
things
are.
K
W
So
that's
a
delicate
patient
to
put
on
the
operating
table,
but
I
mean-
and
it's
gonna
be
a
big
deal.
If
we
open
up
that
document
for
revision,
but
you
know
it
might
be,
we
could
issue
a
point
update,
so
so
for
those
who
are
not
aware,
there's
this
RFC
gets
used
as
a
basis
for
CA
policy
documents
that
are
used
in
the
legally
binding
stuff
and
so
making
edits
to
that.
It
has
rather
dramatic
implications
for
a
bunch
of
the
industry.
AA
W
Q
We
should
also
keep
in
mind
so
referencing,
our
other
older
women,
so
this
is
moving
quite
fast,
so
actually,
like
one
of
these
fonts
was
just
edit.
This
ITF,
when
I
stumbled
across
a
search,
tail
Records
and
my
personal
expectation
would
be
that
there
would
be
a
lot
more
adjourn
or
various
people
are
like
starting
to
beat
on
this
new
thing
in
the
ecosystem
and
there
will
be
new
things
Pat.
That's
also
something
to
keep
in
the
back
of
her
hats.
So.
W
Q
Well,
it's
not
more,
it's
not
really
a
statement,
but
I
know
that
there
are
some
movements
in
the
ITF
which
are
also
looking
at
often
security
considerations,
so
the
routing
people
are
dealing
with
this.
The
question
is
whether
collaboration
with
them
and
getting
something
which
can
be
more
easily
update,
if
not
also
be
an
interesting
thing
to
do.
In
this
context,.
L
Gothics,
it
seems
to
me,
given
what
Richard
said
about
how
this
is
something
which
is
the
as
a
lot
of
perience
that
has
a
lot
of
people
to
put
in
the
world
depending
on
it.
That
sounds
to
me
like
at
least
a
new
working
group,
because
that
needs
to
pull
it
a
lot
more
community
that
are
not
sort
of
spending
on
things
currently.
AA
W
B
G
D
W
C
Mean
it
would
seem
that,
depending
on
the
aperture,
you
want
to
open-
and
you
know
there
is
the
acne
and
acne
kind
of
focused
thing.
If
there
really
are
that
many
different
angle,
once
we're
gonna
need
more
coordination
and
it's
really
kind
of
a
question
of
how?
How
broad
do
you
want
it
to
be,
and
that
suggests
the
form
so.
W
It
sounds
like
there
were
kind
of
three
possible
work
items
we
discussed
here.
One
is
what
you've
presented
today.
Another
one
would
be
an
update
to
acne
that
would
mitigate
some
of
these
concerns,
which
would
probably
live
in
the
acne
working
group
and
that
there
would
be
updating
the
certificate
policy
document
which
Sean.
W
K
U
B
The
the
East
German
judge,
I,
think
you
know,
one
of
us
will
either
take
it
probably
me
or
try
to
shop
it
to
orange,
but
I
think
we
I
think
I.
Guess
I'd
like
to
use
a
safe
dispatch
mailing
list
to
sort
of
refine.
Perhaps
I'm
not
saying
it's,
not
good,
I
haven't
read
it
IANA,
so
I,
maybe
it's
incredible.
It
needs
work
so,
but
so
yes,
so
perhaps
perhaps
the
chairs
could
assist
us,
never
find
the
process
absolutely.
Q
B
Okay,
I
guess
my
request
would
be
like
focus
on
problem
earring
as
much
as
possible
solution.
Earring,
perhaps
only
some
because
as
a
solution
earring,
maybe
maybe
like
a
lot
of
design
work
so
but
III
familiar
with
your
work
and
like
a
bit.
Obviously
the
subtyping.
The
problems
like
critically
important
I
think
it's
fine
to
sort
of
say
here
are
some
things
you
might
do
but
like
like,
we
can't
really
wrap
for
an
axle
on
the
solution
right.
So.
C
So
it
sounds
like
it's
refined,
a
little
more
drop
it
on
the
list,
we're
headed
in
the
direction
of
some
kind
of
ad
sponsorship.
Okay,
the
aperture
stays
staying
small
on
this
thanks.
Okay,
thank
you,
everyone,
okay!
So
that's
the
last
dispatch
item
to
quickly
wrap
up
eatery
where
we
stood
with
all
of
them.
C
The
first
draft
we
heard
it
was
about
certificate
limitation
policy,
and
the
feedback
was
primarily
that
the
use
case
in
motivation
wasn't
exactly
clear
that
if
there's
a
desire
to
kind
of
move
forward,
there's
a
need
to
clarify
and
refine
some
of
those
issues.
Then
the
second
draft
we
talked
about
was
about
algorithm
identifiers
for
HSS,
and
the
feedback
primarily
was
lamps,
has
to
be
the
place
to
take
this
work
and
that's
going
to
require
reach
our
Turing
and
there's
a
conversation
about
how
to
do
that.
C
Reach
our
Turing,
but
that's
the
that's
the
recommended
dispatch
next
step
and,
as
we
mentioned,
that's
just
a
recommendation.
The
next
draft
we
heard
about
was
about
general
considerations
for
crypto
asset
custodians,
and
it
appeared
if
there's
no
natural
home
for
that
work-
and
you
know
some
community
building
and
interest
is
required.
So
you
know
kind
of
next
steps
are
get
a
mailing
list,
build
a
community
around
that.
Maybe
that
leads
to
a
Boff
for
next
steps.
C
Then
we
talked
about
a
noob
and
there's
gonna,
be
further
discussion
tonight,
so
provisionally
we're
recommending
where
the
the
dispatch
process
is
saying.
Take
that
to
EMU
further
discussion
is
going
to
happen
tonight
and
then
we
just
talked
about
extending
security
considerations
for
acne.
Another
refinement
is
going
to
be
kind
of
published.
It's
headed
in
the
direction
of
some
kind
of
ad
sponsor
for
their
discussion.
We
required
about
which
mediate
wealth
will
handle
that.
So
what
with
that
is
there
another
draft?
C
We
want
to
talk
about
or
any
other
business
going
once
going
twice
and
then
before
I
close
I
was
asked
by
the
co-chairs
of
the
of
the
measurement
and
analysis
for
protocols.
Research
group-
that's
meeting
right
now
in
chat
la
no
one
that
they
have
some
security
relator
topics.
So
if
you're
interested
please
join
them
now,
they
run
until
until
six
ten,
all
right
thanks.
Everyone.
