►
From YouTube: IETF103-TUTORIAL-INTAREAOVERVIEW-20181104-1345
Description
TUTORIAL meeting session at IETF103
INTA/RE/AO 2018
https://datatracker.ietf.org/meeting/103/proceedings/
A
Hello,
everyone
welcome
to
the
second
tutorial
in
this
room
and
the
time
slot
in
which
the
third
and
the
fourth
tutorial
take
place
of
this
I
80,
f,
103
and
Bangkok.
Welcome
everyone
to
Bangkok,
I
am
Niels,
don't
be
afraid.
I
won't
be
giving
the
tutorial
but
I'm
a
member
of
the
edge'
team
and
with
the
edge'
team,
we're
trying
to
help
newcomers
and
everyone
in
the
IETF
get
to
know
other
parts
of
the
IETF
and
have
it
to
be
and
a
nice
experience
for
everyone.
A
So
we
do
this
tutorial
these
tutorials
every
time
and
we
want
them
to
make
it
as
them
as
useful
as
possible
for
you,
so
we
will
be
sending
on
the
attendees
list
a
survey.
So
if
you
could,
please
fill
it
in
and
tell
us
what
you
thought
about
about
the
presentation.
That's
that's
coming
up,
but
also
feel
free
to
email,
us
with
suggestions
for
tutorials
that
you
really
would
want
to
see.
They
say.
A
I
won't
take
much
more
of
your
time,
but
if
you
have
questions
and
stuff
feel
free
to
approach
me
or
other
people
of
the
education
Directorate
in
the
hallways
or
find
us
on
the
edge
we
team
wiki,
which
you
can
find
in
the
data
tracker
and
now
without
further
ado
and
introduc
introduction
to
the
intimate
area
by
Pascal,
tibia
Pascal,
who
is
pronouncing
a
surname
much
better
than
I.
Do.
B
B
If
you
don't
know
this
application,
there
is
a
nice
application
for
your
phone,
the
ITF
application.
With
this
you
can
schedule
your
meeting
select
when
you're
going
to
meet
so
attend
which
meeting
and
you
will
find
that
right
after
this
talk,
there
is
a
newcomer,
quick
connection
and
it
will
be
in
garden
at
Queen's
Park.
So
a
lot
of
people
from
many
areas
will
be
there
and
ready
to
answer
your
questions.
That's
actually
where
we
meet
and
greet
and
and
welcome
new
people.
B
And
so,
if
you
have
any
question
about
one
of
the
working
groups,
I
mean
I
will
be
talking
about
or
Suresh
will
be
talking
about.
Then
please
attend
again
it's
in
Queens,
Park
garden
at
Queen's
Park,
so
it
can
be
nice,
usually
there's
food
and
drinks
right.
So
at
least
one
good
reason
to
come,
and
yes,
we
will
answer
any
of
your
questions
with
this.
Here
is
the
program
for
today,
and
maybe
I
will
sit
here
so
I
can
redo
something.
B
Usually
there
is
a
pink
square
somewhere,
because
there's
a
camera
and-
and
you
need
to
stay
on
as
you
speak
near
the
inside-
the
pink
square
so
get
used
to
that.
So
first
thing
I'm
gonna
do
is,
is
for
the
newcomers
reposition,
the
ietf
versus
authorized
use
and
how
we
operate,
because
not
all
the
standard
defining
organizations
operate
the
same
way.
B
B
It's
not
it's
just
my
selection
right,
it's
not
the
best
working
group
or
whatever,
but
they
have
made
the
selections
of
selection
of
working
groups
that
they
want
to
light
Twilight
before
we
deep
dive
into
each
of
them,
and
that's
because
I
used
them
to
illustrate
that
not
all
the
working
groups
function
exactly
the
same
way.
They
don't
all
have
to
deal
with
the
same
kind
of
primes,
and
so
every
working
group
may
have
a
distinct
and
interesting
crowd
so,
depending
on
what
your
interests
are
well
we'll
go
through
that
and
you'll
see.
B
Then
then,
yes,
we
have
the
more
existed
list
of
all
the
working
groups
and
what
they
deal
with
and
I
hope.
We
don't
spend
too
much
time
on
that,
because
you
can
find
it
on
the
web,
etcetera
and
then
we'll
go
through
the
important
links
and
you'll
see
that
the
ITF
website
is
really
well
built
and
easy
to
follow.
So
I'll
show
you
for
that
and
then
questions
etc.
B
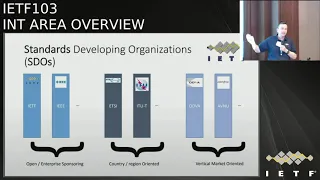
So
the
first
thing
I
wanted
to
show
is
that
you
know
I've
been
participating
to
a
number
of
these
guys
and
I
realized
don't
operate
the
same
way
at
all.
There
is.
There
is
a
category
that
we
call
open
standards,
usually
like
ITF
and
I
Triple
E
and
in
those
kind
of
standard
organizations
people
can
come
as
themselves
and
and
they
can
talk
as
they
want.
There
isn't
a
chip
reader.
They
still
need
to
announce
what
the
affiliation
is
like.
I
work
for
Cisco,
but
still
it
is.
It
is
a
personal
representation.
B
You
speak
for
yourself
and
it's
not
backed
by
countries
or
by
political
organization
or
your
graphical
organization.
It's
it's
mostly
backed
by
companies
which
are
worldwide
I.
Take
that
as
a
difference
between
an
organization
like
@cn,
itu-t
itu-t
is
really
led
by
governments.
I
mean
the
government's
some
people
to
to
to
the
meetings
and
the
local
interests
are
being
served
here.
Etsy
serves
mostly
the
European
zone
with
which
EPP
etc.
Even
if
some
of
the
standards
can
be
spread
larger.
B
So
this
the
second
type
of
category
as
more
regional
and
I'd,
say
state
interest.
Where
has
ITF
and
I
Triple
E
have
more
global
and
I
would
say
corporate
interest,
and
then
there
is.
There
is
a
third
category
which
is
more
like
Alliance.
You
know
like
the
Wi-Fi
Alliance
Oda
Avenue
Oh
Divya
is
for
industry,
OAuth,
newest
audio
video.
You
all
know
Wi-Fi
those
alliances
are
more
vertical.
B
Wi-Fi
is
a
bit
different,
but
DVF
knew
they
really
serve
the
interest
of
a
particular
vertical
industrial,
audio
video,
and
so
you,
you
will
find
again
corporations,
mostly
it's
not
by
state,
but
it's
really
focused
for
particular
class
of
business.
So
with
the
ATF
kind
of
provide
components
and
they
Triple
E
provide
components
that
can
be
integrated
in
standards
that
those
guys
build.
They
will
build
a
full
stack.
B
Okay,
you
know
this
was
supposed
to
be
an
animation.
Yes,
so
that's
maybe
I
should
have
used
mine,
okay,
so
yeah
your
Rd.
If
you
can,
if
you
don't
know
the
PowerPoint,
then
you
will
see
the
animation,
but
the
bottom
line
is
the
areas
at
the
ATF
kind
of
resemble
the
usual
stack.
You
know
that
we
have
defined
this
five
layer
stack
with
with
the
physical
link,
layer,
IP,
layer,
transport,
an
application,
and
you
find
kind
of
the
stack
represented
for
the
layer.
B
B
B
B
Application.
Real-Time,
that's
where
Co
find
sense
for
the
LUT
but
HTTP,
which
is
the
HTTP
beast.
Now
we
are
working
on
the
next
generation
of
HTTP
transport,
so
your
used
of
TCP.
Obviously
it
came
from
here
now
we
are
working
on
MPT
CP
multi
pass
TCP,
so
you
can
have
multiple
paths
being
used
in
parallel
for
TCP
session,
and
there
is
also
this
new
effort,
quick,
which
allows
you
to
build
sessions
of
our
UDP.
B
B
And
last
but
not
least,
we've
got
the
routing
area
which
I
can
of
position
that
layer
three.
This
is
where
all
the
routing
protocols
are
being
designed.
That's
where
BGP
was
designed,
OSPF
was
designed,
and
now
we
have
LS
all
which
is
kind
of
merging.
The
photon
is
a
yes
I,
know
SPF,
but
those
protocols
are
still
alive
and
then
there
is
also
a
listed
spring,
which
is
a
kind
of
a
recent
effort
for
doing
so
swatting.
B
We
call
it
signal
routing,
that's
how
you
can
reroute
some
flows
through
different
paths
to
make
sure
that
you
don't
find
since
you
go
around
the
prime
or
you
don't
conscious
congestion,
the
middle
of
your
network,
so
these
are.
These
are
the
main
areas
of
the
VHF
and
in
my
slides
kind
of
hidden,
you
can
see
the
number
of
working
groups,
they
don't
have
the
same
number
of
working
groups.
Actually
art
is
the
biggest
one.
They
have
29
working
groups
and
that's
why
they
have
three
area
directors.
B
It
is
kind
of
big,
but
we
still
have
only
two
IDs
that
so
you
kind
of
the
most
loaded
IDs.
That
is
worth
a
thing
in
there
when
writing
to
have
more
than
twenty
there
380s
the
most
loaded
might
be
management
know.
Well,
we
have
second
best
something
like
that
very
loaded.
That's
what
it
means.
Then
we
have
this
area
sure,
but
it's
more
like
a
management
tool
right.
We
have
to
work
in
work,
that's
how
we
prepare
for
the
meeting
etc.
So
it's
kind
of
this
one
is
very
special.
B
That's
why
I
put
it
on
the
side
so
driving
down
the
internet
area.
So
I
said
we
are
looking
at
the
IP
layer
technologies
or
the
fundamental
protocols.
Ipv4
ipv6,
DNS
DHCP
I
see
the
base
of
ICMP.
Although
the
basic
building
blocks
that
you
know
about
in
the
IP
stack
are
defined
in
the
internet
area.
Same
goes
for
mobile
IP
EMM
distributed
mobility,
hip
I
would
mention
it.
B
Then
we
also
try
to
make
management
easier
for
how
networks
that's
why
we
have
this
special
working
group.
They
will
mention
why,
if
any
particular
interesting
so
come
back
to
home
net,
defining
how
you
make
the
network
at
home
like
multi,
subnet
home
network,
then
we've
got
all
audio.
You
should
know
if
I
PB
for
ipv6,
so
it's
mostly
six-man,
but
you
also
have
software
which
allows
you
to
build
tunnels
for
visitor
of
a
v6
obviously
summer
before
you've
got
all
the
IOT
at
layer
3.
B
So
that's
that's
where
the
the
fact
what
we
call
IP
over
foo,
what
we
mean
by
IP
over
foo,
is
or
you've
got
this
collection
of
different
link
layers
for
urns,
for
instance,
for
IOT
networks.
Well,
they
are
the
food
IP
overflow,
so
you
have
IP
over
I,
don't
know
Bluetooth
Low
Energy!
You
have
IP
over
I
to
do
that.
B
15
for
IP,
over
foo
and
6,
low
and
and
LP
1
are
the
places
where
those
foods
the
IP
of
foods
are
being
defined
and
then,
finally,
the
int
area
is
where
the
work
on
time
is
happening,
and
you
will
see
that
my
conviction
over
time.
The
network
will
be
your
source
of
time
as
you
connect
to
a
network.
We
don't
do
it
yet
fully,
but
soon
enough,
when
you
connect
to
the
network
before
you
do
anything,
you
already
get
a
sense
of
time.
That's
how
we're
going
to
make
the
network
deterministic!
B
That's
how
we
are.
We
are
going
to
simplify
the
routing
protocols
because,
if
we
add
a
sense
of
time,
a
lot
of
things
in
writing
would
be
a
lot
easier,
so
tick,
tock
and
network
time
protocol
a
protocol
are
ready
to
time
and
they
are
in
the
interior.
I
expect
that
to
grow
time
will
become
more
and
more
important.
They
are
too
and
a
classroom,
so
here
I
give
a
more
complete
list.
So
you'll
have
to
go
through
this
slide,
but
also
that'sthat's
easy
to
find
on
IETF
data
tracker.
B
So
the
first
one.
You
know
it's
kind
of
the
king
of
working
groups,
kind
of
because
that's
where
ipv6
is
being
defined
that
six-man,
so
it
used
to
be
called
ipv6.
But
now
it's
6-man
because
it's
supposed
to
be
maintenance.
Okay,
so
maintenance
saying
you
know:
v6
was
defined.
Let's,
let's
tune
it,
let's
fix
it,
but
not
change
it
too.
Much!
That's
kind
of
the
idea
behind
maintenance.
B
Actually,
the
biggest
thing
that
has
happened
in
six-man
is
the
publication
of
RFC
6200,
which
is
the
the
internet
standard
version
of
Alex,
so
you'll
find
that
we
have
degrees
of
standardization
at
the
IDF
and
the
the
is
degree
when
we
are
really
sure
here
is
the
standards.
Everything
is
quote,
unquote
perfect
in
it.
That's
when
we
reach
the
level
of
internet
standards
that
we
don't
have
many
internet
standards.
Ipv6
became
like
one
last
year
or
the
year
before
became
an
internet
stuff.
Last
year
became
an
Internet
standard
with
six
200.
B
Because
it
is
fundamental,
fundamental
tool,
people
are
very
sensitive
to
the
evolution
of
ipv6,
so
six
men
as
this
quote-unquote
political
dimension
in
it,
where
some
people
will
say
a
you
can't
change
the
protocol.
People
are
deploying
it
they
don't
want
to.
They
want
to
feel
the
protocol
that
deploying
this
table.
We
really
need
to
be
conservative
about
what
we
do
at
six.
Man
and
other
people
will
say
a
if
you
don't
evolve.
You
die
the
world
is
changing.
B
Ipv6
was
initially
designed
ninety-eight,
it
has
to
evolve
with
the
world
so
as
to
to
still
be
aligned,
so
those
two
forces
will
be
fighting
at
six
men
and
that
that's
a
very
interesting
tension
and
very
fruitful
some
time
when
sign
winds.
You
know
that
some
other
times
the
other
side
wins,
and
there
are
examples
of
where
the
evolution
is
happening,
for
instance,
segment
trotting.
That
was
discussing
area
which
will
have
to
change
the
way
ipv6
works
in
sixty
two
hundred.
B
There
was
also
this
discussion
about
headers
sorry,
iti
shower
6268
off
eight,
two:
zero,
zero,
sorry!
So
yes,
bhai
night!
Now
so
in
in
in
ipv6.
Now
you
will
see
that,
for
instance,
the
hop-by-hop
header
is
is
rewarded.
It's
not
a
strong
standard
that
it
used
to
be.
You
can
ignore
it
now.
I
shall
retire
in
the
middle
of
the
internet,
so
things
have
evolved
compared
to
the
earlier
24
16.
B
So
that's
the
political
dimension
and
I
think
it's
kind
of
unique
to
this
working
group
and
it's
a
it,
creates
a
very
interesting
tension.
Another
aspect
which
is
kind
of
unique
to
six
men
and
spreads
on
the
other
groups,
which
was
ipv6,
is
all
these
I
would
say:
sociological,
father,
lack
of
a
better
world.
We
have
to
care
about
how
the
society
uses
the
IP
versus
the
ipv6
addresses
and
now
at
least
to
two
angles,
which
are
very
important.
The
first
is
privacy.
B
If
you
keep
using
a
same
IP
address,
then
people
can
track
you
on
the
Internet.
So
we
won't
addresses
that.
Don't
allow
people
to
track
you
if
you
don't
want
to
be
tracked
as
soon
as
you're
going.
So
this
creates
a
whole
set
of
new
requirement
to
ipv6
and
6-man
has
been
dealing
with
that.
Another
attention
which
is
kind
of
interesting
ears.
B
The
tension
between
I
would
say,
your
hippie
user
wants
to
be
able
to
form
any
addressee
lights
in
any
network
yield
and
the
outside
the
copyright
administrator
network
admin
wants
to
see
who's
logged
way
up
with
which
address.
So
there
is
always
this
tension
between
the
ipv6
desire
of
total
freedom
and
the
copyright
desire
of
knowing
what's
going
on
in
my
network.
So
this
also
has
impact
on
the
definition
of
the
protocol.
And
finally,
there
used
to
be
this
group
called
savvy.
B
Now
it's
disbanded
but
kind
of
six
men
now
we'll
have
to
do
the
maintenance
for
it.
It
means
sauce,
address
validation.
It
means
oh,
if
somebody
has
a
certain
address,
can
somebody
else
use
that
address
did
from
him
a
supposedly
not,
but
with
the
base
ipv6
protocol
it
was
kind
of
heap.
Everybody
can
use
everybody
else's
stuff.
Now
we
want
to
actually
protect
you
on
the
network
to
ensure
that
if
somebody
forms
an
address,
okay
may
be
free
to
form
that
address.
B
But
when
it's
done
it's
easy
trust,
nobody
else
can
come
and
intercept
the
packets
and
the
other
way
around.
If
you
want
to
use
an
address-
and
it's
not
the
politically
correct-
you
should
not
be
allowed
to
do
that.
Okay,
so
it's
more
matter
of
poor
police.
Now
so
within
politics
we're
doing
sociology-
and
we
are
doing
please
and
it's
so
it's
all
those
aspects
actually
chairs
the
protocol.
There
are
number
of
heresies
which
are
which
are
still
happening
about
how
you
control
PVC,
without
changing
the
basic
header
or
anything.
B
We
are
really
changing
the
way
it
can
be
used
in
the
world.
So
that's
six
man
I
mentioned
six
UPS.
Six
UPS
is
not
in
the
interior.
I
told
you
it's
in
the
ops
and
management,
but
he
still
very
interesting
because
it's
the
counterpart,
it's
the
feedback
loop
to
six
pad.
That's
the
real
world
coming
back
at
ipv6
and
say:
okay,
the
results
deployed
this
works.
This
doesn't
work.
B
B
There
are
more,
but
I
pick
those
two,
because
they
are
the
IP
above
who,
as
I
said
before
another
aspect
of
what's
happening
here,
since
we
are
a
are
three
the
earlier
tools
and
now
the
working
group
which
the
area
which
is
facing
the
leaders-
and
there
are
many
of
them,
mostly
with
the
IOT
there
are
tons
of
various
radios
that
different
property.
The
way
you
do
ipv6
of
array
over
them,
the
way
you
for
mattresses,
for
instance,
the
way
your
encrypted
well,
you
encode
the
packet
for
compression
all
this
varies
with
the
food.
B
So
initially
you
know
it
was
ipv6
of
ice
on
that
down
Wi-Fi
easy
from
that
down.
Ok,
Wi-Fi
is
not
Ethernet,
that's
one
thing
and
it
appears
now.
Yes,
the
network
gets
bigger
at
such
rad.
The
difference
between
Wi-Fi
and
and
ethernet
appears
the
point
that
we
may
have
to
look
at
ipv6
how
it
works
on
Wi-Fi
and
then
all
those
other
networks
I
just
listed.
The
number
of
them
is
not
even
a
complete
list,
so
you
see
so
Bluetooth
Low
Energy
back
net,
which
is
for
buildings.
B
Your
field
power
line
using
the
well
wires
z-wave.
It's
radio
for,
like
I,
think
a
two
2.15
floor.
That's
the
radio
used
by
ZB
by
thread
by
60s,
actually
low
one
low.
It's
a
wide
area
network,
low
power,
wide
area.
So
it's
a
few
bits
per
second
and
of
sick
fox
in
the
same
family
and
be
IOT,
is
a
bit
more
powerful,
but
still
in
the
low
power
wide
area
networks.
So
those
out
the
working
groups
where
all
those
things
happen,
meaning
that
the
crowd
in
the
room
will
be
different.
B
You
will
have
a
lot
of
people
specialize
on
their
radios,
people
who
have
never
heard
about
IP
in
the
first
place
and
and
we
pull
them
in
so
that
they
get
interest
in
the
ITF,
and
we
come
back
with
solutions
that
you
can
use
across
this
technology
so
that
are
interested
in
using
them.
For
instance,
LP
one
is
defining
a
compression
and
the
fragmentation
which
can
be
used
in
all
three,
but
at
the
moment
I
was
emitting.
Aloha
Alliance
meeting
in
Tokyo
like
last
week
and
they
were
discussing
about
using
our
fragmentation,
follower.
B
B
This
is
a
unusual
traffic
in
that
it's
mostly
coming
from
the
mathers
all
the
way
to
to
the
application,
but
not
the
other
way,
and
when
it's
going
the
other
way,
it
has
a
very
special
shape
like
it's,
you
have
to
reflash
the
device,
so
this
create
roots
creates
an
imbalance
in
in
what's
going
on
and
that
can
be
leveraged
to
improve
the
compression
of
the
protocol.
For
instance,
she
know
what
kind
of
traffic
goes
from
for
how
you
you.
You
allocate
your
bandwidth
in
your
network
as
we
go.
B
We
realize
that
some
basic
operations
of
I,
like
ipv6
neighbor
discovery,
is
not
appropriate.
Neighbor
discovery
uses
broadcasts,
always
right.
So
it's
it's
using
a
lot
of
broadcast.
When
you
have
a
low-power
radio,
it's
a
match.
You
don't
want
to
broadcast
the
message
time,
you're
looking
for
a
meter,
so
you
have
to
redefine
and
we
are
doing
it
really
finding
ipv6
neighbor
discovery,
which
is
really
a
core
building
block
of
ipv6.
If
you
look
at
it
and
two
big
building
blocks,
one
is
addressing
how
you
form
addresses
and
the
other
one
is
neighbor
discovery.
B
B
B
We
are
already
trying
to
build
a
meta
RFC,
an
RFC
of
RFC's,
because
there
are
like
more
than
8,000
ever
seen
in
the
IETF
and
dusarian
sees
usually
that
composed
of
people
who
never
came
to
the
80s,
and
they
want
to
be
out
a
new,
a
ot
type
of
network
for
industrial
and
and
they
look
at
it
and
say
ooh
out
of
those
8,000
RFC's.
What
should
I
do?
Which
one
should
I
take
the
and
there
is
a
consortium
which
tried
to
as
cosy
VIP
they
wanted
to
do.
B
Is
it
be
for
electrical
for
your
H
kilometers,
and
so
they
came
to
the
HF
many
times
and
they
ended
up
building
this
that,
based
on
RFC's
from
the
interior
overseas
from
the
rotting
area
RFC's
from
the
observer,
and
they
tried
to
put
that
together.
It
was
an
immense,
a
frost.
I
did
know
it.
It
didn't
work
very
well
because
we
realized,
as
we
did,
that
that
those
components
that
we
produced
in
the
various
area
areas
did
not
really
fit
together.
B
So
the
effort
in
six
dish,
okay,
was
defined
for
a
particle
of
5080
2.15
for
mac,
but
three
most
of
the
work
happens
at
layer
3.
We
are
in
the
interior
and
the
questions
re.
How
can
I
build
a
solution
like
like
a
big
RFC
of
Arab
seas
so
that
all
those
alliances
that
was
talking
about
could
adapt
IETF
protocols
more
readily
and
and
and
there
are
we
three
things
that
that
we
did
in
this
working
group?
One
of
them
was
to
define
architecture
which
says
okay.
This
protocol
is
here
it
connects
with
that.
B
If
the
flows
are
redundant,
there
is
which
one
you
pick.
For
instance,
the
routing
protocol
could
be
something
that
nd
is
also
doing,
which
one
and
B
of
that
solution
propose
it
and
at
the
same
time
we
are
finding
gaps
and
60s
has
been
pushing
work
in
six
low
enroll
so
that,
at
the
end
of
the
of
the
story,
the
picture
is
complete,
the
gaps
are
filled
and
overlaps.
Well,
a
selection
is
made
on
which
of
the
overlapping
technologies
being
used
for
a
particular
case.
So
this
is
this:
what
happened
at
the
IETF?
B
At
the
same
time,
we
had
open
source
activities
and
we
have
two
open
source
tags,
which
kind
of
which
are
built
on
this
architecture
and
we
interrupt
them
as
a
third
component,
so
we
have
ad
C
actually
acting
helping
us
doing
all
the
interrupt
tests.
So
we
have
a
real
ad
structure
for
doing
interrupts.
We
have
open
source
code,
then
we
have
the
IETF
meet
RFC
and
with
that
we
prepare
this
special
bundle.
So
you
see
it's
not
classical
working
group
building.
B
Several
heresies
small,
like
how
do
I
make
all
those
Eris's
work
together
for
are
you
cheaper
process?
So
it's
kind
of
interesting
I'm
net
is
a
bit
like
that
they
they
are
building
a
home
network.
Here
we
are
building
an
IOT
network.
So
how
should
my
home
network
operate
so
that
my
grandma
can
never
submitted
network?
And
she
doesn't
understand
anything
about
network
has
to
be
automated.
So
that's
why
I'm
that
is
so
interest
as
well.
B
Each
time
you
we
still
have
to
define
a
few
RFC's,
because
there
are
holes
which
don't
belong
to
other
working
groups,
so
we
have
to
take
them
home,
but
you
see
that
most
of
the
work
is
actually
to
study
how
that
works
and
and
providing
the
big
picture
that
that
actually
works,
and
you
want
me
to
do
it.
You
want
to
do
it.
Ok
little
pose.
This
is
the
time
for
the
drink
and
for
the
deeper
dive
into
all
those
working
groups.
B
I'm,
just
out
of
my
lane,
I
didn't
have
a
chance
to
go
to
my
room.
Yet
there
we
go
so
we
have
like
I,
said
16
working
groups
at
the
in
the
interior
right
now,
so
he
goes
for
the
60.
Ok,
just
to
give
you
an
idea
of
what
they
do,
but
you
had
the
big
picture
already,
so
we
go
so
this
is
this
is
how
actually,
several
years
ago,
Suresh
sorted
them.
B
They
used
to
be
very
in
stable
that
we
used
the
new
areas
and
then
disband
them
and
from
new
areas,
but
over
the
course
of
the
like
10-15
years,
the
areas
that
the
IDF
has
been
very
I've
been
very,
very
stable,
but
the
working
groups
inside
the
area
change
what
I
mean
working
group
last
like
four
years,
maybe
five
some
lasts
lasts
more
like
six
men,
but
usually
that
there
is
to
come
and
go
depending
on
the
needs
of
the
day.
So
we
have
those
really
to
time
which
is
kind
of
a
very
special
sort.
B
B
Now
we
just
have
software
which
we
belongs
to
there,
but
I
kind
of
put
six
men
in
there
too,
because
that's
everything
which
has
been
done
5p,
v6
and
which
is
complete
kind
of
ends
up
being
maintained
by
six
men
and
we'll
go
through
all
the
other
Interior
is
a
bit
special
you'll
find
that
each
area
has
its
own
working
group
for
general
purpose.
Everything
that
fits
to
the
area
but
not
to
an
existing
working
group
can
be
proposed
to
the
interior.
So
we
do
a
rough
season
tint
areas.
B
Well,
we've
got
mobility
related,
look
everything
which
derives
from
over
IP
I
placed
IP
wife
there,
which
is
IP
for
vehicles.
They
are
not
doing
mobile
IP,
but
I
did
not
know
where.
To
put
it,
it's
not
really
power.
It's
kind
of
related
to
mobility
and
related
to
low
power,
but
you
know
saying
that
the
car
is
low.
Power
is
a
bit
in
exaggeration,
so
so
I
place
it
yeah,
and
there
is
another
angle
that
Suresh
put
together
and
I.
Really
like
you
seek
enough.
B
You
know
the
evolution
that
the
working
groups,
which
just
appear
the
most
recent
one
of
those
two
IP
wave
and
look
up
our
wide
area
networks
and
resent
our
DNS
SD.
So
it's
DNS
across
an
ultra
Network
well
and
I,
said
borschov
like
across
a
larger
network
beyond
the
subnet,
then
you
see
mobility
management,
six
male
places
straight
in
the
middle
and
here
to
stay,
and
then
you've
got
others
like
like
this.
B
B
Have
you
heard
about
six
Lipan
right
and
a
bit
that
so
6lowpan
is
how
you
do
ipv6
of
a
constraint
networks
like
a
$2
15
for
initially
low
pan
itself
without
the
the
six
is
the
nami,
the
denomination
by
I
Triple
E
are
fated
to
dock
15,
for
so
it
was
really
I
P,
six,
a
vital
to
the
15th
floor.
So
we
delivered
six
lap
and
6lowpan
neighbor
discovery,
which
is
the
first
attempt
at
doing
this
registration.
B
We
see
that
there
is
this
new
generation
called
the
power
ID
area
which
are
so
strict
that
the
contrary
fit
in
the
same
class
as
6lowpan,
and
so
we
could
not
reuse
the
techniques
that
are
developed
for
all
those
those
technologies.
So
we
formed
a
different,
workable,
different
crowd.
Attending
different
RFC
is
being
produced.
We
formed
a
different
direction
at
some
point.
You
can't
feel
everything
into
six
low
settings
low
power.
B
B
So
six
month,
I
went
through
it.
It's
it's,
it's
maintaining
everything
that
all
the
stack
of
affair,
FCS
that
we've
done
in
the
past
and
more
interestingly,
it's
also
turning
the
oldest
history
and
this
knowledge
that
we
built
across
all
those
RFC's
into
internet
standards,
and
we
have
Bob
in
the
room
here
who
is
highly
responsible
for
that?
So
so,
basically,
we
are
way
to
200,
and
now
we
love
all
the
the
rest
of
the
core
family
of
ipv6,
I,
guess
turning
into
internet
standards-
and
that's
that's
six
men
doing
it.
B
B
In
this
case,
it's
8:02
that
15
4
T
SCH,
meaning
time
slot
each
other
happy
time
so
T
generating
is
very
interesting
because
at
the
Mac
layer
is
cotton
code,
deterministic,
meaning
that
you,
you
basically
catch
your
your
radio
in
frequencies
and
time,
and
you
allocate
a
cell
in
that
matrix
to
a
particular
transmission.
So
you
actually
build
a
schedule.
Just
like
your
3gpp
will
build
a
schedule
where
you
have
a
particular
resource
block,
and
so
15
follows
you
to
do
that,
and
what
60
does
is
build
this
this.
B
This
stack
of
of
IOT
protocols
over
this
particular
block,
so
that
there
was
some
there
were
some
components
which
were
needed
at
the
intersection
of
really
layer
2
which
we
built
in
6
and
we'll
probably
push
them
to
a
triple
because
they
kind
of
belong
to
low
area.
At
the
time.
15
thought
did
not
really
have
an
analysis,
so
this
thin
layer,
which
is
about
above
the
Mac
and
the
right
which
we
adapt
to
to
this
particular
Mac.
There
was
nothing
for
1548
reply.
We
need.
B
Nevertheless,
60
she's
mostly
done
for
at
least
its
current
goals,
and
we
are
completing
our
round
of
RFC's
I,
don't
know
if
we,
which,
after
prob
it's
going
to
be
a
different
default
for
for
deterministic
flows
and
I'm,
trying
to
adjust
that
60s
did
non-deterministic
IP
so
best
effort.
If
you
like,
statistical
max
IP
over
a
deterministic
Mac,
while
you
schedule
the
next
generation
with
scheduled
at
both
layers,
so
you
can
read
no
deterministically
what
goes
where
and
now
you
can
do
more
strict
protocols
like
control,
loops
and
Industry,
or
things
like
that.
B
60
is
still
traditional
IP
over
this
map,
so
you
can
take
a
60
stack,
put
it
on
a
different
back
layer.
Guess
what
ax
is
now
producing
this
OFDM
a
which
can
actually
map
the
time
slots
in
6?
So
if
you
take
what
ax
calls
the
ticks
up,
it
would
be
a
slot
the
time
slot,
and
if
you
use
this
software
DMA
sub
channels,
you
can
actually
map
them
to
60
channels,
channel
status
column.
The
result
of
that
is
whatever
we
design
in
60.
B
A
15-4
could
actually
be
ported
on
Wi-Fi
in
the
new
X
generation.
Make
sure
we
I
will
be
talking
to
Wi-Fi
next
week
about
that,
so
that
you
know
we
do
it
like
a
set
for
one
particular
MAC.
6
weapon
was
done
for
one
particular
Mac,
but
the
goal
is
to
be
able
to
port
it
on
different
Macs
and
get
the
same
result.
Automatic
automatic
on
we
can
th,
see
I
mean
who
knows
about
DHCP
I,
guess
everybody
has
heard
about
it.
It's
hard
to
work
on
IP
without
hearing
about
the
HDD.
B
So
it's
been
there
for
like
a
lot
years,
yeah.
So
incredible
so
still,
tasks
for
doing
work,
because
the
more
you
want
to
provisioning
way
through
DHCP.
Well,
the
working
group
gets
providing
that
so
DHCP
is
still
very
much
alive,
distributed
mobility
management,
so
this
inherits
from
generations
of
work
starting
at
Mobile
IP.
B
So
mobile
IP
had
this
concept
of
a
home
agent
which
made
it
so
that
a
particular
mobile
router
would
build
a
tunnel
to
where
it
should
be,
which
is
his
home
and
the
packets
from
the
internet
would
theoretically
go
to
to
where
I
should
be,
and
then
turn
out
from
this
home
to
why
you
are
that's
mobile
IP
in
the
nutshell.
But
the
problem
was
this
anchor
this
local
anchor,
which
was
your
home
agent
with
DMM?
We
can
distribute
it.
B
So
it's
like
when
you're
roaming,
with
your
phone,
you
you're
capable
now
for
touching
while
you
are
had
builder
called
tunnel
as
opposed
to
a
global
tuner
back
home,
so
DMM
is
still
very
much
alive,
been
there
for
a
while,
because
it
inherits
from
work
which
we
did
in
the
early
2000.
So
this
is
the
continuation
of
Nemo
of
yeah
yeah
mix.
It
mix
a
extend
Nemo,
then.
What
was
this
P
me
up
herself
that
X,
which
is
completed?
So
it's
a
continuation
of
working
Rob.
Sometimes
you
reach
out
our
working
group.
B
Sometimes
we
say:
oh,
this
is
redone,
but
there
is
a
continuation
to
be
made
like
six
load
was
read,
not
6lowpan,
because
there
was
no
we
ban,
but
we
still
have
work
to
do
so.
Dmm
is
taking
this
to
distribute
the
homage
and
kind
of
the
anchor
so
dns
SD
is
the
continuation
of
mdns
module
to
basically
enable
to
discover
something:
a
service
but
not
limited.
B
Now,
to
look
on
network
earlier
to
network,
a
broadcaster
made
the
capability
to
actually
look
at
beyond
your
per
customer
so
that
that
has
huge
number
of
very
interesting
news
cases
as
soon
as
your
network
grows.
But
you
want
to
be
able
to
discover
I,
don't
know
a
video
or
something,
but
it's
not
on
your
local
subnet.
Today,
you're
screwed,
you
can't
find
a
printer
which
is
not
another
consummate,
so
deprived
deprive
is
about
securing
DNS
I,
don't
know
much
about
it.
C
Yeah
so
suresh
krisshnan
on
the
internet
80
like
responsible
or
some
of
the
groups
there,
and
so
this
is
like
pretty
much
for
providing
confidentiality
for,
like
your
dns
queries
because,
like
the
dns
queries
like
leak,
a
lot
of
information
and
the
idea
is
to
minimize
the
information
exposure
due
to
dns
query.
So
that's
what
this
working
group
is
trying
to
do.
B
It
has
been
there
forever.
I'm
surprised,
it's
still
there,
so
it's
all
about
separating
the
naming,
the
identity,
piece
of
an
IP
address
and
the
locally
the
localization
piece
of
you
dress.
Now
you
have
two
addresses
one
which
says.
While
you
are,
and
one
which
says
who
you
are.
The
interesting
thing
is
when
you
talk
hip,
the
upper
stack
says
who
who
doesn't
recap
where
now
if
the
people
are
moving,
actually
there
is
a
mapping
in
the
hip
layer
of
somewhere
under
the
transport
which
which
maps
this
who
who
into
a
where?
B
Well
that's
how
the
packets
gets
to
where
I
am
to.
Where
you
are
so,
you
can
move,
I
can
move,
they
can
move
separately
and
each
time
that
the
mapping
is
updated.
So
the
basically
the
discussion
can
continue.
So
it's
a
variation
of
map
without
a
hunker
kind
of
interesting
model,
but
it's
like
maple.
You
have
not
seen
that
it's
deployed
anywhere
so
surprises
the
other,
but
still
they're
alive
and
kicking
home
net,
so
home
net
formed
to
enable
multi,
subnet
home
networks.
So
it's
kind
of
a
complex
technology.
B
B
I
mean
it's
really
kind
of
a
vision
and
why
don't
have
IP
subnet
they
ever,
maybe
because
I
would
have
to
configure
that
set
them
up
and
I
don't
want
to
go
ahead
and
do
that
and
then,
when
I
move
by
in
TV
or
my
laptop
from
a
room
to
another,
I
have
to
remember
my
laptop
now
right
not
doing
that
now
with
home
that
all
all
those
would
be
behind
the
scenes.
So
you
would,
you
would
benefit
from
you
know
the
broadcast
domain.
B
Isolation
number
of
things
that
you
will
get
from
watching
like
you
can
like
security
isolation.
You
can
have
your
IOT
prefix,
because
you
don't
trust
the
devices
have
some
rules
between
network
and
otherwise
you
like
to,
but
it
will
all
be
automated.
So
one
of
the
protocols
that
home
that
has
done
is
how
do
I
go
ahead
and
discover
my
writers
and
assign
them
prefixes,
so
you're
actually
automatically
subnet
your
network.
B
So
your
service
provider
would
give
you
I,
don't
know
/
48
and
he
and
I'm
that
would
automatically
configure
all
your
writers
with
/,
64
and
right
between
them,
etc.
So
you
get
you
get
the
magic
of
layer
2,
it's
it
all
works
with
the
benefit
of
the
last
row,
so
it's
defined
in
the
context
of
home.
Some
of
the
protocols
could
apply
beyond
that
encompass
or
whatever,
but
start
low.
Just
like
they
said,
six
weapons
started
on
fitting
for
Hamed
starts
at
home
right,
starting
at
home,
hi
py.
B
If
that's
one
of
the
newcomers,
so
IP
wife
is
about
vehicles
and
you
see,
if
you
follow
what's
happening
in
cars
and
I,
you
see
you.
You
will
see
that
the
next
generation
of
cars
are
going
IP.
There
is
a
huge
IP,
an
Ethernet
that
there
is
you
to
work
at
a
Tripoli
about
Ethernet
on
two
wires
here
and
at
least
ten
megabits
to
start
with,
but
but
they
were,
they
want
to
go
into
the
gig,
Sun
and
IP.
At
the
same
time,
why?
B
Because
by
multiplexing
at
the
IP
layer
you
will
save
wires,
you
will
be
able
to
use
wireless.
If
you
want
to
add
some
points
and
if
you
say
wires,
you
safecast,
you
say
building
and
if
you
see
the
shape
of
the
wiring
in
a
car,
it's
completely
awful,
so
I
think,
first
off
fatlings
and
and
some
switches
inside
the
car
will
save.
You
wait,
that's
gas.
We
save
you,
maintenance,
that's
less
wires!
B
That
can
break
up
unplug
so
that
there's
a
huge
benefit
for
cars
in
going
a
pianist
and
I
think
they
are
all
going
very
very
quickly
to
that.
So
that's
one
angle
of
Phi,
P,
their
IP
wave,
is
more
about
the
the
vehicle
to
infrastructure
vehicle
to
environment.
So,
for
instance,
there
is
this
82
11
P,
which
is
a
new
variation
of
a
2
to
11,
which
allows
you
to
connect
as
you
go
well.
The
model
for
ipv6
neighbor
discovery
cetera
is
not
at
all
meant
for
that.
B
So
right
now
I
appeared
in
the
prime
statement
phase,
but
clearly
you
cannot
use
the
traditional
link.
Model
label
discovery
broadcast
model
of
ipv6
in
that
environment.
So
if
we
really
want
to
bring
LP
in
the
vehicle
to
a
cure
vehicle
to
infrastructure,
we
will
have
to
design
something
novel
in
that
group.
So
very
interesting
thing
what's
going
on
there
and
you
don't
new
comer
is
help.
You
want
loop,
our
wide
area
networks.
Have
you
heard
about
sick
folks,
Aloha
resent.
B
Okay,
so
I
love
this
technology,
so
they
really
have
a
padding,
which
is
so
counterintuitive
that
I
read
of
it.
We
are
used
to
making
networks
faster
and
faster
or
Bo
had
more
reliable.
Those
things
go
completely
the
other
way
they
are
slower
and
slower,
and
less
and
less
reliable,
don't
expect
to
have
80%
of
your
packets
wrong.
It's
just
you
know.
You
sends
a
submitter,
send
some
information
and
price
that
it
gets
there
it's
more
fun
than
not
it
does,
but
you
can't
build
anything
which
would
depend
on
it.
B
On
the
other
hand,
you
can
spread
your
sensor
on
square
miles.
We
just
went
out
to
gateways,
you
can
self
already
a
large
area,
so
it's
free
meant
to
have
a
very
cheap
deployment
of
of
matters
which
will
measure
I
grow.
My
tree,
which
will
meet
your
temperature.
Like
you,
know,
sis
make
variations
on
on
the
dead.
B
Volcano
I,
don't
know
something
which
is
not
critical
but
has
to
be
deployed
on
a
wide
area
at
a
low
cost
and
you
may
or
you
may
have
to
serve
tens
of
thousands
of
sensors,
which
don't
speak
very
often.
So
it's
it's
interesting
because
it's
a
hub-and-spoke
model
compared
to
the
ratio
of
15
fir,
which
does
mesh
meshing,
means
complexity,
means
engineering,
which
means
cost
with
that
you
can
really
have
a
high
throughput
eye
quality
network,
but
those
are
take
completely
taking
the
opposite
way.
B
B
Some
people
are
asking
to
provide
an
ipv4
version
of
what
we
did
for
ipv6
now.
To
be
honest,
the
Sheik
I
cities
doesn't
need
to
be
charged
at
all.
It's
just
matter
of
rules,
so
we
can.
We
can
support
ipv4
with
it.
I,
don't
think
we
need
any
change
in
it.
Support
ipv4,
but
just
if
people
need
ipv4,
it's
not
like.
Should
we
say
no
I
mean
it's
a
question.
I
mean
we.
This
is
for
recovering
right.
We
have
not
reach
out
that
for
that,
but
it
will
happen.
B
C
Get
chartered
at
this
point.
But,
like
you
know,
there's
like
stuff,
we
need
to
maintain.
Ipv4
is
like
just
as
IP
as
ipv6,
so
you
know
we're
not
going
to
shirk
our
responsibilities
to
maintain
like
the
things
that
are
out
there
so
like
we
will
be
continuing
to
do
ipv4
related
work.
So
if
that's
your
question,
but
it's
it's
very
unlikely
that
ipv4
only
work
is
gonna.
Get
charted,
at
least
in
this
area
like
I,
know
and
like
in
art.
C
B
Yes
and
as
I
said
to
compress
ipv6
in
11
bytes
or
something
we
had
to
take
very
strict
measures,
and
one
of
them
is
you
don't
really
see
DLP
at
all
in
the
air,
which
means
that
probably
the
same
device
sending
the
exact
same
bytes
could
be
uncompressing
too
before
all
visits,
because
it's
completely
stateful
on
the
network
side.
So
so
there's.
Basically
the
only
thing
that
turns
could
be
that
the
up
limit
or
something
like
that,
and
even
usually
we
make
even
make
it
a
constant,
but
those
can
be
mapped
in
v4
and
v6.
B
It's
just
matter
of
what
you're
calling
it
the
rest
of
network
nodes,
so
interior,
like
I,
said
this
is
another
one
group
that's
here
to
stay,
because
it's
really
associated
to
the
the
area
itself.
It's
everything
that
doesn't
really
fit
in
a
particular
working
group,
but
is
still
of
interest
for
the
area
at
large
L
week
is
an
implementer,
so
I
should
have
mentioned
it
in
my
examples
of
interesting
working
groups,
because
this
is
yet
another
type
of
arcing
rock.
It's
more
like
implementers
talk
to
implementers.
B
Let's
give
not
deployment
best
best
practice
like
in
v6
UPS,
but
more
implementation
best
practice
and
you
will
find
drafts
which
they
a
you
could
do
it
this
way
it
doesn't
take
any
change
in
the
protocol
RFC.
But
if
you
do
it
this
way,
it's
going
to
work
much
better.
It's
going
much
simpler
to
implement.
You
have
this
trick.
B
If
you
do
know
cryptography
this
way,
oh
you
can
you
can
reuse,
I,
don't
know
you
need
what's
curved
and
and
well
anyway,
you
you
can
reuse
different
curves
by
just
tweaking
this,
and
that-
and
that
says
you
code,
you
have
so
little
space
for
your
code.
There
is
a
trick.
So
all
these
happens
at
their
week.
C
C
So,
like
you
know
some
some
devices
have
like
you
know:
10
kilobytes
of
memory,
for
example,
some
of
them
have
like
100
kilobytes,
we
think
of
them
all
as
constrained,
but
this
different
classes
of
constrained
devices
and
that's
where
we
kind
of
define
those
things
and
there's
also
like
some
cool
bug
going
on
right
now,
which
is,
for
example,
like
TCP
right.
So
how
do
you
do
TCP
unconstrained
devices
like
you
know?
How
do
you
set
the
timers
and
those
kind
of
things?
So
it's
like
really
hard
core
implementation
stuff.
B
In
CPU,
well,
I
guess
you
you
have
time
on
your
phone
and
it's
thanks
to
ntp
cents
before
now
is
the
standard
for
getting
time
across
a
wide
area.
It
won't
be
as
precise
as
1588
defined
by
a
triple
e,
because
the
88
would
be
just
on
this
single
Ethernet
and
then
1588
itself
has
to
be
profiled
based
on
the
use
case.
Have
many
repeaters,
you
have.
Are
you
doing
your
smart
grid
network
or
what
here
it's
generic
for
the
internet,
meaning
that?
B
Obviously
you
can't
get
to
the
very
precise
result
you
could
get
with
a
particular
profile
of
1588,
but
still
you
get
a
very
reasonable
sense
of
time,
like
200
milliseconds
across
the
internet.
So
if
your
iPhone
is
as
time
if
most
of
your
network
after
your
PC
has
time,
usually
it's
because
you
have
NTP
v4
behind
the
scene,
software,
it's
it's
kind
of
fall
now
all
right!
It's
it's!
It's
tunneling
v6
about
v4
viruses
or
v4
v6.
B
Tik-Tok
is
studying
the
new
way.
We
can
do
timing,
an
exchange
time,
I've
rolled.
It's
only
scarcely
I'd,
not
have
much
to
say
about
it.
It's
about
time-
and
this
is
not
a
working
group,
so
we
have
done
through
the
working
rows.
But
there's
there's
also
this.
This
kind
of
cross
working
group
he
fought
people
from
different
working
groups,
actually
contribute
to
the
internet
area
Directorate.
It's
kind
of
Suresh
secret
helpers,.
C
Yeah
so
there's
like
people
who
been
like
chairs
before
they
ordered
a
lot
of
documents,
so
we
kind
of
used
them
to
review
documents.
So,
let's
say
a
working
group
is
ready
to
publish
a
set
of
documents.
So
what
me
and
Terry
who's
Mike
Oh
Eddie.
What
we
do
is
like
we
kind
of
push
a
button
to
get
an
indirect
review
so
before
it
leaves
the
working
group.
So
what
happens?
Is
this
the
experts
who
are
kind
of
Outsiders?
C
So
the
working
group
itself
right
because
they
don't
know
the
exact
technologies
of
the
working
group
but
they're
like
well-versed
in
internet
right
area,
ideas
which
is
like
they
know,
IP
very
well.
They
know,
like
you,
know,
DNA
as
DHCP.
Those
kind
of
things
very
well
so
whatever
I
put
in
at
the
end
of
the
list
is
like
you
know,
reading
required,
reading
kind
of
thing,
so
they're
like
very
good
at
it.
So
the
idea
is
to
find
out
issues
pretty
early
before
it
goes
to
the
whole
IETF
okay.
C
So,
like
you
know,
whenever,
like
somebody
is
an
ad
like
they're
there
for
two
years
or
four
years
or
six
years,
whatever
it
is,
and
the
idea
is
to
find
like
a
pool
of
participants
like
from
there.
Who'll
also
take
on
like
responsibilities
in
the
future,
so
like,
for
example,
like
Pascal,
like
you
know,
it's
like
doing
stuff
there
so
like
the
idea
is
like
when
we
want
to
do
this
overview
like
I
want
somebody
from
there
to
do
it,
so
they
get
like
experience
to
do
stuff
in
the
future.
C
B
B
And
then,
just
because
we
are
like
a
layer,
if
you
remember
my
matrix,
the
the
very
beginning
of
the
presentation,
I
had
this
videos
with
with
free
well
areas,
we
had
internet,
we
had
transport
and
we
had
application,
but
on
the
side
we
also
had
maintenance,
security
and
routing.
Well,
you
look
at
it.
These
are
the
interface
of
our
area.
We
have
to
talk
to
to
those
four
areas-
transport
above
us,
but
mostly
rotting-
on
the
left
and
security
and
operation
on
the
right.
B
B
We
need
rotting
and
rotting
needs
us,
because
there
is
an
interaction
between
what's
happening
on
the
mink
layer
on
how
the
rotting
can
abstract
it
and
present
it
to
the
rest
of
the
world
and
obviously
now
the
ATF
as
this
role
that
anything
that
you
set
aside
at
the
ATF
must
be
secured
so
more
often
than
not
before
you
even
go
to
to
all
the
other
areas.
For
the
final
review
of
your
work,
you
asked
some
some
review
from
the
security
area.
B
If
there
is
some
sensitivity
in
what
you're
doing
to
security,
then
we
get
help
from
the
security
Directorate
before
we
even
go
to
ask
review
from
other
directorates.
So
everything
now
has
to
be
quite
safe
that
we
produce
at
the
ATF
and
that's
why
you
will
find
this
section
at
the
end
of
which
RFC
will
produce,
which
is
the
security
consideration.
You
have
to
write
a
security
consideration.
You
have
to
analyze
how
your
which
threat
can
apply
specific
straight
apply
to
your
new
protocol.
B
B
Me
before
up
and
after
me,
b6,
which
is
kind
of
interesting,
but
this
is
this-
is
the
second
version
of
the
v6.
The
first
one
was
37
certified
and
here
all
this
interesting
link.
So
she
she
tried
listening
the
data
tracker.
You
will
see
it
kind
of
it's
gotten
very
friendly,
I,
really
loved
a
new
data
tracker
that
we
have
a
DEA
ATF,
it's
kind
of
the
I
Triple
E
mentor,
but
it's
really
easy
to
navigate.
B
You
can
see
the
working
groups,
you
can
see
the
areas
and
if
you
click
on
the
working
group,
you
can
see
which
documents
are
being
or
troughs
lie
and
goes
through
a
little
bit.
What
the
draft
is
and
then
which
are
RFC's.
So
the
cycle
basically
have
not
seen
it
before
is
that
you
can
publish
any
documents
you
like,
but
you
publish
it
with
your
name.
It's
going
to
be
called
the
draft
doe
draft,
the
John
Doe.
B
If
you
want
to
publish
it
to
a
particular
I,
can
grow
up,
it's
going
to
be
draft
under
working
group
and
then
whatever
you
like
there
0
0,
because
it's
the
flow
generation.
And
now,
if
you
publish
new
variation
of
it,
you
have
to
do
+1
every
time.
So
the
drafts
are
sequence.
They
start
draft
name
working
group.
Whatever
works
qualify,
your
work
sequence
number
and
you
publish
that
at
some
point,
a
working
group,
the
one
group
may
like
it
and
we'll
call
it
draft
IETF.
Instead
of
shall
name
you
give
token
to
the
IDF.
B
The
work
doesn't
belong
to
you
anymore,
belongs
to
the
working
group.
Draft
IDF
working
group
name
whatever
qualifies,
starts
at
zero
again
goes
through
the
process
and
the
Pepsi,
so
it
may
be
a
star
attraction.
Doing
some
standard
work
could
be
informational.
If
it's
not
on
track,
then
then
you
have
initially
well
I
choose
to
be
three
level
nights
on
me
to
you,
have
the
normal
star
track
and
then
you
have
the
internet
standard,
which
is
read
like
to
Gordon
ipv6
8200.
B
B
You
can
also
see
for
given
working
group-
everybody,
you
is
responsible,
so
you
will
find
them
in
archives.
You
just
click
there
and
you
can
register
to
the
mail.
You
will
receive
it.
There
is
no
no
fee
to
pay
nothing,
you
just
just
register
to
it
and
get
the
mail
and
you
can
talk
about
it
and
there
is
the
job
or
the
rumors.
Four
four
four
during
the
meetings,
that's
pretty
much
it
we're
out
of
time,
but
any
questions
and
then
remember:
50
means
from
now.
There
is
the
meet-and-greet.
D
C
This
is
like
pretty
much
a
211
OCB
like
that's
the
only
thing
that
we
are
so
chatted
for
right
now,
so
it's
right
now
they
equal
to
vehicle
and
they
could
infrastructure
like
so
pretty
much
cars
and
trucks
and
platooning
and
and
adaptive
cruise
control.
Those
kind
of
things
are
the
only
things
we're
like.
So
it's
not
like
lot
of
the
safety
stuff
is
not
in
scope
really
right
like
so
as
I
said
like
it
once,
the
working
group
finishes
the
deliverables
we
can
recharter
to
do
more,
but
right
now,
that's
the
scope.
C
C
So
it
does
never
I,
never
seen
a
proposal,
that's
clear
enough
to
charter,
but
if
you
do
have
some
proposal,
that's
like
clear
to
do
because
one
of
the
things
like
I'm
kind
of
pushing
back
on
is
like
very
boil
the
ocean
kind
of
proposals
which
I
have
a
lot
of
things
to
do
so
I
kind
of
want
something
to
be
really
scoped
down.
So
if
you
really
have
something
you
want
to
bring
up
come
talk
to
me,
we
can
talk
about
a
buff
proposal
coming
up
soon
and
then
we
can
go
from
there.
D
B
And
that's
it!
Thank
you
for
being
there
and
I
hope
we
meet
again
at
the
ready,
meet
and
greet,
and
yes,
we
have
a
wiki
which
will
tell
you,
for
instance,
how
you
can
come
here
first
alight,
but
it's
very
useful.
For
instance,
if
you
have
any
direction
anything
which
is
great
receivers,
many
thanks
again
we
go
you're
free
to
go,
enjoy
the
food.
