►
From YouTube: IETF105-IRTFOPEN-20190723-1520
Description
IRTFOPEN meeting session at IETF105
2019/07/23 1520
https://datatracker.ietf.org/meeting/105/proceedings/
A
B
C
C
C
We
have
a
bunch
of
things
today.
Quick
introduction
and
status
updates
get
us
started
and
we
have
a
short
update
from
the
information
centric
networking
Research
Group
talking
about
the
CC
n,
XR
FCS,
and
then
we'll
spend
the
majority
of
the
time
today
with
two
really
excellent
talks
from
the
applied
networking
research
price
with
Metro
Rosen
Schiff
sitting
in
the
front
here
to
start
with
talking
about
MTP
and
new
NTP
client
called
Chronos
and
TJ
Chung
at
the
end,
talking
about
the
role
of
registrar's
in
DNS,
SEC
opponent,
really,
nice
measurements.
C
Let
me
back
it's
a
lot
of
echo
good,
closer
or
further
loosely.
Is
this
better?
Yes,
okay,
excellent!
All
right!
It's
it's
even
more
echoey
from
where
I'm
sitting,
but
if
it's
better
for
you,
that's
good,
okay.
So
this
is
the
IRT
F
open
meeting
the
IRT
F
as
a
reminder
is
a
parallel
organization
to
the
IETF
which
focuses
on
the
longer-term
research
issues.
C
C
We
cover
a
pretty
full
range
of
the
possible
subjects
from
the
crypto
forum
group,
all
the
way
through
to
quantum
Internet
network
measurements,
information,
centric,
networking,
Human,
Rights,
global
access
and
so
on.
The
groups
in
dark,
green,
full
research
groups,
the
ones
in
light,
green
and
gray,
proposed
research
groups.
We
let
new
research
groups
run
for
a
year
and
see
if
that
things
are
working
and
if
so,
they
don't
get
charted.
As
a
full
research
group,
the
coin
group
had
its
first
meeting
in
Prague.
Competition
in
the
network
group.
C
Looked
being
some
really
nice
stuff
I'm
in
network
computing.
The
privacy
enhancements
group
will
be
having
their
third
meeting
later
this
week
and
expect
their
transition
to
a
full
research
group.
Shortly
after
that,
and
the
quantum
internet
group
who
had
not
meeting
this
time
had
a
really
nice
tutorial
in
Prague,
which
I
understood
not
a
word
of
about
quantum
quantum
Internet
and
the
quantum
physics,
but
the
physics
behind
what
it
needs
to
build,
a
quantum
link
and
look
to
be
doing
some
really
nice
work
that
they're
alternating
their
meetings
between
here
and
quantum
physics
conferences.
C
So
they're
not
meeting
this
time.
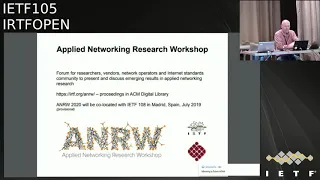
We
also
have
the
applied
networking
research
workshop,
which
run
yesterday.
We
had
a
couple
hundred
people
in
attendance,
a
bunch
of
really
nice
papers.
This
is
a
conference
we
organized
in
conjunction
with
ACM
sitcom
proceedings
are
published
in
the
ACM
digital
library.
It's
a
peer,
reviewed
or
workshop.
C
We
got
some
really
nice
papers
which
are
all
on
the
website
and
we
hope
to
do
this
all
again
next
year,
still
a
little
bit
provisional,
but
hopefully
this
will
be
running
again
and
that
summer,
ITF
in
Madrid
next
year,
so
look
out
for
the
call
for
papers
around
Christmas
time.
Just
after
and
finally,
we
have
the
applied
networking
research
prize,
which
is
awarded
for
some
results
in
recent
results
in
applied.
Networking
research
and.
C
The
two
talks
which
comprise
the
majority
of
this
session
talking
about
MTP
security
and
checking
out
DNS
SEC
deployment,
there'll
be
a
couple
more
NRP
talks
at
ITF
106
in
Singapore
and
we'll
be
opening
nominations
for
the
2020
awards
and
come
October
November
time.
So,
if
you've
read
any
good
applied
networking
research
papers,
keeping
them
in
mind,
we'd
appreciate
you
nominations
later
in
the
year.
C
D
Okay,
there
we
go
so
the
there
were
two
documents
released
as
part
of
this
protocol:
the
versus
85
69,
the
semantics
document,
which
describes
the
behavior
and
the
meaning
of
the
different
fields
and
then
there's
an
encoding
document.
80
609,
which
uses
a
mostly
TLV
format
to
encode
the
protocol
messages.
D
So
for
those
of
you
who
don't
know,
CC
NX
is
one
of
the
IC
energy
information
centric
networking
protocols,
and
the
idea
here
is
that
you
do
something
to
name
the
data
that
you're
requesting
and
you
can
use
that
name
in
fetching.
The
data
so
you're
not
doing
quite
the
host
a
host
networking
you're
trying
to
get
something
by
its
content,
and
this
was
first
proposed
in
2009
and
went
under
a
significant
revision
beginning
in
2014.
D
There
are
four
principal
implementations
that
are
going
right
now.
One
is
called
community
ICN
and
this
is
a
Linux
Foundation
work,
and
this
is
meant
to
be
a
fairly
high
speed.
Implementation
of
uses
of
dr.
packet
packet
processing,
CCN
blight,
which
is
a
widely
used
implementation,
especially
on
smaller
platforms
and
C,
for
this
is
from
the
National
Research
Institute
of
Japan,
and
this
has
also
simulator
emulator
modules
available
for
it.
D
So
all
of
these
are
based
on
the
CC
NX
RFC's
hybrid
ICN,
who
looks
at
integrating
name
based
name
based
routing
into
the
ipv6
address
space,
so
between
the
ipv6
address
and
the
transport
address
it's
kind
of
fully
integrates.
So
it's
not
really
an
overlay.
It's
an
integration.
Thank
you
very
much.
Ok,.
C
C
E
Hi
I'm
and
today
I'm,
going
to
present
a
walk
on
our
to
and
protect
NTP
with
the
host
is
a
joint
work
with
Omega
H.
They
need
to
live
and
appear
so
anti
B,
Network
and
protocol.
It
is
used
to
a
synchronous
time
across
computer
over
the
Internet
I
guess
you
all
know
I'm.
How
make
sure
is
money?
Application
will
be
learning
such
as
TLS,
dinners,
HTTP
cables
and
many
financial
applications
and,
in
a
nutshell,
NTP
is
a
client-server
architecture,
consists
of
two
main
processes,
both
process
and
selection
process.
E
E
However,
NTP
is
highly
vulnerable
to
time.
Shifting
attacks
especially
made
by
man-in-the-middle
attack
here
who
and
who
have
a
control
over
this
section
between
client
and
one
of
the
entity
service
and,
for
example,
let's
assume,
without
loss
of
generality,
that
name
the
man
in
the
middle
control,
the
section
between
the
client
and
the
left
and
Bishop
and
man
in
the
middle
attack
in
CHEM
temper,
NTP
responses.
He
can
impact
the
local
clock
of
the
client
by
simply
dropping
on
delight
in
packets.
E
Algorithms
assume
that
in
currency
are
rare
and
they're
well
distributed
around
a
you,
see
the
correct
time.
That
is
why
powerful
and
sophisticated
man
in
the
middle
attack
again
can
bypass
this
algorithm
and
he's
the
young
scope
of
traditional
and
sweet
women's
in
order
to
face
these
limitations
and
we
suggest
modification
fight
and
the
client
called
homes
it
has
the
following
characteristics:
it
has
provable
security.
We
can
bound
the
probability
of
successful
time,
shifting
attacks
even
made
by
men
in
the
military.
E
We
can
make
what
come
ability
since
there
is
no
need
to
change
anything
in
the
server
side.
Only
small
and
limiters
are
needed
in
this
in
the
client
side
and
we
add
only
low
computational
and
communication
on
overhead,
since
eventually
very
only
few
NTP
servers.
So
in
order
to
prove
that
harness
actually
protect
NTP,
we
need
to
define
our
treat
model.
So
we
assume
that
the
attacker
I
have
fully
control
of
a
large
function
of
the
NTP
service
sake
Porter.
E
We
also
assume
that
he
is
capable
of
both
modifying
the
content
of
the
NTP
response
and
the
timing
when
it's
going
to
arrive
to
define.
And
finally,
we
assume
that
these
malicious
and
try
to
shift
the
client
stop
as
much
as
possible,
so
how
Collins
is
built.
On
the
one
hand,
we
rely
on
many
and
to
be
server,
we
it
servers
and
we
generate
a
large
several
hundred
of
service
per
client
and
in
order
to
raise
the
trishul
needed
by
the
attacker
to
attack,
on
the
other
hand,
require
only
few
servers.
E
E
So
now
out
of
that,
and
the
pool
I
am
informally
going
to
describe
how
we
update
our
clock
so
out
of
hundred
of
servers
in
a
cool
we
choose
tenth
of
them
at
random,
then
we
ordered
them
from
low
to
high.
We
remove
the
D
lowest
and
the
highest
time
samples
and
take
a
look
at
the
remaining
sets,
and
then
we
ask
two
questions.
We
have
two
conditions.
E
E
Otherwise
we
were
sample
and
again
out
of
hundreds
of
servers.
Tenants
are
choosing
tronic
chosen
at
random
and
which
work
this
from
each
side
could
be,
for
example,
third,
and
we
take
a
look,
there
were
many
certain
stand
and
test
the
two
conditions,
whether
they're
close
to
each
other
and
whether
they're
and
every
range
it
goes
today
and
clients.
E
So
first
I'm
going
to
present
our
security
guarantees
and
now
I
will
describe
our
security
analysis.
So
essentially,
what
we
are
showing
in
our
paper
is
that
shifting
time
actually
signed
by
at
least
100
millisecond
from
the
UTC
will
take
the
attacker
at
least
22
years
in
expectation-
and
this
is
when
we
consider
an
extreme
case
were
out
of
577.
Super
are
fully
controlled
by
the
attacker.
We
also
aquarii
15
services
per
hour,
and
so
the
examples
are
within
25
millisecond
from
the
UTC.
E
We
call
this
this
part
L
Omega,
and
these
parameters
are
derived
from
an
experiment
that
we
conducted
on
Amazon
servers
both
in
Europe
and
in
the
US,
and
here
you
can
see
the
benefit
of
using
and
the
current
entropy
as
a
function
of
access
and
the
number
of
servers
that
are
quite
a
bit
probably
and
where
each
one
here
and
I
present
a
different
ratio
of
the
malicious
server
in
between
and
so
consider
pools.
Four
or
five
hundred
servers,
ap
function
of
which
are
fully
controlled
by
the
attacker.
E
And
now
we
compute
the
attacker
probability
of
success
and
four
times
to
take
attack
both
in
the
traditional
NTP
client
and
in
constantly
defines
we
plot
the
ratio
between
these
probabilities,
and
this
is
the
one
axis.
So
if
we
consider
the
last
trial,
when
we
have
out
of
500
several
Thurman's
for
more
fully
controlled
by
the
attacker,
we
can
say
that
using
a
course
improve
the
security
by
a
factor
of
1,000
and
notice
that
there
is
no
great
making
that
by
the
improvement,
is
exponential.
And
now
we
are
going
to
describe
our
security
analysis.
E
So
in
order
to
do
so,
we
have
to
look
at
all
the
scenario
that
can
happen,
which
depends
on
the
number
of
malicious
samples
that
we
query
and
and
see
how
policies
handling
them.
Of
course,
we
take
their
words
and
I
say
my
own.
They,
it
was
cast
in
a
lesson,
and
the
first
in
iron
is
when
the
number
of
the
a
good
samples
is
the.
As
you
remember
out
of
hundreds
of
servers,
we
chose
M
chance
at
random
and
then
we
differ
on
each
side.
E
So,
in
the
first
scenario,
we
have
a
the
number
of
a
good
samples.
You
know
this
is
as
a
yellow
engine
it's
higher
than
there,
and
then
there
are
more
malicious
samples
denoted,
as
the
very
diamond
is
less
than
I
am
minus
D.
So
we
have
to
our
option
here,
because
the
first
one
is
when
we
have
only
a
malicious
sample
women
in
our
remaining
sets.
E
However,
we
have
more
than
the
good
samples
right,
so
we
have
at
least
one
good
sample
in
each
side
of
the
remaining
set,
which
means
and
and
good
samples
are
within
origami
from
the
UTC
from
the
correct
time.
That
is
why
the
remaining
set
samples
should
be
also
close
to
the
sick
and
the
your
averages
wheels
in
order
to
update
our
clock.
Eventually,
it's
close
to
jettison.
The
second
option
is
when
we
have
at
least
one
good
sample
inside
our
remaining
set.
E
However,
according
to
our
second,
if
first
condition
and
all
the
samples
in
the
remaining
set
should
be
close
to
each
other,
our
device-
we
were
some
so
if
we
know
that
we
have
at
least
one
good
sample
in
the
remaining
second,
it's
close
to
get
a
UTC.
The
others
should
be
closely,
which
means
that
their
average
also
will
be
close
to
the
UTC,
and
this
is
why
we
can
say
that
these
attack
strategies
are
in
effect.
E
The
second
scenario
is
when
number
of
the
good
samples
and
is
equal
less
than
D
and
the
number
of
malicious
or
else
is
a
high
or
equal
to
your
a
minus
D.
In
the
worst
case,
we
have
only
malicious
servers
remaining
and
they
are
not
bounded
by
a
good
samples.
However,
according
to
our
second
condition,
their
average,
which
we
finally
use
in
order
to
update
our
clock,
should
be
close
to
the
clients
clock,
which
means
that
there
is
a
boundary
on
the
time
shift
that
we
allow.
E
Moreover,
the
probability
of
this
kind
of
a
scenario
is
extremely
low.
Why?
Because
each
and
requires
the
malicious
symbols
to
be
randomly
chosen
in
much
higher
rate
than
directing
the
population
and,
of
course
repeated
shifts,
is
a
probability
is
negligible.
This
is
why
we
can
set
a
significant
time
shift
here.
Is
a
cocktail
a
prism,
but
even
if
we
cannot
really
shift
the
can't
stop
clock,
maybe
we
can
create
another
kind
of
attack.
Let's
say
you
know
service,
so
how
can?
How
can
we
do
that?
E
For
example,
the
first
condition
saying
that
all
the
samples
should
be
close
to
each
other
and
then
caused
us
to
sample
we're
sampling
again
and
again
and
again
we
get
to
the
panic
mode.
When
we
ask
all
the
several
in
the
book
and
maybe
and
multiple
we're
sampling
by
multiple
clients
course
client
may
cause
denial
servers
over
the
NTP
servers.
E
However,
we
can
prove
that
even
for
low
panic
threshold
K
equals
3,
with
a
means
that
only
after
three
failures
you
a
move
to
their
panic
mode
and
ask
all
the
servers
in
the
pool.
The
probability
of
success
is
negligible,
which
means
that
they,
it
will
take
the
attacker
decades
to
force
panic
mode
on
oneself
or
not
in
one
a
glance
or
and
one
of
it.
When
we
compare
between
corners
and
REM
TPD,
we
see
that
corners
using
greater
variety
of
samples
server
over
time.
E
If
ever
possible
security
guarantees
is
presented
and
it's
a
void,
the
NTP
source,
quality
and
filters.
This
is
why
it
may
be.
It
is
possible
that
address
and
that
there
is
a
worse
effect
on
its
precision
and,
according
so
in
order
to
improve
and
the
precision
without
sacrificing
and
home
security
who
introduced
us
moaning
mechanism
and
that
saying
that
we
favor
the
minimum
sample
of
that
out
of
order
and
offsetting
the
remaining
self.
E
And
if
it's
close
to
the
to
the
average
of
we
evaluate
comes
with
the
small
team
optimism
in
multiplication,
both
in
New
York
and
in
the
US
and
for
example,
this
is
the
results
from
Oregon.
Where
you
can
see
in
the
its
axis.
Is
the
average
offset
and
in
the
y
axis,
is
the
fluctuation
and
the
average
of
the
derivative
each
dot?
E
To
conclude,
ntp
is
a
highly
vulnerable
to
any
time,
shifting
in
tax
and
even
attack
here,
who
controls
even
few
section
in
between
server
and
servers
and
client
can
shift
the
first
time.
So
we
presented
a
modified
and
the
client
co-host
with
provable
security.
Mequon
could
come
ability
and
low
overhead,
and
we
also
shown
that
in
home,
say,
precision
and
offset
are
very
close
to
ntp
around
two
millisecond
upon,
and
this
is
their
their
research,
the
further
research.
So
we
can.
E
We
continue
to
evaluate
concept,
scale,
security,
precision,
currency
overhead,
etc,
and
we
also
working
on
standardized
and
call
in
the
relevant,
a
working
group,
and
we
would
like
to
extend
Hollis
to
address
in
several
attack
strategies
and,
of
course,
we
would
like
to
extend
bonus
to
maybe
other
time.
Synchronization
protocol
such
as
PT,
and
here
you
can
see
that
there
a
link
to
both
our
paper
published
in
and
and
this
s
and
our
life
last
ITF
draft.
Thank
you
very
much
and
thank.
C
C
F
F
E
Okay,
this
is
just
an
estimation
and
it's
like,
but
basically
we
are
because
they're
in
quantum
losses
between
4
&
6
servers,
we
didn't
really
calculate
before,
and
so
this
is
the
answer
about
why
it
is
get
worse
and
a
white
straight
line
and
not
really
increasing
then,
and
the
answer
is
that
we
would
like
to
to
remove
this
from
each
side.
D
was
a
once
there
and
we
wanted
you
to
be
an
integer
number.
So
this
is
why
you
can
see.
Then
it's
tears
so.
G
Hi,
what's
heard
occur,
I,
say
good
work,
I,
love,
taking
a
bit
statistical
analysis
of
your
security
likelihood
I
think
that's
great
and
it
looks
like
it's
a
feasible
solution
with
one
exception,
so
I
assume
it
sounds
like
you,
don't
try
and
handle
men
in
the
middle
type
attacks
where
you
have
an
attacker
very
close
to
you.
That
can
almost
respond
to
most
NTP
servers
right
so
that
thank.
H
E
H
E
Yes,
yeah
now
a
dropper,
we
were
saying
that
in
a
startup
way
and
for
now
he
is
and
panic
mode
at
startup
and
mode,
but
we're
working
on
it
and
maybe
we
can
and
we
don't
have
to
really
worry
all
the
service,
but
only
maybe
in
factor
of
two
of
their
server.
That
would
open
query
and
quantum,
maybe
to
em,
for
example,
and
in
order
to
get
you
to
do
the
same
with
all
so
this
is
exactly
what
right.
Thank
you.
Thank
you.
I
E
J
So
did
you
do
any
analysis
on
the
curve
and
entity
blind
with
fixed,
so
prolonged
entity
kind
has
a
fixture
a
number
of
servers
right
that
it
quits
it's
a.
It
has
a
fixed
number
of
our
service
so
with
a
fixed
number
of
servers
and
using
your
modified
algorithm,
does
it
provide
the
similar
guarantees
or
is
it
similar
security
guarantees?
If
this
client
is
querying
a
fixed
number
of
servers,
as
opposed
to
randomly
selecting
from
a
large
pool
and
using
your
modified
algorithm
for
selection,
does
it
give
the
similar
security
guarantees
or.
E
If
he's
all
it's
under
the
control
of
malicious
attacker,
then-
and
he
can
do
the
repeated
shift
time
I
mean
I
I
allow
it
to
do
an
impaired,
limited
time
shift
and
the
fact
that
I
I'm
telling
that
with
repeated
time
shift
is
probabilities.
Negligible
is
because
I
am
and
querying
different
service
all
the
time.
Otherwise,
I
want
to
be
able
to
say
that.
C
H
C
L
For
the
introduction
Cowan
hi,
my
name
is
TJ
from
RIT
assistant,
professor
first
of
all,
I'm
very
excited
to
talk
about
research,
and
actually
this
is
my
first
ITF
and
I'm
really
excited
to
see
how
smart
is
the
people
making
a
decision
by
humming?
So
so
this
talk
is
about
DNS
and
DNS
SEC.
So
inevitably,
I
need
to
give
you
some
introduction
of
how
DNS
and
DNS
Edwards
I'm.
B
L
Bit
scared
to
talk
about
the
introduction
with
you
in
front
of
you
actually
make
a
standard,
improving
the
internet.
But
let
me
try
my
best.
So
DNS
is
like
yellow
pages
in
your
internet.
It
translated
human
readable
name
to
machine
readable
name
such
as
IP
address
so
I'm.
Sorry,
deep!
There
should
be
a
animation,
but
some
yeah.
L
L
The
idea
is
very
simple:
let's
deploy
public
and
private
key
infrastructure
on
a
DNS
site,
so
example.com
now,
managers
of
key
pair,
private
and
public
key
pairs
and
the
when
the
risk
when
the
DNS
Rica's
calms
it
responds
with
the
signature
so
to
verify
the
signatures.
The
reserver
also
need
to
have
a
public
key
part,
so
the
public
key
is
in
the
DNS
key
record.
So
here
is
another
problem:
how
the
reserver
guarantee
that
this
public
key
actually
belongs
to
D
example:
comm,
so
DNS,
SEC
meters,
existing
hierarchy
of
DNS.
L
So
now
the
comm
John
also
have
DNS
key
public
key
and
private
key
and
use
this
key
to
sign.
Example
that
counts
DNS,
key
and,
of
course,
that
come
John's
a
DNS
key
is
also
signed
by
root
DNS
key.
Then
how
does
a
reserver
verify
the
DNS
root?
T?
It
is
prefetching,
so,
as
you
can
tell,
there
is
a
chain
of
trust
root.
Signs
calm
that
comes
on
is
calm
and
example.com
signs
at
the
end,
RTS
a
DNS
record
right.
L
So,
let's
see
how
this
actual
channel
trust,
making
a
chain
of
trust
process
works,
because
the
making
a
chain
of
trust
between
root
and
calm
and
calm
and
example.com
are
basically
saying
so,
let's
focus
on
the
later
one.
So
the
key
concept
is
very
simple.
So
if
you're,
the
owner
of
example,
calm-
and
if
you
want
to
make
a
chain
of
trust
that
when
you
need
to
do,
is
first
generator,
yes
record
so
des
record
is
just
a
hash
of
your
DNS
key,
so
it
is
based
on
a
long
string,
long
hash
industry.
L
After
that,
you
have
to
unload
it
to
the
your
furniture.
So
in
this
case,
Stockinger
then.com
John
will
sign
this
DNS
key
record
and
I'm
sorry
for
the
animation
and
also
it
generate
a
signature.
So
when
our
reserves
wants
to
verify,
if
this
DNS
key
is
valid,
it
has
to
fetch
a
DES
record
from
the
turn.
John
is
challenging.
Yes,
the.
L
L
Yeah,
so
if
we
reserved
a
path,
choose
TS
record
from
the
parent
own
and
fetch
attendance
key
from
the
child
journey,
if
it
is
same,
then
it's
not.
Of
course
you
need
to
verify
the
signature
of
the
TS
record,
signed
by
the
conjurer,
of
course,
so,
if
you're
the
owner
of
a
domain
name,
if
you
want
to
deploy
the
Unison,
you
need
to
follow
these
three
steps.
First,
you
need
to
have
a
DNS
key
and
using
this
key
you
have
to
generate
a
signature.
L
At
the
last
step,
you
have
to
generate
a
TS
record
and
upload
it
to
your
printer.
So
the
question
and
answer
for
this
research
on
this
analysis
is
how
many
domains
out
there
follow
these
steps.
So
to
do
that,
we
used
open,
Intel
dataset,
which
collects
all
the
domain
names
on
the
recom
that
earth
and
that
almost
two
years
so,
let's
see
actually
there
was
a
black
box
to
hide
the
graph
to
make
a
CD
to
make
a
surprise,
but
it
is
already
revealed.
L
C
L
Yep,
so
y
axis
shows
percent
of
missing
signatures,
so,
as
you
can
tell
nearly
0.2%
of
domain
names
with
DNS
key
missed
the
signature,
so
signatures
are
rarely
missing.
There
is
a
huge
draw
at
this
point.
This
is
two
to
one
all
registrar
I,
don't
want
to
call
name,
but
they
used
to
have
a
DNS.
They
all
a
wiki
kept
with
DNS
key,
but
some
reason
they
forgot
to
sign
it,
but
after
at
that
point
they
finally
signed
generated
signatures.
So
that
is
the
reason
why
there
is
a
huge
drop.
L
Then
how
about
the
finer
one?
The
last
piece
of
puzzle
is:
you
need
to
generate
a
TS
record
and
upload
it
to
the
printer,
so
Y
axis
is
percent
of
domains
missing.
Yes,
record.
Surprisingly,
we
found
that
nearly
30
percent
of
domains
do
not
another
TS
record.
So,
as
you
can
tell,
there
are
two
problems
here.
First,
one
is:
why
does
he
make
the
intersect
deployment
remains
so
small,
even
though
it
was
introduced
about
20
years
ago,
and
the
second
problem
is:
why
are
30
percent
of
domains
still
without
a
TS
record?
L
L
So
to
understand
that
you
have
to
understand
how
you
can
purchase
your
domain
name
and
how
to
deploy
the
NSA.
So
let's
say,
if
you
want
to
buy
a
domain
name,
you
typically
go
to
a
register.
For
example,
cadet
the
registrar
is
organization
that
sells
that
domain
name
to
the
public
and
also
it
has
a
access
to
the
database
managed
by
registry.
So
registry
is
a
basically
top-level
domain
name
John,
for
example,
comm
is
managed
by
Verisign
and
after
that,
after
purchasing
a
domain
name.
You
also
need
to
have
a
name
servers.
L
The
first
choice
you
can
make
is
you
can
just
use
a
name
server
provided
by
the
registrar.
So
in
this
case,
if
you
want
to
deploy
at
the
NSA,
then
GoDaddy
will
generate
a
DNS
key
signatures
and
also
TS
record
right
and
also
it
has
an
access
to
the
database.
Menus
by
registry
so
that
it
can
simply
easily
unload
a
key
s
record
to
the
registry
right.
The
second
choice
is,
you
can
run
your
own
names
over.
L
L
Third
party
knows
operator.
So
in
this
case,
for
example,
Claude
Fleur
will
manage
all
the
DNS
records
for
you,
including
generating
signatures
ts
record,
but
again
third-party
DNS
operator
doesn't
have
any
to
the
registry.
So
you
need
to
copy
the
string
D
s
record,
which
is
basically
a
long
stream
copied
and
pasted,
pass
it
to
the
register
and
ask
them
to
upload
it
to
the
registry.
If
you
think
this
process
is
complex,
actually
I
can
make
it
even
worse.
So,
for
example,
let's
say
you
bought
a
domain
name
from
a
reseller.
L
Reseller
is
organization
that
sells
aluminum
to
the
public,
but
it
doesn't
have
any
or
32
Connect
contact
with
your
registry,
so
what
they
do
is
to
partner
with
a
registrar.
So
if
you
purchase
a
domain
name
from
a
reseller
and
using
a
third
party
knows
operator,
then
you
need
to
copy
a
TS
record
and
pass
it
to
the
reseller
and
ask
them
to
upload
it
to
the
registrar
and
registry,
such
a
simple
process.
L
What
could
possibly
go
wrong
so,
as
you
can
tell,
the
key
part
of
the
pointyness
egg
is
register,
so
what
I'm
going
to
do
is
I'm
going
to
show
you?
Is
we
showing
the
research
that
we
surveyed
by
surveying
popular
register
with
lots
of
domain
name?
So
what
we
do
is
we
first
purchase
a
domain
name
from
a
registrar
and
we
see
if
they
simply
support
the
NSF
on
their
name
servers
after
that
we
disable
it.
We
run
our
own
name.
L
Servers
generate
a
TS
record
and
ask
them
if
you
guys
can
unload
a
TS
record
to
the
registry.
If
they
do,
we
deliberately
give
them
an
inquiry,
TS
record,
which
is
not
matched
with
the
NF
ski.
The
reason
is
that,
because,
if
the
registrar
does
not
check
the
validity
of
the
DNS
key
and
the
TS
record
and
simply
upload
it
to
the
registry,
then
your
domain
name
will
be
instantly
in
accessible
to
the
reserver
that
support
DNS
set
such
as
Google
reserver
or
call
or
cloud
ler
wizard.
L
So,
if
we're
showing
this
before,
showing
me
all
the
details
of
the
analysis,
I'm
going
to
give
you
some
anecdotal
examples
that
we
experienced
your
during
our
experiment,
the
first
one
is,
we
started
the
NS
key
deployment
boy
for
one
register,
but
not
the
Ezra,
so
ask
why
you
guys
do
not
have
noted
the
s
record.
The
first
response
was
that
Oh
they
removed
at
the
NSA
me
and
the
other.
L
Another
red
is
for
responded
back
to
me,
saying
that
hey
most
people
do
not
understand
DNS,
so
imagine
their
white
faces
when
I
mention
DNS
SEC.
So
yeah
this
this.
What
happened
and
also
we
asked
a
register
to
unload
a
TS
record
by
email
from
the
different
email
August
and
the
one
we
use
to
register
it
was
installed
successfully
and
also.
We
asked
already
start
to
him
that
ideas
record
to
our
web.
Our
domain
name
domain
via
a
web
live
chat.
L
He
was
installed
successfully
to
someone
else
domain
name
due
to
a
mistake
by
customer
agent
yeah.
Usually
the
customer
Asian
you
know,
opens
a
multiple
pad
to
deal
with
multiple
customers,
so
just
made
a
mistake
to
pay
city
s
record
to
the
other
domain.
So
this
is
the
detail.
Hey
I'd
like
to
update
my
TS
record.
It's
awesome
one
moment
so.
I
now
update
your
DNS,
a
TS
record
to
an
end
using
a
comp
right,
I'm,
sorry,
but
my
domain
is
Aug
the
intersect
that
come.
Oh
I,
apologize,
you're!
L
Sadly,
only
four
registers
support
the
NSF
on
their
name
servers,
which
is
not
good
for
your
information
we
read
on.
Actually
the
study
was
done
about
twenty
seven,
twenty
seventy,
but
for
their
stuff.
We
just
redid
all
the
survey
few
weeks
ago
and
after
that
we
disable
our.
We
run
our
own
name
servers
and
disable
the
default
names
that
were
provided
by
the
registrar,
and
we
asked
them
to
a
lot
ideas
record.
Interestingly,
15
out
of
20
12
are
supported.
He
has
record
under
so
mainly
there
are
two
functions
functionalities.
L
The
first
one
is,
for
example,
web
supporting
ticket
or
web
live
chat.
So
using
this
methodology
they
all
those
ups
terminal,
yes
record
or
some
registrar's
ask
us
to
send
the
email
with
the
you
know.
Content
is,
of
course,
the
long
string
of
a
yes
record
and
sadly,
only
5
out
of
20
check
the
verification,
so
yeah.
If
you
happen
to
deliver
incorrect,
yes
record,
your
domain
name
will
be
instantly
inaccessible
to
DT
and
as
a
supporting
reservist.
L
So
here's
a
summary
only
4
out
of
20
support
for
our
20
redress
of
for
DNS
SEC
on
their
name
servers.
What
this
means
to
you
is,
if
you
don't
want
to
run
your
own
names
over
most
of
the
time,
you
cannot
deploy
a
set.
If
you
want
to
run
your
own
name
solvers
still,
you
cannot
deploy
them,
except
for
5
out
of
20,
and
only
5
already
serves
up
for
check
it
out.
L
Yes,
record
verification,
which
means,
if
you
happen
to
another
incorrectly
s
record
you
to
copy
and
paste
theater,
then
your
domain
name
will
be
inaccessible
right
then.
The
next
question
is:
why
are
this
Genesis
support
of
registers
so
rare?
Why?
Why
is
that?
Actually
we
already
know
the
answer,
because
the
anisette
introduced
much
more
records
right
because,
basically,
in
this
signature
for
every
DNS
records
and
also
signatures
are
usually
three
to
six
times
larger
than
non
dns
records,
and
also
the
NFC
is
like
your
password.
L
You
have
to
choose
strong,
key
and
also
unique
key,
and
also
you
have
to
roll
over
the
key
regularly
in
a
regular
basis.
Actually,
you
already
seen
why
how
this
policy
impact
on
the
intersect
deployment.
For
example,
we
saw
that
four
out
of
20
registered
support,
DNS
set
on
their
name
servers,
but
in
personally
15
out
of
20
on
allow
us
to
another
key
aspect
right.
The
thing
is
in
the
first
case,
when
the
registrar's
run
began
our
names
over
with
DNS
SEC.
L
They
need
to
manage
all
DNS
records
in
their
name
servers,
but
the
if
the
owner
wants
to
run
their
own
name
servers
than
what
the
registrar
needs
to
do
is
to
simply
receive
what
the
yes
record
and
unload
it
to
the
registry
done
they
don't
need
to
manage
all
the
cancer
occurs
at
all.
So
so,
let's
compare
the
2017
research,
so
our
study
was
done
in
2017
March.
L
So
at
the
time
only
three
out
of
20
registered
supported
the
TNF
secondary
name
servers
at
the
register
side,
name,
servers
and
11
out
of
20
supporting
it
when
the
users
want
to
use
their
own
running
servers
and
proud
of
them
check
the
verification.
So,
as
you
can
tell
it
has
been
improved
but
yep
it
has
to
be
improved.
It's
much
better
than
you
know
decreasing.
You
know
still
way
to
go.
L
So
so,
let's
see
how
the
how
a
registered
policy
impact
on
genetic
deployment.
In
other
words,
how
can
we
encourage
your
register
to
support
the
assay?
The
first
a
perspective
is
registry,
so
we
happen
to
notice
that
the
kpn
touch
registrar,
Alypius,
redish
register
in
a
financial
incentive
from
the
registry
registry
when
they
activate
the
intersect
for
the
domain
names
they
manage.
So
as
you
can
tell
that
NL
that
has
it
is
domain
names.
L
The
uninfected
ployment
ratio
is
nearly
90
percent,
which
is
awesome,
but
how
about
the
other
three
domain
names
teller
than
other
Netcom,
where
they
cannot
get
any
financial
incentive?
So,
as
you
can
tell
actually
I
already
draw
the
figure
outline
here,
it's
nearly
0%
so,
which
means
financial
gain
is
a
huge
incentive
for
the
point
in
a
sec.
They
only
deployed
in
a
sec
when
they
can
get
a
financial
incentive.
L
The
second
perspective
is
registered,
so
we
found
that
obh
and
GoDaddy
registers
on
supporting
DNR
secondary
for
name
servers,
but
OVH
provides
it
for
free,
but
GoDaddy
you
have
to
obtain
by
paying
$35
3
contractivity
anderson
as
you
can,
as
you
can
expect.
The
OVH
DNS
circuit
paloma
ratio
is
over
20%,
but
code
Adi
is
nearly
3
percent,
so
free
DNS
tab,
of
course,
support
and
encourage
encourages
user
to
deploy
in
a
sec,
and
the
third
perspective
is
reseller
C
of
one
umbrella.
L
Spherical
antagonist
is
a
registrar
for
NL
domain
name,
but
there
are
reseller
Furtick
on
the
coordinate,
so
the
top
graph
shows
the
number
of
domains
they
manage
and
the
bottom
graph
shows
the
percent
of
domains
with
a
DNF
ski
and
the
TS
record.
So,
as
you
can
tell
from
the
white
line,
the
DNS
exploration
for
an
L
is
nearly
100%,
which
is
good.
But,
interestingly,
we
observed
that
there
is
a
gradual
deployment,
increasing
ratio
for
the
other
domain
names
the
reason.
L
Instead,
this
register
his
antagonist
actually
started
to
deploy
the
NSA
at
the
end
of
20
2014.
But
what
what
happened?
Was
they
switch?
It
a
register.
The
supporting
of
the
NSA,
but
the
migration
only
happens
when
the
current
domain
name
expires,
so
they,
after
the
previous
domain
name,
expires.
They
migrate
to
a
new
registrar
that
supports
the
NSA.
So
that
is
the
reason
why
you
can
see
kind
of
gradual
deployment,
so
complex
relationship
between
reseller
registrar
also
result
in
a
and
of
slow
deployment
of
the
NSA,
and
the
other
perspective
is
third-party
desecrater.
L
L
So
what
you
need
to
do
is
copy
a
distant,
a
TS
record
and
pass
it
to
the
registrar
to
ask
them
to
note
it
to
the
registry,
but
the
khakhra
shows
percent
of
DNS
key
with
TS
record
or
interestingly,
even
though
the
DNS
key
deployment
in
the
bottom
graph
increasing
right,
but
still
50
percent
of
domain
names
with
the
NF
ski
still
failing
to
deploy
the
s
record.
This
could
be
either
one.
The
administrators
didn't
understand
correctly.
L
L
Today,
only
four
out
of
two
actually
is
for
a
4
out
of
20
register
support
the
inner
cylinder
of
their
cue
name,
servers
or,
interestingly
15,
out
of
20
support,
unloading,
OTS
a
custom,
yes
record,
so
comparing
to
the
Reaser
of
2017,
it
has
been
improved,
but
it
requires
much
more
at
roughly
so
the
NSF
deploy
depends
on
many
policies.
Register
is
supported
for
free
registry,
it'll
be
great.
L
If
it
they
can
offer
financial
incentive
and
reseller
be
over
to
choose
a
partner
register
and
also
when
you're,
using
third-party
I
guess
the
CD
CD
nm
scheme
new
protocol,
which,
although
users
to
another
TS
record
directly
to
the
registry
and
without
any
support
from
the
registrar
will.
This
will
be
very
good
solution.
I
guess
so.
C
G
Let's
her
to
Cariah
saya
great
talk
entertaining
too
and
I
don't
mean
because
of
the
projector
looking
are
you
doing?
Are
you
continuing
to
do
long
running
statistics
gather
gathering
and
are
you
publishing
it
live
at
all
and
then
I
might
offer
to
collaborate
a
little
bit
so
I
actually
have
a
webpage
called
stats
in
a
sec
tool.
G
Tour
where
we
in
Victor
Duchovny
publish
continually
daily
updating
stats
of
DNS,
SEC
deployment
and
Dane
deployment
in
particular,
and
it
would
be
really
cool
to
merge
those
I
think
yeah
Victor
has
a
lot
of
data
that
you
probably
don't
have
it.
You
have
a
lot
of
data
that
I
think
Victor
doesn't
have.
So
we
should
talk
yep
sure
absolutely,
but
are
you
running
it
continually
or
you
yep?
Okay,
awesome.
M
So
you
might
have
your
zone
hosted
on
maybe
CloudFlare
provider,
so
your
zone
might
be
xyz.com
or
whatever
might
be
multi
vendor,
where
it's
hosted
on
or
at
one
android
or
two
in
that
case
again
achieving
DNS
SEC
it's
hard
because
just
matching
the
keys
and
des
record.
So
that's
another
angle
that
you
can
look
at
of
the
zones
that
you
are
scanning
if
they
are
multi
vendor.
M
G
All
right,
yep,
nice
presentation,
you
might
also
on
those
some
30%
that
don't
have
D
s
records.
One
of
the
very
common
things
that
happens
is
people
start
playing
with
DNS
SEC
and
the
first
thing
they
do
when
they
aren't
sure,
is
though
Yankee
BS
records
from
the
parent,
because
then
you
simply
go
undetermined
as
opposed
to
going
invalid.
So
you
may
want
to
start
going
back
and
resampling
on
a
recurring
basis
of
who
may
have
d
s
records
appearing
and
disappearing
yep.
N
Can
I
respond
to
that
as
well,
so
I
would
run
of
the
coasters.
Is
it
paper
we
looked
at
that
and
it's
not
people
playing
around
with
Deena
sake.
It's
people
simply
not
deploying
deploying
IDs
in
one
TLD.
They
sign
everything
they
own.
They
signed
a
whole
portfolio,
but
then
they
only
deploy
the
s
and
the
T
of
these
that
give
them
a
financial
incentives
such
as
not
available
to
see.
O
O
P
Rick
well,
how
embarrassing
I'm
just
one
question
in
the
and
chart
24
one
good
presentation
certainly
appreciate
it
on
24.
This
is:
where
sort
of
the
15
odd,
let
me
see
a
different
chart
24.
This
is
where
the
chart
where
the
15
out
of
20
20
comes
up
and
I'm
curious
as
to
why
the
the
ones
that
provide
the
upload
by
email
yeah
this
one
here,
why
they
weren't
counted
as
being
supportive
of
DNS
SEC,
even
though
they
don't
appear
to
do
it
based
on
when
the
research
was
done
through
their
web
portal.
P
C
K
L
K
K
P
K
What
the
issue
is
here
is
that
as
many
domains
that
you're
looking
at
most
of
them
are
for
small
to
medium
businesses,
small
to
medium
businesses,
don't
have
an
IT
department
mm-hmm.
They
also
probably
don't
really
understand
DNS,
so
heading
DNS
SEC
on
top
of
that,
doesn't
make
that
any
better
for
them.
L
Yes,
but
first
small
companies
and
the
we
thought
we
many
times.
These
are
anecdotal
examples
we
sometimes
or
observe
these
small
companies
just
relying
on
the
default
names
over.
It
means
if
I
register.
So
that
is
why
we
are
encouraging
all
registers
to
support
NSA
on
their
default
name
servers.
If
that's
the
case,
then
they
don't
the
small
companies
to
do
not
need
to
care
about
the
intercept,
because
it
will
automatically
turn
the
dns
set.
Sure.
C
Okay,
so
that's
everything
for
this
meeting.
Thank
you
again
to
both
the
speaker,
something
that
was
two
really
excellent
talks.
I
think
both
TJ
and
Mehta
will
be
around
for
at
least
tomorrow,
I
think
possibly
most
of
the
week.
So
if
you're
interested
in
the
work,
please
grab
them
in
the
hallways
and
thank
you
for
your
attention.
