►
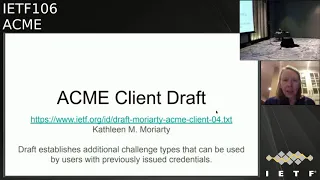
From YouTube: IETF106-ACME-20191122-1220
Description
ACME meeting session at IETF106
2019/11/22 1220
https://datatracker.ietf.org/meeting/106/proceedings/
A
B
B
B
They
can
be
either
you
know,
there's
probably
gonna
be
about.
They
can
be
assured
as
five
sentences
describing
what
conclusions
we
come
to.
It
will,
of
course,
all
be
confirmed
on
the
list.
Anyone
to
volunteer
to
take
minutes
you
just
sort
of
compose.
Thank
you,
you're
wrong.
Okay,
do
it
on
the
etherpad?
If
you
want
or
just
compose
a
mail
message,
stack
me
and
then
hit
Send,
and
then
your
job
is
done.
B
B
B
B
B
Remember
we
are
the
it
was
it.
It
was
a
push
button
on
PowerPoint
that
said,
make
all
letter
Heights
the
same
width
I'm
mad
I
was
great.
I
was
like
looking
free.
You
know
one
of
those
fuzz
out
options
and
I
didn't
see
so
I.
Just
yeah,
though
the
weird
the
weird
thing
about
this
is,
if
you
look
at
the
at
the
end
of
the
third
line,
were
where
it
says
carefully:
that's
in
period
not
an
L
that
it
stretched
out
to
the
same
height
as
all
the
other
letters.
B
Okay,
yeah
come
on.
Okay,
no
well
continued
there,
we
go
all
right
document
status.
These
are
the
ones
that
are
done.
Draft
Acme
CAA
was
in
the
queue
was
published
two
days
ago
three
days
ago,
so
cool
Acme,
IP
challenged
IP
address
challenges
in
the
queue
TLS,
a
LPN
in
the
queue
and
Acme
star,
which
is
sort
of
the
first
of
two
of
the
short-term
certificate.
Stuff
is
also
an
acute.
C
You're
on
shuffle
we
haven't
published
Rev
since
last
IDF.
We
did
meet
with
people
from
city
and
I,
so
we
have
better
understanding
of
that
use
case
and
the
next.
So
the
draft,
the
next
big
thing
on
the
draft
right
now
is
a
way
for
the
identity
owner
to
to
signal
a
csr
template
to
the
name
delegation
client,
so
that
the
NDC
can
actually
generate
a
CSR
policy.
B
D
Hey,
can
you
me
yes,
okay,
fantastic,
so
yeah
I
just
wanted
to
say
we
did
submit
new
version
of
the
both
of
the
two
acmetropolis
related
to
the
ongoing
stir
work.
The
good
news
is
we're
now
getting
the
point
actually
where
the
stir
CAS
are
imminently,
gwyne
to
diploma
it's
a
goal
at
least
America,
that
there
will
be
initial
shakin,
CAS
and
December
timeframe.
D
Actually,
it's
pretty
cool
weather
Acme
immigration
would
be
part
of
that
initial
phase
of
it
we're
not
quite
sure
yet
we
think,
probably
more
at
the
end
of
January,
we'll
have
some
better
visibility
into
exactly
when
that
is
gonna,
get
factored
into
the
way
that
practically
these
certificates
get
issued.
I
think
it's
still
everyone's
long-term
plan,
it's
written
into
all
the
at
aspects,
but
as
with
many
of
these
kinds,
there's
like
a
tremendous
interest
in
just
getting
something
out
now
that
is
signing
calls
and
working
so
I
mean
I.
D
Think
my
intuition
on
news
is:
we've
submitted
these
versions,
I
think
they're,
probably
stable
I
would
still
hold
them,
though,
for
another
cycle,
I
think
just
because
I
kind
of
want
to
see
what
is
gonna
happen
and
what
at
us
is
gonna
end
up
correcting
or
not.
As
you
know,
we
do
the
initial
rollout
of
these
things,
and
so
I
would
say
what's
CDs
again
in
Vancouver
I
doubt
they'll
be
any
different,
but
they
might
be
okay,.
D
I
mean
you
know,
I
see
no
reason
to
last
call
it
until
we,
you
know,
get
at
least
this
initial
deployment
out
of
the
way,
and
we
know
that
since
I
mean
it,
you
know
there's
CDs
and
stuff
already
out
there.
It's
like,
let's
just
see
what
happens
for
a
bit,
but
let's
target
that
we
probably
could
like
push
these.
Not
these
done
and
around
Vancouver.
Okay,.
A
B
B
E
C
F
B
G
B
B
B
H
H
Think
I
know
what
to
do
about
this
at
this
point.
I
think
because
this
document
requires
expertise
from
like
as
mine
people
as
well
as
acne
people
as
well
as
pure
email,
people
I,
will
I
think
it's
ready
for
working
group
law.
Scholars
is
knowing
that
there
is
one
issue
that
I'll
fix
and
particularly
if
people
can
have
a
look
at
security
considerations
that.
B
Okay,
how
many,
how
many
people
use
email
all
right?
How
many
of
those
would
be
hands
up
of
red?
Yes,
it
was
a
leading
question.
How
many
of
you
read
the
document
Thank
You,
Russ?
Okay,
what
we'll
do
I
mean?
It
was
the
timetable.
Was
you
know
before
next,
before
Vancouver
or
in
Vancouver?
So
we'll
do
a
last
call
will
issue
a
last
call
after
the
holidays
early,
you
know
January,
okay
and
then.
H
H
H
B
I
Okay,
so
this
is
a
new
draft.
It
was
split
out
from
Jack
me
into
great
construct
based
and
feedback
last
time
around.
So
what
this
does
is
what
the
Acme
specification
allows
you
to
do.
Is
it
allows
and
based
in
C
a
policy?
It
allows
an
ACME
client
to
prove
the
main
ownership
of
a
parent
domain
and
then
allows
declined
to
register
and
obtain
certs
for
all
the
subdomains,
when
I
would
have
to
do
an
explicit
proof
of
ownership
for
all
two
subdomains.
I
I
I
It's
just
using
standard
DNS
text,
authorization
for
the
prove
it
on
the
parent
domain
and,
on
the
right
hand,
side
it
declines,
is
placing
an
order
for
a
subdomain
of
that
parent
domain
and,
what's
not
illustrated
here,
but
what
is
possible
and
allowed
is
declined
can
place
new
water
request
for
multiple
different
clients
hurts
off
that
subdomain
without
having
to
do
an
explicit
authorization
for
each
one
of
those
subdomains.
Okay,
next
slide
so
the
direction.
So
when
I
talked
about
this
last
time
around,
we
said
2-0
changes
required
to
baseline
Acme
to
support
this.
B
I
So
this
one
minor
change
it's
in
a
wrapper
that
have
raised
and
it's
fixing
of
two
hundred
rock
a
response
who
are
appropriate
currently
RFC.
If
I
fight
the
text
mandates
a
to
one
response
to
all
new
all
set
requests
and
clearly
that
doesn't
make
sense
if
client
issues
and
when
you
are
the
same,
knew
what
set
request
twice
and
it
in
what
said
request
art
the
object
already
exists,
and
so
that's
what
acne
some
of
the
mains
does
is.
If
the
authorization
already
exists,
it
recommends
returning
at
200,
okay
and
set.
It
was
201.
I
I
Matter,
okay,
nevermind,
there's
one
one
minor
addition,
which
is
an
a
new
directory
metadata
field
for
a
server,
can
advertise
whether
it
supports
and
subdomains
or
not
and
based
on
feedback
on
kind
of
member
holders.
On
the
matters,
where
was
private,
if
there's
no
field
entry,
there
is
no
assumed
default
value,
so
the
server
doesn't
specify.
Then
the
client
doesn't
know
and
that's
it,
and
so
that's
it.
So
it's
missing
security
considerations,
but
Tim
has
said
he
will
write
these
Tim
as
a
co-author.
He
said
be
right
here.
I
B
B
J
In
some
respects,
this
is
like
a
wild
card,
not
in
every
respect,
but
in
this
best
that,
like
the
authorizing
for
the
parent
but
then
you're,
you're,
you're
issuing
for
the
child
and
I
was
just
hoping.
You
could
contrast
the
security
implications
of
that
with
a
wild
card,
because
the
wild
card
is
an
explicit
indicator
in
the
document
for
in
the
transaction
that
you're
doing
a
walker
certificate.
So
I
don't
know
I'm,
you
thought
it
through,
but
I
sort
of
like
as
I
was
reading.
I
was
like
that's.
J
J
Sure
yeah
I
mean
a
certain
a
blocker
to
acceptance,
but
it's
a
walker,
but
you
think
about
it
as
we
move
forward
with
this
yeah
I
guess
I
recall,
like
I,
think
I'm
a
little
denial
of
the
Savior,
because
I
recall
when
wild
cars
were
first
being
done
with
acne.
There
was
like
talk
of
like
they're,
doing
a
random
challenge
for
a
second
subdomain,
and
it's
like
anyway
like
worth
we're
thinking
about
as
we
as
we
go
for
yeah.
J
Not
I'm
not
sure
my
concern
is,
if
I
even
have
one
but
I
guess
what
I
remember
it
is
it's
like
when
did
like.
Obviously,
there's
there's
like
Kern
Acme
right
has,
as
I
said,
has
like
a
challenge
check
for
like
the
wrong
card
and
one
for
the
non
wild
card.
There's
indicator
in
the
messages
somewhere
and
I'm
trying
about
why
us
there
and
so
I
can
tell
I
remember
why
that's
there
I'm
not
sure
whether
it
we
need
something
like
that
here.
J
K
M
J
Agreed,
but
my
understanding
is
so
I
think,
there's
the
issuance
pieces,
the
verification
piece
because
I
understand
it.
This,
like
bootstraps,
a
verification
for
the
parent
domain
into
an
arbitrary
number
issuances
for
the
child
domains,
and
so
in
that
respect,
it's
like
a
what
and
that
respect
it's
like
a
wild
card
in
it.
You
did
one
dedication
that
correspondence
somehow
to
the
parent,
and
now
your
issue
and
now
you're
getting
certificates
that
for
the
children
now,
the
fact
you
have
to
get
multiple
cific,
it's
like
is
is
like
a
different.
J
It's
there
for
anaesthetic,
aliy,
but
it
still
has
the
property
that
the
that
the
caught
that
yeah,
that
the
client
is
basically
good.
The
client
is
basically
getting
authorized
for
everything
on
everything,
the
left
of
the
other
parent
and,
in
one
case,
that's
like
a
silent,
the
in
which
case
in
one
case,
taking
advantage
of
her
authorization
for
each
subdomain
requires
a
transaction
in,
but
in
other
case
it
is
not,
but
in
it's
still
like
the
same
authorization
logic.
M
J
It's
very
common
I
mean,
like
you
know,
but
I
guess
I
mean
the
in
the
usual
assumption.
The
usual
assumption
in
DNS
right
is
the
parent
controls
child,
but
it
doesn't
necessarily
mean,
but,
as
I
say
on
the
in,
in
this
context,
I
mean
in
this
like
I,
say
this
contest
I'm
just
saying
we
had
a
special
indicator
that
said
I'm
getting
authorization
for
everything
the
left
of
this,
and
we
did
that
when
we
did
a
wild
card
and
I'm
just
saying
this.
M
N
This
is
d
kg,
so
the
you
can
measure
roughly
how
common
it
is
that
something
like
this
might
be
problematic
by
looking
at
the
public
suffix
list.
So
the
public
suffix
list
is
is
definitely
not
short
and
it
includes
lots
of
instances
of,
but
not,
but
is
not
exhaustive,
but
instances
of
organizations
where
that
have
sort
of
child
subdomains
that
that
probably
shouldn't
involve
x.509
issuance
just
because
the
parent
is
authorized
or
because
one
of
the
children
is
authorized.
So
so
so,
yes
is
an
issue.
N
The
authorization
is
very
similar
to
doing
a
wild
card
and
I
wonder
once
again
which,
since
we
failed
at
D
bound
this
may
be.
There
may
be
some
subtle
differences
between
this
and
actually
issuing
a
wild
card,
sir
itself,
and
maybe
there's
another
cut,
we
need
on
the
PSL
so
be
good
to
talk
to
folks
for
working
on
that
hoping
selfies
list.
A
B
I
Okay,
and
so
so,
this
one
was
presented
last
time
around
and
subdomains
was
part
of
this
last
time
around,
but
we
split
her
out
into
separate
draft.
So
what
this
does
is
describes
how
acne
can
be
integrated
with
multiple
other
structural
mechanisms,
primarily
ESG,
based
ones
which
brewskis
based
on
top
of
on
teep
next
slide,
so
documents
a
few
different
use
cases,
acne
integration,
est,
active
integration,
risky
acne
integration
with
a
variation
of
risky
which
is
risky
default
card,
registrar,
acne,
integration
with
teep
and
Alec
and
I
are
working
on.
I
A
new
draft
keep
updated,
shows
how
acne
integrated
with
this
as
well
and
the
fact.
We
think
that
acne
doesn't
really
fit
well
into
into
baseline
teep
and
acne
needs
the
tip
extensions
that
we've
defined
and
number
five,
and
that's
primarily
around
peak
as
he
is
10,
because
he
is
seven
handling
and
CSRF
crude
hunting,
etc.
Next
slide,
what's
changed,
acne
subdomains
has
been
split
out
into
a
separate
dock
and
whiskey
cloud
rights,
for
our
use
case
has
been
added,
but
it's
pretty
much
the
same
as
brewski
from
an
acne
perspective.
Next
slide.
I
Okay,
so
est
NTP
used,
you
can't
eat
those
specifications,
define
how
the
client
interacts
with
the
EC
or
the
teep
server,
but
they
do
not
specify
it's
explicitly
out
of
scope.
How
the
est
or
teep
server
interacts
with
the
backend
CA,
and
what
this
draft
does
is
glue
the
two
together
and
show
how
acne
can
be
used
as
that
integration
between
either
the
est
or
the
teep
server
and
the
acne
CA
next.
I
So
the
slide
here.
This
summarizes
what
an
est
integration
could
look
like.
On
the
left
hand,
side
we
have
pre-authorization
of
a
parent
domain,
so
I'm
reverting
the
subdomain
draft
here.
So,
on
the
left
hand,
side,
the
est
RA
is
doing
pre-authorization
of
a
parent
domain
and
the
on
the
right
hand
side.
I
When
a
client,
that's
called
a
pledge
here
when
a
client
or
a
pledge
is
doing
a
simple
enroll
against
the
est
or
a
the
East
er
a
can
turn
around
and
do
an
acne
integration
and
get
a
search
you'd
for
a
subdomain
identifier
after
parent
to
me-
and
it's
previously
authorized
and
what's
missing
here,
but
doesn't
really
integrate
impact
this
integration
per
se.
But
it's
documented
in
the
draft-
and
not
here
is
declined,
should
really
be
doing
a
serious
or
attributes
request
response.
I
First
and
it's
document
in
the
draft
just
not
shown
in
the
slide
I,
don't
think
I've
shown
on
this
slide.
Next
slide.
Yeah
I
haven't
shown
explicitly
the
the
tip
College
Law,
but
the
tip
call
floor
looks
very
similar
to
this
and
it's
in
the
it's
in
the
draft
next
slide,
and
so
especially
from
this
again
is
some
security
considerations
are
missing,
and
but
this
doesn't
require
any
changes
whatsoever
to
es
T
or
T
pop
date,
and
it
doesn't
require
any
changes
to
Acme.
I
It's
just
informational
and
stitches,
showing
how
you
stitch
you
two
together
and
the
integrations
do
span
across
tree
working
groups,
anima,
acme
and
emu,
so
we're
wondering
Curtis
leaves.
Is
there
interest
in
so
the
questions
for
the
room
is
history
interest
in
continuing
this
work?
What
do
we
do
next
and
if
anyone
is
interested
in
adopting
it,
where
should
we
adopt
it?.
B
I
K
Co-Author
on
this
and
involved
in
all
those
working
groups,
I
think
that
that
that
we
felt
that
the
things
that
we're
doing
were
more
technically
Acme
things
and
we
really
need.
We
really
will
come
to
your
group
easier
than
you'll
come
to
our
group
to
give
us
input.
So
we
would
rather
do
it
here.
Then,
in
our
group,
that
was
our
feeling
at
the
time.
Okay,.
B
B
I
L
I
B
I
G
Doing
it,
that's
that
was
the
main
question.
Okay,
thank
you!
So
high
vroom
engine
lui,
I
may
not
have
it
remember,
you're
right
so
just
gonna
kind
of
correct
me,
but
to
emu.
I
didn't
hear
the
conversation
back
and
forth
so
he
knew
there
was
interest
and
and
kind
of
work,
but
we
punted
the
discussion
about
what
to
do
which
working
we
want
to
do
it
actually
to
here.
Okay,.
B
C
B
B
I
Yeah,
so,
okay,
this
the
last
presentation.
This
is
something
else
that
came
up.
An
annuity
currently
been
discussed
in
the
email
are
not
directly
related
to
any
of
these
two
presentations
and
but
there's
a
conversation.
Ongoing
DME
mailer
about
documenting
clear,
best
practice,
recommendations
to
supplicants
for
how
they
should
check
the
identity,
search
that
an
each
server
presents
to
it.
I
Recommendations
for
what
a
supplement
should
check
and
depending
on
whether
it's
presented
with
a
private
CA
certificate
or
a
root,
Republic
CA
certificate
and
and
we'd
really
like
somebody
from
a
public
CA
to
help
write
those
recommendations.
We
think
we
know
what
they
should
be
or
we
need
somebody
from
actually
run
the
public's
here
to
help
with
that.
So
we're
looking
in
for
health
in
you
with
them
drafting
those
best
practice
recommendations.
B
M
I
I
M
I
M
I
Well,
if,
if
you're,
if
the
supplicant
knows
it's
presented
or
a
private
CA,
then
it
makes
sense
to
check
in
EKU.
But
if
it
knows
it's
presented
with
a
identity,
cert
that
signed
by
one
of
the
public
see
is.
There
is
absolutely
no
point
in
checking
with
this
field.
It
can
only
really
check
for
a
DNS
name
and
it's
it's
hammering
out
exactly
what
the
best
practice
recommendations
should
be.
K
K
O
N
This
is
Daniel
con,
Gilmore
I'm,
just
gonna
repeat
what
I
think
I
just
heard,
but
I
think
I
just
heard.
Is
we
don't
believe
as
the
community
of
technical
people
who
work
with
these
authorization
systems
that
it
is
possible
to
use
the
web
PKI
with
anything
that
the
EKU
field
is
meaningful
because
we
cannot
possibly
hope
to
change
any
of
it?
Is
that.
I
M
M
Right
one
is
the
EKU
and
the
other
one
is
the
identity,
and
so
the
identity
they
want
to
put
in
this
is
a
private,
non
verifiable
identity,
the
SSID
right.
So
that's
the
big
problem
from
a
commercial
CA
point
of
view,
because
they
issue
a
cert
was
something
in
there
that
they
can't
validate.
They
get
in
trouble
and
somebody
beats
up
on
them
and
you
probably
know
who
that
will
be
so
I've
heard
it
it's
fun.
Well
me
not
really
so
so
that's
the
first
problem,
the
identity
problem,
I
believe,
is
the
big
problem.
M
The
little
problem
is
in
EKU
and
I'd
like
to
see
the
EKU
change
because
I've
had
is
it
so,
but
they're
not
yeah
yeah
be
nice
if
they
used
it
right
so
and
that's
a
small
problem.
So
that's
just
it.
That's
just
you
know
working
through
the
process
of
getting
it
like
you
able
to
get
one
of
those
right.
It's
it's
already.
It's
already
defined
it's
already
there.
It's
just
a
matter
of
changing
the
process
so
that
you
can
actually
get
one.
The
bigger
problem
is
the
identity
piece,
but.
I
N
Of
the
different
EKU
is
it
allows
you
to
identify
that
the
verification
process
is
differ
from
your
verification
process.
That's
used
for
sure
the
the
server
off
yeah,
and
so
that
way
a
if
a
public
CA
wants
to
issue
something
like
that
as
long
as
they
don't
also
issue
it
with
the
server
auth
EKU,
then
they're
not
violating
what
they
claim,
they
would
be
doing
right,
which
is
rechecked
for
server
off
in
the
following
way.
You've
got
a
separate
thing.
N
Yes,
you
do
need
to
define
how
you
verify
that
identity
there
mm-hmm,
but
you're
no
longer
are
worried
that
someone's
going
to
use
one
of
these
certificates
in
this
other
context,
where
they
shouldn't
be
allowed
to
use
it.
So
if
we
think
that
that
that
CA
is
king
can't
issue
an
alternate
EKU,
then
we
have
really
done
something
terribly
wrong,
because
we've
boxed
them
out
of
operating
the
space
and
asking
them
to
use
it
as
certain
asking
them
to
use
server.
N
K
Michael,
it's
a
chicken
and
egg
problem,
we're
not
a
big
enough
market
for
them
to
care.
So
we
have
to
find
a
way
to
flow
through
their
existing
market
mechanism,
which
sucks,
but
the
alternative
is
that
either
we
have
clients
that
get
our
man
in
the
middle
because
they
they're
easily
they'll
bind
to
any
public
name
right
or
we
have
private
CAS
that
we
have
to
monitor
leakin
figure
into
clients
which
defeats
the
whole
zero.
You
know
touch
point
right,
so
we
have
this.
This
thing,
like
you
know.
K
Yes,
we
want
to
use
the
technology,
as
you
say
right,
but
we're
not
yet
we
we
don't
have
enough
enough
leverage
to
actually
make
it
happen.
So
what
are
we
gonna?
Do
we're?
Basically,
wind
up,
you
know:
pin
zero
zero,
zero
again
right.
That's
what
happens
if
we
can't
go
forward.
You
know
I
mean,
pin
zero,
zero,
zero,
yeah,
okay,.
M
P
So
yeah
this
is
just
Holloway
I,
think
that
this
is
kind
of
a
mess
and
I
don't
know
that
there's
an
easy
way
out,
but
there
is
one
thing
that
many
you're
like
four
or
five
years
ago,
the
Wi-Fi
Alliance
was
working
on
some
hotspot,
2.0
thing
where
they
did
I
believe
there
is
a
CA
that
issues
certificates
for
hotspots,
which
might
be
what
you
want.
I,
don't
know,
but
might
be
something
to
look
into.
Okay,.
