►
From YouTube: IETF106-NTP-20191120-1000
Description
NTP meeting session at IETF106
2019/11/20 1000
https://datatracker.ietf.org/meeting/106/proceedings/
A
A
B
A
A
A
So
this
is
our
agenda
for
the
day
we
have
and
we're
at
the
administer
the
agenda
bassing
portion
of
the
session.
So
this
there
have
been
a
number
of
changes
from
what
was
posted
into
the
data
tracker.
So
we
have
to
go
back
and
update
that
a
little
bit,
but
there
has
already
been
some
bashing
today.
Any
other
agenda,
bashing,
nope
all
right.
A
A
A
We
will
get
that
working
group
last
call
out
this
week,
given
the
holidays
and
everything
we
will
make
it
a
three
week
working
group
last
call-
and
if
you
have
any
questions
now,
would
be
a
good
time,
because
the
author
is
going
to
exit
for
another
meeting
shortly,
all
right.
So
there's
no
questions
on
that
excellent
and
then
the
remaining
document
that
we
have
that
we
won't
be
discussing
more
detail
later
today,
is
the
inter
leave
modes.
We
did
a
working
group
last
call
on
that
and
that
is
still
to
be
resolved
as.
A
So,
additionally,
that
we
do
have
two
documents
that
have
been
adopted
since
the
last
meeting
and
one
is
on
rough
time
and
the
other
one
is
on
the
Chronos
work
that
Mehta
was
doing.
There
are
no
updates
for
either
of
those,
so
my
request
to
the
working
group
would
be
to
start
reviewing
them,
so
we
have
agreed
to
develop
these
two
documents,
it's
time
to
start
making
progress
on
them.
Any
questions
on
these
two
documents:
oh
okay.
A
A
A
C
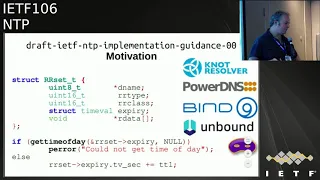
So
this
document
sort
of
came
out
of
a
internship
that
intraoral
did
with
enamelled
loves
to
study
the
impact
of
vulnerabilities
of
ntp
on
DNA,
send
in
a
check
to
do
a
impact
study,
and
we
wish
a
few
things
which
vulnerabilities
that
could
have
been
mitigated
within
the
dienes
of
hair
itself.
So
the
applications
did
not
use
certain
time
values
correctly.
C
C
So
you
see
in
the
nest
as
the
TTL
for
certain
DMS
record
it's
a
period.
We
call
this
relative
time
instead
of
a
specific
point
in
time,
which
we
call
a
absolute
time
and
DNS
software.
Typically,
the
not
not
visual
for
parody
image
by
nine
inbound
antennas
mask
implemented
this
as
taking
the
current
world
clock
point
of
time
and
then
adding
the
period
to
it
and
scheduling
the
expiry
date.
For
that
point
in
time
which
made
it
fellow
go
for
cash
sticking
attacks,
cash
exploration,
attacks.
C
So
that,
in
the
documents,
it's
the
scope
is
to
explain
what
kind
of
methods
there
are
to
express
time
for
applications
or
the
absolute
point
in
time
versus
their
periods
and
the
different
clocks
that
are
maintained
by
digital
systems,
which
may
be
used
to
deal
with
those
different
time
mechanisms
and
what
the
trade-offs
are
between
using
the
one
or
the
other.
And
that
gives
from
guidance
to
help
implementers
make
informed
choices.
C
From
the
description
in
document
on
implementation
approaches
in
a
example,
you
can
get
the
different
clock
times
with
a
perfect
system
and
a
business
system,
so
the
research
visuals
that
we
did.
The
impact
study
on
DNS
was
first
presented
at
the
IP
key
two
years
ago
here
in
Singapore
at
the
ITF
100.
At
the
same
time,
we
presented
this
draft
trying
to
provide
guidance
to
application
implementers
I
think
the
written
group
was
or
wanted
to
work
on
this.
But
then
there
was
a
sort
of
critique
on
the
terminology
used
in
the
draft
at
that
moment.
C
So
we
leave
out
the
complete
terminology
and
made
it
to
restricted
to
be
the
bare
minimum
to
describe
a
huge
which
was
presented
one
year
later
at
the
ITF
103
in
Bangkok
and
the
I
think
was
received
well
by
the
working
group.
There
were
a
few
comments
which
I've
merged
into
the
documents
or
addressed
in
the
document
which
was
presented
at
the
last
ITF
in
Montreal.
C
A
So,
between
the
last
meaning
in
this
one,
we
adopted
this
as
a
working
group
draft.
Has
anybody
reviewed
the
draft
that
was
published
anybody
either?
Any
folks
I
know
that
we
are
missing
a
number
of
our
regular
working
group.
Participants
at
this
particular
meeting.
Are
there
anybody?
Is
there
anyone
in
the
room
that's
willing
to
commit
to
reviewing
this
draft
there?
We
go
okay.
B
B
B
B
D
At
ITF,
1.1
or
Bundy
started
missing
a
cat
once
the
first
hackathon
for
for
the
NTS
draft,
the
first.
At
that
time
it
was.
There
were
only
two:
the
proof
of
concept,
implementation
for
Martin
Allen
from
tenure
function,
and
we
had
been
following
hackathons
in
ITF
102.
He
skipped
one
Osby
and
the
man
of
Abia
of
already
had
for
implementation,
which
proved
into
about
interoperability.
D
So
to
speak
that
have
been
basically
met,
not
people
who
implement
who
did
work
on
there.
:
implementation
of
the
NTS
and
this
time
Krista
was
there
to
prepare
scripts
for
monitoring
Santa's
operation
and
to
write
somehow
tools
and
service
wise
I've
tried
to
to
compile
the
list
of
services
NTS
services
already
available,
and
at
this
table
you
will
see
six
available
available,
NTS
services,
the
first
one
from
the
University
of
Australia,
which
is
basically
Martin
langa,
then
CloudFlare,
who
was
the
first
to
announce
this
actually
and
that
net?
D
E
E
D
F
Hi,
my
name
is
Sanjeev
and
to
be
sick.
The
version
which
supports
NDS
is
already
in
the
Debian
distribution
and
downstream
of
it
as
well.
It
will
be
available
in
the
new
version
will
be
available
in
1900
in
2004,
in
Ubuntu
as
well.
I'm,
not
sure
about
fedora
also
has
NTP
SEC,
but
their
default
client
is
Kony,
so
I'm
not
sure
how
many
federal
guys
will
install
NTP,
SEC
or
dokoni
also
has
NDS
support
so
from
the.
A
What
we
currently
have
is
a
list
of
items
in
a
wiki
in
the
NTP
wiki,
so
I
don't
know
some
of
the
key
folks.
That
would
help
leave.
This
conversation
are
not
here
this
time,
so
they
I
guess
what
my
quite
my
my
ask
to
the
working
group
is:
if
you
go
and
you
look
at
the
NTP
wiki
supported
by
the
IETF,
there
is
a
number
of
NTP
v4
issues
that
have
been
identified,
and
so
we
haven't
committed
to
doing
an
NTP
v5.
A
G
A
Not
yet
it's
really
a,
we
had
been
resisting
it
for
a
while
I
think
we
wanted
to
get
into
yes
out
the
door
and
so
I
think
in
the
next
meeting
or
two
well.
There
is
the
there
is
a
goal
in
a
sense
that
we
have
been
talking
for
quite
a
while
about
combining
NTP
and
tik-tok
and
chartering
a
single
time
working
group.
So
that
is
something
that
that
Suresh
is
smiling
at
me,
because
we've
been
talking
about
it
for
a
while.
A
Right
so
and
I
think
the
context
of
discussing
that
charter
will
also
talk
about
a
timeline
but
I.
Think
it's
one
of
the
challenges
that
I've
found
over
the
years
in
this
working
group
is
there's
a
lot
of
you
know.
A
lot
of
folks
will
tell
you
what
we
should
be
doing,
but
it's
a
real
challenge
to
get
people
to
step
forward
and
write
the
documents
and
so
developing
a
timeline
for
NT
p
v5
without
people
that
are
willing
to
actually
write
the
documents
is,
is
a
challenge
so
I.
A
You
know
I
think
at
this
point,
we're
really
trying
to
clear
off
all
of
our
things
that
we
haven't
gotten
done
and
get
them
out
the
door
recharter
and
then
talk
about
a
timeline.
So
but
in
the
mean
time
I
mean
we
had
a
fairly
robust
conversation
on
this
in
our
last
virtual
interim
and
I.
Think
that
doing
that
in
the
context
of
I,
think
it
would
be
helpful
to
do
to
have
those
conversations
when
you
go
ahead
and
begin
pulling
the
pieces
together
identifying
what
we
think
we
should
solve
and
said
shouldn't
solve.
A
But
there
are
a
number
of
things
that
I
think
the
other
thing
was.
There
was
a
number
of
drafts
that
came
through
that
the
feeling
was
we
kept
trying
to
tweak
things
to
fix
them
and
before
and
the
real
answer
was
we
just
needed
to
move
to
a
b5
and
clean
up
some
of
the
things
that
were
causing
us
issues.
A
Anyway,
so
that
work
is
beginning,
please
look
at
the
wiki
and
go
from
there
any
other
questions
on
b5.
This
is
going
to
be
the
fastest
ntp
meeting
in
history,
so
go
to
the
tick-tock
working
group
status.
So,
as
I
mentioned,
there
is
a
tick-tock
working
group
and
the
plan
for
that
initially
was
that's
the
wrong
presentation.
You
need
to
go
the
chair,
slides
I,
believe
it's
the
first
time.
B
A
A
G
G
G
The
the
central
idea
of
the
draft
is
to
propose
another
kind
of
synchronization
protocol
different
for
NTP.
It's
more
intended
to
synchronize
two
end
points.
We
can
synchronize
several
the
end
points
also,
but
the
basis
is
different
because
we
send
a
packet
for
a
second
is
different
from
NTP
and
use
this
base
on
our
filtering
method.
G
We
can
reach
more
precision
in
the
frequency,
and
this
is
why
trying
to
illustrate
in
the
Nexus
we
we
added
and
idea
the
central
point
with
Antibes
when
you
try
to
to
get
NTP
server
in
some
country
like
Latin,
America
or
Africa,
it's
very
difficult.
You
are
not
20
millisecond
away.
You
are
normally
fast
and
further
than
that,
this
could
be
an
option
to
make
synchronization
for
clogs
that
the
initial
intention
for
was
to
make
some
measurements
in
one
one.
Wind
delay
in
IPP
working
group
and
the
IPP
say
me
that
tik-tok.
G
A
A
A
A
A
So
1588
version
2
was
published
in
2008
and
it
included
something
called
an
XK.
The
other
thing,
you'll
note
is
the
1588
nib
that
we
previously
published
was
for
1588
version
2.
So
in
2013
we
started
the
par
for
the
1588
revision
and
in
that
context
there
was
a
security
subcommittee
that
started
working
on
it.
The
basis
of
the
work
for
that
security
subcommittee
was
the
security
requirements
document
that
was
developed
here,
RFC
73
84.
A
We
had
originally
thought
that
the
two
solutions
would
be
a
little
bit
closer.
We
had
originally
thought
we'd
be
able
to
reuse
the
two
solutions
between
the
two
because
there's
still
they're,
both
both
basically
packet
time,
synchronization
protocols
that
seem
like
they
were
similar
enough,
that
we
would
be
able
to
get
some
crossover,
that's
not
not
where
we
ended
up,
but
there's
always
hope
for
the
future
and
just
like
in
the
last
week
or
so.
A
A
Approach
that
we
use
that
was
used
in
1588
was
to
include
security
and
mechanisms
and
guidance
that
can
be
used
together
or
in
or
individually,
and
that
the
individual
mechanisms
would
be
optional
and
one
of
the
real
challenges
was
1588
was
the
number
of
different
because
the
constituents
that
would
better
so
you
have
the
telecom
community,
the
industrial
automation
community.
You
have
a
number
of
different
communities
like
that,
and
they
all
have
different
perspectives
on
what
their
security
solution
should
be
and
the
mechanism
would
be
provided
and
then
the
applications
later
it
develops.
A
Profiles
and
based
on
those
profiles.
Profiles
is
something
that
1588
does
in
general,
it
does
tailoring
of
the
protocol
for
the
different
communities
based
on
using
profiles,
and
so
the
idea
is
that
we
would.
The
same
thing
would
happen
for
security.
Is
that
that
different
communities
would
tailor
them
differently?
A
Basically,
it
is
a
multi-pronged
approach
which
has
integrated
security
mechanism,
which
was
added
to
version
2.1.
An
export
external
transport
security
mechanisms,
which
was
just
some
guidance
talking
about
how
external
mechanisms
that
might
already
be
in
place,
could
be
used
to
help
secure
PTP
architectural
guidance
and
monitoring
and
maintenance.
A
So
if
you
look
at
the
document,
there's
going
to
be
a
normative
section,
an
option
that
is
normative
at
sixteen
dot
fourteen,
which
is
the
mechanism
itself
and
then
there's
an
access
which
is
all
of
the
security
material,
and
so
there
is
a
a
PPP
packet.
There's
a
TLB
that's
been
defined.
That
includes
the
authentication
top-4
for
security.
It's
been
added
to
the
PTP
packet.
That's
the
rough
idea
of
it
right
there
there
that
all
of
the
key
management
is
currently
left
outside
the
scope
of
this
document.
A
So
there
is
some
guidance
on
how
to
use
Tesla
and
there's
some
guidance
on
how
to
use
G,
DOI
and
they're
used
in
different
context
for
the
two
different
approaches.
Prong
B
is
Mac.
Second
IPSec
as
the
two
external
security
mechanisms
that
we
thought
might
might
be
present
and
then
redundancy
is
all
of
the
architecture.
Guidance
is
provided
and
then
finally,
monitoring
and
management
guidance.
So
all
I
really
wanted
to
do
here
was
to
sort
of
point
out
that
this
work
is
ongoing.
It
is
kicking
off
now
that
version
2.1
has
been
published.
A
A
Not
actually
expecting
any
guidance,
what
the
way
that
that
particular
that
prong
B
was
developed
was
two
different
communities
came
forward
and
said:
this
is
how
we're
using
IPSec
in
the
context
of
in
the
in
that
particular
case.
It
was
that
industrial
automation
types
of
applications,
so
it
wasn't
so
much.
How
should
it
be
used?
It
was
more
like
how
how
are
the
systems
that
we
are
currently
deploying
are
using
this
technology?
A
Now
so,
and
it's
a
really
pretty
lightweight
section,
it's
not
providing
a
lot
of
specific
guidance
on
how
to
use
it
as
much
as
it's
saying
that
there
is
probably
security
mechanisms
that
exist
in
your
in
your
system,
and
you
need
to
think
about
a
how
they
interact
with
your
time
synchronization,
because
a
lot
of
times
folks
deploy
things,
and
they
don't
think
in
the
context
of
the
impact
that
the
security
that
exists
all
around
it.
It
has
on
the
synchronization
capabilities
itself,
so.
H
A
H
A
I
H
A
All
I
really
wanted
to
do
is
to
provide
you
a
quick
snapshot.
We've
been
talking
about
it
previously
and
then
also
to
point
out
that
there
is
some
thought
about
how
NTS
might
be
used
in
this
context.
If
you
go
back
to
some
of
the
original
documents
around
NTS,
we
had
a
general
NTS
specification
and
the
thought
was
the
IETF
would
develop.
You
know
NTS
for
NTP
and
I
Triple
E
would
develop
NTS
for
1588,
that's
not
where
we
ended
up,
but
I
think
there's
moving
forward.
A
There's
still
some
places
where
we
can
reuse
technology,
which
would
be
really
helpful
so
with
that
I
think
we're
at
the
end
of
our
agenda
and
quite
possibly
the
fastest
ntp
meeting
ever
with
area
directors
are
happy
about
that.
The
one
thing
I
did
want
to
talk
about
was
virtual
interns
going
forward.
We
had
planned
last
time
to
do
two.
We
managed
execute
on
one
I.
A
Think
virtual
interims
really
helped
us
keep
a
pulse
of
getting
our
work
done.
So,
given
that
we're
coming
up
into
the
holidays,
we
will
probably
be
looking
at
one
in
early
to
mid
January.
I.
Think,
probably
December
is
going
to
be
a
little
bit
too
too
early
and
there's
a
whole
bunch
of
new
documents
that
need
review.
So
please,
please
PLEASE
start
reviewing
these
documents
and
comment
on
the
mailing
list
and
with
that
any
other
questions,
comments.
