►
From YouTube: IETF109-TEEP-20201118-0730
Description
TEEP meeting session at IETF109
2020/11/18 0730
https://datatracker.ietf.org/meeting/109/proceedings/
A
A
Can
you
hear
me
yes
now
I
can
hear
you
great
okay,
so
we've
got
both
chairs
here
and
we've
got
a
full
agenda
for
today,
since
we
only
have
one
hour.
This
is
in
my
normal
ietf
session,
so
the
note
will
apply.
Most
of
you
are
familiar
with
it
for
the
agenda
and
again
I
want
to
thank
alessandro,
akira
and.
A
A
This
is
only
a
one
hour
session,
so
hopefully
we
have
enough
time
to
get
through
all
of
this
and
dave.
I
didn't
have
time
and
I
forgot
to
to
send
out
the
rats
session
cancellation,
but
if
we
need
to,
we
can
set
up
another
interim,
perhaps
not
this
week,
but
in
a
few
weeks
we
can
do
a
doodle
poll
to
further
the
work.
A
B
B
B
So,
since
itf
108,
we
did
those
two
action
items
except
for
one
thing:
the
second
action
item,
which
was
adding
the
unneeded
tas
text.
We
revisited
so
a
little
over
a
month
ago,
october
16th,
I
posted
the
list,
the
question
that
was
raised
that
had
to
do
with
do
we
really
want
to
add
unneeded
tas
to
the
list
of
things
that
are
requested
for
rats
claims.
So
this
is
the
diagram
that
appears
in
the
architecture
document
and
has
for
a
really
long
time.
B
Whereas
you
know
what
goes
in
say,
the
t
protocol
messages
that
carry
the
evidence
well
things
that
the
tam
is
about
that
the
verifier
doesn't
really,
and
so
the
question
is-
or
the
point
was
well,
this
notion
of
requested
tas
and
unneeded
tas
they're
not
really
needed
by
the
verifier
they're
for
use
by
the
tam,
and
so
the
point
was
raised.
It
says
actually
put
him
in
the
rat's.
Claims
is
probably
the
wrong
place,
because
the
verifier
doesn't
care
that
tam
does,
and
so
the
proposal
was
just
put
them
in
the
teat
protocol.
B
Messages
not
put
them
in
the
evidence,
because
the
verifier
doesn't
care.
There
was
no
objections
raised,
and
so
that
was
done
and
you'll
see
that
that
affects
the
transport
spec
too,
and
so
now
this
principle
that
claims
are
used
for
things
that
are
important
to
the
verifier
protocol
fields
are
used
for
things,
that's
important
just
to
the
tab,
that's
the
principle
that
we
try
to
use
throughout
now,
and
so
that
one
was
done
since
ietf
108,
but
wasn't
discussed
before
other
than
on
the
list.
B
So
next
slide
again,
unless
people
have
objections
or
questions,
I'm
going
to
keep
going
in
the
interest
of
time
all
right.
So
there
was
this
open
question
about
that.
Thiru
had
asked
about
clarifying
the
use
of
symmetric
keys
to
erase
it
the
changes
shown
on
the
screen,
don't
need
to
discuss
unless
somebody
wants
to
because
tyro
who
allow
the
issue
said.
It
looks
good
and
closed
the
issues
so
next
slide
unless
somebody
has
something
they
want
to
discuss.
A
B
Similarly,
we
had
a
solicitor
review
from
russ
housley
most
of
his
comments,
or
I
should
say
you
know,
maybe
half
of
a
little
bit
more
of
his
comments
were
addressed
prior
to
108.
Some
were
not,
and
so
this
is
the
leftover
ones.
The
remaining
comments
from
ross.
You
can
see
the
paragraphs
that
we
did.
The
chairs
verified
and
closed
the
issue,
so
we
believe
that
this
one
is
also
done,
but
you
can
see
the
text
there
in
case
somebody
wants
to
discuss
it.
I
think
we
can
just
go
on.
B
All
right,
this
one
was
another
one
that
was
another
list
post
from
last
month
and
the
issue
here
again
was
raised
since
ihf-108,
and
the
issue
was
as
follows:
the
term
ta
in
the
document
was
defined
as
an
app.
That
quote
runs
in
a
tee
where
runs
means
to
humans
that
there's
code
there
and
it's
not
just
a
piece
of
data.
Okay.
B
So
you
use
the
deep
protocol
to
install
the
code
and
separately
use
the
tek
protocol
to
install
you
know
the
data
configuration
blob
that
it
needs,
but
other
text
in
the
document
only
ever
talked
about
installing
quote
tas
right,
which
implied
that
it
could
not
be
used
to
install
things
that
are
just
the
data
blobs
and
so
hence
the
contradiction
that
was
purely
editorial
now
to
resolve
this.
There
was
already
a
sentence
in
the
document
that
used
lowercase
trusted
components
in
a
way
that
could
clearly
be
read
to
mean
either
a
ta
or
personalization
data.
B
So
the
resolution
was
we
just
capitalized
that
stuck
in
the
terminology
section
to
say
whenever
we
mean
either
code
or
you
know,
data,
only
we
just
use
trusted
components,
and
so
this
proposal
was
raised
on
the
list
a
month
ago.
There
was
no
objection
so
right
before
the
draft
deadline.
We
just
did
it
and
it's
same
in
the
other
specs
too.
B
Next,
I'm
keeping
an
eye
on
the
queue,
so
I
don't
see
anybody
so
just
keep
going
all
right.
So
last
week
we
had
the
hackathon
which
akira
is
going
to
talk
about
later,
but
one
of
the
issues
that
we
found
during
hackathon
was
this
one
that
affects
the
architecture
document.
Okay,
if
you
remember
at
ietf108,
we
had
this
discussion
about
a
way
to
tell
the
tam
that
you
don't
need
a
ta
anymore,
so
that
the
tam
can
then
choose
to
delete
it.
B
B
But
again
this
was
not
in
the
posted
document
yet
because
it
was
only
found
during
the
hackathon
last
week.
Okay,
but
there's
already,
you
can
see,
there's
a
per
request
there.
So
there's
already
proposed
text
which
is
on
the
screen,
and
so
the
belief
is,
unless
there's
objections,
that
we
would
merge
the
pr
right.
There's
no
text
to
be
written
in
case
unless
you
don't
like
the
text.
So
next
slide.
B
Unless
there's
questions,
we've
got
lots
of
issues
in
the
tea
protocol
to
discuss,
and
so
I
I'm
trying
to
go
through
the
things,
because
most
of
these
are
editorial.
Only
if
you
remember,
we
had
a
discussion
before
about
removing
text
that
talked
about
security
domains
out
of
the
architecture
document
right,
not
that
it's
disallowed,
because
you
might
be
able
to
use
a
suit
manifest
to
do
things
with
security
domains
but
removed
it
from
the
architecture
document.
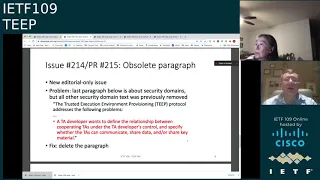
B
However,
when
we
remove
that
text,
the
following
paragraph,
that's
in
red
was
left
in
there
which
we
missed
because
it
doesn't
use
the
word
security
domain,
but
it's
talking
about
a
problem
that
security
domains
solve
and
it's
under
the
heading.
The
t
protocol
addresses
it.
Well,
that's
not
addressed
by
the
t
protocol,
it's
addressed
by
the
suit
manifest,
and
so
the
editorial
fix
is
delete.
B
C
B
All
right
trying
to
figure
out
if
you
have
an
objection
to
removing
it,
I
would
say
maybe
moving
this
paragraph
to
a
different
document
which
we
don't
have
a
document
that
talks
about
security
domains
in
the
suit
manifest
yet,
but
that's
where
it
would
go
in
my
opinion.
So
all
right,
your
still
list
is
being
shown
in
cube
brennan.
So
I
don't
know
if
I'm
gonna
keep
going.
I.
B
We
could
choose
to
do
nothing,
okay,
and
so
the
observation
is
that
the
t
protocol
won't
be
used
for
everything.
Okay,
three
reasons
for
that
number,
one
for
sim
chips
which
have
you
know,
a
a
t-e-e
and
an
e-uicc
sim
chip
is
already
in
wide
used
by
mobile
operators
and
they're,
not
using
the
t
protocol
they're
using
the
gsma
protocol.
And
if
you
look
at
their
architecture
document,
it
has
diagrams
look
just
like
petite
ones,
just
with
different
labels.
B
Number
two
global
platform
already
standardized
otrp,
which
we
didn't
they
are
now
under
the
second
version
of
it,
meaning
the
second
you
know
1.1
instead
of
v,
1.0
and
so
for
secure
elements.
Gold
platforms
are
using
otrp
third
point.
If
we
go
back
a
couple
like
at
least
two
years
ago,
david
wheeler
gave
a
presentation
about
you
know
in
when
we
were
doing
otrp
about
why
a
bunch
of
stuff
doesn't
make
sense
for
sgx,
because
there's
no
such
thing
as
enumerating
tas
in
sgx.
B
There
was
a
presentation
I
gave
on
behalf
of
mike
purcell
about
the
anarchs
project
about
a
year
ago,
when
we
were
talking
about
which
direction
the
transport
protocol
does,
and
so
we
said,
the
heat
protocol
is
actually
a
use
for
that
one,
but
transports
in
the
direction
so
last
slide
going
to
the
next
one,
which
is
just
showing
some
proposed
text
in
the
per
request.
Should
we
choose
to
do
something?
B
This
is
what
we
might
say
if
we
were
to
say
something,
and
so
in
the
introduction
section
you
know
it's
applicable
to
tees
that
can
install
and
enumerate
tees
in
a
tee
secured
location
where
another
domain
specific
protocol
standard
that
meets
the
needs
is
not
already
unused.
That's
an
example
of
something
we
might
say:
okay,
the
sgx
section
and
the
trustzone
section.
B
We
have
sections
on
both
of
those
which
kind
of
imply
when
you
read
them
that
protocol
is
applicable,
and
so
all
that
text
there
is
fine,
but
we
might
augment
it
with
a
paragraph
like
these.
That
say,
in
which
cases
it
might
actually
be
applicable
to
sgx,
and
this
is
using
the
nrx
model
without
ever
using
the
word
anarchs
here
and
similarly
for
trust
zone
where
there's
multiple
ta
stores,
such
as
an
opti
than
anything
where
you
can
install
stuff
in
a
trusted
location,
it's
applicable.
For
so
that's
an
example
of
what
we
might
say.
B
D
So
what
I
was
trying
to
ask
is,
you
said,
applicability.
I
think.
That's
that's
a
good
point.
So
I've
I've
been
a
little
bit
absent
last
time
in
the
wg
meetings,
and
now
I'm
wondering
what's
the
key
difference
between
gsms
and
gp's
cheap
flavors.
That
already
are
there
what's
what's
this
solution,
bringing
to
the
table
is
that
a
applicability
content
that
should
also
be
highlighted
somewhere.
B
My
I've
looked
at
the
gsma
spec.
I've
looked
at
the
otrp
spec.
My
belief
is
that
they
are
roughly
accomplishing
the
same
goals,
but
gsma
and
otrp
respectively,
are
for
very
domain
specific
purposes
like
otrp.
Has
lots
of
security
main
stuff
built
in
and
gsma
stuff
has
stuff?
That's
very
specific
to
you
know
mobile
operators
and
sims
and
stuff,
but
at
a
high
level
they
do
the
same
thing,
and
so
my
belief
is
gsma
already
has
a
deployed
protocol,
there's
no
incentive
for
them
to
switch
at
least
right
now.
B
D
B
B
D
E
Thanks
harness,
isn't
you
yeah
yeah?
I
just
wanted
to
add
this
is
honest
here
like
there's,
obviously
a
a
long
history
with
otrb
and
why
we
have
chosen
to
design
deep
in
the
way
it
is
currently
designed,
and
I
don't
think
that
history
needs
to
go
into
the
document,
because
it's
obviously
like
the
dirty
laundry
of
standards,
work
between
different
organizations
and
how
things
can
go
sideways
in
some
sense
yeah.
E
One
of
the
reasons
why
otrb
and
deep
now
look
different
this,
and
I
think
this
is
quite
important-
is
that
we
made
use
of
eat
and
and
the
rats
work,
as
well
as
the
suit
work,
which
I
believe
and
that's
what.
If
you
look
at
the
the
content
of
the
otrb
protocol,
that's
what
most
of
it
talks
about,
and
so
we
we
managed
to
sort
of
generalize
this
and
put
it
into
separate
buckets.
And
I
think
that
solution
is
like
technically
much
better.
E
B
B
B
We
just
copied
a
sentence
from
an
existing
rfc
that
doesn't
reference
2018,
so
we
match
kind
of
what's
already
gone
through
iesg.
There
was
a
discussion
at
108
around
headers,
so
we
removed
cash
control,
as
hannah
said
proposed,
and
there
was
one
fix
that
when
I
followed
up
with
mark
nottingham,
he
said
unsupported.
Media
type
should
be
415,
not
406..
So
we
corrected
that
in
the
text
next
slide.
B
I
only
got
one
more
slide,
so
please
go
to
slide
four
okay.
There
we
go
only
one
new
issue
was
raised,
which
is
that
issue
that
we've
already
discussed
in
the
architecture
document,
and
so
we
made
similar
changes
here
and
there's
the
open
pull
request
on
the
unneeded
ta.
That
would
affect
this
stock
too
again.
Similarly,
if
we
accept
it
on
the
architecture,
we
accept
it
here.
So
that's
it.
Nothing
new
to
discuss
here
that
we
didn't
discuss
during
architecture
or
already
at
108,
so
done
cool.
A
A
E
F
F
G
F
E
A
B
B
B
Okay,
all
right
so
there's
a
number
of
issues,
there's
three
collectively
that
I'll
talk
about
here
that
are
introduced
on
the
curious
slides
and
so
today,
every
teat
message
has
a
token.
The
token
is
an
unsigned
integer
that
the
tam
sends
that
agent
echoes
back
in
the
response,
so
this
does
require
the
tam
to
create
state
to
store
the
token,
even
for
a
query
request
now,
a
courier
quest
other
than
the
token
is
identical
to
when
it's
sent
to
every
client.
B
The
only
thing
that
differs
in
query
requests
is
the
token
field.
Okay.
So
that
means
that
you
have
to
keep
state
and
there's
no
other
reason
in
the
query
request
to
keep
state
the
query
response
at
least
allows
you
to
or
requires
you
to,
depending
on
who
you
implement.
It
includes
the
attestation
evidence
the
attestation
evidence
already
has
a
separate
challenge
field.
That's
in
the
query
request.
That's
echoed
back
in
the
attestation
evidence!
Okay,
so
if
you
think
about
well,
how
do
I
do
replay
protection?
B
I
need
tokens
for
that
to
ensure
you
know,
freshness
and
so
on.
Well,
you've
already
got
the
challenge
field
for
that.
There's
multiple
layers
of
stuff
going
on
right,
there's
the
tls
layer
which
might
terminate
outside
the
tees.
You
can't
trust
that
there's
the
cose
header
there's
fields
in
the
teep
message
like
token
and
then
there's
things
inside
the
evidence,
and
so
since
replay
protection
with
evidence
is
already
done
by
the
challenge.
B
As
long
as
you
already
have
as
long
as
you're
using
the
challenge
and
the
eat
or
evidence,
then
you
don't
need
the
nonce
for
purposes
of
matching
or
replay
protection,
because
you
can
already
get
that
out
of
the
challenge.
Okay.
So
if
you
do
do
a
token,
then
this
introduces
this
complex
question
I
ran
into
with
the
implementation
says.
So
when
do
you
clean
up
state
right?
So
let's
say
you
send
the
query
request
and
you
never
get
a
query
response
right.
B
You
actually
have
to
clean
up
state
according
to
some
implementation,
to
find
things
so
there's
some
complexity
to
deal
with
that.
Okay,
but
does
it
actually
buy
you
anything
in
the
query
requesting
response?
So
the
first
question
is:
could
we
just
get
rid
of
the
token
and
the
query
request
and
the
query
response?
B
This
in
the
latest
drafts
that
we
have
the
success
and
error
message
can
include
suit
reports.
The
suit
reports
have
the
results
of
the
install
and
the
delete
okay
and
so
in
a
suit
report,
and
this
is
echoing
stuff
out
of
brendan's
suit
report
draft
there's
a
manifest
digest
that
one
is
what
identifies
which
suit
manifest
was
being
installed
or
uninstalled.
That
might
have
the
success
of
errors
and
the
suit
record
has
you
know
a
a
an
array
of
zero,
more
suit
records
that
have
you
know
success
or
failure,
results
or
status
points
or
whatever?
B
So
my
claim
is,
I
don't
know
that
you
actually
need
a
token
for
matching
purposes
in
the
installer
delete
either,
because
we
have
the
suit
manifest
digest
and
things.
So
you
can
ask
well
what
about
replay
protection?
Well,
how
do
you
know
that
the
suit
reports
that
you're
getting
aren't
replayed
by
you
know
the
re
or
something
from
things
that
were
suit
reports
from
you
know,
last
week
five
months
ago,
or
something
like
that?
How
do
you
know
the
student
reports
are
fresh?
Okay
and
so
again,
maybe
you
saw
that
at
the
cose
layer.
B
Maybe
you
saw
it
in
the
suit
report
itself,
but
I
don't
know
that
you
need
to
solve
it
in
the
teep
message,
and
so
the
proposal
too
is:
could
we
use
either
the
cose
header
or
the
suit
reports
and
not
use
the
token
and
installer
delete
either?
And
so
let
me
open
it
up
here
because
I
see
conus
is
already
in
queue.
E
So
the
the
token
which
is
announced
that
it's
initially
sent
by
the
dam
and
then
relate
back
in
the
response
you
said
like
you-
could
also
use
the
nuns
for
that
purpose.
But
it's
not
it's
not
necessarily
the
case
that
the
nonce
is
always
used.
When
this
the
ban
doesn't
need
attestation
information,
then
it
wouldn't
use
the
nons.
E
B
So
I
think
two
things
we
talked
about
during
the
hackathon
one
is:
is
there
any
such
case
where
you
would
not
want
to
include
the
evidence
and
number
two?
If
there
is,
could
you
just
have
the
token
be
optional
and
only
used
in
such
a
case
and
number
three?
Are
you
actually
buying
anything
given
that
the
suit
that
they,
sorry,
that
the
query
requests
are
identical?
B
E
Yeah,
so
for
me,
like
the
reason
why
there
was
the
need
to
associate
the
response
to
request,
was
we
said
in
the
architecture
document
that
we
may
have
actually
multiple
des
on
a
single
device,
and
this
is
request.
It
needs
to
know
how
to
match
one
request
to
the
other.
I
think
that's
where
it
came
from
initially.
C
So
that
when
I
wrote
this,
I
had
assumed
that
there
was
going
to
be
a
replay
protection
layer
underneath
the
suit
report.
But
I
don't
see
a
problem
with
including
it
and
I
think
pretty
much
anywhere
that
it's
used.
Replay
protection
is
probably
going
to
be
a
question,
so
it
probably
needs
some
kind
of
counter
in
there,
but
I
suspect
it
needs
to
be
very
loosely
defined
because
the
the
content
of
whatever
token,
if
you
will
the
suit
report
contains,
is
probably
highly
application.
Dependent.
B
C
D
So
hi
this
is
hank,
so
I
I
heard
the
term
evidence
so
then
I
my
attention
was
packed,
of
course,
so
my
assumption
is
that
the
request
does
not
include
a
heat,
but
the
reply
will
substitute
the
nuns
for
the
eat
or
I
expected
the
time
to
issue
a
eat
on
the
on
the
request.
Also,
I
I
didn't
see
the
request.
B
The
request
can
include
a
challenge
which
you
can
interpret
as
being
nonce,
but
it
could
be
something
more
than
a
knowledge
just
depends
on
what
the
what
the
mechanism
is.
So
when
I
say
challenge
you
can
re,
you
can
hear
that
as
saying.
Oh,
he
said
nahs
right,
so
the
request
has
a
challenge.
The
response
includes
the
evidence
as
long
as
the
tam
requested
it,
and
so
the
challenge
is
used
in
computing,
the
evidence
so
and
the
evidence
is
it
by
default
and
eat.
Yes,.
D
D
I
think
it's
a
good
idea
and
the-
and
I
just
want
to
have
a
small
comment
here-
clarifying
comment
on
the
reports,
so
the
suit
report
was
created
with
evidence
and
attestation
results
in
mind,
so
it's
ease
of
computability,
so
it's
relatively
high,
highly
refined
evidence
claims
here
that
could
be
used,
probably
even
in
metrics
for
attestation
results.
It's
relatively
easy
without
a
complicated
policy.
B
Okay,
so
I
think
so
far
what
I'm
hearing
just
to
summarize,
the
last
three
speakers
put
together,
is
just
that
there
might
still
be
a
case
for
a
token,
but
maybe
it's
not
required.
Maybe
it's
optional
and
I
think
akira
has
in
his
deck
a
slide
that
shows
the
different
uints
and
things
that
was
one
of
the
proposals
and
so
I'll.
Let
akira
cover
that
option
in
his
slides
and
but
otherwise.
I
think
we
actually
depend
on
the
resolution
to
the
suit
discussion
to
resolve
this
one
for
sure.
E
B
C
Yeah,
so
there
was
a
comment
that
you
made
about
the
about
using
it
for
attestation
hank.
Specifically,
you
made
that
comment.
I
I
did
look
through
that
and
I
discussed
that
with
with
dave,
and
I
think
the
conclusion
that
we
came
to
was
that
using
it
for
attestation
might
be
possible,
but
that
it's
probably
more
complex
than
is
necessarily
useful
for
attestation
purposes.
As
a
general
case.
G
A
B
13.,
okay,
thank
you
just
cut
me
off
because
I
I
I
believe
that
we
have
more
slides
and
we'll
get
through
so
we'll
get
through
as
many
as
we
can
and
then
we'll
stop.
So
all
right.
So
this
one
again
there's
two
issues
that
have
to
do
with
cipher
suites,
okay.
So
what
the
draft
does
right
now
is
it
defines
two
cipher
suite
values.
You
can
see
there
kind
of
defines
like
an
iona
registry
and
there's
two
values
out
of
there
defined
right
now
and
the
messages
you
can
see.
B
The
supported,
cypher
suites
is
an
array
of
sweet
values,
and
so
that's
what
the
tam
sends
and
then
the
agent
sends
back
a
selected
one
which
is
a
single
one
and
then
the
combined
cdl.
You
see
this
cypher
sweets
as
bitmaps.
Okay,
well,
you've
got
this
array
of
sweet
values
that
looks
like
a
typo.
So
that's
what
72
is
is
why
does
that
say
as
bitmaps?
We
think
that
you
just
say:
cipher
sweets
and
bleep.
Those
two
words.
So
that's
issue
72
73,
which
I
think
is
just
trivial
editorial.
B
So
73,
on
the
other
hand,
is
you've,
got
two
different
values
defined
right.
If
your
tam
only
supports
value
one,
your
agent
only
supports
value
two
or
vice
versa.
You
don't
have
interoperability,
so
the
question
is
what
cipher,
suite
or
suites
are
mandatory
to
implement
on
each
end?
That's
what
73
is.
I
don't
know
what
the
recommendation
is
there,
but
I
would
defer
to
any
crypto
people
here
if
they
have
a
recommendation,
sure
what
should
be
mandatory
to
implement.
B
F
So,
jumping
in
this
is
ben
k
duck.
We
tend
to
prefer
the
x25509
and
dsa
of
de
novo
deployments,
where
you
don't
have
any
legacy
considerations
to
to
work
with,
but
we
tend
to
have
to
fall
back
to
p256
and
es256
for
cases
where
you
have
like
a
tpm
or
a
smart
card
that
can
only
do
the
older
algorithms.
B
F
B
B
Right
so
you
can,
I
mean,
there's
multiple
ways
to
get
interoperability
right.
You
can
either
pick
one
and
say
both
ends
have
to
do
that
one
and
could
choose
to
negotiate
something
else
or
you
can
say
that
one
end
has
to
do
all
of
the
set
and
the
other
end
can
choose
which
one
it
wants,
and
so,
if
you
think
about
tp
agents
that
are
in
constrained
devices,
then
maybe
mandating
too
or
you
want
the
one
that's
best
for
a
small
iot
device
or
something
like
that.
B
A
A
H
B
B
Yeah,
okay,
so
here
there
is
this
thread
that
was
joint
rats
and
teeth
with
the
title.
Each
claims
needed
by
t
right.
This
one
is
still
open.
Where
the
architecture
document
says,
here's
some
things
you
have
to
be
able
to
express
in
claims
somehow
and
doesn't
say
how
that
leaves
it
to.
You
know
something:
it's
a
normative
spec.
B
Already
there
and
lauren
said,
respondents
saying
yep:
we
need
a
new
claim,
yep
we
need
to
claim
and
in
rats
yesterday
or
whatever
lawrence
mentioned,
that
they're
still
working
on,
they
have
pull
requests
and
stuff
in
progress,
and
so
because
of
that,
my
summary
is
that
we
that
the
proposal-
at
least
I
think
from
lawrence
and
myself-
is
that
we
should
not
define
yet
and
let
tell
proven
otherwise
any
type.
Specific
claims
right.
B
Lawrence's
belief-
and
I
agree-
is
that
everything
in
this
list
is
things
that
would
be
applicable
outside
of
teep
and
so
would
go
into
the
eat
spec
or
something
in
the
rats
working
group,
and
we
can
just
refer
to
it,
and
so
some
of
them
are
there.
Now
some
of
them
are
not,
but
and
in
rats
lawrence
mentioned
that
for
firmware
and
software
identifiers
right.
B
He
says
the
intent
for
software
claims
to
use
coswood,
and
this
is
on
a
slide
in
the
rats,
you're
working
group
and
but
there's
nothing
in
the
eat
document
about
coswoods,
yet
okay,
so
I
think
I'll
mention
that
in
the
next
slide
or
two
slides,
if
I
get
to
it,
so
we'll
come
back
to
that.
But
here
I
think
there's
nothing
for
us
to
do
yet
right
now,
I'm
just
reporting
out
that's
what
I
saw
on
the
thread
so
next
slide.
A
B
A
glue
on
your
okay,
so
yeah
coming
now
drilling
down
to
this
causewood
stuff.
Okay,
so
what
we
need
in
teep
is
we
need
a
version
independent
id
and
by
version
independent,
I
mean
you
know
as
you
rev
your
suit
manifest
with
you
know,
patches
and
so
on.
You
increase
your
manifest
sequence,
number
you're,
going
to
increase
your
component
id
sequence
and
your
version
number,
and
so
on,
but
version
independent
identifier
that
we
can
use
in
messages
and
abstract
apis,
like
request
ta.
B
B
The
coswood
spec
has
this
tag
id
that
says
it's
a
16
byte,
uniquely
identif,
uniquely
referencing,
a
software
component,
so
to
my
unknowledgeable
eyes
that
tag
id
looks
like
it
would
meet
the
requirement,
but
it's
optional
in
suit,
and
so
one
thing
we
could
do
is
to
say
suit.
Manifest
carried
in
teep,
for
this
purposes
need
to
use
the
coswood.
But
this
is
the
other
one
that
I
needed
brendan
here
and
so
brendan.
Please
correct
what
I'm
what
any
misunderstandings
I
have.
B
If
you
have
something
that's
great,
I
think
when
I
had
asked
about
a
component
identifier
in
some
message-
maybe
you
I
don't
remember
which
message
it
was.
I
didn't
see
anything
in
the
suit
manifest
document
right
now
that
was
directly
usable
other
than
causewiz.
So
please
correct
me:
if
there
is
something
that's
version,
independent
id,
so.
C
What
you
have
in
in
suit
for
purposes
like
this
is
the
component
identifier
and
the
way
that
it
works
is
it's
an
array
of
byte
strings
so
that
you
can
represent
a
notional
path.
So
when
we
talked
about
trusted
domains
previously,
the
idea
was
that
we
were
going
to
have
a
te
identifier,
followed
by
a
trusted
domain.
Identifier,
followed
by
a
vendor
identifier,
or
maybe
I've
got
those
two
in
the
wrong
order,
not
important
and
then
followed
by
some
kind
of
ta
identifier.
C
B
E
B
B
That
can
depend
on
other
suit
manifests
the
things
it
depends
on
might
be
even
having
to
come
from
a
different
tam
right,
there's
a
case
that
we
talked
about
in
the
context
of
the
architecture
document
where
you
have
personalization
data
that
might
need
to
come
from
a
different
tam
than
the
ta
binary.
That's
one
of
the
use
cases
we
talked
about.
You
know
last
year
sometime,
and
so
let's
assume
that
you
have
a
dependency
from
suit,
manifest
a
on
to
suit
manifest
b.
B
B
You
know
a
depends
on
b,
so
there's
at
least
four
options
here,
and
maybe
different
people
have
different
preferences
here
and
it's
also
possible
they're
gonna
be
multiple,
correct
answers
and
so
option
number
one
is
to
say
well,
the
tam
has
to
resolve
all
the
dependencies
and
then
pushes
down
the
blob
of
all
the
suit
manifest
down
to
the
agent
in
one
install
message.
Well,
that's
problematic.
B
B
Well,
you
could
just
not
respond
to
the
first
install
message
until
all
the
dependencies
are
resolved
and
suit
processing
completes,
but
maybe
that'll
take
a
bunch
of
time.
So
what
does
the
tame
do
in
the
meantime
and
option?
Number
four:
is
the
agent
resolves
those
dependencies
but
sends
back
some
progress?
Notification
of
the
tab?
Maybe
there's
other
options,
but
those
the
four-
and
I
think
I
am
out
of
time
now,
and
so
my.
B
G
A
A
G
G
Initially
my
plan
was:
there
was
many
update
for
the
xero4
draft
in
the
deep
protocol,
so
up
catch
up
with
the
latest
draft
with
on
monday
and
tuesday
and
then
announcing
about
wednesday
when
we
all
get
together
with
do
the
connecting
individual
time
and
time
server,
tama
time
server
and
deep
device.
But
what
really
happened
was
we
were
busy
in
internal
updating
in
implementation
of
deep
device
to
adopt
the
therefore
draft
until
thursday,
night
or
something?
G
So,
what
really
happened
was
having
a
discussion
meeting
on
friday
and
that's
the
photo
during
the
hackathon
agenda
in
this
slide.
So
that's
the
reality,
but
we
got
many
things
raised.
I
mean
not
raised
but
to
find
improve
the
draft.
So
yeah
that's
wait
and
that's
the
from
the
next
slide.
Next,
please.
G
G
Please-
and
these
are
the
details,
but
most
of
the
details
listed
here
is
overlap.
What
about
what
dave
have
presented
before
and
it's
related
with
the
most
of
it
is
token
and
and
another
another
two
topics
of
how
to
consider
a
consideration
of
the
token
and
the
second
is
the
detail,
t
protocol
message,
compatibility
and
detail
compatibility
is
we
could
something
we
could
improve
with
with
a
github
issue
and
pull
requests
and
merging
it.
G
We
need
some
kind
of
id
and
so
right
now
the
ta
name
change
the
tc,
so
tc
unique
id,
and
if
we
not
explicitly
written
in
this
draft,
we
might
end
up
somebody
in
the
implement
implementer
using
token
in
for
the
tc
id
unique
id,
which
is
not
a
good
practice.
So
I
think
we
we
we
have,
we
we
did
have.
We
were
discussing
what
what
is
the
unique
id
really
going
to
be
used
and
and
on
the
fridays
dcid?
G
So
and
another
discussion
was
right:
now
we
were
all
busy
just
supporting
seaboard
and
the
keep
seaboard
present
a
representation
for
the
binary
was
keep
the
updating
where
we
were
just
following
the
update.
Was
it
end
up
our
work,
but
in
the
next
next
step
will
be
supporting
coset
and
then
we
really
need
which
cypher
suit
should
we
need
to
implement
for
the
at
least
for
the
hackathon,
or
interpret
the
test
between
the
time
server
and
deep
device?
And
that's
something
I
saw
the
discussion
in
the
dave's
slot.
G
Yes,
yeah:
these
are
almost
related
to
the
token
or
tip
tip
message,
details
of
the
binary
format
or
not
notation
representation,
and
one
thing
improvement
is
we
have
we
didn't
have
a
time,
but
we
we
now
have
the
unneeded
ta
list.
So
we
could
use
that
for
the
removing
the
ins,
the
binary
inside
the
chip
device.
C
G
G
B
Yeah
dave's
in
the
queue
so
accurate.
There
was
one
thing
and
I
don't
remember
which
issue.
If
you
can
point
people
to
it,
it
was
the
one
where
we
had
the
discussion
about
the
the
integer
field
at
the
end
and
being
able
to
combine
stuff
into
the
star
ant
and
stuff
which
which
issue
number
was
that
remember.
