►
From YouTube: IETF110-RATS-20210310-1430
Description
RATS meeting session at IETF110
2021/03/10 1430
https://datatracker.ietf.org/meeting/110/proceedings/
D
D
D
Topic
lawrence
is
also
on
tap
for
that
one
and
then
third
is
a
discussion
about
how
coswood
and
eat
go
together,
and
so
we
have.
We
have
plenty
of
time
allocated
for
that,
so
it
really.
If
there's
if,
if
there's
time,
I
think
we
will
try
and
the
trails
will
will
do
an
update,
a
brief
update
on
the
milestones
progress,
any
other
topics
we
need
to
consider.
D
D
B
E
Please
so
this
is
the
same
slide
from
last
time,
just
a
list
of
the
things
that
that
I'm,
I
think,
should
be
in
eat
the
the
the
set
of
claims
that
we
should
be
having
you
eat
that
that's
kind
of
the
in
the
eat
draft.
That's
the
ones
we
want
to
standardize
for
the
the
e
draft
can
be
lots
of
claims
after
this
you
know
in
the
registry,
but
this
is
the
the
plan.
What
I'm
planning
for
to
complete
the
draft
next
slide.
E
E
In
some
detail,
then
there
was
a
bit
of
a
few
little
modifications
to
sub
modules
and
nested
eats,
and
I
think
those
are
in
pretty
good
shape.
I
have
an
implementation
of
of
of
that
and
I
think
thomas
was
working
on
an
implementation
of
that.
Then.
Last
time
we
talked
about
public
keys
and
that
was
that's
been
added
to
the
draft.
E
So
the
the
big
areas
where
we
have
work
to
be
there's
where
there's
work
to
be
done
is
coast,
wood
measurements
and
then
the
identifying
the
verifier
input,
which
is
endorsements
and
key
ids.
So
we
talked
about
go
to
next
slide,
oh
yeah,
and
then
there's
other
than
work
on
specific
claims.
I
need.
I
still
need
to
do
a
substantial
rework
in
relation
to
the
rats
architecture,
so
it
uses
the
terminology.
E
E
So,
just
just
a
short
change:
a
list
of
changes
the
ue
ids
are
now
based
on
the
imei
based
ueids
are
now
14
byte
strings
the
sub
modules.
Now
a
cwt
sub
module
is
allowed
in
a
jwt
and
vice
versa
and
the
the
how
seaboard
tags
are
to
be
used
in
a
like
when
you
put
a
cwt
module
inside
a
cwt
module
how
the
tagging
works
added
that
we
added
the
cryptographic
keys
in
claims
added.
The
hardware
version
claims
some
some
tweaks
for
debug
status.
E
E
So
the
a
lot
of
the
work
to
be
done
is,
as
I
said,
on
swids
coast,
widths
and
measurements
and
we'll
get
into
that
later,
and
then
there's
also
a
fair
bit
of
work
to
be
done
on
endorsements
and
key
ids,
and
most
of
that
is
going
to
be
just
frame
up.
I
have
a
pull
request
on
that.
I
don't
intend
to
actually
define
an
endorsement
format
next
slide.
E
E
E
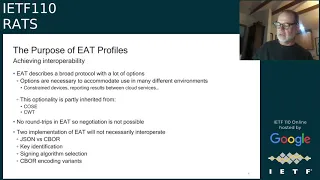
So
this
is
to
me
this
is
about
actually
getting
to
interoperating
implementations
of
eat,
so
the
eat
protocol,
or
he
describes
it's
got
a
lot
of
options.
I
mean
you
know,
and
these
it
has
all
these
options
to
work
in
lots
of
different
environments
and
lots
of
different
use
cases.
Some
of
them
have
to
do
with.
You
know
whether
it's
constrained
device.
E
Are
you
using
this
on
a
constrained
device
or
are
using
this
to
report
results
between
cloud
services,
for
example,
for
the
two
extremes,
something
and
two
things
that
are
very
different,
so
constraining
device?
You
want
very
few
claims,
very
small
representation,
moving
data
between
cloud
services.
You
probably
are
happy
with
that
json
and
you
might
have
lots
and
lots
of
claims.
E
Some
of
this
optionality
is
inherited
from
cos
a
and
from
cwt.
You
know,
for
example,
kosei
supports
lots
of
algorithms
and
you
need
to
narrow
down
to
pick.
You
know
one
or
two
algorithms
or
a
set
of
algorithms.
Somehow
so
you
actually
have
interoperability
in
cwt
claims
are
all
the
claims
are
optional.
E
E
E
E
E
E
E
That
that
that
claim
is
not
required.
It's
just
to
help
a
helpful
hint
for
parties
to
know
which
profile
is
in
use
and
the
format
of
the
name
document
is
text.
It's
not
standardized
for
machine
processing,
so
the
profile
addresses
four
major
things:
serialization
format
protection
I
like
whether
the
the
the
eat
is
signed
or
encrypted
or
signed
and
encrypted
or
not
protected.
It
addresses
key
identification
and
it
addresses
what
what
claims
are
required
and
prohibited.
E
E
So
the
serialization,
so
it
says
whether
you
could
use
sibor
or
json
or
both
and
how
the
nesting
can
work
like
if
you're
you
know,
your
main
format
is
seaborg.
Is
it
okay
to
nest
a
jwt
adjacent
token
in
in
the
seaboard?
Vice
versa
for
seabor,
it
narrows
whether
you're
using
a
definite
and
indefinite
length
for
maps
and
arrays
and
strings,
and
it
says
how
to
use
seymour
tags.
E
E
E
E
E
E
And
add
them
add
them
to
the
registry
or
not,
and
a
profile
may
allow
optional
claims
and
in
that
case
verification
wouldn't
fail
if
they're
present,
I
also
should
have
added
here
a
profile
can
narrow
a
claim.
So
you
know
you
might
say
or
refine
a
claim.
So,
for
example,
in
the
location
claim,
some
things
like
accuracy
are
optional,
so
a
profile
could
say
that
they
are
not
optional.
E
F
Yeah,
I
just
want
to
say
that
that's
a
great
list.
I
think
that
the
keep
working
group
was
the
first.
You
know
customer
of
rats
and
so
the
t
protocol
spec
itself
is
kind
of
the
first
candidate
profile.
As
I
understand
it,
and
so
this
is
a
great
list
of
requirements
that
the
cheap
protocol
spec
should
cover,
of
which
it
covers
some.
But
not
all
of
these.
That's
why
I
thought
this
was
a
great
list.
F
I
guess
there's
a
medic
question
is:
do
you
think
that
a
profile
that
would
that,
as
you
start
to
have
other
other
using
protocols
and
things,
do
you
think
that
a
protocol
would
typically
itself
specify
what
profile
it
is
or
do
you
envision
there
be
that
profiles
be
something
that
that
protocols
would
negotiate
to
say
which
profile?
Is
it
I'm
asking?
What
you
think
is
the
more
typical
use
case?
F
E
G
Hey
it's
gary
here.
Sorry,
I
missed
c
it
it
couldn't.
Do
the
raise
hand
raise
hand
feature
so
dave,
I
I
can
say
at
least
in
our
internal
production,
we're
running
into
situations
where
it
has
to
be
essentially
some
sort
of
declarative
measure.
It
can't
be
negotiable,
and
so
that's
particularly
the
case
where,
indeed,
is
being
used
in
the
context
of
a
device
that
lacks
ip
connectivity.
G
So
you
can
think
of
maybe
a
device,
that's
listening
on
the
bluetooth
low
energy
advertising
channel,
but
it
is
requested
to
send
back
up
a
up
and
at
a
station
through
a
hit
through
a
unicast
connection.
So
in
that
case
we
just
don't
negotiate.
We
need
to
get
that
out
of
station
up
right
away.
It's
assumed
that
they
will
that
the
relying
party
would
be
able
to
process
whatever
whatever
profile
would
be
declared
inside
of
the
inside.
F
C
F
E
H
H
E
H
B
E
H
So
I'm
bringing
up
this
question
because
this
reminds
me
of
that
I
think
that's.
A
subset
of
your
problem
statement
is
that
we
have
this
very
versatile
cozy
envelope
and
and
you,
if
you
mandate
that
is
implemented,
you
have
to
implement
that
jana
algorithm
list
and
that's
probably
not
always
going
to
happen.
So
what
we're
doing
right
now
for
cozy
is
actually
to
rewrite
the
whole
cozy
spec
and
just
cherry
pick,
what
we
want
from
that.
So
like
there's,
always
of
course,
the
the
central
envelope.
H
There
is
the
tag,
for
example,
messages
or
keys,
or
something
in
cozy,
and
then
the
cherry
pick
the
unprotected
and
protected
stuff
and
and
put
them
in
to
our
like
and
rewrite
the
old
cdl
and-
and
if
I
look
at
this
like
from
your
point
of
view
now
I
would
say
that's
a
profile
for
cosy
use
edge.
You
could
restrict
the
number
of
the
the
the
accepted
values
for
algorithm
ids.
You
could
say
I
only
want
these
two
optional
and
that
were
mandatory
and
nothing
else
and
such
so.
H
E
Yeah,
I
suppose
you
could
do
it
that
way.
I
I
was
not
the
way
I
and
I
think
I've
seen
that
in
the
coastwood
draft.
I
thought
I
thought
that
was
a
little.
I
mean
that
wasn't
my
origin
initial
thought
to
do
it.
My
initial
thought
was
just
to
say:
you
know
he
used
text
to
describe
how
you
want
cos
a
to
be
used,
and
I
mean
my
thought
also
is
you
know.
Kose
should
be
for
a
lot
of
these
things.
H
Maybe
there's
some
middle
grounds
here.
Sorry,
sorry
so
step
in
here
just
for
a
second,
so
I
I
think
writing
something
in
english
text
when
you
can
have
a
formal
language
is
not
a
good
idea
anymore,
because
then
imposition
kicks
in
and
interoperability
lacks
and
suffers
at
some
point,
maybe
and
and
if
you're
very
precise,
and
what
you
expect
to
be
in
the
message.
E
C
You
know
just
just
to
think
of
what's
what
hank
was
saying.
I
think
we
could
so
your
list
of
requirements
is
so
precise
that
we
could
come
up
with.
You
know,
for
example,
a
a
draft
template
in
markdown
or
in
xml
rfc,
with
with
all
the
sections
pre-populated,
and
you
just
fill
in
the
blanks
and
stuff
like
that.
C
That
might
be
an
option
to
semi-automate
the
thing,
because
if
you're
talking
to
ctdl
hank,
then
you
know
constraining
a
type
is
not
that
easy?
I
mean
it's
not
like
json
schema
where
you
can
override
the
type
and
apply
more
constraint
on
that,
and
then
ctm
doesn't
seem
to
be
prone
to
that
manipulation.
H
Yeah:
okay!
Well:
how?
If
you
write
it
in
english
text,
you
would
end
up
with
the
same
content
as
you
would
do
in
a
complete
rewrite
right,
because
everything
you
touch
and
you
have
to
mention
the
you
have
to
write
and-
and
I
think
that
that
in
the
content
of
the
english
text,
you
would
find
the
exact
same
thing.
When
would
you
write
it
in
the
cdn
that.
C
H
I
I
I
would
like
to
disagree
with
hank
here,
because,
having
looked
at
this
from
a
deep
point
of
view,
as
we
discussed
in
the
earlier
session
today
like
it's,
these
simple
things
of
saying
something
like
we
don't
use
encrypt
zero,
but
only
encrypt
and
use
encrypt,
I
don't
think
it
needs
any
cddl
to
do
that.
I
think
we
are
sort
of
doing
overkill
here.
I
It's
just
like
I
had
to
realize
working
on
the
course
you
spec
and-
and
the
same
applies
to
what
lauren
said
to
other
specs
as
well-
is
that
some
were
not
meant
to
be
limited
in
any
in
any
shape
or
form.
They
just
specified
everything
that
came
to
the
to
the
mind
of
the
author
or
the
working
group
at
that
time,
and
so,
instead
of
listing
these
20
options,
you
say
like
for
that
profile.
You
just
use
one.
H
So
sorry
to
kick
in
here
again,
but
but
yes
exactly,
you
say
that
you
say
your
start
message
is
just
one
type
and
you
write
cozy
and
then
you
go
from
there
cozy
zero,
for
example,
and
you
go
from
there
I
think,
even
in
cdl
it
is
like
25
number
of
characters
than
in
english
text,
because
you
have
to
write
and
in
your
message
you
must
and
then
you
can
also
write
in
cdda
start
messages
equals
cozy
zero
and
you
have
your
rule,
that's
done
so
I
I
I
still.
I.
B
B
I
I
think
what
lawrence
is
saying
that
hey
we
have
too
many
options.
We
somehow
need
to
sort
of
produces
and
if
you
write
the
profile
and
use
cdl
to
describe
what
you
want
an
implementer
to
do,
then
that's
fine,
maybe
for
you
and
and
maybe
not
for
someone
else.
I
don't
think
we
should
mandate.
It
has
to
be
done
in
cddl
like
or.
H
I
H
Now
that
that
might
be
the
fact
that
the
cosi
has
this
extraction,
script
implied
that
provides
you
with
the
complete
full
cdl
vba
diverge
from
that
since
cosy
I.
I
was
not
a
big
fan
of
that.
We
always
have
a
redundant
block
of
the
full
cdta
for
implementers
and
and
then
the
the
fragments
broken
out
as
is
done.
It's
cozy
reassembling
them
is
a
little
bit
tricky
and
annoying.
H
H
E
E
E
E
And
I've
started
looking
at
coast,
woods
and
sweds
and-
and
I
haven't
looked
at
suit-
manifests
or
comeds
yet.
But
my
initial
thought
right
now
is
that
it
should
support
coast
widths
and
possibly
with
some
extensions,
or
you
know,
allowing
extensions
and
perhaps
some
others-
I
mean
we
don't
have
to
just
pick
one
official
format
and
only
support
it,
although
it
would
be
nice
to
pick
one
that
is
widely
used,
so
we
don't
want
having
a
thousand
flowers
blooming
here,
doesn't
help
interoperability.
E
E
E
E
E
We
know
we
have
to
carry
more
than
one
coast:
wood,
because
there's
two
different
types
and
if
you're
putting
coast
woods
on
that
represent
installed
software,
there
could
be
many
software
packages
installed.
So
you
can't
just
have
one
coast
wood
to
describe
it
all,
because
those
were
created
independently
and
signed
independently.
So
you
have
to
carry
it,
you
have
to
relay
all
of
them.
E
E
E
E
Okay
yeah,
so
you
know
go
back
back.
Please.
I've
also
been
having
a
side
discussion
about
coast
with
you
know,
there's
some
they're,
they're,
somewhat
file
system,
oriented
and
seems
like
you
could
that
doesn't
work
for
all
all
devices.
It
seems
like
you
could
work
around
that
by
extensions
another
thing.
I
thought
that
you
know
in
the
phone
world
a
lot
of
the
software
is
in
form
of
applications,
so
coswood
doesn't
have
anything
that
describes
an
application.
E
E
F
Yeah,
just
making
sure
you
can
hear
me,
my
question
is:
there's
you
have
three
options
on
the
slide.
Are
you
saying
that
all
three
options
are
supported
or
is
there
a
question
to
the
working
group
about
which
option
should
be
allowed,
or
I
couldn't
understand
what
the
three
options
were?
Who
is
the
chooser
of
the
option?
F
E
E
H
H
E
F
F
Hank,
let
me
elaborate
on
why
I
said
the
preference
and
that's
I
hypothesize.
It
will
be
common
in
protocols
that
you'll
want
to
have
some
information
about
some
additional
information
about
each
cause.
Word,
that's
not
beyond
that
which
is
embedded
in
the
coswood
itself,
okay
and
so,
and
option
number
one.
You
can't
do
that
without
having
something
like
a
parallel
array
or
duplicating
the
causewood
into
some
other
structure
too.
So
that's
why
I
don't
like
option.
One
is
if
you
need
to
pass
anything,
that's
on
a
per
coswood
basis.
F
You
can't
do
it
in
option
number
one
without
doing
option
number
two
or
three.
So
that's
why
I
said
I
didn't
like
number
one:
okay,
if
you
only
have
the
list
of
causewoods,
then
it's
all
the
same
right.
It
doesn't
matter
which
option
you
choose
option.
One
is
fine,
but
I
hypothesize
that
it
is
common
to
have
additional
information.
F
That's
what
I
think
is
the
cleanest
way
to
do
it.
I
think
that
matches
well
things
like
layered
attestation,
where
you
have
a
wood
per
layer,
for
example,
and
you
have
a
set
of
claims
about
each
layer
and
you
can
reuse
the
same
claim
ids
about
you
know
like
I
don't
know
time
stamp
or
time
sense,
boot
or
time
sense
that
that
software
has
been
running
things
like
that,
you
could
reuse
the
same
thing
in
each
sub
module.
I
think
that
would
be
fine.
That's
why
I
think
three
is
the
cleanest.
F
So
that's
why
I
said
my
preference
is
to
say
you
can
have
multiple
of
them
and
with
each
coswood
you
can
have
another
set
of
eight
claims,
including
standard
ones,
your
private
ones
or
whatever
else,
and
my
understanding
is
sub
modules.
Let
you
do
that
already
and
so
that's
the
long
reason
for
my
preference
for
three.
Hopefully
I
got
my
assumptions
right
and
but
if
not,
then
you
can
at
least
understand
what
my
preference
is
and
map
them
to
something
else.
If
that's
option
four
or
something
so.
E
H
H
H
I
guess
that's
okay,
but
that
is
an
another
threshold
where
you
have
to
can
make
mistakes.
So
that's
my
only
small
issue
with
three
I'm
still,
okay,
with
the
with
the
evidence
payload
claim,
because
I
think
it's
fine,
because
payload
apparently
is
more
on
the
rim.
Stuff
that
we
are
building
with
here
with
with
thomas
and
co
and
and
evidence
is
more
on
the
the
eat
stuff,
and
it
makes
a
lot
of
sense
to
to
say
yeah.
This
is
not
evidence
when
you
put
it
into
a
heat.
H
D
Ned
yeah,
so
kosovo
has
a
you
know,
a
signature
is
attached
to
it.
It
has
a
signature
attached
to
it.
We
have
a
draft
that
describes
how
to
do
an
unsigned
eat.
Is
this
as
option
are
any
of
these
options?
Are
all
these
options,
this
asserting
or
assuming
that
the
signature
component
of
coast
wood
goes
away,
or
are
we
saying.
E
H
E
H
Yeah,
this
is
saying
speaking
to
that
yeah.
That
is
correct.
They
are
not
altering
them.
The
the
the
co-rim
part
extends
a
single
item
into
a
coast
wood,
but
leaves
it
a
coast
bed.
So
so,
of
course,
we
can
better
reference
commits
that
they
can't
do
this
natively.
We
would
have
a
clunky
structure.
We
want
to
do
it
with
the
neat,
orderly
structure,
so
there's
a
tiny
extension
to
close
with
this
rim
stuff,
but
that's
it.
It's
the
same
as
before,.
E
E
I
I
think,
that's
one
possibility,
if
that's
you
know
unworkable,
or
somebody
comes
up
with
you
know
some
brilliant
alternative
to
ghostwoods.
For
that
that
could
also
be
an
option.
I
don't
think
just
because
we
picked
coast
woods,
we're
picking
the
the
one
and
only
format
for
for
carrying.
You
know
software
descriptions
and
measurements.
C
Okay,
because
for
our
use
case,
the
pc1,
as
you
know,
going
for
crossfit
is
a
bit
overkill,
because
the
overhead
of
the
encoding
and
the
fact
that
we
need
to
please
the
cosmic
format
in
many
respects
that
are
not
essential
to
us.
You
know
creates
this
multiple
bytes
of
rubbish,
basically
that
we
just
need
to
put
there
in
order
to
to
please
the
the
format
so
yeah.
For
the
time
being,
we
have
defined
our
own
software
measurement
claim
right.
C
E
B
E
E
G
Yeah
thanks
lawrence
sorry
to
insert
this
in
here,
but
just
as
a
disclaimer,
I'm
the
co-chair
of
the
fido
alliance,
iot
working
group,
and
we
we're
developing
a
well
we're
pretty
far
along
in
developing
a
device.
Onboarding
spec,
it's
available
on
our
website
and
and
we
do
have
a
normative
dependency
on
feet.
G
One
of
the
things
that's
been
discovered
is
that
the
way
we
are
using
juice
is
we're.
Taking
our
ueid
is
we're
using
a
we're,
calling
it
something
called
the
guide
in
the
spec
global.
You
you
globally
universal
id,
and
our
reading
was
that
that
maps
directly
to
the
ueid.
So
we
said
that
for
any
payload
we
can
go
ahead
and
transmit
what
we,
what
the
spec
calls
as
a
guide
in
the
ueid
field.
G
The
current
text
states
that
the
ueid
quote
should
be
permanent,
so
I've
given
so
I've,
given
some
guidance
to
the
fido
working
group
that
we
can
live
with
that
language,
because
it's
a
should
requirement
and
and
just
move
on.
But
the
issue
is
you
know,
the
issue
is
what
it
you
know
is
does
does
the
rats
working
group
feel
similarly
on
this,
and
it
would
be
something
that
I
think
we
need
to
get
resolved
before
last
week
we
may
want
to
resolve
before
last
call.
G
The
issue
has
been
posted.
The
fido
iot
working
group
has
proposed
text
where
we,
where
we,
where
we
just
we're
summarizing
we
describe
where
ueid
could
it
could
be
replaced
during
a
device
life
cycle,
so
this
is
kind
of
so
this
is
kind
of
a
pesky
issue.
I
think
what
lawrence
lawrence
may
have
some
words
on
this
on
privacy,
preservation
and
ueid,
as
well
so
I'll
kind
of
give
the
floor
back
over
to
lawrence
yeah
we're
taking
questions
lawrence.
Did
you
want
to
comment
on
this.
E
Yeah
so
I
mean
my
my
intention:
was
you
know
that
uids
should
be
permanent,
that
they,
maybe
I
should
even
say,
must
be
permanent,
that
this
shouldn't
be
changing.
The
uid
shouldn't
be
allowed
and
then,
in
the
discussion
on
the
on
the
github
issue,
I
proposed
an
s-u-ue
id,
which
is
a
semi-permanent
ueid
which
can
be
changed
on
change
of
ownership
and
and
factory
reset
and
stuff.
Like
that,
I
also
think
there's
other
possibilities
for
addressing
privacy
preservation
for
ueids.
G
E
G
Okay,
it's
holding
up
the
fido
spec
progress,
that's
what
I
mean.
I
should
have
probably
mentioned
that.
So
you
know
I
I
think
if
we're
saying
that
we
don't,
if
the
group
wants
us
to
go
and
revisit
this
and
I'll
say
that
the
fido
stack
has
to
you
know,
you
know
the
use
of
the
photo
spec
for
ueid
may.
It
may
have
to
be
revisited,
though,
because
the
rat's
document
may
evolve.
G
B
G
B
A
And
milestones
we
did
not
cover
those
it
I'd,
love
to
get
an
estimate
from
you
and
I'll
bring
it
to
the
list
lawrence.
In
terms
of
where
you
think
eid
is
at,
I
don't
think
you're
going
to
make
the
milestone
and
tuda,
and
some
of
the
other
drafts
won't
make
your
milestones
either
some
of
the
other
ones
that
are
earlier
on
the
milestones,
I
think
look
fine,
so
we'll
do
that
on
list.
Thank
you.
