►
From YouTube: IETF114 V6OPS 20220726 1400
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
B
So
hi
all
I'm
warren
I've
been
serving
as
opseidi
for
a
long
time
now.
I
think
that
the
same
currently
in
my
third
third
term,
I
think,
and
while
I
am
still
enjoying
it,
I
think
it
would
be
useful
for
there
to
be
a
bunch
of
other
candidates
as
well
for
the
upcoming
upcoming
cycle,
so
I
will
probably
run
again,
but
I'd
also
really
really
like
some
other
people
to
run.
B
So
if
anybody
is
potentially
interested
or
just
want
to
know
more
about
the
position
or
find
out
what
it's
actually
like,
please
come
and
find
me
at
some
point:
I'm
happy
to
chat,
let
you
know
sort
of
the
time
investment
what's
actually
needed,
etc.
So
you
know,
look
for
me
I'll,
probably
be
wearing
a
hat.
Come
chat,
happy
to
talk.
D
A
E
F
E
E
E
So
there
are
obviously
some
ways
to
adjust
this,
although
I
will
assert
that
operationally,
they
are
all
very,
very
heavyweight
and
not
really
sustainable,
they're
problematic
to
scale
across
diverse
multifunctional
organizations.
They
impose
very
significant
impediments
to
operations
where
ipv6
is
already
really
hard
to
get
in
the
door
in
a
lot
of
enterprises.
E
They
would
require
automation,
platforms
that
are
also
you
know,
sort
of
in
their
fledgling
state
and
that's
not
to
even
mention
all
of
the
embedded
devices,
operational
technology,
car
partner,
guest
equipment
and
other
legacy
stuff
that
you
know
you
may
or
may
not
see,
but
everybody
probably
has
some
of
that.
You
just
have
no
mechanism
for
changing
what
the
address
table
preferences
are.
So
you
can
do
this
in
linux.
E
So
in
addition
to
that,
if
you
go
and
look
at
some
of
the
files
in
the
code,
you'll
still
see
remnants
of
rfc
3484
in
actively
deployed
and
up-to-date
systems.
Now
that
was
written
6724,
which
replaced
3484
was
written
in
2012
that's
10
years
ago.
So
even
after
10
years,
we
still
don't
have
a
full
migration
over
to
whatever
the
current
rfc
standard
is
for
this.
Addressing
that
tells
me
mean
time
to
replacement
implementation
replacement
is
over
10
years.
E
So
that's
one
of
the
reasons
that
we
haven't
actually
proposed
a
solution
to
this,
because
it's
going
to
take
a
very,
very
long
time
to
even
get
it
in
place.
So
what
we
want
to
do
is
just
codify
the
problem
so
that
anyone
that's
looking
for
it
can
go,
find
it
very
easily
because
I'll
be
fully
honest.
It
was
very
difficult
for
me
to
find
information
on
that.
E
So
here's
a
quick
example
very,
very
simple.
This
is
just
something
that
I
threw
together
in
my
little
lab
that
I've
got
it's
just
a
simple
ping
that
shows
you.
If
I've
got,
you
know
the
dns
records
matching
a
record
quad
a
record
both
pointing
to
the
same
dns
name.
You
know
obviously
v4
and
v6
address
families.
If
I
just
do
a
simple
ping
which
will
use
the
dns
resolution,
it
will
always
use
the
ipv4
address.
E
There
are
lots
and
lots
and
lots
of
other
examples
of
this,
and
you
know
all
of
the
caveats
of
you
know.
Applications
can
decide
blah
blah
blah
yeah,
that's
also
relevant.
However,
this
is
a
pretty
good
example
and
probably
sort
of
the
first
order
testing
that
any
operational
engineer
is
going
to
do
and
they're
going
to
right
away
say
well.
This
doesn't
look
right
next
slide,
all
right,
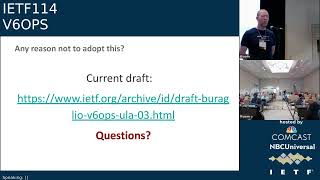
so
is
there
any
reason
not
to
adopt
this
draft?
That's
my
question
to
you:
if
you
haven't
read
it,
it's
pretty
easy!
E
G
E
G
E
E
I'm
not
saying
it's
bad.
Well,
I'm
just
saying
that
as
someone
who
has
helped
support
engineers
for
a
very
long
time,
that's
not
something
it's
something
that
throws
them
off
and
it's
something
that's
relatively
unexpected
by
people
that
are
just
coming
into
ipg
v6,
and
so
therefore,
it
typically
is
a
bit
of
an
impediment,
because
it's
a
one-off.
G
Right
so
I
mean
what
I'm
getting
at.
Is
that
what
you
described
doesn't
surprise
me
at
all
and
doesn't
seem
like
an
operational
problem
to
me
at
all,
and
so,
if
a
lot
of
people
see,
if
a
lot
of
people
have
the
reaction
that
you
do,
then
it's
probably
worth
documenting
that
if
you
deploy
a
dual
stack
environment,
you
shouldn't
expect
that
ipv6
will
always
be
chosen.
But
aside
from
that,
I
don't
see
why
there's
a
an
issue.
H
Hi
jen
linkova.
First,
let
me
answer
to
ted's
comment.
Actually,
this
is
bad
because
dual
strike
is
supposed
to
be
a
path
to
eventually
get
rid
of
before,
if
you're,
never
using
v6.
You
have
no
idea
if
your
v6
is
working
while
you
kind
of
assume.
Oh
I've
been
running
ipv6
for
years,
so
this
is
actually
not
not
a
good
situation.
H
However,
my
question
is
so
I
read
the
draft
and
I
was
kind
of
confused
about
that
purpose,
because
the
behavior
is
actually
documented
in
default.
Address
selection,
rfcs
right.
So
I'm
just
curious.
If
the
conclusion
of
the
document
should
be
just
don't
use,
ula
use
global
address
space
and
your
problem
just
go
way.
The
way
automatically.
E
I
mean
that's,
certainly
one
answer
and
I
won't
say
that
it's
wrong.
That
would
be
the
answer
that
I
would
prefer,
although
I
did
not
think
that
I
should
be.
You
know
those
of
us
that
wrote
this
draft
wasn't
just
me
thought
that
we
shouldn't
be
that
prescriptive
with
it.
We
really
just
wanted
to
identify
the
behavior
I
would.
I
would
prefer
gua
addresses
everywhere.
E
H
Like
I
understand,
but
then
we
probably
just
say,
if
you
using
ula,
be
ready
for
this,
it
basically
becomes
useless.
So
there's
no
reason
to
have
ulas
because
they're
not
going
to
be
used,
but
if
you
really
want
to
get
v6
experience,
use
global
addresses
and
my
my
opinion,
it
would
be
much
more
useful.
H
The
document
will
be
much
more
useful
than
because
it
will
be
actionable.
People
can
read
it
and
come
to
some
conclusions
and
we
can
give
them
some
operational
guidance
instead
of
just
telling
them
things
which
they
could
probably
find
in
another
document.
They
just
look
hard
enough,
and
actually
I
find
your
slide
very
optimistic,
because
you're
saying
that
in
10
years
enterprises
need
ipv6.
I'm
really
glad
to
see
to
hear
that,
because
most
enterprises
do
not
agree.
I
I
E
E
I
I
There
is
no
repeatability
when
you
got
to
address
families
well,
there
should
be
at
least
the
expectation
of
it
yeah.
There
is
an
expectation
that,
if
you're
talking
to
a
global
address,
you'll
do
v6,
first
sure
and
if
you're
talking
and
if
you're
talking
to
a
ula
you'll
do
ula
first,
if
your
vendor
has
done
the
right
thing,
if
your
vendor
has
stuffed
it
up,.
E
I
E
I
E
G
E
And
again,
I'm
not
trying
to
propose
that
we
fix
anything.
All
I'm
doing
is
writing
a
draft
that
says
this
is
unintended,
and
this
is
this
is
unexpected,
so
that,
when
other
enter,
when
other
engineers
go
to
do
test
these
things
that
they
can
go
okay.
Well
now
this
is
written
and
now
I
know
what
to
expect.
J
J
Just
using
gua
would
be
great,
except
there's
not
a
lot
of
address
space
that
you,
if
you're
not
actually
grabbing
a
gui
address
space
for
some
purpose
to
use
in
things
like
what
you
did
kevin
with
building
labs
and
documentation
and
stuff.
So
yep
we're
kind
of
falling
in
between
a
little
space
here
where
things
can
get
complete.
E
Yeah
and
you're
right
so
there
are,
there
are
some
other
things
as
well
that
are
not
just
the
you
know
the
lab
space
and
other
things,
which
is
how
I
ran
into
it.
There
are.
There
are
reasons
that
that
organizations
don't
go,
get
gua
space
that
aren't
just
because
they
don't
want
to
pay
for
it.
There
are
also
small
deployments
that
will
enable
ula
by
default
as
their
ipv6
stack,
and
you
know
those
are
mostly
open
source,
but
they
exist
out
there
and
are
on
by
default.
K
Okay,
everything
cisco.
I
agree
with
you,
it's
unexpected,
maybe,
but
it's
fully
intended
behavior.
But
my
main
point
when
I'm
coming
to
the
mic
is
to
challenge
your
statement
telling
that
enterprise
mainly
use
ula.
That's
not
really
what
I'm
seeing
and
I'm
meeting
many
enterprise
customers
right
simply.
E
E
M
J
N
I
A
N
N
About
the
methodology,
well,
no
rocket
science
here
and
just
the
traceroute-like
technique,
although
this
is
with
our
own
library,
and
what
we
do
is
that
we
test
each
pair
of
vms
in
both
directions.
So
vma
is
the
sender
and
vmb
is
the
receiver
and
we
do
the
opposite
for
each
pair
for
each
experiment,
we
have
a
test
with
udps
layer,
4
and
tcp
as
layer
4,
because,
as
I
mentioned
initially,
we
were
suspecting
that
we
might
have
some
differences
between
the
two
and
spoiler.
N
N
We
also
test
it
with
no
next
header
and
also
with
ethernet
as
the
next
header,
so
based
on
rfc
8986
and
for
each
experiment.
We
try,
without
extension,
editor
as
a
comparison,
so
we'll
see
the
result
right
after
this,
and
what
we
do
for
the
prop
traffic
is
that
we
marked
it
with
an
email
address,
so
that
entities
could
identify
us,
and
it
is
based
on
the
draft
that
you
see
on
the
screen.
N
So
the
two
tricky
parts
here
is
that
if
you
want
to
be
able
to
attribute
the
drop
to
a
specific
autonomous
system,
well,
you
will
face
a
lot
of
routers
that
do
not
respond
and
so
for
the
first
figure
on
the
top.
You
see
that
the
first
two
rotors
responded
and
then
nothing
and
actually
this
is
what
we
saw
very
often.
N
So
if
this
is
the
truth,
without
extension,
header
and
then
you
made
a
test
with
an
extension
letter,
if
there
is
a
drop
somewhere
on
the
path,
it
becomes
hard
to
guess
which,
as
is
responsible
for
the
drop.
So
this
is
something
that
we
have
to
improve
in
the
algorithm
and
next
slide.
Please
all
right,
so
the
interesting
part
so
for
the
hub
by
hub
first,
this
is
in
red,
obviously,
because
this
is
very
bad.
N
So
if
you
take
the
first
row
with
the
length
of
8
bytes,
you
see
that
you
have
roughly
10
9
or
10
persons
going
through
and
obviously,
if
you
increase
the
size.
So
if
you
take
256,
you
roughly
have
three
persons.
So
this
is
very
bad
and
it
goes
worse
if
you
increase
the
size.
So
overall,
you
cannot
rely
on
buy
hops
if
you
want
to
use
them
over
the
public
environment.
N
So
if
you
look
at
the
udp
column
from
size,
8,
bytes
to
24
included,
this
is
for
yellable
and
once
you
reach
32,
you
see
a
little
bit
of
drops.
So
this
is
still
good,
but
you
cannot
call
it
a
reliable
anymore,
but
the
big
drop
that
we
noticed
is
once
you
reach
64
bytes,
and
it
goes
worse
and
worse
when
you
increase
it
again
again
here
you
see
some
differences
between
udp
and
tcp.
N
I'm
rooting
headers
in
orange
2
because
some
are
good
and
some
are
bad.
The
one
that
are
going
through
are
types
2,
3
and
5
and
6,
and
actually
the
ones
that
are
not
reliable,
not
that
bad
but
still
unreliable
are
type
zero
one
and
four-
and
this
is
not
really
a
big
surprise
here-
because
zero
and
one
are
supposed
to
be
duplicated
and
type
4-
is
segment
rotating.
So
this
is
actually
quite
a
good
news
from
a
security
point
of
view.
N
N
So
what
we
can
learn
from
this
is
that
by
hub
again
you
cannot
use
them
and
and
think
they
are
going
through
destination
options.
You
have
hope
until
a
specific
sizes-
and
we
have-
I
think
nalini-
is
there-
she
has
a
draft
about
a
destination
option
not
only
for
limited
domains
but
for
the
public
internet.
O
N
N
So
what
we
plan
for
this
draft
is
to
continue
measurements
with
the
wild
version.
So
up
to
now
we
had
a
specific
testbed
with
21
vms.
Now
we
want
to
probe
in
the
wild
on
random
prefixes,
and
actually
we
already
have
some,
let's
call
them
earlier
results
and
the
trend.
This
is
still
to
be
confirmed,
and
the
trend
is
that
it's
like
the
same
that
we
observed
some
are
improving.
Some
are
not,
but
basically
this
is
the
same.
N
N
P
Yeah
nalini
elkins
inside
products
yeah.
I
know
this
is
very
very
interesting.
I
think
we've
talked
a
bunch
about
this
and
it
would
be
very
interesting
to
find
out
exactly
why
and
we're
already
collaborating,
because
one
of
the
things
that
we
have
seen
is
that
there
are
certain
routers
which
have
bugs
which
keep
hot
by
hop
going
out
at
the
source
and
so
anyway.
P
So
so
what
we're
doing
is
we're
expanding
our
testing
because
we
have
done
some
testing
to
see
you
know
because
we've
had
I
get
our
results
are
to
the
contrary.
We've
shown
large
ftps
succeeding,
but
we
need
to
test
more
because
you
know
it's
only
from
you
know
two
or
three
continents
that
we've
done
it,
and
so
I
think
we
all
need
to
find
out
more
about
exactly
where
and
why
things
are
being
dropped.
Is
it
at
the
destination
network?
Is
it
bugs
or
you
know,
un
defaults
quite
what
yeah.
Q
Q
K
Q
Q
Q
So
at
the
end
of
the
day,
what
matters
is
the
result
of
the
you
know
the
the
whole
length
of
the
ipv6
extension,
the
the
ipv6
header
chain,
so
for
the
same
value
of
the
length
of
the
extension
header
for
this
for
tcp,
it
results
in
a
longer
extension
header
chain.
That's
why
you
get
like
higher
drop
rates.
N
H
H
So
I
guess
here
the
reason
might
be
the
router
might
need
to
see
syn
flags
and
if
your
tcp
flags
go
with
behind
the
value,
router
can
like,
like
routers
copy
on
cheap
or
something
like
looking
for
the
flags.
They
might
just
not
see
the
packet
as
being
tcpc
and
then,
as
a
result
drop
it.
So
what
I'd
like
you
to
say
is
that
esp
is
actually
a
very
good
example
proven
that
extension
header
works
when
we
need
them
like
when
mobile
phone
makes
a
wi-fi
calling
it's
using
asp
right.
H
So
esp
has
a
very
good
use
in
internet
and
it
works
yeah,
so
all
like
in
most
cases
we've
seen
packet
drops
because
there
is
no
reason
for
that
packet
to
go
through
anyway
right.
So
I
think
again
when
we
saying
that
we
cannot
use
extension
headers
on
the
internet.
We
need
to
find
good
use
of
them,
which
will
be,
which
would
benefit
users
in
general,
and
then
I
guess
the
situation
will
change.
Yes,
obviously,
the
random
packets
are
dropped.
I
A
D
N
A
A
A
B
B
A
Yeah,
so
I
am
a
little
bit
extracted,
so
I
think
that
you
know
with
so
many
rfcs.
There
are
two
issues.
The
first
issue
is
that
you
know
some
people
may
not
know
and
they
deploy
the
the
nd
and
the
first
hop
and
later
they
find
out
and
therefore,
when
later
after
you
have
already
deployed,
you
find
a
problem
and
you
need
to
fix
it.
Then
it's
more
difficult
to
change.
The
other
issue
is
that
you
may
you
may
know,
and
it
may
scare
you
that.
Oh
you
know
there
are
so
many
excuses.
A
Therefore
you
know
I
would
like
to
stop,
and
this
is
why
we
believe
that
having
a
complete
summarizing
all
the
issue
is
good
because,
just
like
I
have
seen
90
1999
in
the
past,
I
met
multiple
operators
and
they
are
concerned
that
oh
ipv6
have
a
lot
of
security
issues,
but
once
we
say
that
all
will
have
obviously
1999
and
it
summarizes
all
the
ipv6xcus
and
we
also
provide
solutions.
People
feel
much
more
comfortable,
and
so
this
is
what
we
are
trying
to.
Basically
do
the
same
thing
next
slide,
please.
A
So
in
this
draft.
We
basically
summarize
all
the
nd
issues
known
up
to
this
point
and
in
this
version
compared
to
the
previous
version,
a
major
improvement
is
that
we
now
clearly
separate
the
cause
of
the
issue
and
the
consequence,
because
in
the
previous
version,
we're
kind
of
like
you
know,
we
talked
about
multicast
excel.
We
talked
about
performance
excel,
but
many
of
the
performance
xu
are
actually
caused
by
multicast.
A
So
in
this
version
we
clearly
separate
out
the
cause
and
the
consequence-
and
there
are
really
there's
only
three
cause.
The
first
cause
is
multicast,
which
can
cause
performance
and
reliability
issue.
The
second
issue
is
that
and
the
trust
all
the
holes.
So
if
certain
holes
in
a
public
access
environment
cannot
be
trust,
then
you
will
have
a
problem.
This
is
some
other
issue
and
that's
the
third
cause
is
that
nce
is
installed
on
vmax,
and
this
can
also
cause
some
issue.
A
A
A
So,
overall,
we
also
learned
a
lesson
from
all
these
solutions.
You
know
the
solution
didn't
clearly
talk
about
isolation,
but
when
we,
when
we
look
at
it,
they
many
of
these
solutions
actually
have
a
common
thing,
which
is
to
isolate
holes,
to
solve
the
issues,
and
this
is
a
good
lesson
and
also
from
all
these
solutions.
We
find
out
that
there
are
four
isolation
methods
appear
in
different
drafts,
but
we
check
them
out.
A
Basically,
these
are
the
you
know:
link
isolation
is
separating
holes
in
layer
two
and
then
there's
also
the
subnet
isolation,
which
is
to
isolate
holes,
giving
these
holes
a
different,
subnet,
graphics
and
then
there's
the
gua.
We
call
it
the
gua
isolation,
it's
basically
the
original
nd
approach,
the
nd
approach,
which
is
to
set
the
prefix
pio
the
l-bit
to
zero.
In
this
case,
the
host
will
not
hold
the
communication
with
the
gua
will
go
through
the
router
and
will
not
communicate
the
host
will
not
communicate
directly,
but
the
lla
they
can
still
communicate
directly.
A
A
A
A
G
A
And
then
you
know
after
you
use
this
combination,
what
kind
of
issues
are
still
remaining?
You
know
what
you
may
need
to
do
so
for
each
basically
for
each
of
the
combination.
We
is
playing
all
of
these,
so
these
kind
of
like
provide
a
systematic
way
for
an
enterprise
for
enterprise.
The
scenario
can
be.
There
are
many
scenarios
and
therefore
you
know
by
providing
a
systematic
guidelines.
A
Enterprise
can
kind
of
go
through
the
list
so
that
they
can
decide.
Okay,
you
know,
for
my
first
hop
what
will
be
the
best
solution,
so
this
is
the
the
idea
of
the
draft.
We
now
believe
that
the
drive
is
in
a
very
good
safe,
and
we
hope
that
people
will
will
eat
and
provide
a
comment,
and
at
some
point
we
probably
want
to
ask
the
google
the
wg
for
adoption.
Thank
you.
H
H
I
H
A
We
please
don't
just
look
at
this,
for
example,
gua
isolation,
you
know
kind
of
like
by
itself.
We
are
basically
going
through
a
list
and
starting
from
the
strongest
isolation.
Therefore,
if
you
feel
that
all
these
holes
cannot
be
trusted
at
all,
then
you
probably
want
the
stronger.
You
know:
isolation
yeah.
It
will
not
even
get
to
the
gua
isolated
yeah.
H
But
quite
often
you
cannot
do
this
because
hosts
might
need
to
talk
to
each
other,
especially
all
these
you
know,
like
special
systems,
I'm
not
talking
about
laptops,
I'm
talking
about
like
building
management
systems
and
so
on.
They
must
talk
to
each
other.
So
I'm
basically
trying
to
understand
what
kind
of
security
and
threat
preventions
you
are
getting
by
item
number
three,
because
my
understanding,
you
are
human,
good
behavior.
The
host,
in
this
case.
A
Again,
you
don't
want
get
to
if
you
get
to
gua
isolation,
we
will
point
out
that
the
point
out
that
you
know
it
solves
certain
problems,
but
there
are
other
problems
that
it
does
not
solve.
Therefore,
you
know
if
you
are
with
the
gua
isolation
you,
if
you
are
concerned
that
the
holes
cannot
be
trusted,
then
you
may
need,
to
you
know,
add
the
field
ring,
etc
to
to
deal
with
that.
So
it's
not
that
you
know
you
get
to
a
gua
isolation
and
and
zua
isolation
will
take
care
of
everything.
H
H
A
H
R
Okay,
this
is
the
overview
of
the
drafts
in
ihf
113,
we
presented
the
requirements
to
multi-domain
activities
only
network
based
on
the
comments
received,
the
new
draft
focus
on
framework
and
the
title
has
been
cheap
twice.
So
this
case
is
one
draft
multiple
titles.
Okay,
next
slide,
please
all
right
comments
have
been
received
from
this.
Ops
all
are
appreciated.
R
Since
ietf
113,
the
following
variants
had
been
made,
the
document
architecture
is
adjusted
to
make
the
logic
straight
forward,
and
the
section
of
scenarios
has
been
emerging
to
other
sections
based
on
the
comments
of
sheep
atp
and
some
requirement
items
have
been
deleted.
We
add
illustration
how
new
framework
dos
v
for
recess
converge
compared
to
other
solutions.
R
R
Also,
there's
so
many
activities
and
only
techniques,
but
challenges
or
issues
are
still
met
when
playing
fbs
is
only
in
networks.
I'll
give
some
a
brief
introduction.
The
first
one
is
partial:
fpv
is
only
deployment,
some
domains
ipvcs
only
and
others
are
not.
The
second
one
is
unless
three
traffic
winding
when
stateful
v46
gateway
deployed
as
an
edge
of
the
backbone.
The
next
one
is
the
visibility
of
the
ordinary
addresses.
R
This
means
that,
when,
as
obviously
b
is
used
to
encapsulation
fpv
for
packaging
activates
its
own
network,
the
old
ipv
kit
contains
no
original
ipv4
address
information.
The
next
one
is
the
consistent
data
format.
Some
domains
use
translation,
some
domains
encapsulation,
which
so
this
would
lead
to
excessive
conversion
gateways
and
the
network
complexity
and
last
night.
Please.
R
R
For
ipv4
service
deliver
all
activities
on
the
network.
Ipv4
package
will
be
transformed
into
ipv1
by
translation
encapsulation
in
ue
or
at
the
edge
of
the
devices.
Then
the
forwarding
activity
for
data
in
the
form
ipv6
packet
will
follow
topology.
This
is
network.
This
is
easy
to
understand
right,
but
in
the
new
framework
each
pe
id
device
will
be
identified
by
at
least
one
ipv6
mapping
prefix.
R
It
will
also
have
one
or
more
associated
ipv4
prefix,
which
are
extracted
from
local
ipv4
working
tables
or
dress
posts.
The
mapping
relation
between
ipv4
address,
block
and
ipv6
mapping
prefix
is
called
mapping
rule.
In
this
framework.
The
method
will
have
at
least
the
following:
data
from
structure:
ipv4
address,
blog
and
activision
mapping,
prefix
and
maybe
include
other
information
in
the
future.
So
these
mapping
rules
can
be
transmitted
across
domains.
R
It
gives
the
direction
and
the
egress
of
ibv
for
data
transmission
in
multi-domain
api
basis
on
the
networks
using
mapping
rule
exchange
the
egress
pe
compare
rsp
that
if
the
destination
address
of
ipv4
packet
is
within
the
scope
of
ipv4
address
block
of
the
mapping
rules,
please
send
them
to
me
so
the
ingress
pe
can
use
the
mapping
rule
to
generate
the
corresponding
ipv6
address
by
appending
ipv4
address
to
the
activities.
Mapping
prefix.
This
works
both
for
sales
and
destination
address
this
kind
of
package
called
ipv4
embedded
activities
package.
R
R
That's
nice,
please.
So
this
illustrates
the
framework.
From
the
perspective
adapting
ep
devices.
Adapter
is
a
function
of
entity
in
the
p
device
which
implements
a
conversion
of
ipv4
packs
into
ipv6
for
ipv
systems
iqb
for
self
delivery.
It
has
three
components
as
in
which
is
the
first
one
is
role
management
layer
deal
with
the
management
american
rules,
the
manager,
the
mapping
rule
database
in
a
pe
store.
All
the
mapping
rule
records
it
receives
the
interface
with
the
adaptive.
Rp
is
used
for
the
exchanging
a
mapping
rule
with
each
other.
R
The
interface
with
routing
process
layer
is
used
for
the
transmission
of
mapping
rules,
so
the
underlying
rocking
processing
is
in
charge
of
the
exchanging
mapping
rule
with
each
other
with
other
piece,
and
it's
related
about
information
so
to
support
the
transformational
mapping.
Rule
has
rarely
maybe
the
field
b2b
for
plus
protocol
or
other
control
protocols
needed
to
be
extended.
R
R
Here
I
want
to
further
illustrate
the
gap
and
how
the
new
framework
addresses
the
gap.
You
know
in
ic
5565
the
software
mesh
architecture,
the
software
tunnel
requires
address
or
remote
software
in
the
pawn
to
be
the
same
as
the
address
of
the
bgp
network
right.
The
bt
network
is
used
for
the
tunnel
in
the
pawn.
R
R
Firstly,
the
root
response
to
the
mapping
prefix
of
the
egress
will
be
announced
through
the
whole
network,
so
the
ingress
will
know
how
to
forward
the
activity
packet
to
the
egress.
Secondly,
the
mapping
rule
will
also
be
exchanged
between
the
lingua
as
the
egress
keys.
This
step
should
precede
the
precise
for
data
for
data
transformation,
otherwise
the
data
already
from
ipv4
packet
will
be
dropped
due
to
the
absence
of
the
fpv's
mapping
prefix
corresponding
to
the
designation
ipv4
address.
R
Certainly
when
our
ingress
p
receive
previous
packet
from
client-facing
interface,
it
looks
up
in
micro
database
to
find
the
mapping
rules
which
has
matched
the
text
destination
active
address.
Then
the
increase
pe
must
convert
ipv4
destination
address
into
ipv6
address,
using
the
mapping
prefix
and
forward
it
to
the
egress
pe.
This
yeah.
With
this
new
framework,
ipv4
embedded
ibvc
package
can
transverse
multi-domains
networks
next
month.
Please.
R
R
The
field
trail
covers
redo,
means
metro
area
network,
we
see
every
backbone
network
is
es,
number
is
4134
and
the
cloud
system
networks
mean
for
hard
turn,
which
are
different
domains.
The
field
trail.
Actually,
the
physical
trail
has
no
functional
requirements
to
the
heavy
backbone.
The
backbone
only
needs
to
know
the
passing
of
the
rod
corresponding
to
the
mapping
prefix.
R
So
we
deploy
the
pe
devices,
which
is
adapt
capable
in
the
production
networks.
Different
p
are
configured
with
different
activities:
micro
prefix,
they
jointly
create
a
multi-domain.
Previous
only
network
mapping
rules
are
exchanged
between
p
devices.
The
network
can
speculative
ipv's
packing
ipv4
embedded
package.
It
also
can
support
the
communication
initiated
from
the
outside,
so
it's
open,
based
on
the
so
based
on
the
implementation
and
the
trail
nationalities.
R
Based
on
the
implementation,
in
the
trail,
we
found
that
this
framework
works
well,
it
is
scalable
and
can
integrate
with
existing
fpv.
Only
approaches
such
as
four
six
four
accelerate
the
addition.
This
only
activities
only
model
can
naturally
be
extended
to
to
multi-domain
that
was
operated
by
different
operators
right.
So
next
we
will.
The
first
refinement
document
will
be
made
to
consolidate
the
requirements
and
further
stabilize
the
text
at
2d
script
that
describes
the
framework.
R
H
Genuine
collaboration,
I
read
the
document
and,
to
be
honest,
I'm
slightly
confused
about
the
requirements
because,
for
example,
the
first
requirement
says
it
should
be
beneficial
for
wider
ipv6
adoption.
I'm
a
bit
confused
how
to
find
out,
if
particular
solution
satisfies
that
requirement
or
not.
Secondly,.
H
H
I
am
not
sure
why
even
mentioning
sr
v6
as
a
requirement,
because
I
not
sure
that
we
shall
be
mandating
any
particular
technology
right
people
might
want
to
use
some
other
technologies.
So
I
don't
think
it's
like
should
be
in
the
document
and
third,
like
this
document
says
no
additional
security
compromises
from
risk
assessment
perspective.
It
might
be
not
true
right.
You
might
agree
to
accept
some
risk
if
your
risk
assessment
shows
that
benefits
of
the
solution
exceeds
potential
impact.
H
R
R
We
cannot
suppose
that
all
the
service
is
ipv6
based
because
this
is
not
under
control
operators,
so
we
hope
that
the
network
analyst
should
be
activision-based,
so
I
think
this
will
be
helpful
for
ipv6
development,
as
actually
which
has
been
done
by
some
operators-
folks,
for
example,
4x4
athletes
which
have
been
done
some
operators
which
is
closed,
the
ipv4
after
the
networkly
and
ipv4
services
right.
So
this
is
the
first
question
and
the
second
question
about
srv6
yeah.
R
R
R
The
key
device
mainly
implements
the
microsoft
management
and
the
conversion
between
ipv4
and
ipv6
package.
Actually,
it's
some
kind
of
router
right
and
under
the
convergence
aesthetics,
there's
no
state
maintained
at
the
age
of
network,
so
it
does
not
introduce
too
much
security
issues
to
the
whole
network.
Of
course,
maybe
the
material
exchange
will
be
based
on
bgp
net
broker
in
the
future,
but
this
is
there's
some,
maybe
some
issues
which
means
based
on
bb4
protocol.
I
think
this
can
discussed
in
other
future
documents.
That's
my
answer.
Thank
you.
F
F
F
R
R
R
The
second
one
is
about
srv6,
as
as
I
have
mentioned,
that
different
people
may
have
different
understanding
to
these
issues,
because,
as
of
this
is
a
new
thing
right,
it
is
still
in
a
stage
of
trail
and
maybe
some
deployment,
maybe
some
trail.
But
I
think
this
can
be
is
a
further
discussion
in
the
future.
I
don't
think
this
is
a
very
cl
srv6.
R
F
R
R
D
B
B
S
S
So
we
had
33
top
level
teams,
we
had
800
plus
applications
and
by
applications
I
mean
external,
facing
web
apps.
These
were
not
count.
This
does
not
include
the
internal
applications
and
then
the
number
that
really
stands
out
is
the
69
authorizations
we
had
to
get.
The
project
was
so
large
that
we
had
to
get
69
directors
or
senior
managers
to
sign
off
on
on
the
project
and
if
they
didn't,
then
we
none
of
us
would
have
been
able
to
move
forward
and
I'll.
Tell
you
why
that
was
in
a
little
bit.
S
Excuse
me
so
the
the
domain
transition
was
very
public.
It's
obviously
tracked
it's
very
visible
externally,
externally
and
internally,
and
there
was
extremely
high
level
of
integrative
efforts
between
applications
and
infrastructure
teams
and
compute
and
network
with
the
primary
infrastructure
teams.
The
applications
teams
were
again
the
business
applications
that
had
external
facing
web
apps
next
slide.
S
S
So
we
have
the
systems
management,
and
that
means
that
that
you
know
the
development
test,
release
and
update
system
management
applications,
the
business
applications
themselves.
This
could
be
the
legacy
on
prime
and,
of
course,
web
mobile
and
cloud,
and
they
all
have
and
they're
all
split
by
different
teams.
So
multiple
teams
would
have
the
same
ecosystem
for
themselves.
S
And
then
we
have
the
another
layer.
Is
the
application's
life
cycle,
so
there's
always
a
matter
of
legacy,
the
ones
that
are
live
and
the
one
the
applications
that
are
transitioning
in
the
design
process.
We
have
to
worry
about
development
and
test
environments
and
teams,
release
systems
and
teams
and
management
systems
and
teams.
S
It
also
means
that
we
have
to
really
keep
our
evangelist
hats
on
at
all
times,
because
applications
teams
are
not
necessarily
so
immersed
in
the
v6
world,
as
as
you
all,
as
we
all
are
and
they're
constant.
We
need
to
really
reduce
the
creation
of
new
legacy
applications
every
day
that
we
don't
address
these
up.
S
The
the
applications,
then
there's
just
new
applications
released
and
that
just
creates
more
legacy
and
more
inertia,
and
we
obviously
don't
want
to
have
dual
stack
maintenance,
it's
just
too
expensive
and
complicated,
and
everything
is
just
getting
more
and
more
complex
as
we,
you
know,
as
time.
Moves
on
next
slide.
S
So
incremental
so
here's
our
sophisticated
analogy,
and
so
I've
circled
every
point
where
the
network
infrastructure
would
integrate
with
another
ip
enabled
technology
or
application.
It
could
be
another.
You
know
a
harder
soft,
so
every
time
we
there's
a
red
circle
there,
then
we
have
to
figure
out
every
time
that
water
in
this
case
network
traffic
flows.
S
Then
we
need
to
just
make
a
determination
if
we're
going
to
enable
the
next
chain,
the
next
section
of
pipe
or
are
we
going
to
find
a
way
to
to
truncate
it
and
not
let
the
new
traffic
go
so
every
time
there's
a
new
intersection.
There
really
needs
to
be
a
cross-functional
determination
of
how
you're
going
to
handle
that
new
traffic
when
it's
entered
when
it's
flowing
out
of
the
infrastructure
and
into
its
applications.
S
S
S
The
next
slide,
so
as
businesses
grow
and
evolve,
they're,
just
adding
more
and
more
and
those
teams
end
up
under
new
leadership,
new
systems
that
they
deploy
but
next
slide,
but
they
all
tend
to
still
sit
on
the
same
network
infrastructure,
and
so
when
we
look
think
back
to
that
69
authorizations
that
we
needed
to
get.
This
is
one
of
the
primary
reasons
for
that
is
because
the
more
that
more
teams
share
the
same
infrastructure,
then
you've
either
got
you've,
got
to
make
some
deliberate
decisions
about.
S
S
Are
you
going
to
bifurcate
that
by
team,
or
are
you
going
to
really
try
to
eat
that
elephant
hole
and
try
to
convince
all
of
those
teams
to
go
at
once,
because
they're
all
going
to
be
affected
by
whatever
global
configs
you
you've
got
and
shared
infrastructure,
so
that's
a
very
deliberate
decision
that
has
an
enormous
impact
on
your
ability
to
move
forward
at
cisco.
You
know
I
had
the
wind
at
my
back.
S
I
had
cisco
had
a
very
strong
inherent
business
reason
for
pursuing
the
way
they
did,
but
you
know
finance
retail
health
insurance
marketing
manufacturing.
They
don't
have
that
same
driver.
So
you
know
the
ability
to
get
all
these
teams
to
go
once
may
not
be
as
easy
as
it.
Well
wasn't
it.
It
wasn't
easy,
but
but
it
may
not
have
the
same
impetus
that
we
had
at
cisco
next
slide.
S
So
the
technology
recommendations,
one
of
the
few
of
the
things
that
made
us
successful,
is
that
I
got
the
all
the
teams
together
and
that
would
be
external
and
internal.
So
I
I
was
able
to
gather
the
our
cloud
providers
and
all
the
key
architects
on
the
applications
and
the
infrastructure
side,
and
we
we
traced
the
ip
address
from
this
point
of
origination
to
the
next
hop.
Where
did
it
go?
What
happened
to
it?
Where
did
it
go
from
there?
S
What
happened
to
we
walked
and
we
walked
that
through
all
the
way
through
the
systems,
and
we
were
able
to
really
reduce
our
risk
by
following
that
process.
Again,
global
configurations
are
really
going
to
be
important
again.
Do
you
bifurcate
them
and
and
meet,
and
have
your
configurations
like
your
traffic
profiles,
meet
be
specific
to
a
team?
S
You
have
to
come
up
with
a
transition
mechanism
to
make
that
happen,
and
then
we
didn't
go
over
the
teams,
but
another
got.
You
was
security
parity
with
the
floor
and
those
offshore
offices.
You
can't
always
control
what
they
what
happens
in
offices.
You
don't
control,
obviously,
and
so
applications
teams
are
constantly
rolling
on
and
off
projects.
They're
much
more
dynamic.
In
my
experience
than
infrastructure
teams
are
so
that
makes
it
a
lot
busier
and
having
to
meet
that
the
requirements
for
those
teams.
S
Teams
who
are
looking
for
consistent
results
before
they
sign
off
on
something
when
they're
doing
their
release
window
and
the
behavior
expected
behavior
of
happy
eyeballs
occurs
that
can
take,
make
them
see
a
little
nervous,
and
so
I
these
are
not.
They
may
not
get
consistent
results
with
v6.
So
I
had
the
good
fortune
of
having
andrew
yurichenko
on
my
release
window,
but
you
know
not.
Everyone
has
that
benefit.
S
We
can't
do
everything
but
having
some
high
level
recommendations
on
where
those
points
of
integration
are
and
how
do
you
go
about
managing
the
global
configuration
so
that
you
can
be
more
incremental
in
your
transition,
the
key
applications-
I
I
anyone
who's
talked
to
me
from
any
you
know
in
30
seconds
on
this
knows
that
I
I'm
very
strong
about
getting
non-hight
decision
makers
involved
in
this
process
because
of
budget.
I
think
we're
at
a
point
where
we
need
them
to
partner
with
us
in
order
to
move
this
forward.
A
So
I
have
a
question
from
your
leading
of
you
know:
six
codes
from
ipv4,
auto
ipv6
corporate
network
as
the
program
manager.
What
do
you
feel
is
the
the
most
challenging
thing?
What
you
have
some
some
kind
of
like
lessons,
or
you
know
insight
that
you
want
other
enterprise
to
to
do.
For
example,
do
you
feel
that
you
know
the
the
difficulty
is
just
get
started
once
you
get
started,
you
will
always
reach
that
or
you
know
before
you
start.
A
S
At
this
point,
I
I
think
that
it's
important
to
get
those
other
teams
that
may
not
be
so
involved
in
your
v6
transition.
I
mean
we
really
need
to
move
this
forward.
So
in
terms
of
enterprise
yeah,
I
think
one
of
the
key
reasons
we
were
successful
at
cisco
was
they
had
already
have
a
process
called
primes,
and
so
they
had
already
identified.
S
They
already
had
working
relationships
with
the
prime
contacts
in
those
key
business
areas,
so
that
really
helped
in
that
you
know
when
we
built
our
communication
strategies
when
we
had
our
our
communications
announcements,
it
was
really
a
lot
easier.
Knowing
that
we
had
the
support
of
those
key
contacts
in
those
areas,
that
would
have
been
much
more
difficult
to
get
and
they
were
key
in
getting
the
69
sign-offs.
It
wasn't
me
getting
all
of
them.
It
was
partnering
with
those
those
those
other
teams
and
getting
that
done.
D
T
T
A
very
brief
introduction
on
the
company
alibaba
is
famous
for
its
ecommerce
application
like
tomorrow
and
tmo.
It
also
has
applications
for
entertainment,
travel,
messaging
and
working
platform
tools
like
maps,
it's
a
more
than
one
billion
users
in
china
and
three
305
million
international
users
out
of
china.
T
In
addition,
alibaba
also
served
as
a
cloud
infrastructure,
including
idc,
covering
28
regions
with
85,
available
zones
globally
and
provide
city
and
services.
These
services
and
cloud
services,
large
and
small
businesses
develop
their
services
and
build
its
own
application
based
on
cloud
platform.
Next
slides.
T
First,
I
would
like
to
briefly
introduce
the
timeline
the
faces
of
ipv6
options
in
alibaba.
The
first
phase
I
referred
as
to
research
and
preparing
faces
during
the
2012
and
2017
people
do
evaluation,
experiments
and
small
iq
six
trial
projects
inside
this
company
people
think
ip6
is
good,
but
not
ready
for
commercial
and
production
of
network.
So
during
the
period
between
2018
and
2019,
alibaba
started
the
ipv6
program
to
enable
its
co-application
and
infrastructure
to
support
ipv6
carefully
for
each
step,
the
ipv6
active
users
start
growing.
T
I
call
this
space
as
to
small
scale,
ipv6
commercial
adoption
for
the
past
two
years
after
I
joined
this
team,
people
have
confidence
and
started
to
enable
a
larger
scope
of
to
enable
large
scope
of
apps
regions
and
cloud
platforms
based
on
the
experience
gained
in
early
phases.
The
number
of
ipv6
users
are
sorry,
and
if
you
seek
traffic,
the
ratio
increases
as
well.
You
may
notice
the
figures
in
the
in
the
slides.
T
T
T
There
are
a
team
of
inside
of
our
campaign.
I
focus
on
that
software
defined
network
based
on
srv6
towards
a
fine-grained
network
services
for
application.
As
to
the
general
challenges
for
online
services,
the
stability,
accessibility
and
risk
issues
is
a
matter
of
primary
importance
for
large
scale.
Online
services
and
the
language
infrastructure
must
support
new
services.
T
We
cannot
stop
and
wait
for
ipv6
adoption,
and
should
it
introduce
complexities,
risk
and
additional
works
for
us
when
alibaba
started
its
ipv6
commercial
adoption
in
in
2000
in
2008
early
year,
early
2008,
the
end-to-end
network
is
not
ready
for
ipv6
commercial.
You
use
compared
to
ipv4,
so
it
also
adds
some
challenges.
T
In
addition,
it's
not
easy
to
coordinate
to
10
20
different
business
units
and
more
than
500
engineers
work
for
for
one
project.
So
in
the
following
slides,
I
will
focus
on
some
technical
considerations
for
engineers,
the
first,
the
first
and
the
primary
technic
challenge
is
how
to
migrate
online
services
smoothly
without
interference
of
users
and
opera
applications.
T
The
second
second
one,
a
sub
sub
challenge
is
how
to
measure
the
quality
of
ipv6
network
and
adobe
adopting
new
stack
environment,
and
I
will
also
talk
about
the
small
technical
considerations
regarding
the
ipv6
mtu
next
slides,
please
to
better
understand
how
to
enable
ipv6
for
online
services.
In
this
page,
there
is
a
very
high
level
online
services
architecture.
T
You
can
see
there
too.
There
are
three
parts:
one
is
the
user
side,
application
of
browser
es
and
isp
network.
They
are
supposed
to
support
ipv6.
In
the
first
place
extensive
airflow
has
been
taken
taken
on
taken
in
in
in
the
alibaba
team
to
enable
apps
to
adapt
to
that
new
stack.
I
will
talk
about
it
later.
The
second
part
is
the
access
point
of
application,
which
receive
ipv6
connections
from
users,
go
through
security
checks
and
deliver
it
to
the
best
application
servers
which
handle
the
connections.
T
It
should
be
upgraded
to
provide
public
facing
services,
and
we
also
have
third
party
is
the
cloud
services
for
cloud.
Vpc
users
there
are
inner
facing
services.
Some
people
hope
that
ipv6
only
induction
in
interface
facing
services
will
release
the
scratch
of
ipsec
for
private
address
use,
but
it's
not
highly
priority
right
now.
T
The
first
one
is
the
proxy
solutions.
In
alibaba
cloud,
we
adopt
some
solutions
like
the
global
accelerators,
which
enable
the
ipv6
capabilities
for
public
efficient
access.
No
change
are
required
for
the
legacy
infrastructure
for
users
who
already
deploy
their
services
on
the
cloud.
They
can
choose
the
load,
balance
of
four
to
or
six
to
four
or
dual
stack
or
six
to
six
load
balance.
Just
as
alibaba
apps
do
now.
Edible
cloud
has
full
capabilities
of
new
stack
generally.
The
idea
is
to
we.
T
T
Okay,
let's
focus
on
the
major
technic
challenge
I
proposed
in
previous
slides
how
to
migrate
online
services
smoothly.
Firstly,
we
should
understand
the
quality
of
ipv6
network.
Now,
nowadays
we
have
in
alibaba
we
have
application
performance
management
platform
looking
to
the
status
of
ipv6
network
performance.
T
T
Today,
the
coverage
of
ip6
is
also
a
very
important
matrix
in
the
early
of
in
the
early
in
the
early
months
of
this
year.
It's
around
this
90
percent
and
almost
widely
deployed
in
the
mobile
lte
network.
The
coverage
is
very
narrow
in
wi-fi
access
network.
We
also
notice
that
in
the
dual
stack
wi-fi
network,
many
users
may
experience
phoenix
due
to
the
broken
wi-fi,
routers
or
routing
settings.
There
are
many
failure
cases
we
connect
next
slides.
T
Firstly,
we
we
do
measurement
to
pre,
detect
the
quality
of
fp6
network,
as
I
introduced
previously,
and
the
second
one
is
the
push
configurations
and
content
to
specific
use
groups
based
on
different
factors
like
geolocation,
the
the
annual
ios
platform
or
isp
networks,
the
third
and
improved
I
happy
eyeballs
implementation
adopted
using.
We
combine
the
dns
response
with
a
quarter
a
and
a.
T
Slides
to
increase
ipv6
ratio
for
for
the
apps,
for
example,
the
table
app.
For
example,
we
make
a
list
of
domain
to
be
ipv6
enabled
there
are
more
than
500
domains
in
taobao,
for
example,
are
priorities
set
to
first
to
enable
the
cdn
domains
and
domains
related
to
resource
on
the
first
page,
for
example,
the
apps
also
pre-pool
ipv6
address
of
domains
if
they
can
use
ipv6,
it
works
well
to
mention
the
behavior
of
apps
in
the
dstack
environment,
when
the
ipv6
is
allowed
to
use
in
the
early
phase
of
ipv6
adoption.
T
30
minutes
penalty
was
set
for
each
ipv6
phoenix
because
at
that
time
the
early
phase,
the
the
net
that
the
quality
of
ipv6
network
is
poor.
In
order
to
increase
the
the
traffic
ratio
of
ip6,
we
we
tried
the
the
app
tried,
the
ipv6
first
and
fore
back
to
ipv4.
You
finished
it
works
good
for
mobile
network,
but
for
back
recently
in
broken
wi-fi
situations.
T
T
Okay,
there
is
one
issue
that
we
are
talking
recently
regards
to
the
ipv6
mtu.
We
all
know
that
ipv6
parkit
is
prone
to
be
dropped
due
to
the
meter
box,
like
fireworks
and
nets,
etc.
To
avoid
finish
caused
by
pv6
package
job
years
ago,
my
colleagues
choose
a
very
product
value
for
the
ipv6
mtu
and
tcpmss,
as
we
show
in
the
slides
which
decrease
the
transmission
efficiency
compared
with
ipv4,
and
now
we
are
going
to
test
and
implement
larger
ipv6
mtu
and
tcp
mss
in
cydia
environment
next
slides.
T
T
In
the
wi-fi
network,
v6
traffic
increase
from
the
authority
data
are
more
than
14
in
lte
network
and
10
percent.
In
the
main
network,
the
ipv6
performance
is
almost
close
to
ipv6
before
and
better
than
ipv4.
In
some
cases
we
do
we
did
some
tests
on
inside
alibaba
and
we
found
that
this
stack
is
proved
to
be
the
best
approach
of
adopting
ipv6
adopting
fpv6.
Yes,
there
are
also
some
better
aspects.
T
T
T
Next
slide:
yeah.
Okay,
as
a
conclusion,
I
think
ip6
is
fully
mature
and
alibaba's
in
upgraded
in
infrastructure
and
application
in
less
than
five
years,
and
now
enable
1
billion
and
96
users
globally.
We
notice
that
stability
and
risk
control
are
crucial.
Considerations
for
online
scale
large-scale
online
services.
T
However,
I
put
a
lot
of
effort
to
ensure
the
smooth
transition
and
the
farmer
paths
to
deploy
at
v6
in
last
year,
k5p6
in
considerations
in
the
first
place,
because
upgrading
language
infrastructure
is
very
hard
and
hurts
a
lot,
it's
much
more
complicated
than
a
new
one.
So
in
alberta,
cloud
new
products
and
new
version
products
are
now
required
to
support
ipv6
capability
as
a
waiter.
T
So
the
next
conclusion
is
that
the
two
stack
is
the
only
approach.
We
proved
that,
however,
I
think
from
pleasant
view.
The
ipv6
community
should
consider
a
calm
down
timer
for
ipv4,
because
they're
obvious
obvious
that
ipv4
and
v6
are
competing
in
some
use.
In
some
cases,
the
users
have
the
presentations
to
adopt
ipv6
if
ipv4
is
still
available.
So
that's
the
my
observations.
O
T
C
T
C
T
T
T
T
That's
how
how
we
we're
looking
forward
that
the
more
traffic
can
migrate
to
ipv6,
then
we
can
do
the
scheduling
for
each
applications.
Yeah!
That's
why
we
that
that
the
current
talking
right
now
is
to
increase
traffic,
if
that,
if,
though,
if
there
is
no
trafficking
in
the
network,
how
you
there's
no
requirement
no
urgent
requirement
to
use
that
capability.
R
D
R
Okay,
I
have
one
question
about
activities
only
for
cloud
data
centers.
You
have
mentioned
that
activities
only
will
be
the
ultimate
stage
of
cloud
platform
and
cloud
service
right.
You
know
that
graphic
center
hosts
a
vm
or
vpcs
for
customers
right.
So
my
question
is
your
definition.
Activation
only
is
based
on
the
assumption
that
the
vpc
will
be
applicable
only
or
do
stack
if,
if
the
vpc
can
reduce
that
how
to
support
the
dual
stack
of
vpc
in
applications,
only
a
cloud
large
softbox,
okay,.
T
T
U
I
have
seen
netflix
translation
from
six
to
four,
but
I
I
have
not
six
have
not
seen
the
plan
in
opposite
direction
from
four
to
six,
because
in
the
future
definitely
you
will
have
a
small
number
of
users
which
would
be
ipv4
only
and
you
will
have
ipv6
only
applications.
Do
you
have
a
plan
for
load,
balancer
or
network
translation
or
something
to
translate
from
four
to
six.
