26 Dec 2020
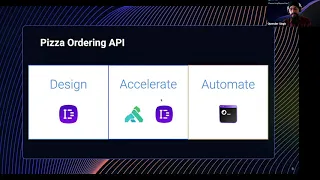
All organizations want software development to improve quality and velocity. Optimizing the development workflow around APIs has proven an important part of achieving these outcomes. Organizations that shift from ad hoc API development to spec-based API development based on standards such as OpenAPI and GraphQL are leading the way. In this session, Kong engineers will share how Kong can help.
You will learn how to:
- Enable API implementers to quickly build quality interfaces and make them available for reuse
- Enable API consumers to easily make use of interfaces available to them for their development needs
- Gain the most value from the Kong portfolio of products, including - Insomnia Core and Insomnia Designer, Kong Gateway, Kong Vitals, and Kong Developer Portal
You will learn how to:
- Enable API implementers to quickly build quality interfaces and make them available for reuse
- Enable API consumers to easily make use of interfaces available to them for their development needs
- Gain the most value from the Kong portfolio of products, including - Insomnia Core and Insomnia Designer, Kong Gateway, Kong Vitals, and Kong Developer Portal
- 2 participants
- 21 minutes
24 Dec 2020
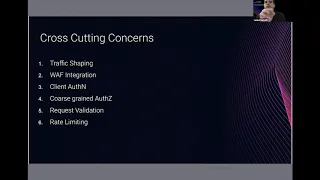
In this Kong Summit 2020 session, we will cover the architecture and approach we used to build out our digital platform at Goldman Sachs by leveraging Kong’s API gateway to implement a secure ingress controller for all digital channels, including private/public API and web interfaces. We will discuss how we integrated Kong’s API gateway with AWS native services to implement mTLS, observability and container runtime, as well as share our operational experience of running resilient API workloads in production.
- 1 participant
- 21 minutes
23 Dec 2020
This Kong Summit 2020 session focuses on the war stories, and subsequently the patterns HyperCurrent employed, from building an API chargeback/monetization product using OAS, Kotlin, Spring Boot and Kong. We will discuss how a programmatic approach can be used to deliver an elegant REST-ful API while enforcing an anti-corruption layer for domain logic without writing API contracts by hand. By using Kotlin and Spring Boot along with a controller/DTO approach, we can automatically produce an OAS contract, HTML docs, a console and a client side SDK.
- 1 participant
- 28 minutes

22 Dec 2020
Insomnia Designer is a collaborative API design tool for designing and managing OpenAPI specs. This session will cover how to design and test APIs, as well as how to extend Insomnia with custom plugins. Kong Champion Mert Simsek will dive into how as a team is leveraging Insomnia Designer to share information and data APIs across teams to improve their overall process.
- 1 participant
- 16 minutes

22 Dec 2020
Comcast has taken a journey to develop an API gateway initially using open source software and in-house enhancements, and later transitioning to open core commercial software to improve the overall service delivery experience for developers. In this session, Comcast will discuss enhancements that the team made to adapt the community edition of Kong, and subsequently the enterprise edition, to support a self-service, multi-tenant, yet still managed, production API gateway solution, as well as open source contributions made to the Kong community along the way.
- 2 participants
- 23 minutes
21 Dec 2020
In this session, we will explain the various communication design patterns for microservices running at scale, including:
- Brief introduction to microservices
- Microservice design patterns
- Communication patterns between microservices using service mesh and API gateways
- Running microservices on the cloud (multi-cloud and hybrid cloud)
- Scaling microservices
- Brief introduction to microservices
- Microservice design patterns
- Communication patterns between microservices using service mesh and API gateways
- Running microservices on the cloud (multi-cloud and hybrid cloud)
- Scaling microservices
- 4 participants
- 26 minutes

20 Dec 2020
The Department for Work and Pensions (DWP) is the UK’s biggest public service department, administering the State Pension and a range of working age, disability and ill health benefits to around 20 million claimants and customers. When COVID-19 hit, we urgently had to enable scalable data access and process automation to meet an unprecedented demand for our services as our citizens became increasingly dependent on us during the lockdown.
In this session, we’ll talk about the key role our APIs play in meeting this demand and supporting remote working across the UK. We’ll also show how APIs and events are driving the next phase of our ongoing transformation to break down silos and deliver a much more holistic service to the citizen whilst maximizing re-use of technical products across DWP.
In this session, we’ll talk about the key role our APIs play in meeting this demand and supporting remote working across the UK. We’ll also show how APIs and events are driving the next phase of our ongoing transformation to break down silos and deliver a much more holistic service to the citizen whilst maximizing re-use of technical products across DWP.
- 2 participants
- 27 minutes

19 Dec 2020
SaaS cloud deployments are highly distributed with workflows that stitch them together to deliver differentiated services at scale and on-demand. When regulated verticals like finance customers use such deployments, the requirements around security, compliance and visibility, access control, tenant-separation with authentication/authorization, rate-limiting, ability to connect to federated identity solutions — and above all — resilience, availability and DR become critical to such deployment topology. As Symphony delivers secure collaboration solutions for FinTech with its distributed cloud stack, we will discuss how Kong played an important role as an API gateway in achieving the specific requirements above and share a customer perspective of Kong.
- 2 participants
- 19 minutes

18 Dec 2020
During the early days of finding product-market fit, clouds were small. Often, we start with an EC2 instance here, a managed service there, then some Docker containers, microservices, and wait, Kubernetes! As clouds grow with the teams that maintain them, stable relics and legacy systems remain in production. The effort first goes towards building the future and satisfying clients — they’re paying!
At FinTech Studios, we are reconciling with these old burdens. As we continue to embrace our Kubernetes overlords, we must connect and secure the past and present without sacrificing the future, such as on-prem deployments, hybrid clouds, and traffic tracing and permissioning. Kuma, the now CNCF Sandbox service mesh born at Kong, allows us to make these gaps observable, use automated deployment practices like CD and Helm, and most importantly, integrate at our own pace.
As Kuma users, we will dive into deployment patterns with Kuma via Helm; some of its features like sidecar proxies, mTLS, mixed K8s and VM deployments; service observability; and the community support that makes it all possible. Kuma provides an easy on-ramp Day 1 while planning for Day 2, bringing business value at each step.
At FinTech Studios, we are reconciling with these old burdens. As we continue to embrace our Kubernetes overlords, we must connect and secure the past and present without sacrificing the future, such as on-prem deployments, hybrid clouds, and traffic tracing and permissioning. Kuma, the now CNCF Sandbox service mesh born at Kong, allows us to make these gaps observable, use automated deployment practices like CD and Helm, and most importantly, integrate at our own pace.
As Kuma users, we will dive into deployment patterns with Kuma via Helm; some of its features like sidecar proxies, mTLS, mixed K8s and VM deployments; service observability; and the community support that makes it all possible. Kuma provides an easy on-ramp Day 1 while planning for Day 2, bringing business value at each step.
- 1 participant
- 20 minutes

17 Dec 2020
Continuing on the journey of building a new API platform, NAB’s primary focus this year has been improving API quality by building tooling for API design and API governance. This Kong Summit 2020 session will cover NAB’s new API search capability, which allows quick API discovery across the organization, and how the team implemented decentralized API governance.
- 2 participants
- 22 minutes

15 Dec 2020
Organizations are moving from centralized data centers to distributed cloud native platforms. Due to the complexity of such a migration, an organization would be running a hybrid multi-platform environment which spans from the old to the new world. It starts at the edge of a system, using functionality provided by an API gateway or platform. In this session, Daniel Kocot will discuss:
- Strategies for application modernization
- Best practices for happy path migration
- How an API platform can become part of the migration process
- Strategies for application modernization
- Best practices for happy path migration
- How an API platform can become part of the migration process
- 1 participant
- 25 minutes

14 Dec 2020
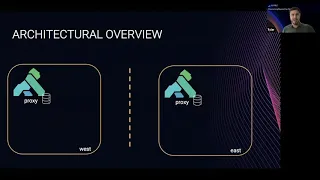
Are you an enterprise architect who is currently facing the challenge to secure and observe service connectivity across every cloud and every cluster, including hybrid Kubernetes and VM environments?
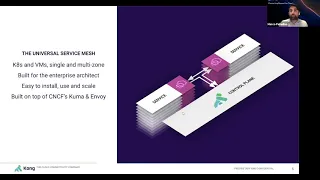
Kong Mesh, built on top of CNCF’s Kuma and Envoy, is a universal service mesh delivering simplicity and scalability to every application. Join us as Kong’s CTO Marco Palladino shares how Kong Mesh enables you to:
Deploy Kong Mesh in a multi-zone environment spanning across multiple clusters and regions
Enable zero-trust security on a multi-zone Kong Mesh deployment to secure cross-cluster and cross-cloud connectivity
Discover and route traffic from one zone to another, including “one click” cluster/region shifting by using the “Traffic Route” policy
Kong Mesh, built on top of CNCF’s Kuma and Envoy, is a universal service mesh delivering simplicity and scalability to every application. Join us as Kong’s CTO Marco Palladino shares how Kong Mesh enables you to:
Deploy Kong Mesh in a multi-zone environment spanning across multiple clusters and regions
Enable zero-trust security on a multi-zone Kong Mesh deployment to secure cross-cluster and cross-cloud connectivity
Discover and route traffic from one zone to another, including “one click” cluster/region shifting by using the “Traffic Route” policy
- 1 participant
- 54 minutes
13 Dec 2020
When building and growing an engineering culture, capabilities such as an API gateway sound like an easy win. However, the continued push for self-service and automation is always in contention with the need for governance — visibility often conflicts with security. Join Cargill’s Colin Schaub as he discusses the growth, evolution and foibles of Cargill’s API platform using the Kong API gateway and developer portal while on the journey towards building a foundational engineering culture at Cargill.
- 1 participant
- 23 minutes

12 Dec 2020
Learn how to:
- Deliver turnkey API Management and Service Mesh across all your clouds
- Manage services natively in Kubernetes and run across any protocol and architecture
- Manage all your services end-to-end from design to production, using declarative configuration for DevOps automation
- Integrate Kong Mesh into the Kong Enterprise platform to enable ingress and egress traffic for your service mesh
- Deliver turnkey API Management and Service Mesh across all your clouds
- Manage services natively in Kubernetes and run across any protocol and architecture
- Manage all your services end-to-end from design to production, using declarative configuration for DevOps automation
- Integrate Kong Mesh into the Kong Enterprise platform to enable ingress and egress traffic for your service mesh
- 2 participants
- 27 minutes
11 Dec 2020
Organizations that embrace GitOps are able to develop and automate their end-to-end software development lifecycle by combining the power of Git, CI/CD and Kubernetes. However the path to get there can be rocky: operating in a multi-cloud environment, working with hybrid microservice and monolith APIs, helping teams discover and publish APIs to use, and moving legacy services to Kubernetes pose no shortage of organizational and technical challenges.
In this session, we’ll share insights that we’ve learned from some of our most successful users on how to break these challenges down into bite-sized pieces and build a plan of attack no matter what stage you’re currently in.
You will learn how to:
- Improve the compliance and functionality of your APIs in the API gateway
- Deploy across diverse architectures and environments, including cross-cloud and Kubernetes
- Publish APIs to portals and service registries for other developers to discover and use
In this session, we’ll share insights that we’ve learned from some of our most successful users on how to break these challenges down into bite-sized pieces and build a plan of attack no matter what stage you’re currently in.
You will learn how to:
- Improve the compliance and functionality of your APIs in the API gateway
- Deploy across diverse architectures and environments, including cross-cloud and Kubernetes
- Publish APIs to portals and service registries for other developers to discover and use
- 2 participants
- 26 minutes

10 Dec 2020
iFood is the largest food delivery app company in Brazil and is using Kong to deal with all incoming traffic of its microservices. All of the workload creates a perfect yet challenging environment for SRE work, including developing automation, monitoring the system and helping improve resilience. In this session, we will show the environment and techniques we used to improve iFood stability.
- 2 participants
- 34 minutes

9 Dec 2020
With the universal adoption of Kubernetes across cloud and data center platforms, organizations now enjoy a level of consistency across heterogenous infrastructure like never before. This opens up interesting challenges and opportunities for application deployment and IT operations. In this talk, we will discuss how organizations deploy Kubernetes across cloud, data center, branch offices and the edge. We will also cover how organizations can build a universal computing platform across multiple Kubernetes clusters running on heterogenous infrastructure. As a result, they get unprecedent application portability, deployment agility, security and control.
- 1 participant
- 24 minutes

8 Dec 2020
To keep pace with the company’s rapidly growing menu innovation strategy and expansion to digital channels, elevating the API strategy became a priority at Papa John’s. Learn how the team reduced time to market and enabled API innovation with the growing list of external channels. This session will discuss deploying Kong in a hybrid environment, making use of the Kong Developer Portal and integrating to a CI/CD pipeline to automate deployments.
Learn more about Kong: https://bit.ly/2I2DypS
Learn more about Kong: https://bit.ly/2I2DypS
- 1 participant
- 17 minutes

8 Dec 2020
Join Kong CTO Marco Palladino as he shows Kong VP of Marketing Sandeep Singh Kohli how to make Carbonara just like they do it in Rome. Growing up in Milan, Italy, he learned the basics of great Italian cooking from his grandparents at a young age. Since then, Marco has perfected the craft and will reveal some family recipe secrets during this cooking class. Some say five-star Italian food provides the fuel to create the world’s most reliable service connectivity platform.
Learn more about Kong: https://bit.ly/2I2DypS
Learn more about Kong: https://bit.ly/2I2DypS
- 2 participants
- 40 minutes

7 Dec 2020
Learn more about Kong Mesh: https://bit.ly/37fudp3
Are you an enterprise architect who is currently facing the challenge to secure and observe service connectivity across every cloud and every cluster? Kong Mesh, built on top of CNCF’s Kuma and Envoy, is a universal service mesh tailored to the enterprise architect that must provide modern and secure connectivity to the applications that the teams are building.
Join Kong Mesh Engineer and Kuma Contributor Jakub Dyszkiewicz to learn how Kong Mesh can help you:
Apply a zero-trust security model out of the box to encrypt traffic and reduce the risk of breaches, including mTLS and traffic permissions ACL to secure traffic paths from one service to another
Assign an identity to every service and workload that runs in the mesh by automatically issuing and rotating mTLS certificates, thanks to Kong Mesh built-in capabilities
Capture and observe all the logs, metrics and traces that service traffic is generating in order to identify problems faster, as well as knowing the state of the service mesh in real time
Are you an enterprise architect who is currently facing the challenge to secure and observe service connectivity across every cloud and every cluster? Kong Mesh, built on top of CNCF’s Kuma and Envoy, is a universal service mesh tailored to the enterprise architect that must provide modern and secure connectivity to the applications that the teams are building.
Join Kong Mesh Engineer and Kuma Contributor Jakub Dyszkiewicz to learn how Kong Mesh can help you:
Apply a zero-trust security model out of the box to encrypt traffic and reduce the risk of breaches, including mTLS and traffic permissions ACL to secure traffic paths from one service to another
Assign an identity to every service and workload that runs in the mesh by automatically issuing and rotating mTLS certificates, thanks to Kong Mesh built-in capabilities
Capture and observe all the logs, metrics and traces that service traffic is generating in order to identify problems faster, as well as knowing the state of the service mesh in real time
- 1 participant
- 25 minutes

5 Dec 2020
Learn more about Kong: https://bit.ly/2I2DypS
Declarative configuration management allows organizations to scale efficiently, but it is not a silver bullet. At Checkr, we faced additional scenarios, where declarative configuration is not suitable by design. In this talk, Checkr Staff Software Engineer Ivan Rylach will look into these cases and walk through the architecture that addresses them.
Declarative configuration management allows organizations to scale efficiently, but it is not a silver bullet. At Checkr, we faced additional scenarios, where declarative configuration is not suitable by design. In this talk, Checkr Staff Software Engineer Ivan Rylach will look into these cases and walk through the architecture that addresses them.
- 1 participant
- 12 minutes

4 Dec 2020
You want to migrate your existing application to serverless — and you don’t know where to start. This is a common problem that a lot of architects, CTOs and developers have, as it is very rare that we start as a greenfield project.
In this talk, I will cover some introductory concepts for serverless and walk you through different strategies for migrating an existing application to serverless. We will look at known architectures, existing challenges in our applications and how we can overcome them with serverless. I will also share lessons learned from working on the migration of one existing microservices application into serverless.
Learn more about Kong: https://bit.ly/2I2DypS
In this talk, I will cover some introductory concepts for serverless and walk you through different strategies for migrating an existing application to serverless. We will look at known architectures, existing challenges in our applications and how we can overcome them with serverless. I will also share lessons learned from working on the migration of one existing microservices application into serverless.
Learn more about Kong: https://bit.ly/2I2DypS
- 1 participant
- 23 minutes

3 Dec 2020
In this fireside chat, industry leaders with experience driving revolutions in software development and infrastructure will discuss transitions to microservices, Kubernetes, cloud native and open source across industries. The panel will also discuss how requirements have changed, and what paths these technologies and architectures could take in the future.
Learn more about Kong: https://bit.ly/2I2DypS
Learn more about Kong: https://bit.ly/2I2DypS
- 3 participants
- 33 minutes

2 Dec 2020
Learn more about Kong: https://bit.ly/2I2DypS
SIGHUP provides enterprise-grade cloud native infrastructure automation for Kubernetes and cloud native stacks. In this session, we’ll dive into how we leverage Kong for Kubernetes including:
1) Our opinionated reference architecture on VM
2) Configurations (healthchecks, Prometheus integration)
3) Installing and managing a Cassandra cluster
4) IaC with decK in Enterprise (hello RBAC users)
5) Easy developer portal with “portal” (Why didn’t you tell us?)
6) We got you covered with serverless (Lua will be always your friend)
7) Why we love Kong for Kubernetes
SIGHUP provides enterprise-grade cloud native infrastructure automation for Kubernetes and cloud native stacks. In this session, we’ll dive into how we leverage Kong for Kubernetes including:
1) Our opinionated reference architecture on VM
2) Configurations (healthchecks, Prometheus integration)
3) Installing and managing a Cassandra cluster
4) IaC with decK in Enterprise (hello RBAC users)
5) Easy developer portal with “portal” (Why didn’t you tell us?)
6) We got you covered with serverless (Lua will be always your friend)
7) Why we love Kong for Kubernetes
- 2 participants
- 17 minutes

1 Dec 2020
Learn more about Kong: https://bit.ly/2I2DypS
Applications architected as microservices are becoming more prevalent every day, but just like their monolithic ancestors, microservice applications must adhere to organization-wide constraints around compliance, security, performance, etc. Authorization — controlling which people and machines can perform which actions — is a foundational security problem that requires new solutions in a microservice world because of changes in requirements around performance, availability and even where authorization gets enforced architecturally.
This talk discusses these new requirements, architectural choices for how to satisfy them and modern technologies for rolling them out. We describe taking a policy-as-code approach, where authorization policies are decoupled from the underlying microservices yet employ a shared-fate evaluation model so that policies are consistent, enforced consistently, meet high-availability and performance demands, and enable relatively rapid security reviews and hot-patching. Specifically, we describe how to employ the Open Policy Agent for a unified approach to policy-as-code, where policies are enforced through the Kuma service mesh.
Applications architected as microservices are becoming more prevalent every day, but just like their monolithic ancestors, microservice applications must adhere to organization-wide constraints around compliance, security, performance, etc. Authorization — controlling which people and machines can perform which actions — is a foundational security problem that requires new solutions in a microservice world because of changes in requirements around performance, availability and even where authorization gets enforced architecturally.
This talk discusses these new requirements, architectural choices for how to satisfy them and modern technologies for rolling them out. We describe taking a policy-as-code approach, where authorization policies are decoupled from the underlying microservices yet employ a shared-fate evaluation model so that policies are consistent, enforced consistently, meet high-availability and performance demands, and enable relatively rapid security reviews and hot-patching. Specifically, we describe how to employ the Open Policy Agent for a unified approach to policy-as-code, where policies are enforced through the Kuma service mesh.
- 3 participants
- 26 minutes

30 Nov 2020
Learn more about Kong: https://bit.ly/2I2DypS
Slack is a natural gateway to API transformation because it solves the inherited complexity of enterprises fast-changing their work and communication methodologies. The challenge is to accelerate and democratize access to microservices, enabling an ecosystem based on cross-pollination, distribution and transparency while avoiding duplication of effort. Efficient collaboration and communication are the core of this process. The developer community needs a tool which allows them to operate these workflows while simplifying access to traditionally complex processes. Slack has then become the saving grace for many development teams in a remote-first world.
In this Kong Summit 2020 talk, the audience learned:
- How to set up Ops to seamlessly integrate with Slack
- How to create an API based on a pre-defined template within Slack
- How easy an API registration in Kong can be done via Slack
- How to bring command, pipeline and services together seamlessly
- Allow for transparent and analytic feedback loops within Slack
- How to discover APIs in an easy and immediate way
Slack is a natural gateway to API transformation because it solves the inherited complexity of enterprises fast-changing their work and communication methodologies. The challenge is to accelerate and democratize access to microservices, enabling an ecosystem based on cross-pollination, distribution and transparency while avoiding duplication of effort. Efficient collaboration and communication are the core of this process. The developer community needs a tool which allows them to operate these workflows while simplifying access to traditionally complex processes. Slack has then become the saving grace for many development teams in a remote-first world.
In this Kong Summit 2020 talk, the audience learned:
- How to set up Ops to seamlessly integrate with Slack
- How to create an API based on a pre-defined template within Slack
- How easy an API registration in Kong can be done via Slack
- How to bring command, pipeline and services together seamlessly
- Allow for transparent and analytic feedback loops within Slack
- How to discover APIs in an easy and immediate way
- 1 participant
- 27 minutes

29 Nov 2020
Learn more about Kong: https://bit.ly/2I2DypS
Building a thriving API ecosystem is more than offering a stable and performant gateway solution; it’s about the people, processes and practices which contribute to long-term success. Since Kong Summit 2019, our experiment in open source has grown to support over 90% of UnitedHealth Group’s RESTful traffic. The path to success within this Fortune 10 healthcare giant has been paved with intriguing challenges, unexpected hazards and valuable lessons. Watch this Kong Summit 2020 session to learn our roadmap for how to build a thriving API ecosystem, engineered for long term success, with Kong at its core.
Building a thriving API ecosystem is more than offering a stable and performant gateway solution; it’s about the people, processes and practices which contribute to long-term success. Since Kong Summit 2019, our experiment in open source has grown to support over 90% of UnitedHealth Group’s RESTful traffic. The path to success within this Fortune 10 healthcare giant has been paved with intriguing challenges, unexpected hazards and valuable lessons. Watch this Kong Summit 2020 session to learn our roadmap for how to build a thriving API ecosystem, engineered for long term success, with Kong at its core.
- 2 participants
- 30 minutes

28 Nov 2020
Learn more about Kuma: https://kuma.io/
Applications architected as microservices are becoming more prevalent every day, but just like their monolithic ancestors, microservice applications must adhere to organization-wide constraints around compliance, security, performance, etc. Authorization, controlling which people and machines can perform which actions, is a foundational security problem that requires new solutions in a microservice world because of changes in requirements around performance, availability, and even where authorization gets enforced architecturally.
This talk discusses these new requirements, architectural choices for how to satisfy them, and modern technologies for rolling them out. We describe taking a policy-as-code approach where authorization policies are decoupled from the underlying microservices yet employ a shared-fate evaluation model so that policies are consistent, enforced consistently, meet high-availability and performance demands, and enable relatively rapid security reviews and hot-patching. Specifically, we describe how to employ the Open Policy Agent for a unified approach to policy-as-code where policies are enforced through the Kuma service mesh.
Applications architected as microservices are becoming more prevalent every day, but just like their monolithic ancestors, microservice applications must adhere to organization-wide constraints around compliance, security, performance, etc. Authorization, controlling which people and machines can perform which actions, is a foundational security problem that requires new solutions in a microservice world because of changes in requirements around performance, availability, and even where authorization gets enforced architecturally.
This talk discusses these new requirements, architectural choices for how to satisfy them, and modern technologies for rolling them out. We describe taking a policy-as-code approach where authorization policies are decoupled from the underlying microservices yet employ a shared-fate evaluation model so that policies are consistent, enforced consistently, meet high-availability and performance demands, and enable relatively rapid security reviews and hot-patching. Specifically, we describe how to employ the Open Policy Agent for a unified approach to policy-as-code where policies are enforced through the Kuma service mesh.
- 1 participant
- 33 minutes

27 Nov 2020
Learn more about Kong: https://bit.ly/2I2DypS
COVID-19 has hit our country hard, and the healthcare industry is still reeling from national attention on the blatant disparity of the effects of COVID-19 in specific underserved populations. Recognizing the disparity, healthcare leaders continue to struggle with interoperability and data sharing; we must free the data and move beyond the debate of public or private cloud. It’s time to prepare for the eventuality of leveraging all available cloud environments to handle the data workload and application needs to end digital disparity in healthcare. Join Clearsense CIO Charles Boicey as he explores the requisite architecture to support healthcare from a data platform perspective in a hybrid cloud environment.
COVID-19 has hit our country hard, and the healthcare industry is still reeling from national attention on the blatant disparity of the effects of COVID-19 in specific underserved populations. Recognizing the disparity, healthcare leaders continue to struggle with interoperability and data sharing; we must free the data and move beyond the debate of public or private cloud. It’s time to prepare for the eventuality of leveraging all available cloud environments to handle the data workload and application needs to end digital disparity in healthcare. Join Clearsense CIO Charles Boicey as he explores the requisite architecture to support healthcare from a data platform perspective in a hybrid cloud environment.
- 1 participant
- 32 minutes

25 Nov 2020
Learn more about Kong: https://bit.ly/2I2DypS
While the concept of serverless applications has grown over the past years there are plenty of instances where the serverless model doesn’t fit all needs. For those coming from on-premises or hybrid scenarios, moving to serverless might look like needing to move everything or building very differently than you have in the past. In this Kong Summit 2020 session we’ll demystify the central component of the serverless movement, AWS Lambda, a serverless compute service that changes how applications are built and managed, but only in some ways. We'll cover how you can use your existing Kong infrastructure with AWS Lambda to reduce your operations overhead and gain the benefits Lambda provides of pay for what you use, automatic scaling, and high availability by default. We'll cover some of the ways to troubleshoot Lambda issues and how to measure performance of your applications.
While the concept of serverless applications has grown over the past years there are plenty of instances where the serverless model doesn’t fit all needs. For those coming from on-premises or hybrid scenarios, moving to serverless might look like needing to move everything or building very differently than you have in the past. In this Kong Summit 2020 session we’ll demystify the central component of the serverless movement, AWS Lambda, a serverless compute service that changes how applications are built and managed, but only in some ways. We'll cover how you can use your existing Kong infrastructure with AWS Lambda to reduce your operations overhead and gain the benefits Lambda provides of pay for what you use, automatic scaling, and high availability by default. We'll cover some of the ways to troubleshoot Lambda issues and how to measure performance of your applications.
- 1 participant
- 29 minutes

24 Nov 2020
Learn more about Kong: https://bit.ly/2I2DypS
We all know that we shouldn’t store secrets in mobile apps, but what is the practical alternative? We all know that we should use certificate pinning for our APIs, but how can it be done simply and safely? This Kong Summit 2020 talk will describe a real project to explore some of the challenges of implementing good security practice in a large organization and discuss a third-party solution (Approov) which addresses both of the issues above in a relatively simple way using industry standards and working neatly with Kong.
Approov is an API security solution which attests that API requests have come from genuine mobile app instances, ensuring that bots, scripts and re-packaged apps can’t communicate with backend systems. Further, Approov includes a dynamic pinning capability which makes implementing and managing pinned connected much easier than has previously been possible.
Approov’s Kong plugin enables the benefits of Approov without the need to modify backend systems, blocking all bots and scripts even if they present valid credentials. Join this session to learn how to improve security hygiene significantly with minimal effort.
We all know that we shouldn’t store secrets in mobile apps, but what is the practical alternative? We all know that we should use certificate pinning for our APIs, but how can it be done simply and safely? This Kong Summit 2020 talk will describe a real project to explore some of the challenges of implementing good security practice in a large organization and discuss a third-party solution (Approov) which addresses both of the issues above in a relatively simple way using industry standards and working neatly with Kong.
Approov is an API security solution which attests that API requests have come from genuine mobile app instances, ensuring that bots, scripts and re-packaged apps can’t communicate with backend systems. Further, Approov includes a dynamic pinning capability which makes implementing and managing pinned connected much easier than has previously been possible.
Approov’s Kong plugin enables the benefits of Approov without the need to modify backend systems, blocking all bots and scripts even if they present valid credentials. Join this session to learn how to improve security hygiene significantly with minimal effort.
- 2 participants
- 22 minutes

23 Nov 2020
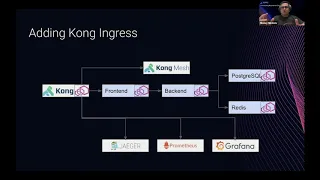
Canary deployment is a helpful tool that allows companies to put in production multiple versions of its products to control flow and access based on different sets of rules, clients, amounts and operations. In this Kong Summit 2020 session, we will discuss best practices for canary deployment and share our experiences using Kong Enterprise — supported by Kuma capabilities — in achieving this.
Learn more about Kong: https://bit.ly/2I2DypS
Learn more about Kong: https://bit.ly/2I2DypS
- 2 participants
- 24 minutes
20 Nov 2020
The team at Tyler Technologies has used Kong to help take the company’s applications from on-premise installations to multi-tenant cloud services. In this Kong Summit 2020 session, we’ll explore how Kong can help make this move without clients ever knowing it even happened, how we use Kong Brain to automatically generate OpenAPI documentation for our integrators and the AWS infrastructure choices we made to get a large, robust Kong instance running in AWS.
Learn more about Kong: https://bit.ly/2I2DypS
Learn more about Kong: https://bit.ly/2I2DypS
- 1 participant
- 23 minutes

19 Nov 2020
Learn more about Kong: https://bit.ly/2I2DypS
For many organizations, moving legacy applications to modern cloud infrastructures holds great promise, such as reducing IT overhead and accelerating development times. However, in reality, these projects can be fraught with delays and service interruptions while burdening your team with transition tasks.
In this Kong Summit 2020 talk, we are covering how to seamlessly connect the old world with the new, as well as how to modernize legacy services to run on a modern cloud native stack. With technologies such as Kong Mesh, a control plane for service mesh built on Kuma, and Weave Kubernetes Platform, teams can progressively move legacy applications to Kubernetes — controlled and securely. Built-in GitOps workflows ensure developer-friendly operations for Kubernetes, while ensuring high availability and disaster recovery across multiple backends.
For many organizations, moving legacy applications to modern cloud infrastructures holds great promise, such as reducing IT overhead and accelerating development times. However, in reality, these projects can be fraught with delays and service interruptions while burdening your team with transition tasks.
In this Kong Summit 2020 talk, we are covering how to seamlessly connect the old world with the new, as well as how to modernize legacy services to run on a modern cloud native stack. With technologies such as Kong Mesh, a control plane for service mesh built on Kuma, and Weave Kubernetes Platform, teams can progressively move legacy applications to Kubernetes — controlled and securely. Built-in GitOps workflows ensure developer-friendly operations for Kubernetes, while ensuring high availability and disaster recovery across multiple backends.
- 1 participant
- 16 minutes

5 Nov 2020
Kong leaders, along with industry special guests, will continue to explore connectivity in this new digital reality and unveil more exciting, new products that will redefine what connectivity means today — and beyond.
Learn more about Kong: https://bit.ly/2I2DypS
Learn more about Kong: https://bit.ly/2I2DypS
- 8 participants
- 31 minutes

4 Nov 2020
In this fireside chat, Kong’s Sandeep Singh Kohli sits down with the founder and CEO of CodePath.org, Michael Ellison, to discuss the trends and common pitfalls of workforce diversity initiatives in the tech industry.
Check the Guide to Building Racial Equality and Inclusivity in the Tech Workplace: https://bit.ly/387k8uJ
Check the Guide to Building Racial Equality and Inclusivity in the Tech Workplace: https://bit.ly/387k8uJ
- 2 participants
- 16 minutes

3 Nov 2020
Kong Co-Founders Augusto Marietti and Marco Palladino, joined by other Kong leaders and industry guests, will share their vision for connectivity in this new digital reality and unveil exciting, new products that will redefine what connectivity means today — and beyond.
Learn more about Kong: https://bit.ly/2I2DypS
#KongSummit20
Learn more about Kong: https://bit.ly/2I2DypS
#KongSummit20
- 10 participants
- 1:13 hours

