►
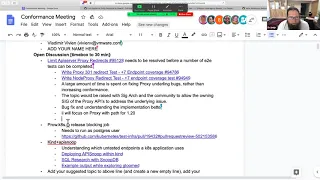
From YouTube: 20201006 SIG Arch Conformance
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
C
B
B
A
So
feel,
free
to
add
anything
else
to
the
agenda
at
the
bottom.
If
you're
something
you
want
to
discuss
or
add
your
name
to
the
attendees
list
today,
we've
got
three
topics
so
far
on
the
agenda.
Think
of
other
things,
that's
fine.
One
of
them
is
one
of
the
end
points.
I've
been
working
on
this.
This
release
for
120
is
our
api
server
proxy
redirects
issue,
and
I
will
make
that
a
bit
bigger
to
share
the
screen.
Rheon.
A
E
Yeah,
I
think
just
sharing
the
screen
or
urine
is
okay.
Thank
you.
At
this
point,
it
was
just
the
time
to
look
at
fixing
this
issue
that
I
thought
was
going
to
be
quite
short,
so
it
was
more
around
trying
to
get
some
extra
help
on
looking
at
resolving
the
issue,
because
I'm
wanting
to
focus
more
on
the
actual
performance
of
this
part.
E
C
A
A
E
A
So
let
me
go
back
here
and
say
for
so
like
we
have
these
other
two
tests
that
are
already
here.
That
are
seven
points,
each
that
are
dependencies
and
those
are
right
out
of
that
right.
Out
of
the
document,
the
agenda
items
over
here
and
they're
all
options
of
connect
with
pod
proxy
or
connect
with
node,
proxy
and
you're
saying
we
should
just
focus
on
the
ones
that
do
not
include.
B
B
A
A
We
should
probably
create
a
separate
issue
and
follow
that
up
saying
these
and
these
three,
these
what
other
other
tests
18
tests
18
end
points
hit
by
this
test
are
covering
stuff.
That's
not
that's
considered
it's
hard
because
it's
all
stable
right,
it's
released,
so
we
can't
really
update.
We
can
update
the
underlying
implementation,
but
the
api
is
exposed,
but
to
say
we're
going
to
put
these
this
specifically
the
ones
that
are
affected
by
the
the
proxy
redirects
issue
that
we
we
can't
fix
quickly
on
the
side.
A
No,
no,
I
don't
think
we
should
remove
it
I'd.
Definitely
it
should
definitely
be
required
for
conformance
and
the
issue
of
us.
Having
that
the
reason
we
remove
stuff
from
targets
for
conformance
is
if
they
are
too
difficult
like
in
the
case,
so
we
don't
have
a
framework
for
storage.
Yet,
in
the
case
of
this
we
have
we.
A
We
understand
that
enough,
but
there's
actually
some
bugs,
and
then
in
this
case
that's
what
I
think
liggett
is
trying
to
raise,
there's
some
bugs
in
the
implementation
that
we
need
to
fix,
and
we
need
to
to
understand
what
the
behavior
we're
trying
to
test
is.
It
needs
to
have
a
consistent
surface
area
and
I
don't
think
that's
the
same
as
saying
we
don't
need
to
write
conformance
tests
for
this.
It's
just
that
we're
exposing
some
some
possible
bugs
in
the
kubernetes
implementation
that
the
the
de
facto
one.
A
A
A
All
right
I'll
take
that
as
a
no.
The
next
part
is
that
we
did
get
our
prow
case.io
release
blocking
job
into
place,
but
it
is
failing
and
it's
failing,
because
on
our
deployment
we
actually
had
some
security
contact
stuff
set
for
the
file
security
group,
and
this
allows
us
to
be
able
to
run
the
container.
Have
it
access
everything
as
a
postgres
user,
so
setting
your
effective
uid,
basically
to
the
70.-
and
I
think
yesterday
is
why
is
this
here
it's
from
spiffx
and
we
were
having
some
issues.
You
can
go.
A
A
A
So
hopefully,
that's
enough
of
the
of
the
information
we'll
have
to
hear
back
from
possibly
effect.
If
anybody
else
has
any
thoughts
on
this
or
if
there's,
if
anybody
has
any
expertise
to
lend
once
this
is
up,
we'll,
hopefully
have
emails
going
out
on
proper
failures
rather
than
in
this
case,
just
a.
A
Some
of
the
things
that
I
is
doing
with
within
the
conformance
area.
So
this
is
what
we've.
What
we've
done
here
with
this
first
link
is
our
directions
for
deploying
api
snoop
in
kind.
This
is
inside
a
document.
I
wrote
just
to
go
through
glue.
You
could
use
any
piece
of
software
once
you
get
past
the
kind
create
cluster
and
the
coupe
cuddle
wait
for.
So
these
basically
running
these
two
commands
here
drop
them
in
the
chat.
A
A
So
we
end
up
using
some
extra
mounts
inside
of
our
control
plane,
node,
to
pick
up
those
files
for
api
snoop
for
the
manifest,
and
also
the
audit
folder,
which
we
we
create
as
a
sub
folder
here
under
audit
and
the
manifest
folder
here,
and
we
just
make
sure
that
postgres
is
exposed
and
then
for
the
worker
node.
We
normally
expose
the
docker
socket
so
that
we
can
run
our
containers
that
can
interact
with
the
over
line
area.
A
So
under
our
audit,
if
you're
not
familiar
with
how
the
the
the
sync
works,
the
sync
is
just
a
coupe
config
that
points
to
a
particular
url
and
because
we're
deploying
kind
onto
the
local
host.
We
are
on
and
map
that
port
9000
we're
able
to
just
go
to
localhost,
and
this
actually
works.
As
far
as
where
the
audits
go.
A
The
policy
itself
is
all
the
things
please
the
metadata
when
you're
done
when
the
response
is
complete,
very
very
simple
deployment
that
allows
us
to
just
run
that
one
command
and
have
everything
come
up
in
order
for
it
to
have
a
target
to
hit
on
that
local
host.
This
is
where
we
go
ahead
and
deploy
a
pod.
A
A
A
Does
some
interesting
things
like
reaching
out
to
the
latest
ci
jobs
and
ensuring
that
we
load
that
data
into
the
database
and
then
the
last
part
is
deploying
an
audit
logger
which
logs
to
the
database-
and
this
is
that
endpoint
that
runs
on
port
9900,
that
we
configured
the
api
service
audit
sync
to
send
to
so
that
was
a
little
bit
of
a
deep
dive
into
using
deploying
api
snoop
in
kind
and
then
in
this
case
we
we
just
deployed
blue,
but
it
really
doesn't
matter
what
you
do
go
deploy
some
stuff.
It's
amazing!
A
It's
your!
Your
workloads
will
be
portable.
If
you
do
the
kubernetes
cloud
thing
and
then
we
scroll
down
to
the
bottom-
and
this
is
the
interesting
part
we're
going
to
say
well
what
did
we
see
and
then
you
can
just
do
sql
queries
to
go.
What
was
not
often
do
what
is
not
like
kubernetes
like
cubestar,
or
in
this
case
I
noticed,
there's
some
glue
stuff
running.
A
A
So
in
this
case
we
were
able
to
use
this
query
to
identify
that
glue.
Cuddle
runs
git
code
version,
which
is
currently
not
conformance
tested,
and
so
I'd
encourage
you
to
take
your
amazing
applications
that
you
deploy
into
the
kubernetes
cloud
and
deploy
some
snoop
db
inside
there
and
and
query
what
is
it
that
we're
we're
doing
here
today
and
and
what
is
important
to
us
to
make?
Oh,
my
gosh,
that's
super
important
part
of
kubernetes
is
critical
to
our
billion
dollar
thing.
F
A
A
So
we
have
a
template
that
we,
so
we
just
run
cluster
setup,
it's
very
similar
except
we're
not
using
kind
right.
Well,
we
use
kind,
because
it's
cluster,
like
init
the
infrastructure
for
packet
and
then
wait
till
packet
cluster
api
is
available,
create
our
name
space
create
and
we
go
through
and
deploy
our
humax
chart
and
wait
for
that
to
come
up
and
actually
attach
to
an
n-cluster
e-max
session
that
has
a
shared
environment
for
us
to
pair,
in
which
also
deploys
api
snip.
A
When
it
does
that
deployment
for
us,
but
it's
not
in
the
end
not
too
much
terribly
more
complicated
than
than
our
other
approach
of
running
it
outside,
except
in
this
case
you're
on
your
local
computer,
and
you
can
use
your
local
favorite
editor
and
your
p
sequel
commands
to
to
fire
at
it.
So
if
you
were
to
run
your
own
applications
with
a
coupe
config
attached,
those
binaries
should
reach
the
api
server
and
log
into
this
audit.
Api
db.
A
A
The
the
stuff
that
was
based
there
glue
is
a
feature-rich
something
on.
I
was
looking
for
something
between
envoy
and
kubernetes,
and
this
thing
does
some
envoy
kubernetes
things
which
looks
great
and
we
we're
looking
for
more
of
these
anything.
Anybody
knows
that's
envoy,
based
that
particularly
has
a
nice
test
suite.
So
we
can
shake
the
application
rigorously
within
a
living
kubernetes
cluster
and
see
what
parts
of
the
api
it
hits
to
hopefully
find
kubernetes
endpoints
that
are
reached
that
are
not
tested
to
kind
of
show.
A
F
A
F
Now
I
have
a
question
I
I
don't
know
how
relevant
it
is
to
what
we're
talking
about,
but
what
does
conform
for
something
like
what
what
you
were
just
looking
at.
What
does
conformance
look
like
with
respect
to
what
we
do
with
with
api
snoop,
for
instance,
the
is
it
the
same
when,
when
they're
looking
at
conformance
for
what
was
it,
you
were
just
looking
at
that
not
snoop
envoy,
sorry,
yeah.
A
A
Different
they
they
have
a
basically
some
that
the
protocol
they
have,
they
have
clients
and
servers,
and
they
don't
have
a
formal
super,
formal
definition
of
what
that
is.
It's
not
too
dissimilar
from
how
quickly
the
kubernetes
api
moves,
where
we
have
lots
of
people
adding
things
in
every
release.
The
swagger
json
updates
to
have
some
fun
stuff
in
there,
but
for
them
it's
a
series
of
of
communication
protocols
for
updating
it's
called
xds
and
that's
part
of
all
the
discovery
services,
as
they
continue
to
inform
each
other.
A
What's
going
on
both
the
the
the
structure
of
that
and
the
format
and
content
of
the
messages
so
using
something
you
know
similar
to
the
things
that
we've
we've
done
like
our
stuff
right
now
is
for
us
to
explore
and
understand,
to
write
the
test
and
to
see
where
the
gaps
exist
and-
and
I
don't
think
they
have
that
yet
for
envoy
and
for
the
kubernetes
community.
We
it's
directly
underpinning
to
go
to
cncf
api
snoop.
A
The
deployment
we
just
looked
at
as
part
of
our
main
set
of
apps,
like
snoop
db
and
audit
logger,
are
what
we
just
deployed
to
look
at,
but
it's
underpinning
the
the
app
itself.
So
if
we
look
at
snoop
snoop
app
snoop
app,
you
can
run
this
by
itself
and
it
will
expose
that
db
that
gets
queried
and
turned
into
api
smooth.cncf.
A
I,
and
so
this
coverage
map
comes
from
two
things:
one
the
consumption
of
ci
runs
okay,
and
so
it
says
this
data
comes
from
stuff
just
a
few
days
ago.
If
I
clicked
on
it
here-
and
I
clicked
on
it
here,
we
can
see
this-
is
these
generate
audit
logs
the
json
files?
So
we
we
slurp
those
in
to
display
this
graph
of
what's
actually
covered
by
our
community
as
far
as
the
possible
apis.
A
A
A
A
So
the
snoop
db
underlies
two
completely
separate
functions
using
the
same
table
right.
What
is
in
the
ci
logs
for
the
given
releases
to
see
where
we
sat
then,
and
then,
when
you're
writing
a
test?
What
our
is
our
test?
Actually
increasing
it?
So
all
of
our
like
we
have
another
repo,
that's
under
api's
new
picket
writing,
so
our
ticket
riding
deployments
go
through
and
don't
find,
let's
find
a
more
recent
one.
A
Maybe
we
use
the
db
from
within
our
org
files
inside
of
our
editor
to
clearly
say
well
what
is
not
hit
yet
well.
These
are
not
hit
yet
where's
the
documentation.
Let's
write
a
mock
test
that
actually
test
it
and
then
at
the
bottom
of
it
we
do
a
query
and
say
well
this
increased
my
coverage
yeah.
It's
going
to
increase
it
by
three
and
it's
actively
coming
from
within
the
cluster
that
you're
developing
on
and
you
can
get
really
detailed
information
on
where
that's
going.
A
And
these
files
export
to
markdown
like
here's
one
for
pod
proxy
options
test.
This
markdown
is
what
we
spaced
into
our
tickets,
so
that
our
flow
goes
all
the
way
from
data
driven.
Where
should
what
should
we
be
working
on
to
ensuring
that
our
we're
consistently
communicating
the
community
in
the
same
way,
so
that
we
need
to
update
our
flow?
We
just
update
the
mock
ticket
template
that
we
start
from
it'll
be
a
template
ticket
in
here
mocktemplate.org
20
days
ago.
F
A
A
A
A
What's
not
tested
based
on
the
ci
runs
you
just
saw
or
more
precisely,
when
the
database
comes
up,
it
gets
the
latest
passing
ci
run
within
the
last.
You
know
four
hours
usually,
and
so
these
are,
when
you
bring
up
your
workstation
the
results
of
untested
things
within
the
last.
You
know
when
the
last
circus,
I
think
they
run
every
every
three
hours
or
so.
A
When
it
becomes
part
of
our
test,
we
write
this
little
section
here
and
go
inside
the
org
file
or
markdown,
and
we'll
actually
run
that
and
verify
that
it's
increasing
coverage
all
inside
of
our
own
cluster,
while
it's
up
export
the
mark
down
and
update
the
ticket.
So
that
never
is
something
that's
super
public,
though
you
could
walk
through
the
file
yourself
and
verify
our
results
by
by
doing
the
same
same.
A
A
A
It
says
clone
api,
snoop
cd
to
the
kind
folder
and
create
it
wait
for
it's
ready
and
you
can
just
select
distinct
user
agent
and
you'll
see
all
the
parts
of
kubernetes
hitting
itself
which
is
kind
of
fun,
and
then
you
could
probably
use
more
sql
food,
we're
probably
going
to
create
a
little
library
of
useful
queries
to
filter
out
and
find
because
that's
where
all
of
the
charts
everything
else
come
from
is
useful.
Sql
queries
in
this
case,
we're
trying
to
deploy
envoy
envoy
doesn't
hit
the
api
at
all.
A
A
A
F
A
It's
been
hard
because
we
we
had
a,
I
think
at
one
of
the
meetings
we've
talked
about.
Wouldn't
it
be
nice
if
we
could
deploy
something
in
the
cluster
and
could
look
at
the
api
and
I
think,
within
within
24
hours,
we
had
our
initial
pr
for
audit
audit
sync
dynamic
audit,
sync
and
that
stayed
in
alpha
and
unfortunately
languished
to
get
removed
in
one
one
in
one
one,
twenty
or
one
one
nineteen
was
was
cut,
so
we
no
longer
have
the
way.
D
A
Months
ago
we
knew
it
was
coming
because
the
pr
was
like
a
month
into
the
release
cycle
and
we
knew
we'd
have
to
completely
change
the
way
that
we
deploy,
and
that
would
be
limited
to
deploying
snoop
db
within
clusters,
where
we
could
modify
again
that
go
into
this
kind,
folder
to
modify
the
parameters
of
api
server
and
any
managed
service.
You're
not
really
going
to
be
able
to
say.
A
Please
add
these
args
to
api
server
and
then,
in
addition
to
not
to
adding
args,
it's
a
lot
harder
for
a
lot
of
other
provisioning
mechanisms,
because
you
need
the
files
as
well,
and
in
this
case
we
you
know
we
went
through
and
then
we'll
add.
These
extra
amounts
to
go
from
our
host
folder
into
not
only
kind
they're,
not
only
docker,
but
then
into
dot
kinds,
containers
within
docker,
so
that
these
it
all
came
up.
A
G
I
would
love
to
hear
thoughts
go
ahead.
Ben
yeah,
I
was
just
gonna
say
I
mean
we.
We
have
a
sort
of
a
cluster
api
story
right
where
we
stand
up
kubernetes
clusters
using
various
controllers.
We
have
a
controller
that
knows
how
to
talk
to
kubernetes
and
stand-up
vms.
We
have
a
controller
that
then
knows
how
to
configure
kubernetes
in
those
vms,
and
then
we
have
another
control.
That
knows
how
to
post
configure
the
kubernetes.
G
A
What
we
do,
if
I
go
back
to
our
there,
was
our
I'm
just
gonna.
So
if
you
go
to
umax.org,
this
is
kind
of
like
our
workflow
and
we
have
a
there's
under
infra
cluster
api.
So
this
is
our
cluster
api
setup
and
you
start
by
having
a
cluster.
Don't
care,
do
your
mini
cube,
kind,
they're
your
happy
place
and
get
all
of
your
and
this.
This
is
just
lispy
code
for
how
we
work.
A
Then
that
just
brings
up
cluster
api
for
packet
because
lovely
folks
as
they
are,
they
donate
all
of
the
the
things
we
need
to
get
our
job
done
and
then
we
wait
for
cluster
api
to
be
ready
and
if
you
want
to
look
at
the
logs
while
you're
waiting,
this
is
a
great
place
to
go.
Look,
and
this
is
our
cluster
configuration
and
we
use
some
of
those
variables
to
pop
out
and
say
wonderful.
Let's
take
our
template,
which
I'll
show
you
in
a
minute
to
create
a
file
for
your
user
you're
special.
A
A
A
We
also
have
post
cube
admin
commands
which
we'll
come
back
to.
This
probably
makes
more
sense
to
do
the
pre
cube
admin
commands,
and
this
is
where
we
lay
out
via
here
doc,
the
sync
and
the
policy,
because
you
got
to
get
them
on
disk
and,
if
anybody's
a
cloud.
Sorry
cluster
api
wizard.
If
there's
a
better
way.
Let
me
know
this
is
the
way
that
we
we
went
with
our
knowledge
and
we
also
do
the
normal
things
for
getting
ready
for
deploying
docker
and
wait
for
that
to
come
up.
A
A
So
we
in
roots
home
folder,
we
check
out
snoop
and
we
create
a
name
space
for
it
and
we
install
snoop,
dp
and
auto
logger
from
the
charts
there,
because
we
don't
have
public
charts
yet
and
because
we
already
configured
api
snoop
to
do
this,
the
and
we
couldn't
install
into
the
clusters
up.
It's
kind
of
this
weird
state.
I
didn't
know
how
to
get
api
server
to
just
ignore
the
fact
that
the
audit
logger
is
not
there.
So
it
does
take
a
little
bit.
A
Maybe
like
four
minutes
for
everything
to
to
come
up.
We
also
deploy
our
humax
deployment
using
helm
using
the
chart
within
that
folder,
and
we
have
an
api's
nuke
values
that
has
all
the
things
specific
for
us
developing
on
api
snoop
for
within
and
the
cluster,
including
communicating
directly
to
this
new
db
as
a
device,
and
then
that's
that's
kind
of
it.
The
rest
of
it
is
the
packet
machines
themselves,
how
big
they
are,
what
the
ssh
keys
are
and
yeah.
A
A
A
Right,
if
you
want
to
use
this
file,
there's
a
secrets
here
and
if
you
I'm
sure,
if
you're
exploring
this,
I
can
probably
work
with
packet
to
get
you
some
keys
or
if
you
do
happen,
to
update
this
to
work
on
other
cloud
providers.
I
would
love
to
get
the
your
your
working
cluster
api
cluster
api
templates
back,
so
we
can
kind
of
contribute
to
keep
anyone
who
has
x.
A
For
deploying
api,
snoop
or
writing
conformance
tests
or
seeing
if
their
application
is
using
things
that
need
test
written
for
them,
I
think
that's.
My
hope
is
that
we
can
write
go
back
over
here.
If
you
look
at
what
I'm
trying
to
do
in
my
pr
for
api
snoop
for
add,
envoy
glue,
research
and
the
end,
the
markdown
file
here.
C
A
A
G
Yeah-
and
I
think
that
that's
that's
what
seems
really
interesting
to
me
right
now
is
is
like.
I
know
that
we
hit,
I
mean
we
have
all
sorts
of
things,
that
we
do.
I'm
sure
we're
hitting
all
sorts
of
endpoints
it'd
be
really
interesting
to
to
see
if
we
can
get
a
sense
of
what
it
is
that
we're
hitting
and
what
it
is,
that's
not
being
tested.
