►
From YouTube: ROS 2 Security Working Group June 8, 2021
Description
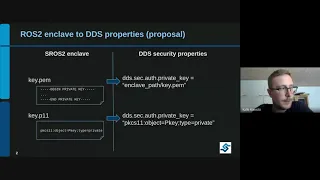
Discussion on adding PKCS11 support to ROS 2
A
B
B
B
So
what
we
are
proposing
here
is
a
simpler
solution
that
could
be
implemented
in
quite
a
shorter
time
and
without
large
changes,
and
the
idea
is
keeping
the
current
concept
of
enclaves
but
making
extras
aware
of
the
file
extension
somehow
so,
for
example,
for
a
private
key
file.
If
there
is
a
kickout
pen
file,
make
it
as
always
and
just
set
the
tts
property
to
the
file
path.
B
Obviously
the
middleware
has
to
be
it
has
to
support
a
pikachu
s11
uis,
but
that's
also
out
of
the
scope
of
of
errors,
and
that's
that
that's
just
another
another
issue.
But
we
think
that
this
is
pretty
simple
and
that
may
give
extras
the
support
for
pikachu
11
us
in
just
to
communicate
them
to
the
to
the
middle.
B
D
Yeah
not
not
much,
I
think,
in
the
discussion.
We
also
discussed
a
little
bit
like
what.
What
do
we
want
to
include
in
the
in
the
scope
of
this
approach
and-
and
I
think
at
least
for
our
use
case-
it's
quite
okay-
to
call
it
rather
bare
minimum,
meaning
that
we
just
want
to
protect
the
private
key
on
the
crypto
backend
and
consume
that
over
the
over
t,
p
kcs11
interface.
D
So
basically
that
would
then
mean
that
we
just
need
to
have
key
creation
requests
and
and
signing
requests
going
through
that
channel
and
what
would
be
out
of
scope
is
basically,
then
all
the
certificates
and
and
those
basically
public
artifacts,
so
all
the
ca
files
and
certificate
pen
files,
but
yeah.
I
think
that's
just
some
insight
of
our
discussion.
I
I
don't
think
that
include
or
well
actually
yeah
it
also
it's
relevant
for
esros.
B
Yeah,
even
in
that
case,
I
guess
that
if
we,
if
we
at
the
end,
if
we
go
this
in
this
path,
even
adding
the
rest
of
the
elements
like
the
certificates
and
such
to
this
mechanism-
wouldn't
be-
I
mean
it's.
So
it's
easy
to
do
and
we
can
have
that
already
in
place
in
in
this
rows,
regardless
of
the
middleware
supporting
it
or
not.
D
B
C
E
D
C
So
yeah
you
don't
have
you
don't
have
to
you?
Don't
have
to
solve
the
problem
now,
but
hypothetically,
if,
if
a
user
was
using
a
a
tpm,
where
would
they
configure
would
be
the
appropriate
location
in
their
in
their
application
code
or
some
kind
of
config
file
that
their
application
then
reads
is
that
if
they
didn't
pass
the
tpm
uri
to
sros
and
then
sros
should
pass
that
to
the
dds.
C
D
That's
a
good
question
like
I:
I
haven't
worked
in
environments
without
a
file
system,
so
can't
really
answer
to
that,
but
but
basically,
if
environment
wire
apples
are
okay
for
those,
although
isn't
that
also,
and
just
a
matter
of
file
in
at
least
in
linux
systems,
so
I
don't
know
how
but
yeah
but
yeah.
Basically
the
configuration
is
rather
simple.
It's
just
a
string,
so
so
I
guess
no
matter
what
they
where
they
store
it.
D
A
Yes,
you
think
about
it,
but
yeah
to
add
on
that
rough,
and
I
think
when
we
talked
about
it
last
time,
we
actually
separated
out
the
two
problems,
one
of
them
for
using
pks
and
one
of
them
for
doing
this
with
a
on
a
device
that
doesn't
have
a
file
system
and
we
weren't
going
after
the
the
device
without
a
file
system
problem.
Yet.
C
B
E
A
B
E
B
Based
on
site
extension,
not
completely
because
you
still
have
to
to
let's
say
serialize
or
somehow
that
that
information,
if
you
are
going
to
pass
the
the
serialized
key
directly,
you
have
to
set
the
correct
the
correct
format
to
that.
To
that
string,
I
believe
that's
the
a
data
uri
and
that
would
be
so
data
column
and
then
the
serialization
in
the
case
of
pikachus
11.
That
would
be
because
you
see
that
in
column
and
then
the
object
and
for
the
file
path.
B
E
Yeah,
that
makes
sense.
Okay,
and
I
guess
one
other
like
practical
question
on
that
front.
How
do
we,
how
do
you
envision
estrus
to
sorting
out
like
we
would
be
looking
for
like
a
site
starting
with
key,
and
then
we
have
like
a
priority
list
like
I
guess
in
practice,
in
deployed
system,
you
would
never
have
a
pen
file
and
a
p11
file,
but
like
how
do
how
do
we
expect
the
system
to
behave
if
you
have
both
like
should
like
the
p11,
be
the
one
taking
priority
or.
B
A
D
I
think
it
goes
down
a
little
bit
to
the
middleware,
because
I
think
this
uri
would
go
quite
directly
to
the
middleware
api
eventually,
but
this
is
quite
standard
format.
This
big
ss11
uri.
So
I
guess
we
can
quite
easily
mitigate
the
risk
if,
if
there
is
any
just
buy
with
some
regular
expression
to
validate
the
syntax.
A
A
D
A
C
A
D
A
A
D
C
D
D
Yeah
exactly
exactly
so,
they
either
need
to
fetch
that
overpick
ss11
or
they
just
get
it
from
the
file
system,
and
I
think,
for
sake
of
simplicity,
I
would
even
suggest
that
we
keep
that
as
it
is
today
the
public
certificates
because
they
are
public.
I
I
don't
see
much
reason
to
you
know
protect
the
hardcore.
A
So
so
you
have
the
certificate
and
then
you
have
the
certificate
authority
and
I
think
it
and
both
of
them
obviously
have
the
private
side
it's
right,
so
so
the
private
side,
key
of
the
certificate
authority,
also,
if
I'm
not
mistaken,
that
will
need
to
be
in
the
tpm.
So
you
can
ask
the
tpm
to
sign.
A
D
A
C
D
Like
the
whole
yeah,
both
ways
are
definitely
possible,
but
but
basically
generating
csrs
and
and
otca
sort
of
logic
are
not.
You
know,
part
of
p11
specifications,
so
it's
much
higher
level.
So
anyway,
whatever
ca
solution
will
be
used,
can
consume
big
ss11
to
do
the
crypto
operations,
but
but
bill
has
or
needs
some
higher
level
software
to
let
it
be
open,
ssl
or
whatever,
to
to
actually
sign
the
csrs
and
whatnot
but
yeah.
D
C
So
I
think
I
was
working
on
sros
one.
I
was
looking
at
other
key
management
tools
and
I'm
trying
I'm
trying
to
look
at
what
it
was,
but
there's
a
rather
large
open
source
project
for
key
management.
Stuff,
like
everything
from
you
know,
your
your
classic
certificate
authority
chain
management
to
stuff
more
advanced.
Like
token
generation.
D
D
C
I
I
had
an
earlier
project
called
keyment,
which
a
lot
of
the
stuff
we're
using
now
kind
of
drives,
but
the
the
idea
with
ikea.
It
was
like
similar
to
event
where
you
had
a
workspace
for
your
key
material,
and
you
had
like
a
you,
had
a
source
file
without
all
the
configurations.
That
would
be
where
you
encode
the
permissions,
the
structures
for
your
certificate
authorities
and
who
you
want
what
to
sign.
C
Then
you
would
have
your
build
where
you
would
generate
all
the
certificate
requests,
signing
requests
and
intermittent
key
material
so
that
the
private
keys
would
be
generated,
but
the
certificates
wouldn't
be
signed
and
then
you'd
have
like
your
install
folder,
which
would
have
all
the
final
resulting
files,
but
having
that
level
of
like
different
directories
for
intermittent
stages
of
your
key
store
was
kind
of
helpful.
Because
then
you
could,
you
know,
pull
in
any
other
external
tool
that
can
work
with
the
file
system
to
manage
your
key
material.
A
A
Think
we're
on
a
great
path.
I
think
probably
the
next
step
is,
if
you
guys
are
up
for
it
to
actually
propose
some.
You
know,
design
updates,
yeah,
just
simpler
is
better,
I
think
so.
The
idea
of
just
simply
having
and
recognizing
a
p11
file-
that's
a
uri,
I
think
is
is
really
is,
is
really
straightforward.
It's
a
clean
solution.
A
You
know
how
how
you
actually
implement
it
and
how
we
tool
sros
2,
can
be
a
separate
discussion
right
because
I
think
there's
a
bunch
of
different
use
cases
that
can
derive
from
this
one
of
them
being
keeping
the
key
in
the
key
store.
I
think
another
one
is
imagine
if
your
ca
was
on
a
physical
device,
you
plug
it
into
the
robot
to
have
it
generate.
You
know
its
own
keys
and
then
you
pull
it
off.
So
essentially,
you
use
some
physical
to
have
a
robot
join
a
swarm
like
all
that
becomes
enabled.
A
D
A
E
D
Yeah
so
yeah,
I
think
the
requirement
is
pretty
much
says
that,
as
you
said,
because
11
uris
needs
to
be
supported
and
obviously
those
crypto
operations
that
we
require,
which
was,
I
think,
just
rsa,
was
it
pss
signing
scheme
and
yeah
key
creation,
but
but
it's
very
basic
concept
and
I
I
cannot
think
of
any
any
vendor
middleware.
That
would
not
support
this.
D
So
we
kind
of
discussed
what
would
be
the
reference
implementation
and
there
is
this
open
source
project
called
openhsm
and
or
software.
I'm
sorry,
soft
hsn,
which
is
basically
a
software
mock-up
of
a
hardware
security
module
and
it
has
big
it
works
as
a
big
s11
back-end.
So
if
we
get
it
working
with
this,
it
should
pretty
much
work
with
any
any
commercially
available
solution
as
well.
B
Being
a
word
that
now
not
only
file
your
eyes
would
be
available,
but
also
because
you're,
single
and
your
eyes
so
that
at
least
they
can,
if
they
are
not
supporting
this,
at
least
they
can,
you
know,
fall
back
or
or
exit
there,
gracefully.
Somehow,
I'm
not
trying
to
open
a
path
that
will
it's
not
a
path.
A
So
they
knew
we're
running
a
long
bit
long,
but
only
throw
it
out
there
is.
We
have
a
ta
there's
a
tsc
meeting
scheduled
for
next
week
next
thursday.
I
wonder
if
it
might
be
worthwhile
to
for
either
of
you
or
both
of
you
to
actually
present
just
at
a
high
level.
What's
going
on
and
that
becomes
you
know,
a
notification
that
you
know,
there's
there's
a.
B
B
D
A
E
A
A
A
E
I
guess
one
concern
I
have
is
not
every
like
vendor
dds
vendor
is
on
the
psc
and
and
like
it.
I'm
not
sure
that
is
the
one
way
to
communicate,
changes
that
are
expected
to
be
supported
by
various
middlewares,
not
that
it
should
not
be
presented
to
the
tfc,
but,
like
I
believe
there
is
a
team
on
github
or
something
or
like
a
group
on
this
course
with
people
from
various
dds
vendor
companies
and
like.
E
A
Okay,
yeah
great
point
so,
and
maybe
I'm
rushing
this
a
little
bit.
Maybe
you
want
to
flush
it
out
a
little
bit
more,
so
I'll
just
leave
that
out
there.
If,
if
at
some
point
you
want
to
present
this
to
the
tsc,
but
otherwise
you
know
we
flush
it
out
on
on
discourse
or
I
think
there
is
a
just
a
little
bit
of
it
yeah
socialization
of
it.
I
just
leave
it
at
that.
A
Community,
okay,
so
I'll
leave
it
at
that.
If,
if
you're
interested
in
you
know
getting
on
the
tsc
agenda,
we
can
do
that,
but
I
think,
like
mikhail
pointed
out,
there's
probably
other
places
where
we
need
to
socialize
it
as
well,
and
part
of
that
will
probably
be
if
you
put
out
a
design
doc
update,
making
sure
that
gets
visibility
as
well.
So
but
again,
I
think
it's
really
really
neat
feature
there.
D
E
I
don't
remember
exactly
what's
in
there,
but
my
guess
is
that
there
is
one
explaining
how
key
like
security
material
is
retrieved,
and
so
I
think,
a
pull
request
modifying
that
one
to
just
add
the
option
for
pkcs
and
explaining
how
it's
gonna
work
would
be
the
good
place
to
start
and
then,
like
just
drop.
A
note
like
on
the
matrix
chart-
or
I
think
like
most
of
us
may
be
watching
that
repo.
So
we
will
then
like
iterate
on
it
and
and
then
it's
gonna
be
open
robotics.
E
A
So
so
I
think
great
discussion
again.
I
just
want
to
move
on
to
the
real.
Briefly
to
the
last
item
I
had
on
the
agenda,
there's
a
I
opened
up
a
pull
request
for
the
raws
to
documentation,
I'll
drop
the
link
in
there.
If
you
get
a
chance
to
review
that
I'd
really
appreciate
it.
This
takes
the
documentation
for
using
security,
that's
in
the
sros
2
repo
and
adds
it
to
the
the
the
raws
tutorials.
A
So
I
wanted
folks
to
understand
how
to
troubleshoot
and
validate
the
the
certificates,
and
then
I
also
added
a
section
on
network
traffic.
That's
just
me
because
to
me
the
truth
is
in
the
packets,
so
I
wanted
just
a
real
quick
like
this
is
how
you
can
see
that
the
packets
are
encrypted
and
stuff
like
that,
so
some
other
minor
changes
and
whatnot.
A
E
A
A
A
Okay,
so
hopefully
I've
been
faithful
to
the
content.
There
is
one
to
do
under
there,
where
there's
the
example
about
using
security
across
two
machines,
which
right
now
uses
copying
files.
You
know
copying
the
entire
key
store.
I
would
rather
just
copy
the
cas
over
and
then
recreate
the
enclave
on
the
other
machine,
so
that
tutorial
should
be
kind
of
updated.
I
think
to
reflect
that,
but
I
just
didn't
want
to
make
that
change
at
this
point.
