►
From YouTube: Exploring Embedded Rust for Functional Safety
Description
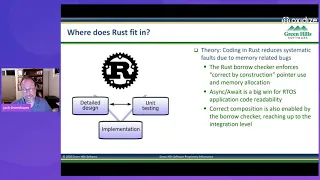
Jack Greenbaum from Green Hills Software shares his experience with exploring Embedded Rust for use in functional safety systems at Green Hills Software. This includes the parts that are easy, a few rough edges for the end to end Embedded workflow, and recommendations for bringing Rust to the broader Embedded Systems market and Function Safety Systems in particular.
Interested in using Rust for safety critical systems? Reach out to us at sealed-rust@ferrous-systems.com!
A
A
So
I'm
going
to
start
tonight
with
an
introduction
to
green
hill
software
and
functional
safety.
Functional
safety
is
one
of
those
things
that
it
sounds
like
it's
something
you
ought
to
know
what
it
is.
But
then,
when
you
dig
into
it,
you
don't
so
it's
sort
of
a
cryptic
topic
for
a
lot
of
folk
I'll
talk
about
why
you
might
want
to
use
rust
in
a
functional
safety
system
and
and
explore
whether
it's
suitable
for
functional
safety
systems.
Today.
A
A
If
you
drive
a
japanese
us
or
european
produced
automobile,
then
you
likely
are
have
some
green
hill
software
in
there,
because
we've
been
shipped
in
130
million
vehicles
to
date
in
aviation.
If
you,
when,
back
when
we
used
to
fly
on
commercial
aircraft,
you
probably
flew
on
an
aircraft
that
used
green
hill
software.
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
I
I
didn't
have
time
to
get
a
picture
of
the
the
test
lab
at
green
hills.
Our
test
labs.
We
have
a
board
for
every
bsp
that
we
support
and
connected
to.
It
is
a
jtag
probe,
a
serial
port,
a
network
power
supply
and
an
ethernet
port,
and
we
have
hundreds
of
these
and
we're
running
validations
constantly,
and
you
can't
do
that
with
an
off-the-shelf
system.
A
A
That
read
your
code
and
look
for
whether
you,
whether
your
engineers
accidentally
cut
and
pasted
from
open
source
and
look
for
open
source,
license
headers,
and
then
things
like
secure
boot
signers,
you
know.
So
if,
if
rust
is
to
be
adopted
it
it
can't
be
tied
to
a
single
tool
chain
and
embedded,
and
this
is
really
what's
what's
different
about
embedded
and
therefore
functional
safety.
A
A
A
A
The
cortex
m3
based
software
hardware,
abstraction
layer
that
rust
embedded
provides
the
rtfm
real
time
for
the
masses.
This
is
a
great
system
for
building
small
embedded
systems
and
it
just
works,
and
that's
really
one
of
the
things
I
like
about
it,
and
that's
why
I
really
do
believe
yeah.
This
is
a
better
way
to
go
than
an
arduino.
A
So,
let's
just
look
one
level
deep
here:
what's
different
about
programming,
rust
embedded,
then
any
other
rust
platform.
Well,
one
thing
is
this:
is
this
link
map
this
link.x
file?
This
is
input
to
the
linker.
Remember
I
was
talking
about
linkers,
so
in
embedded
systems,
you
have
to
tell
the
linker
where
to
put
things,
because
you've
got
a
lot
of
different
types
of
memory
and
embedded
systems
that
you
don't
have
in
a
general
purpose
os
and
the
general
purpose
os
everything's,
just
memory,
it's
just
ram
and
pages,
it
looks
infinite
to
you.
A
Well
memory
is
not
that,
like
that
in
embedded
systems,
you
have
flash
typically
you're
booting
from
flash
rust,
embed
it'll
flash
it
for
you.
It's
really
awesome,
then
you've
got
to
manage
your
ram
and
sometimes
you'll
have
different
types
of
ram
fast
ram,
external
slow
ram,
so
that
linker
command
file
is
is
really
important.
So
that's
a
that's
a
difference
here
and
then
you've
got
the
cargo
run
command
that
doesn't
just
shell
out
it
actually
talks
to
this
part
of
the
board
here
is:
what's
called
this
is
a
small
jtag
run
control
thing?
A
A
What
if
I
wanted
to
use
it
with
something
more
industrial
strength?
What
what
do
I
have
to
do?
Can
I
take
rust
embedded
as
it
exists
today
and
use
it
in
a
more
commercial
manner,
so
this
board
I'm
showing
now
this
one's
on
my
desk
as
well,
while
actually
on
a
little
rack
next
to
my
desk-
and
you
know,
some
things
to
note
is
compared
to
the
hobbyist
nucleo
arduino
baseboard.
This
one's
got
a
display.
Okay,
it
costs
a
little
bit
of
money.
It's
got
canon
rs232
down
here,
but
really
importantly,
it's
got
an
arm.
A
A
This
trace
pod
connected
to
the
trace
port
with
the
appropriate
electrical
on
this
higher
cost
board.
Lets
me
do
that,
so
the
extra
peripherals,
the
extra
debug?
That's
what
makes
this
a
more
commercial
oriented
board?
This
is,
in
fact,
a
reference
board.
That's
frequently
used
for
medical
designs,
infusion
pumps
and
those
types
of
systems.
A
So
I
asked
the
question:
what
do
I
have
to
change
if
I
want
to
use
this
board?
Well,
the
first
thing
is:
I
already
have
this
board
up
and
running
with
the
green
hills
tool
chain.
I've
got
a
green
hills,
linker
command
file,
oh
shoot,
but
I'm
using
the
rust
linker
here.
Okay,
what
am
I
going
to
do
about
that
and
then
cargo
run
cargo
run
knows
how
to
talk
to
open
ocd
devices
and
run
control
them.
A
The
greenhouse
probe
is
not
an
open
ocd
device,
so
I
can't
just
immediately
use
cargo
embedded
as
its
shipped,
but
I
don't
have
to
go
very
far
and
that's
because
cargo
will
also
build
a
static.
Lib
it'll
build
a
crate
as
a
static
library,
a
dot,
a
file
fully
linked
with
everything,
but
the
operating
system,
this
dot
a
file,
looks
to
a
tool
chain
like
any
other
dot
a
file.
A
A
A
A
A
This
is
a
really
good
integration
point
and
it's
supported
today.
Now
there
are
downsides,
we
lose
cargo
run.
I
put
that
with
strikethrough
because
I'm
not
sure
in
an
embedded
world.
I'm
not
sure
cargo
runs
a
great
thing
for
the
use
model
of
an
arduino
yeah
in
a
commercial
world,
but
cargo
test
is
a
loss.
A
A
A
A
A
Now,
if
you
look
at
the
backing
material
behind
sealed
rust,
you'll
see
that
james
calls
out
and
ferrous
systems
calls
out,
and
the
supporters
of
sealed
rust
call
out
that
rust
is
already
in
a
really
good
place
because
of
the
test
infrastructure
and
the
rfc
process.
You
know
the
rationale
for
the
design
choices
is
there.
This
is
a
good
place
to
start
from,
but
the
level
of
rigor
needs
to
be
brought
up
the
level
of
formality
and
stability.
A
You
know,
I've
said
a
couple
times
that
code
lives
forever
code
lives
much
longer
than
you
ever
possibly
imagined.
Stacks
are
really
an
example.
Some
of
the
can
stacks
in
automobiles
from
the
big
companies
15
20
years
old
same
software.
They
just
keep
rebuilding
it.
It's
too
expensive
to
test
again.
A
A
B
A
We
think
that
sealed
rust
or
something
like
it
is
needed
to
enable
use
and
safety
systems
and
and
that's
what
will
unlock
commercially
available
qualified
tool
chains.
I
don't
think
any
one
vendor
or
any
one
program
adopting
rust
is
going
to
be
able
to
pay
for
all
the
process
that
provides
the
assurance
that
we've
built
a
system
that
properly
takes
the
safety
into
account.
A
B
I
am
muted
thank
you
yeah,
so
we've
had
a
couple
questions
in
the
chat,
so
we're
a
little
over
time,
but
we've
got
time
for
a
couple
questions
before
we
go
back
into
break.
So
the
first
question
was
from
evan
richter
and
evan
richter
asked
jack.
I
would
love
to
hear
your
thoughts
on
efforts
to
help
the
difficulty
of
testing
on
embedded
platforms,
fuzzing
and
coverage.
Guiding
fuzzing
in
particular,
has
really
taken
off
in
the
last
five
years,
but
still
it
is
very
difficult
to
harness,
embedded
solutions
into
a
fuzzing
target.
A
A
B
All
right,
I've
got
a
second
and
probably
last
question
for
you
b
brown
in
the
chat
is
asking.
I
appreciated
the
static
lib
example
of
how
to
plug
into
an
existing
project,
but
do
tool.
Companies
worry
that
their
long-term
market
share
may
reduce
if
new
projects
pick
a
fully
open
source
tool
chain
with
c
and
c
plus,
plus
the
open
source
tools
can
be
so
clunky
that
id
ees,
like
iar,
add
a
ton
of
value,
but
the
rust
tool
chain
is
just
so
easy
and
user
friendly.
A
You
know
my
attitude
about
open
source
is
if
open
source
is
good
enough
for
you
go
for
it.
You
know
our
customers
find
that
open
source
doesn't
have
properties
that
they
need
for
long-term
support
and
functional
safety.
They
don't
have
certifications,
they
don't
have
long-term
support.
They
may
lack
features
for
embedded
systems.
Companies
often
pay
us
to
customize
tool
chains
to
exactly
their
specifications.
A
A
A
You
know:
that's
just
not
stuff
that
open
source
is
good
at
so
open
source
is
good
at
stuff.
That's
used
by
a
whole
ton
of
people
and
less
good
at
stuff.
That's
used
by
fewer
numbers
of
people-
and
you
know
we're
always
going
to
have
value,
is,
is
what
I
think
greenhill.
There
will
always
be
a
need
for
a
company
like
green
hills,
even
as
open
source
takes
more
and
more
of
the
software
content.
As
you've
observed.
B
All
right,
thank
you
so
much
jack.
I
know
we'll
probably
have
at
least
one
more
question
in
the
chat
and
it'd
be
great
to
if,
if
you
could
comment
on
that
on
the
matrix
chat,
but
I
know
you
also
need
to
get
to
sleep
before
you
come
back
for
our
safety
critical
panel
tomorrow
for
you
and
later
today
for
us.
So
thank
you
so
much
for
your
talk
and
we're
gonna
go
to
break
now
and
we'll
be
back
in
a
couple
minutes
with
our
next
talk.
Thank
you.
Everyone.
