►
From YouTube: EEA Education Series Conf Call 5
Description
August EEA Education Series
The Current State of Wallet Access and Security for Corporate Users
Learn about the current state of Wallet Access and Security for corporate users from some of the top wallet and user access providers for business and commerce. Wei Wu Zhang, the head of development for AlphaWallet and Tom Teman, a co-founder at Portis/ShapeShift, present their latest offerings and explain how they balance seamless user access with optimal security measures, all while enabling improved interaction with smart contracts and on-chain logic.
Twitter: Wei Wu Zhang @zhangweiwu, Tom Teman @tomteman
A
Hello:
everyone
thank
you
for
joining
us
for
today's
eea
education
series
c.
Today
we
will
discuss
the
current
state
of
wallet,
access
and
security
for
corporate
users.
Everyone
is
in
listen
only
mode.
However,
you
are
encouraged
to
ask
questions
by
using
the
question
box
in
your
control
panel.
Today's
call
is
being
recorded
and
will
be
available
to
all
attendees
soon
after
today's
presentation,
the
enterprise
ethereum
alliance
is
a
member
member-driven
standards
organization
whose
charter
is
to
develop
open,
blockchain
specifications
that
drive
harmonization
and
interoperability
for
businesses
and
consumers
worldwide.
A
B
Well,
thank
you
teresa.
I
want
to
also
give
a
shout
out
to
ken
from
as
well
as
teresha
king
from
the
eea
for
designing
and
organizing
this
webinar.
My
name
is
tom
lindeman.
I
work
at
consensus.
I'm
the
chair
of
this
security
special
interest
group
and
would
like
to
welcome
folks
from
around
the
world
as
well.
We
opened
this
session
up
to
non-eea
members.
You
can
get
an
idea
of
some
of
the
things
that
we
talk
about
in
these
working
groups
and
I've
got
great
topic
today.
B
It's
on
wallets
and
security
be
a
little
bit
of
a
spin
from
the
corporate
point
of
view,
since
we
are
the
enterprise
ethereum
alliance
and
this
call
will
also
serve
as
the
august
education
call.
So
today
we've
got
wei
wu
zhang
from
alpha
wallet
and
he's
going
to
be
digging
into
some
of
their
new
features,
as
well
as
a
thing
called
token
script
that
well,
I'm
not
gonna,
get
it
right,
but
it
kind
of
lets
your
tokens
run
as
as
dapps
inside
your
wallet.
B
B
I'm
not
not
sure
how
I
how
I
did
that,
but
I
was
just
standing
in
the
right
place
at
the
right
time.
It's
very
very
cool.
At
the
end,
I
will
ask
some
more
questions.
I
will
probably
take
some
q
a
from
everybody
as
well
so
type
your
questions
into
the
chat,
as
teresa
said
and
onward
we
go.
I
believe
we're
going
to
have
wei
wu
from
alpha
wallet.
B
C
C
But
going
beyond
that.
Of
course,
it's
for
more
security,
because
then
the
user
wouldn't
step
into
the
wrong
depth
and
to
manipulate
which
one
might
manipulate
your
pokemon
and
it's
more
available
than
the
website,
and
but
it's
also
very
going
beyond
that
very
well
integrated
with
the
wallet
and
other
websites.
So
it
makes
it
easier
for
you
to
use
your
token
for
your
user
to
use
your
token
on
other
website
that
is
not
developed
by
you
and
you
can
see
your
token
balance
and
activities
together
with
other
tokens.
C
C
C
C
It
turns
out
that
to
support
this,
you
need
not
only
bitcoin
to
support
it,
but
also
what
it
supported,
and
it
was
10
years
ago,
but
sadly
today-
and
this
feature
is
still
missing
in
a
lot
of
almost
all
certain
areas-
and
here
is
one
scenario
where
multisig
can
really
shine-
I'm
starting
this.
I
will
extend
from
this
story
to
other
stories
later.
So
let's
say
that
you
are
running
exchange
and
typically
you
have
a
custodian
exchange
user
deposit
money
into
the
exchange
and
later
when
they
want
to
create
order.
C
C
If
you
have,
if
multisig
is
implemented,
then
the
user
should
be
able
to
send
the
order
with
in
the
cryptographically
signed
message
directly
from
user's
wallet
and
and
if
there
is
order
to
be
filled.
Even
if
the
user
is
not
online,
it
should
be
possible
by
a
counter
sign,
user's
order
and
withdrawn
money
from
users
wallet.
C
Therefore,
you
can
have
more
security
because
you
have
less
contract
party
risk
and
you
also
have
less
attack
service
in
the
sense
that
the
money
doesn't
stay
on
the
exchange
account
for
a
long
time.
So
in
this
case,
we
we
demonstrated
multisig
but
to
really
make
it
useful.
We
need
to
introduce
another
concept
called
the
temptation.
C
It's
not
a
new
concept.
The
test
station
has
been
used
for
for
30
days
three
decades,
so
compared
to
let's
say,
compare
sending
ether
by
motorcycle,
which
is
the
case
where
I
send
it
to
someone.
I
want
to
be
sure
the
recipients
have
the
private
key
compared
to
that
which
is
on
the
left,
observe
on
the
right,
where
we
have
use
case,
where
you
can,
I
can
send
ether
by
email,
borrowing
from
the
early
internet
and
development.
If
you
can
send
money
by
email,
which
is
what
people
do.
C
C
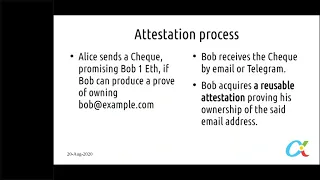
So
this
would
be
the
process
that
alice
sends
a
check
promising
bob
one.
If,
if
bob
can
produce
a
proof
of
owning,
blobatix,
example.com
and
bob
on
the
other
side
can
can
can
get
the
check
and
then
acquire
a
test
station
from
a
tester
to
prove
that
his
own
email
address
and
with
these
two
pieces
of
message
and
he
can
redeem
the
money.
So
it's
like
multisig
with
three
parties,
but
with
a
process
in
it
and.
A
C
C
They
say
you
can
write
that
it's
up
to
100
ether
per
day
and
the
actual
access
is
controlled
by
the
employee
having
a
test
station
that
assigned
him
to
the
role
that
can
use
this
authorization
to
spend
money
from
company's
this.
This
will
be
example,
and
if,
if
if
it
is
done
with
token
script,
the
the
clerk
will
be
able
to
use
this
functionality,
even
if
they
are
you
accessing
a
website
that
simply
won't
either
and
does
not
have
the
functionality
of
recognizing
attestation
or
multisig
on
the
right
side.
C
This
example
contract
work.
So
let's
say
a
customer
write
a
check,
the
five
ether
redeem,
but
if
a
job
is
done,
let's
say
the
job
is
renovating
his
home,
then
the
contractor,
who
renovated
his
home,
can
get
a
test
station
from
a
third
party
to
a
test.
The
work
is
done
and
then
withdraw
an
uniform
wallet.
C
C
The
check
check
protocol
I'm
presenting
here
is
a
work
work
in
progress,
but
you
already
have
a
protocol
that
protects
the
email
address,
with
a
pedestal,
commitment
and
with
zero
knowledge
proof
the
actual
paper
on
this
process
and
can
be
downloaded
from
somewhere
on
the
web.
I
forgot
to
attach
the
link.
Maybe
later
I
can
ask
the
the
host
to
allow
me
share
the
link
in
the
group
chat
message.
C
C
C
Then
he
can
see
that
this
computer
game
store
can
interact
with
5
tokens,
observe
the
5
tokens
below
the
address
bar
and
then,
if
the
user
activates
one
of
the
tokens,
called
amazing
bundle,
you
can
see
the
price
reduced
from
55
to
about
twenty
dollars,
and
this
is
because
the
bundle
guarantees
that
maximum
gain
price
is
twenty
dollars
for
whatever
game
you
buy,
you
have
to
pay
a
hundred
dollar
per
year
for
to
get
this
bundle.
That
will
be
a
new
business
model
and
this
business
model
can
be
enabled
with
a
test
station.
C
No
blockchain
transaction
has
to
happen
for
this
to
work,
just
the
user's
interaction
with
web
and
in
the
next
picture,
the
user
activated
gamer
credit,
which
is
a
payment
token.
Imagine
you
have
a
new
ico
that
issues
this
token
and
motivation
mechanism
that
people
want
to
have
this
credit
they
can.
C
But
all
these
are
fundamentally
attestations
and
and
then,
if
you
want
to
transfer
them,
it
will
be
blockchain
trans
transaction.
But
if
you
just
want
to
use
it
in
business
process
and
you
can
pretty
much
use
a
signed
message
and
ask
users
to
co-sign
it
and
produce
some
some
proof
and
then
it
would
enable
new
business
models.
I
think
I
can
I'll
end
here
is
that
good.
B
B
B
B
C
B
D
E
Hey
everyone,
so
I'm
tom,
I'm
one
of
the
original
co-founders
and
ceo
of
cordis
a
little
bit
of
history.
So
the
idea
for
I've
been
in
in
blockchain
since
around
2013
been
a
big.
You
know,
fan
of
the
ecosystem
and
back
around
end
of
2017
early
2018,
and
I
started
portis
because
I
saw
a
problem
in
the
ecosystem
where
nobody
could
actually
use
dapps.
It
was
super
complicated
and
when
we
build
the
poorest
solution,
one
of
the
things
that
I
saw
is
key
is
well
using.
E
That
phrase
is
kind
of
funny,
but
what
I
saw
is
key
is
self-custody
of
your
private
key
and
a
lot
of
the
solutions
out
there
had
if
you're
talking
about
stuff
like
like
exchanges,
london
asks
you
to
they'll
hold
your
private
key
for
you
and
you're.
This
is
not.
It
goes
against
a
lot
of
the
things
that
are
the
ethos
of
blockchain
and
it's
also
a
big
security
risk
and
a
liability.
E
On
the
other
hand,
asking
users
to
store
their
private
key
on
something
like
metamask,
which
was
pretty
much
the
only
solution
back
then
beside
you
know
for
users
to
interact
with
apps,
and
that
was
you
know,
that's
kind
of
rough.
In
addition
to
being
technically
very
complicated,
it
also
means
the
user
if
they
lost
their
laptop.
That's
it
it's
gone
forever.
E
So
the
way
we
tackle
this
problem
is
by
using
end-to-end
encryption
and
if
anyone
here
is
familiar
with
lastpass
or
one
password,
it's
kind
of
the
same
just
instead
of
passwords,
it's
your
private
keys.
So
what
you
do
is
everything
is
encrypted
inside
the
device
inside
the
browser.
So
you
create
your
wallets,
you
encrypt
them
locally.
We
store
that
encrypted
blob,
but
we
have
no
way
of
decrypting
it
we're
using
script.
E
100
000
iterations
we're
doing
the
standard
way
that
it's
done
so
unless
you
chose
something
very
poor
like
one
two
three,
there
is
no
way
to
do
a
dictionary
attack
or
anything
like
that.
It
will
just
take
thousands
of
years,
so
users
get
that
experience
of
we
log
in
with
an
email
and
password.
We
have
that
cloud
experience,
so
you
can
log
in
from
your
phone
then
from
your
computer
and
it's
the
same
device.
E
If
you
lost
your
phone,
you
can
just
log
in
again
and
do
whatever
you
want,
but
on
the
other
hand,
it's
your
private
key.
It's
never!
You
know
it's
never
unencrypted
anywhere
else.
Besides
on
your
device,
when
you're
using
it
another
key
feature
was
very
important
for
us
is
being
cross
blockchain.
So,
in
addition
for
supporting
ethereum,
which
is
the
thing
we
did
from
day,
one
because
we're
big
ethereum
fanboys
and
we
believe
a
lot
in
this
ecosystem.
E
E
You
know
types
of
private
keys,
more
blockchains
and
we're
making
sure
that
they
can
also
be
interoperable
in
at
least
from
a
user
experience
perspective.
It
becomes
easier
because
it's
just
the
same
account.
You
have
an
email
and
password
and,
as
you
know,
ship
should
recently
acquired
us.
So
that
also
means
that
if
we
wanna
let
the
user
easily
switch
between
tokens,
we're
making
it
very
very
simple
for
him,
so
they
don't
even
have
to
you
know
deal
with
the
complexity
of
what's
going
on.
We
feel
that
we
need
to
hide
everything
from
the
user.
E
D
E
Have
yeah
great
so
we
have
approximately
100
apps
and
companies
that
are
using
us.
Thousands
of
developers
have
tried
our
sdk
we've
been
very
admin
about
being
very
dev
oriented
from
day
one
and
the
way
we
see
it
is
kind
of
like
a
good
story.
I
think
that
demonstrated
is
the
android
story
where,
because
it
was
very
good
for
developers,
a
lot
of
developers
built
a
lot
of
apps
for
android,
so
android
becomes
stronger,
which
means
more
developers
build
apps
on
it,
etc,
etc.
E
We
always
want
to
make
sure
that
we're
using
the
standards
that
are
out
there,
for
instance,
one
of
the
things
that
from
day
one
we
saw
as
a
problem
and
the
way
we
solved
it
by
the
way
was
kind
of
this.
It's
a
very
classic
and
lean
startup
way
of
solving
it,
which
is
the
gas
fees.
That
was
a
very
big
problem
for
users,
because
they
want
to
just
interact
with
that.
They
want
to
sign
a
transaction.
E
They
want
to
just
kind
of
write
something
to
the
blockchain,
but
now
they
need
to
get
even
if
it's
one
dollar
of
each
because
back
then
transaction
cost
cents
not
dollars
like
they
did
today.
But
even
if
they
need
that
those
couple
of
cents
they
have
to
go
in
an
exchange,
they
have
to
buy
it
and
we
added
direct
per.
We
have
it
like
a
way
of
purchasing
with
a
credit
card,
but
still
that's
a
big
hurdle
for
a
user
to
to
deal
with
that.
E
Even
if
we're
talking
long
term,
that's
someone
else
else
has
to
pay
it.
So
as
a
very
lean
startup
way
of
solving
it,
we
gave
each
user
one
dollar.
We
just
wanted
to
do
an
experiment
and
see
if
that
works,
and
it
did
it
worked
great,
but
it
doesn't
scale.
Obviously,
and
people
will
also
try
to
abuse
it.
E
So
we
wanted
to
solve
it
in
a
more
sophisticated
manner,
but
we
said
you
know
what
let's
wait
for
the
ecosystem
to
take
care
of
that
and
that's
the
gas
station
network
which
solves
it
by
letting
you
three
layers
to
pass
along
the
transaction
and
we
supported.
We
were
the
first
swift
we
provided
to
support
gas
station
network.
Now
the
new
version
is
coming
out,
so
we're
obviously
upgrading
to
it
there's
nft
support.
We
have
the
features
like
trust,
this
app,
which
lets
users
say.
Look.
I
trust
this
application.
E
Don't
ask
me
to
sign
a
transaction
each
and
every
time.
So
just
let
me
say
I
trust
it
and
if
it
goes
above
like
if
I'm
paying
for
something
if
it's
an
actual
payment
or
if
the
gas
fee
is
like
it's
making
like
thousands
of
transactions.
Okay,
maybe
we
need
to
stop
because
there's
like
a
bug
or
it's
malicious,
then
I
need
to
start
proving
it,
but
we're
trying
to
we
get
the
distance
blockchain
and
there
shouldn't
be
trust,
but
that
doesn't
mean
that
you
can't
have
sometimes
a
little
trust
if
you
want
to.
E
It,
doesn't
have
to
be
so
maximized
and
we
added
capabilities
of
direct
purchase,
letting
users
use
their
credit
card
to
buy
something
when
they're
using
adapt
and
we
had
a
provider
where
we
were
in
between
providers
right
now,
so
we
had
to
take
it
off,
but
it's
coming
back
very
shortly.
A
direct
purchase
flow,
for
instance,
again
trying
to
create
this
web
2
experience
for
users,
so
they
don't
really
know
they're
using
blockchain.
Our
whole
mindset
has
always
been
users
shouldn't
care
about
blockchain
because
they
don't
care
about
it.
E
Just
like
they
don't
care
about
the
underlying.
You
know
how
the
internet
works.
They
just
want
to
use
the
applications,
so
the
direct
purchase
flow
allows
a
user.
Let's
say
they
go
on
something
like
god's
unchained:
they
want
to
buy
some
packs,
they
don't
need
to
go
and
purchasing
crypto,
come
back
finish
the
transaction
and
wait
for
everything.
They
just
click
one
button
and
it
goes
through.
We
actually
kind
of
pre-sign
a
transaction.
E
We
never
hold
anybody's
funds,
and
so
there's
that
we're
currently
adding
a
star
wars,
support
for
zk
snarks
for
the
reddit
bake
off
they're,
having
we're
trying
to
always
make
sure
that
the
latest
technology
that
the
developers
we
see
that
the
developers
are
interested
in.
So
we
add
that
if
it's
more
changed,
if
it's
more
standards,
if
it's
more
other
user
experience,
you
know
capabilities.
E
So
we
we
have
a
lot
of
dapps
using
us
and
at
some
point
that's
like
bigger
applications,
bigger
companies,
even
approach
us
and
say:
look
we
love
what
you're
doing,
but
we
want
to
truly
own
it.
We
want
some
white
labeling
so
back
in.
I
think
it
was
around
march
this
year.
So
a
little
bit
earlier
than
that
we
started
to
talk.
We
had
conversation,
we
coined
us.
E
E
There's
a
whole
lot
of
reasons
why
you
don't
really
want
to
hold
anybody's
private
key,
so
I'm
going
to
show
you
a
quick
video
just
to
kind
of
demonstrate.
I
want
to
show
what
can
you
do
once
you
as
a
company?
You
don't
have
to
worry
about
the
whole.
How
do
I
manage
a
user's
private
key
in
a
way
which
is
super
simple
and
also
very
easy?
E
D
E
D
E
Yeah
well,
this
was
created
like
with
a
fake
account,
so
no
worries,
I'm
actually
going
to
show
you
a
c
phrase
as
well.
So
and
yeah,
that's
the
one.
So
if
you
haven't
checked
out
the
shapeshift
mobile
app,
I
said
just
you
give
it
a
try.
It's
you.
You
get
three
dollars
worth
of
bitcoin
for
free,
so
this
is
like
a
standard
onboarding,
as
you
can
see,
and
all
the
user
needs
to
put
in
is
their
email
address.
E
E
We
can
help
you
recover
it
if
you
lose
it.
That's
kind
of
the
tough
part,
but
that's
like
with
great
power,
comes
greatly
responsibility,
aspect
of
it
so
and
the
user.
We
keep
on
bugging
him
telling
them
to
store
their
password
in
a
safe
location.
They
have
a
recovery
phrase
as
well
in
case
they
forget
it
and
we
have
additional
we're
putting
in
additional
safeguards
in
place
like.
E
E
E
Here
we
go
so
he
clicked
on
the
email
and
that
will
kind
of
verify
and
that's
it.
That's
all
you
did
like
email
password,
verify
your
email
a
little
bit
of
onboarding
to
let
you
see
what's
going
on,
but
this
is
a
very
familiar
experience
for
a
user.
This
feels
just
like
using
web2,
and
the
good
thing
about
this
is
that
if
they
suddenly
drop
their
phone
in
the
ocean,
something
happens
they
it
gets
stolen,
lost
smashed,
which
happens
a
lot
of
phones.
It's
not
like
the
private
key
only
lives
on
the
phone.
E
That's
a
very
scary
thought
and
on
the
other
hand
you
know
it's
not
just
like
a
as
long
as
it
doesn't
have
tons
of
value.
Then
they're
not
worried
about
you
know
if
they
didn't
write
down
their
recovery
phrase,
because
if
they
chose
a
password
that
they
easily
remember,
which
is
powerful
enough,
they
can
easily
access
it
from
a
new
device
and
from
another
device
if
they
want-
and
it
can
have
this
cloud.
Experience
of
you
know
a
synchronization
between
all
of
their
devices
and
the
video
shows.
E
The
demonstration
like
a
lot
of
assets
are
supported.
If
it's
ether,
if
it's
bitcoin,
if
it's
cosmos
and
right
now
we're
in
the
process
of
making
this
unification
between
shapeshift
and
portis,
which
means
that
very
soon,
when
you
go
on
all
of
the
depths
powered
by
portis,
you
will
also
have
access
to
all
of
shapeshift's
capability
which
is
moving
between
tokens,
and
that
means
that
you're
going
to
have
a
very
powerful
experience
and
one
last
video
I
want
to
show.
I
hope
I
have
enough
time.
It's
like
a
couple
of
seconds.
B
Go
ahead,
okay,
great
actually
I'll
toss
them
on
a
quick
question.
So
when
I
create
that
password,
that's
going
to
oh
there,
it
is
right
there
I
was
just
going
to
say:
is
there
a
way
you
know
in
the
background,
does
this
generate?
You
know
the
standard.
You
know
14
or
25
word
recovery
phrase
or
is
it?
Does
it
always
stay
as
a
strong
password
and
so.
B
E
Yeah,
of
course,
of
course,
so
there's
there's
two
parts
to
that
question,
because
there
is
the
way
how
we
used
to
do
it
in
porters.
When
we
do
the
shapeshift
integration,
we're
changing
it
a
little
bit
but
actually
making
it
a
little
better.
You
know
in
a
way,
I
would
say
more,
better,
not
cryptographic
wise.
The
cryptography
is
the
same
in
the
sense
of
making
it
sure
that
it
we
never
wanted
to
lock
anyone
in
so
those
12
words
that
you
just
saw.
E
If
you
were
quick
enough,
you
can
take
them
and
they're
not
you're,
not
going
to
have
the
three
dollars
of
bitcoin
by
the
way
you
don't
actually
get
it
until
you
do
kyc.
So
if
you,
if
anyone
here,
wants
to
be
clever,
it's
gonna
be
an
empty
wallet.
So,
but
what
I'm
saying
is
is
that
we
wanted
to
make
sure
that
those
12
words.
If
suddenly,
you
decide,
you
know
what
I'm
fed
up
with
youtube.
I
don't
like
them
or
maybe
you're
afraid
that
shape
shifts
will
disappear.
E
One
day,
those
12
words
will
work
on
any
standard
wallet
out
there.
Okay,
this
is
what
we
call
a
vip
42,
a
recovery
phrase.
It's
completely
standard.
Anyone
out
there
supports
it.
The
way
we
did
the
backup
recovery
phase
report
is,
you
do
have
those
12
words
for
the
different
wallets,
but
the
main
one
is
24
words
that
we
created
for
ourselves
and
it
wasn't
as
standard
so
we
changed
it
for
shape
shift,
but
the
cryptographic
is
the
same.
So
what
happens
when
you
put
in
a
password?
E
What
we
actually
do
is
we
create
a
random
key
when
you
sign
up
for
the
first
time
a
completely
random
key
and
your
password
is
used
and
we
have
a
white
paper
explaining
everything,
it's
a
technical
white
paper,
so
it's
just
like
mostly
explaining
that
flow
of
the
encryption
decryption
and
all
that
nothing
about.
There's
no
token
or
anything
like
that.
So
what
happens
is
that
you
create?
Let
me
stop
sharing
for
a
second.
E
Can
you
see
me
now?
Oh,
stop
sharing
the
screen
yeah.
So
what
happens
is
that
when
the
user
signs
up
they,
we
create
a
random
64-bit
key
for
them.
They
encrypt
it
with
their
password
using
s-script.
The
way
you
do
it
with
s-script.
It
makes
sure
that
it
cannot
be
brute
force
with
a
password,
so
it
takes
like
if
I
don't
know
the
password
and
I
try
to
brute
force.
E
It
will
take
me
thousands
of
years
to
try
and
brute
force
it
even
with
like
the
strongest
computers
so
and
then
that
private
key
that
we
generate
completely
randomly
that
is
used
to
encrypt
those
12
words.
So
what
happens
is
that
you
send
us
back
your
encryption
key
and
your
encrypted
blob,
which
is
your
12
words
we
hold
on
to
those,
but
we
can't
really
do
anything
with
them,
because
the
the
encryption
key
was
encrypted
using
script
with
your
password.
E
We
we
can't,
we
don't
know
your
password,
we
never
know
your
password.
This
is
the.
This.
Is
the
only
user
experience
difficulty
that
we
have
here,
but
it's
it's
a
it's.
We
see
it
as
a
necessity.
If
you
want
to
maintain
self-custody
is
the
fact
that
if
you
forgot
your
password-
and
you
don't
have
your
recovery
phrase-
we
can't
help
you,
but
I
think
that's
also
a
good
thing,
because
in
a
way
what
this
means
is
that
you
know
you
have
complete
control
of
your
private
key.
E
So
we
hold
on
to
that
encrypted
private
key
and
we
hold
on
to
that
encrypted
blob
that
encrypted
blob
of
your
seed
phrase,
which
you
encrypted
with
that
private
key.
So
when
you
want
to
log
in
you
get
back
your
encrypted
blob,
you
get
back
your
encrypted
private
key.
You
decrypt
that
that
that
private
key
that
key,
that
you
encrypt
everything
with
you
decrypt
it
with
your
password
and
now
you
can
decrypt
your
blob
and
you
can
do
everything
you
want,
and
you
have
this.
You
know
access
to
everything.
B
B
I
certainly
remember
the
first
time
I
typed
my
credit
card
into
amazon
and
I
was
just
like
all
right.
Well,
that's
it.
Like
all
my
money's
gone,
I
don't
know
what's
going
to
happen,
but
the
way
that
blockchain
works
and
the
beauty
of
it
and
the
power
of
it.
It
is
the
strong
encryption,
and
so
this
this
concept
of
you
know,
do
you
think
people
are
ever
going
to
get
used
to
this.
B
This
notion
of
you
know
if
you
lose
that
password
or
if
you
lose
that
private
key.
You
know
your
funds
are
gone.
I'm
sorry,
didn't
you
read
the
little
note
at
the
beginning
or
if
you
send
a
transaction
to
the
wrong
address
it
it's
gone
and,
and
so
that's
both
scary
and
dangerous.
But
that's
also
one
of
the
reasons
that
this
technology
is
powerful.
Like
are
people
going
to
get
used
to
that
like.
D
E
Well,
yeah,
that's
a
great
question,
but
you're
kind
of
like
a
a
technical
person,
probably
an
early
adopter,
you're
you're,
not
the
person
that
we're
actually
worried
about,
and
this
was
always
what
we
when
we
talk
about
poorest
to
other
people.
This
is
always
like
these
two.
You
know
orthogonal
vectors
of
usability
and
security
and
on
one
spectrum,
there's
like
a
hardware
wallet.
You
know
a
hardware
wall
is
the
most
and
I
keep
telling
people
look.
If
you
got
a
million
dollars
use
a
hardware.
E
Wall
use
a
keepkey,
for
instance,
that's
the
shapeshift
hardware
wallet,
and
that's
because
our
encryption,
it
doesn't
work
well.
Well,
because
our
encryption
runs
on
this.
It
runs
on
a
phone.
It
runs
on
a
laptop.
These
things
have
an
attack
surface
which
is
much
bigger
than
a
dongle
which
is
never
connected
to
the
internet,
and
it's
super
super
secure
it
does.
It
does
a
very
specific
thing
and
it
does
it
well.
E
You
know,
there's
no
me
you
can
never
make
mistakes.
We're
just
kind
of
trying
to,
I
say,
grind
the
corners,
so
you
can't
really
hurt
yourself
with
that
and,
for
instance,
the
hall
forgot.
The
pack
forgot
my
password
issue,
so
I
mentioned
that
in
the
sense
that
when
you
start
off,
I
don't
want
to
bug
you
too
much,
because
if
I
also
bother
you
too
much
then
you'll
just
ignore
me.
E
It's
like
a
kid
who
cried
wolf,
but
once
I
see
that
you
have
let's
say
a
thousand
dollars,
two
thousand
dollars
worth
of
value
in
your
wallet,
then
I
maybe
start
bugging
you
a
little
bit.
Make
sure
you
forget
your.
You
remember
your
password.
Make
sure
that
you
know
you
wrote
down
your
recovery
phase,
and
this
is
like
part
of
a
bigger
thing
that
we're
offering
you
know
all
together
when
you're
using
a
package
like
portis.
So
if
you're
a
company
adapt
an
enterprise
and
you're
building
a
dap,
you
have
enough
on
your
plate.
E
D
E
Can
build
your
own
text
messaging
solution?
Sure
you
can
do
that,
but
but
why
I
mean
it'll
cost
you
more
you'll
have
it's
kind
of
like
that
classic
story
about
developers
when
a
classic
developer
mistake,
a
rookie
developer
is
implementing
the
daytime
themselves.
It
seems
super
simple
right.
It's
day
time,
then
you
learn
about
how
does
daylight
savings
work
in
different
countries
and
all
kinds
of.
C
Well,
I
think,
a
lot
of
since
we're
talking
about
enterprise
sector.
I
think
a
lot
of
the
existing
key
management
solutions
can
a
good
bit
of
it,
but
not
entirely
can
be.
It
can
be
used
on
blockchain
as
well.
So
so
one
thing
you
just
mentioned
key
recovery.
So,
for
example,
there
are
secret
sharing
based
key
management
solution
and
that
can
be
reused
as
a
key
recovery
mechanism.
C
C
That
is
largely
ignored
because
blockchain
was
so
young,
that
is,
the
keys,
have
gone
style.
So
the
the
assumption
is
that
if
you,
the
key,
has
been
around
for
a
long
time,
then
you
can
pretty
much
assume
some.
Some
people,
not
in
your
company,
have
the
key
because
it
could
be
in
usb
stick
that
when
they
left
it
on
the
on
the
on
the
presentation
table
and
some
interns
student
pick
it
up
and
they
deliver
it
to
me
midnight
so
that
I
can
use
my
money
and
he
could
have
made
a
copy.
C
So
there
is
no
mechanism
available
today
to
revoke
a
key.
You
can
certainly
transfer
all
your
money
to
a
new
key,
but
that
requires
every
contract
that
has
your
money
or
crypto
asset
allows
you
to
transfer
to
a
new
key.
So
there's
no
underlying
layer
that
allows
you
to
transport
an
asset
without
transport
transporting
assets.
Give
you
the
access
new
key.
I
think
this
is
going
to
be
a
problem
in
a
few
years.
Now
it's
where
we
are,
but
eventually
I
have
not
solved
it
from
the
wallet
along.
E
We
should
be
careful
about
maintaining
the
old
paradigms
that
we
have
and
having
a
key
management
store
for
an
enterprise.
I
think
in
a
lot
of
ways
it's
kind
of
like
you
know
how
sometimes
companies
use
blockchain,
but
they
don't
really
need
blockchain
that
that
happens.
Sometimes
it's
a
very
pop.
It's
sometimes
very
kind
of
tempting
to
do,
because
you
want
to
you're
very
excited
about
using
this
new
technology
and
a
lot
of
times.
E
Exactly
it's
like
it's
like
a
problem.
Looking
for
it's
like
a
solution
looking
for
a
problem
and
but
when
there
is
an
actual
thing
you
want
to
use
blockchain
for,
because
you
have
a
real
problem
of
trust
like
supply
chains,
etc.
It
doesn't
really
make
sense
that
any
one
of
those
entities
can
hold
the
private
keys
in
their
servers
for
a
couple
of
reasons.
E
C
That's
not
what
I
mean
by
having
a
layer
for
key
replacement.
That
is
not
delicate
key
to
someone,
but
to
have
let's
say
a
lower
level.
Blockchain
call
call
that
can
allow
you
to
have
a
new
key
tested
by
the
old
key
and
send
it
across
the
network.
And
then
everybody
start
to
recognize
the
signature
from
the
new
kit
officer
operate
all
that's.
It.
E
Yeah
there
are
ways
to
do
that
also
with
ethereum
smart
contract.
This
that's
something
that
we
explored
back
in
the
past.
So,
instead
of
just
having
a
wallet,
you
have
a
smart
contract
and
then
you
can
have
like
in
a
way
kind
of
like
you
have
an
administrator
or
a
power
user,
or
just
a
user
or
visitor.
You
can
have
different
keys
to
manage
one
master,
private
key
that
can
do
stuff
in
smart
contracts.
You
maintain
one
identity.
E
E
So
one
of
the
adapts
using
port
is,
for
instance,
it's
a
y
combinator
that
it's
called
the
multis
multis.co,
if
I'm
not
mistaken,
so
they're
handling
multi-signatures
for
enterprises
for
big
companies
that
need
to
handle
crypto
funds
and
want
to
have
an
easy
system
of
you
know.
You
have
your
board
and
you
have
five
people
and
three
out
of
five
people
can
sign
a
transaction.
It's
like
a
multisig
wallet
but
on
steroids,
because
you
need
a
lot
of
just
like
when
you're
using
sas
products
and
you
have
a
nice
dashboard.
E
C
About
that
is,
potentially
you
can
have
a
multisig
and
ecdsa
multisig
without
changing
the
contract,
because
there
are
underlying
protocols
that
allows
you
to
do
this,
so
it's
transparent
to
the
blockchain.
It
gives
a
little
bit
of
flexibility
to
enterprise
and
yeah
with
its
own
problem,
but
yeah
it's
possible
to
not
change
the
contract
too
much
and
just
offer
it
from
the
wallet
perspective.
B
B
C
This
lab
stuff,
which
which
which
requires
you
to
make
a
product
in
six
months
or
three
months,
and
they
always
point
with
this
trap.
So
there
are
always
people
who
wants
to
do
this,
but
the
the
right
way
to
look
at
it
is
not
not
on
the
okay.
If
you,
if
you
cannot
solve
the
problem
between
two
parties,
then
let's
have
a
big,
bigger
party
that
covers
both
that
that's
a
traditional
management
thinking.
C
It
wouldn't
work
when
you
go
across
the
corporate
boundary
and
even
in
large
organizations
like
in
the
bank,
bank
or
blockchain
architect
for
two
years,
even
in
the
bank,
there's
a
boundary
that
you
cannot
form
a
bigger
party
between
two
banks
when
it
comes
to
two
banks:
interchange
assets.
So
when
the
problem
comes
to,
when
there's
problem
like
that,
rolling
back
is
one
of
the
things
that
could
be
done
by
a
consortium,
but
the
practical
ways
to
use
the
technology.
C
We
call
it
dvp
security,
so
dvp
security
is
instead
of
calling
smart
contract
and
letting
smart
contract
do
the
job.
You
would
run
the
smart
contract
yourself
and
compute
the
result
and
you
write
your
result
as
a
requirement
for
the
transaction
to
be
executed
successfully
and
then
post
that
through
the
blockchain.
Therefore,
you
have
less
trust.
Trust
problem
with
the
other
party
and
the
other
party
can
probably
even
take
your
what
we
call
a
dvp
attestation
to
the
next
level
with
next
market
and
still
carry
carry
on
execution.
C
C
A
C
Dvp
security,
guarding
the
smart
contract,
so
this
reduced
the
chance
you
need
to
have
a
consulting
rotates
back
and
across
the
key
management
is
popular,
especially
let's
say
in
the
banks.
They
have
a
specialized
department
to
do
this
and
the
special
signing
devices
that
can
send
millions
a
time,
but
it
doesn't
go
through
organizational
boundary,
and
I
would
still
say
that
if
you
can
find
the
entity
who
can
do
this
for
the
organizations,
then
you
don't
need
blockchain.
It's
the
requirement.
C
B
Yeah
yeah
yeah,
I
I
gosh
when
was
that
it
was
around
2002.
I
actually
wrote
a
patent
at
microsoft
that
allowed
companies
to
share
share
their
private
keys,
so
they
could
do
email
across
separate
domains
across
different
company
entities,
and
it
was
like
now
that
I
look
back
at
it.
It's
terrible
what
a
terrible
idea!
C
Google,
I
asked
you
to
upload
your
key
to
the
google
play
store
so
that
they
will
sign
new
release
on
your
behalf,
and
their
idea
is,
we
are
going
to.
You
know
only
take
the
relative
section.
So
if
this
guy
is
running
a
low-end
mobile
phone,
then
we
don't
provide
high-end
assets.
We
just
recompile.
We
can
recon
re-reassemble
your
data
and
then
we
need
your
keys
to
send
the
new
stuff.
That's
not
an
excuse.
You
can
produce
a
multi-signed
file
locally.
C
You
can
send
it
a
hundred
times
for
different
devices
and
or
upload
to
google,
or
you
can
even
use
merkle
tree
so
that
you
can
send
portions
of
it.
You
can
send
a
big
signature
that
covers
one-handed
portion,
so
so
I
think
they
just
don't
want
to
use
that
new
technology.
I
think
they
just
just
think
that
the
trust
problem
is
easily
solved
by
you
past
me
that
that's
it.
E
I
think
I
think
enterprises
are
also,
and
rightfully
so,
because
you're
usually
moving
a
very
big
ship
they're
a
little
bit
scared
of
new
technology
that
hasn't
been
tried
and
tested,
and
why
I'm
excited
about
about
the
space
right
now
is
because
we're
seeing
more
and
more
solutions
that
are
you
know
getting
are
have
been
tried
and
tested.
If
obviously
d5
that's
really
exciting
right
now,
but
also
you
have
stuff
we're
talking
about.
E
How
do
you
manage
so
dows
have
been
around
for
quite
a
while,
and
a
lot
of
companies
are
starting
to
use
them
in
very
interesting
ways
and
that's
another
way
in
a
sense
to
do
q
recovery.
You
can
use
dao,
you
can
create
your
own
contract
and
write
something
new,
but
I
think
a
lot
of
enterprises
you
know
rightfully
so
will
be
a
little
bit
wary
to
be
the
first
ones
to
try
out
this
new,
potentially
vulnerable,
or
you
know
something
that
hasn't
been
tried
by
tons
of
organizations.
Yet.
E
They
will
be
in
some
some
sort
of
smart
contract
where
that
private
key
has
access
to
it,
especially
when
we're
talking
about
d5,
it's
not
it's
the
token.
The
ethereum
is
going
to
be
the
gas,
the
theorem
right
now
that
people
are
holding
in
their
wallets
it's
because
of
speculation,
and
they
want
to
have
you
know.
I
I
personally
don't
necessarily
believe
that
ethereum
is
going
to
be
the
new
money.
I
always
viewed
it
as
oil
like
bitcoin,
is
the
gold
gold.
The
theorem
is
the
oil
and
you
know
buying
barrels
of
oil.
E
C
Important
point
on
enterprise
key
management
that
is
in
another
press
setting.
You
actually
don't
usually
recover
the
key,
so
the
the
the
the
keys
are
not
recovered.
Kids
are
reclaimed.
So
if
you,
if
you
simply,
whenever
there's
a
problem,
you
make
a
new
key
and
then
you,
you
assume
all
the
rights,
the
new
key,
you
don't
otherwise,
there's
a
company.
You
should
incorporate.
E
Exactly
exactly,
I
agree
and
that's
why
I
think
in
a
way
having
this
self-custody
for
your
employee
and
making
sure
they
have
it.
If
you
have
a
way
of
recovering
it,
I've
given
them
a
new
one,
but
it
could
be
proven
that
it's
a
new
one
so
that
that
old
one.
If
something
was
done,
you
know
that
you
couldn't
touch
it
and
once
you
reclaim
it,
there
could
also
be
a
process
in
place
that
the
user
then
signs
for
it
or
something,
and
there
are
different
ways
of
doing
it.
E
So
you
know
that
once
the
user
got
that
new
one,
that's
it
it's
only
his
and
you
never
were
able
to
actually
see
it
like
he
can
generate
a
new
private,
key,
privately
sign,
something
and
then
you're
saying
then
the
the
enterprise
will
say.
Okay,
we
allow
this
private
key.
The
signal
that
was
signed
the
time
this
message
from
now
on
that
new
private
key
has
access
to
everything,
because
we
voted
on
it
with
the
dow
and
we
say:
okay,
that's
cool.
E
We
trust
this
new
person,
so
you
can
find
ways
of
having
a
way
to,
like
you
said
not
to
weak,
not
to
restore
a
private
key
but
reclaim
a
private
key,
but
still
making
sure
that
as
an
enterprise,
you
don't
have
the
legal
liability
and
all
the
headaches
that
come
along
with
holding
private
keys.
That
was
one
of
the
main
reasons
why
we
did
it
early
on
reporters
were
like.
We
don't
want
to
deal
with
all
the
legal
issues,
in
addition
to
other
considerations
of
having
I'm
holding
people's
private
keys.
E
B
B
B
C
And
a
common
pattern,
when
that
happens,
is
that
actually,
I
demonstrated
in
my
slide
a
little
bit.
The
common
pattern
is
that
is
instead
of
sending
money
or
doing
transactions
to
a
specific
key.
You
do
it
to
an
identifier
and
then
later
the
identifier
holder
holds
a
test
station
to
show
that
his
key
is
associated
with
that
identifier
and
therefore
it
separates
the
key
management
process
and
transaction
process.
C
C
Then
bob
goes
to
a
tester
and
the
test
that
he
owns
that
email
address.
Well,
given
that
email
address
is
easier
to
attack
the
ethereum,
it's
probably
not
a
good
idea
for
large
amount
of
transaction,
but
this
pattern
separates
the
the
the
testing
obligation,
the
the
the
comfortable
accountability
thing
with
the
transfer,
which
is
the
financial
thing.
C
It's
it's
a
it's.
The
patterns
that
emerges
quite
often
in
business
scenario,
while
I
was
experimenting
on
blockchain
projects
in
commonwealth
bank
in
australia,
so
so
so
much
it
occurred
so
so
frequently
that
I
decided
to
make
a
particle
out
of
it
and
in
the
public
key.
A
lot
of
things
have
to
change,
because
in
public
ethereum
you
have
to
protect
the
user's
identifier,
and
so
there
you
go
with
all
the
crypto
magic
I
provide
the
link.
D
E
B
Go
ahead,
no,
no
I'm
just
gonna,
say
teresa
as
we
get
down
to
the
to
the
final
minutes.
Here
I
didn't
see
any
questions
in
the
chat
that
we
hadn't
kind
of
covered,
and
I
wonder
if
there
we
go
apps
app
supporters,
dot
io.
I
did
have
a
bunch
of
questions
on
on
the
different
apps
that
you
guys
are
seeing
and
like
are
they
you
know?
Are
they
integrating
with
your
platform
or
are?
Are
they
extending
it
in
some
way?
B
A
B
C
I
provided
earlier
that
the
core
necessity
for
token
script
is
the
capacity
to
securely
pass
the
code
to
operate
with
smart
contract
to
a
different
website
where
you
can
use
tokens
to
do
the
two
two
main
things
that
we
use
token
to
do
at
all.
That
is
first
reduce
market
friction,
so
more
chain.
More
deals
can
be
done.
Third
help
of
your
token.
The
second
is
allow
integration
so
that
your
token
works
on
other
web
systems.
E
E
It's
like
this
grand
open
api
that
everybody
can
communicate
with
and
we're
trying
to
make
this
very
simple
for
users
to
be
onboard,
because
the
more
users
are
on
the
system,
the
more
we're
going
to
be
seeing
this
interoperability
take
place,
and
it's
also
going
to
be
relevant
for
enterprises
as
well,
because
there
are
also
going
to
be
a
lot
of
enterprises
in
the
world
who
are
going
to
be
building
a
lot
of
applications
and
even
regular
people.
If
it's
on
the
public
blockchain
can
interact
with,
I
don't
know
coca-cola
supply
chain
they
can.
E
B
B
Token
program,
hey,
I
sure,
do
I
sure
do
appreciate
it.
You
guys.
I
know
we
didn't,
do
a
dry
run
or
anything
like
that,
but
the
conversation
went
really
well
and
I
sure
do
appreciate
it.
I
actually
would
would
like
to
maybe
continue
this
conversation
at
some
point,
maybe
maybe
here
again
in
an
eea
webinar
a
little
bit
later,
but
I
certainly
do
want
to
thank
you-
and
I
guess
we're
a
little
bit
over
time,
but
that's
okay,
teresha
was
there.
Was
there
anything
else.
A
Yes,
thank
you
and
tom
for
joining
us
today.
I
want
to
reiterate,
with
tom,
said
as
well:
we
enjoyed
having
you,
please
feel
free
to
place
your
social
media
handles
in
the
chat
so
that
all
attendees
can
follow
your
work
and
for
our
attendees.
If
you're
more
interested
in
all
the
leading
blockchain
work
going
on
in
eea,
please
feel
free
to
reach
out
to
our
membership
director
jack
lee
or
send
an
email
to
our
membership
at
enth
alliance.org.
