►
From YouTube: IETF96-SUPA-20160721-1830
Description
SUPA meeting session at IETF96
2016/07/21 1830
A
We're
just
starting
to
hand
out
the
blue
sheet,
so
please
make
sure
that
you
sign
the
blue
sheet
before
you
leave
the
room.
We're
check
a
few
times
during
the
meeting
to
make
sure
that
everyone
touches
signing
the
blue
sheets
and
perhaps
where
they
are.
We
had
a
volunteer
already
on
the
list
for
the
minute
taker
today.
I
think
we're
like
see
are
you?
Are
you
still
able
to
use
your
fingers
this
evening?
You
haven't
been
using
your
keyboard
too
much.
Can
you
be
our
minute
taker?
Okay?
A
Well,
we've
got
and
Neville
taking
notes
as
well
and
I'll
take
some
notes,
so
we
should
have
that
covered,
but
it
would
be
nice
if
we
had
a
jabber
scribe
so
up,
Adrian
sat
in
the
seats
in
the
hot
seat,
so
great
Thank,
You
Adrian,
so
we
have
a
one-hour
session.
This
is
the
agenda,
we're
going
to
start
with
our
current
working
group
documents.
So
let's
kind
of
use
this
as
a
quick
status
update
now
so
congratulations.
We
now
have
to
work
in
group
documents
commiserations.
A
We
now
have
to
working
with
governments,
so
this
is
our
generic
policy
information
model
document.
This
was
kind
of
an
optional
document.
It
was
something
that
was
discussed
in
charger
in
the
milestones,
but
it
seemed
that
the
previous
ITF
it
was
a
document
that
people
were
willing
to
read
and
work
on.
So
we
decided
to
adopt
this
particular
piece
of
work
as
our
first
item.
A
We
recently
closed
the
pole
and
adopted
the
data
model
dot
document,
so
we
now
have
some
sort
of
tangible,
concrete
pieces
of
work
that
we
really
need
to
kind
of
polish
and
work
on,
and
we
will
talk
about
these
documents
and
the
challenges
and
and
what
would
like
to
see
with
these
documents
during
today's
session
we
also
have
a
discussion
from
will
highlighting
the
framework
proposal.
We
had
two
documents
presented:
welp
sent
to
the
list
discussed
a
brief
discussion
last
week
by
Burt.
Thank
you.
A
A
Actually,
sorry
georgius
is
going
to
be
presenting
that
the
the
agenda
on
the
website
is
actually
accurate.
These
slides
are
not
accurate,
so
update
that
and
then
finally
rakesh
do
we
have
Rakesh
in
the
room.
I
saw
you
yet
earlier
great,
so
Rakesh
is
going
to
present
some
work
and
there's
maybe
some
applicability
or
overlap
or
cross
fertilization
between
I
to
NSF
and
super.
So
this
is
everyone
happy
with
the
current
agenda.
Are
there
any
changes
or
requests?
C
B
D
B
So
hi,
my
name
is
John
stroessner,
and
this
is
an
unreadable
screen,
but
now
it
is
thank
you.
This
is
the
supe
generic
policy
information
model
and
a
it
works
yay.
This
first
slide.
There
were
still
some
questions
about
G.
Do
we
really
need
an
information
model
or
not?
And
so
this
slide
is
saying:
it'd
really
be
nice,
because
otherwise
you
have
two
problems
both
of
them.
Interoperability.
B
First
problem
is
that
you're
going
to
have
different
types
of
policies
from
different
actors.
The
second
is
that
because
of
that,
you'll
have
different
types
of
grammars
terminology
and
concepts
used.
A
resulting
con
problem
is
that
unless
we
have
an
information
model
to
normalize
concepts,
if
we
want
to
reach
out
to
chef
or
puppet
or
ansible
or
AWS,
etc,
it's
going
to
be
rather
difficult
to
do
in
the
interest
of
time.
B
We
renamed
and
redesigned
one
of
the
classes
called
supe
vendor
decorated
component.
It's
not
it
wasn't.
Really.
We
decided
that
making
it
vendor
specific
was
really
too
hard
for
right
now
and
in
the
interest
of
time
we
wanted
to
make
it
more
generic,
which
made
more
sense
anyway.
So
we
made
those
changes.
We
responded
to
questions
in
the
mailing
list.
B
We
did
some
final
relationship
fine-tuning
to
make
the
yang
easier
and
we
built
a
gang
model
from
the
information
model,
then
to
go
from
dash
0
0
of
the
working
group
draft
201
in
honor
of
Monty
Python
and
a
now-deceased
parrot.
The
declarative
model
has
ceased
to
be.
The
introduction
was
rewritten
and
clarified.
We
did
one
final
major
redesign
of
the
metadata
class
other
than
that
the
model
is
stable.
B
We're
experimenting
with
adding
a
couple
of
small
classes
to
take
care
of
the
problems
that
one
has
with
null
in
implementations
that
will
be
in
debt,
the
next
version,
but
other
than
that
the
content
is
stable.
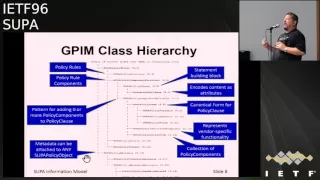
This
is
the
GPM
taxonomy,
so
there
is
yay
so
here
at
the
top
of
the
tree
right,
you
have
policy
policy
structure
is
the
superclass
for
building
policy
rules
and
then
policy
component
structure
is
the
superclass
for
building
components.
That
can
be
put
inside
a
policy
rule
the
other
major
classes.
B
Here
under
policy
components,
you
have
a
policy
clause
which
is
the
basic
building
block
for
building
statements
that
are
policies.
You
have
a
decorator
which
enables
us
to
add
zero
or
more
checks
or
portions
of
objects
to
a
policy
clause
and
that
that
is
an
implementation
optimization,
because,
instead
of
requiring
all
of
the
attributes
for
a
class
to
be
added
at
runtime,
I
can
pick
off
an
attribute
here,
a
method
there.
It's
a
well
established
pattern
used
in
Java
and
Python
and
other
languages,
and
we've
imported
it
for
policy
clauses.
B
Next
steps
there's
one
last
software
pattern
that
we
want
to
put
in
as
a
completely
optional
set
of
classes
to
protect
from
the
nastiness
of
knowles
and
give
a
more
generic
error
handling
capability
for
the
data
model
and
the
main
work
of
four
dash.
0
2
is
going
to
be
adding
lots
and
lots
and
lots
of
examples,
and,
as
always
feedback
is
welcome.
That's
it
questions.
I
guess:
I'm
I
should
have
been
faster,
David.
E
B
F
Okay,
thank
you.
John
I
will
now
briefly
talk
about
the
data
model
because
there
isn't
a
lot
to
say.
We
took
the
00
of
the
adoptive
data
model.
Draft
is
just
exactly
the
same
as
the
last
draft.
That
was
it
was
under
my
name,
so
there
are
no
changes
there.
So
there's
nothing
for
me
to
discuss
in
that
regard.
We're
working
on
building
a
01,
so
we
say
we
have.
We
haven't
actually
managed
to
get
the
01
up
there.
We
were
hoping
to.
F
We
didn't
quite
make
it,
so
we
had
it
where
we're
in
the
process
of
adding
explanatory
text
on
how
the
yang
was
constructed.
There
are
some
pieces
in
the
yang
itself
that
sort
of
suggest
what
we
did,
but
we
need
to
actually
put
in
all
of
the
explanation
that
says
we
took
the
information
model
and
here's
what
we
did
to
construct
the
data
model,
to
make
it
easier
for
you
to
read
the
ayah
the
data
model
or
to
understand
the
relationship
between
the
two.
F
Whichever
way
you
want
to
deal
with
it
and
the
process
of
construction
is
a
human
algorithmic
transform,
it
is
probably
the
case
you
could
get
ninety-five
percent
of
the
way
there
with
a
machine
transform.
If
you
could
process
the
X
the
UML,
but
we
just
did
it
by
hand,
and
we
will
do
the
updates
to
bring
the
dash
L
1
into
alignment
with
the
changes.
Jon
just
talked
about
by
hand,
because
we
don't
expect
to
have
lots
of
complicated
issues
there.
So
these
two
slides
just
got
reversed.
F
This
should
have
been
the
first
slide.
I,
don't
know
how
that
happened.
My
apologies,
the
point
is,
you
have
the
00
it.
It
only
appeared
yesterday
because
we
submitted
it
last
week
with
the
ad
approval.
Only
the
secretary.
It
was
too
busy
to
actually
do
the
ad
approved
submission
during
the
block
and
we
didn't
realize
it
haven't
gone
through
when
we
finally
realized
it.
F
This
relies
very
heavily
on
inheritance
structures
which
are
have
to
be
represented
a
different
way
as
I
discussed
last
meeting,
so
all
modeling
changes
will
be
done
to
both
the
IM
MDM.
So
if
you
look
at
the
modeling
use,
whichever
document
you're
more
comfortable,
looking
at
tell
us
what
modeling
issues
you
find,
we
will
make
sure
it
gets
applied
in
both
cases.
You
don't
need
to
worry
about.
Do
I
need
to
send
you
the
comments
twice.
No,
just
tell
us
what
your
what
issues
you
find.
F
The
working
group
discusses
what
the
working
group
tells
us
to
do
to
the
model
we
do.
We
will
make
sure
it's
there
obviously
gang
problems
if
you
find
specifically
that
this
yang
doesn't
work
or
it's
the
wrong
way
to
do
it
say
so.
We'll
fix
the
annular
the
data
model
and
if
you,
if
the
working
group
says
I,
you
shouldn't
be
using
enumerations,
you
should
be
using
integers
for
something
fine,
we'll
do
that
and,
as
I
said,
we'll
add
explanatory
text
we're
working
on
trying
to
find
the
right
balance
between
the
detail.
F
We've
got
in
the
IM
and
we've
got
a
lot
of
detail
there.
I
don't
want
to
repeat
all
of
that
detail
in
the
yang
model,
but
we
want
to
put
enough
information
enough
description
into
the
DM
that
a
reader
can
have
a
reasonable
understanding
of
what
they're
doing
there
it'll
say
for
further
details,
see
the
IM,
but
there
has
to
be
a
reasonable
level.
F
F
F
H
B
Are
toying
with
the
idea
of
actually
going
from
what
we're
to
software
and
I
don't
know
if
we
could
make
it
by
soul,
but,
as
Joel
said,
when
you
look
at
the
yang
you're
going
to
be
struck
with
G
there's
a
pattern
here
where
there's
actually
three
patterns
in
the
yang.
So
therefore
we
should
be
able
to
build
software.
If
we
do
build
software
and
it
actually
works,
then
we'll
either
put
it
in
well.
B
We
would
obviously
put
in
github,
but
we
probably
put
it
in
one
of
the
hackathons
you
know
with
yang,
so
that
other
people
can
look
at
it
and
say
gee.
How
good
is
this?
Can
we
take
other
information
models
and
use
that
to
generate
reasonable
yang,
so
keep
your
fingers
crossed
and
we'll
see
what
happens.
I
Bethania,
so
if
I
had
to
implement
the
datum,
all
I
my
understanding,
Ross,
we
have
the
information
model
so
that
if
people
want
to
model
it,
the
data
using
yang,
maybe
SMI-
maybe
go
by
or
maybe
something
else,
I
have
no
something
in
the
future.
I
don't
know,
that's
why
we
have
the
information
model
and
I
thought
that
I
would
hope
that
if
we
have
a
data
model
that
comes
out
of
that
based
on
the
information
model,
I
understand
that
that
it
would
be
a
standalone
document
that,
if
I
want
to
implement
I
would
hope.
F
F
We
will
put
in
enough
information
that
the
DM
will
be
understandable
and
should
be
implementable.
You
shouldn't
need
to
unplug
the
objects
but
tip
them
at
the
whole
system.
There's
probably
going
to
be
information
in
the
IM.
From
my
perspective,
it's
much
easier
to
work
with
the
IM
in
terms
of
understanding
information
structure
for
other
people.
The
DM
is
easier
to
work
with,
so
you
can
give
you
can
do
either
one
for
understanding
the
information
relationships,
but
some
information
relationships
are
not
represented
in
yang
and
so
I
can't
do
anything
about
that.
F
J
Not
Amish,
connellan
and
I
need
to
read
all
this
as
well,
but
we
with
with
SMI
and
the
GTMO,
which
was
information
model,
the
language
that
expressing
information
models
for
some
of
the
standard,
mid
modules
who
went
kind
of
used,
the
kind
of
two
types
of
tube
methods
and
no
I,
don't
know
if
they're
any
of
those
are
possible.
One
of
them
was
actually
including
relationship
with
the
information
model,
Claude
section,
which
actually
was
basically
tables
of
mapping
of
objects,
including
their
inclusion.
J
F
Data
model
will
be
complete.
The
only
question
is
how
much?
How
do
you
we
get
enough,
descriptive
text
to
be
useful
without
copying,
for
both
things
that
have
all
of
the
details
and
that's
take
a
look
at
that
part.
Isn't
there
yet,
but
do
take
a
look
at
the
data
modeling
and
the
information
modeling
and
say:
is
this
readable
data
modeling
thing
there
are
deep.
F
All
the
details
are
currently
in
the
IM,
as
I've
said,
we
do
need
to
put
significantly
more
detail
into
the
yang
draft
I'm,
not
saying
we're
going
to
leave
all
of
the
details
in
the
IM,
because
it
does
need
to
make
sense
to
be
coherent
as
a
data
model
document.
It's
just
a
question
of
how
much
detail
we
put
in
how
much
explanation
so
as
I
say,
expect
mostly
examples
to
be
in
the
IM,
but
there
will
be
enough
examples
that
you
know
how
the
yang
works
and
you're
not
left
going.
What
is
that
yang?
F
G
This
is
fine,
but
I
want
to
also
make
a
statement
that
we
we
have
some
sort
of
deadline
to
make
it
easy
for
the
working
group,
like
you,
know
the
deadline
for
submission
and
for
two
drafts
right.
Did
this
one
you're,
the
one
for
sure
the
updated
like
this
week,
and
you
also
still
the
one
from
the
prius
ITF.
So
you
know
maybe
we
want
to
and.
F
While
we
were
asked
to
change
the
document,
we
were
posting
the
00
and
we
were
also
waiting
for
everybody
to
agree
on
the
existing
document
before
we
started
making
changes
because
we
needed
to
keep
the
existing
document.
So
we
could
post
till
I
was
trying
to
work
with
what
I
was
asked.
We're
going
to
make
changes,
we're
not
going
to
wait
till
the
next
meeting
to
post
any
changes,
we're
going
to
use
the
list
and
try
to
get
things
moving
a
lot
faster.
A
D
Okay,
this
is
will
from
highway,
so
I
presented
es
el
super
policy
management,
our
framework
and
thanks
to
do
all
the
author's
efforts
we
have
this
on
draft.
So
first
of
all,
I
will
talk
about
a
little
bit
about
the
background.
So
first
you
can
see
the
position.
Is
that
really
the
behind
the
schedule
actually
arm?
So
this
should
be
submitted
the
earlier
and
the
history
about
this
draft
came
to
quite
a
long
time.
D
So
I
want
to
talk
a
lot
about
the
details,
but
just
on
before
I
mean
super
was
created,
we
have
to
draft
from
my
colleague
drafted,
miss
Jo,
and
this
draft
are
I'm
a
prior
prior
to
the
what
created
and
in
14th
and
15th,
and
next
we
thanks
to
Maxim
from
2f.
We
have
a
super
value
proposition.
This
is
enter
the
suggestion,
I
mean
from
the
working
group
and
the
cheers
and
the
deer.
D
We
have
a
brief
section
about
the
framework,
very
simple
one
and
then
in
this
year
earlier
on
april,
we
have
a
on
because
on
the
yummy
Maxim
change,
the
work
so
I
mean
change
that
responsibility.
So
I
lead
this
new
draft,
which
is
on
on.
We
formally
replaced
the
very
beginning,
the
first
one
they
drafted
Joe
and
we
modified
according
to
the
latest
discussion
and
we
add
the
details
to
describe.
What's
the
framework
look
like-
and
this
is
now
I
standalone
framework
draft
and
we
updated
the
earlier
this
month-
201.
D
We
thanks
to
all
the
reviewers,
and
we
have
addressed
the
most
of
the
comments
and
we
added
a
figure
about
the
relationship
among
the
service
policy
and
resources
and
the
we
recently
just
updated
in
202.
But
it's
not
submitted
right
and
now
I
distributed
to
the
all
the
reviewers
to
let
them
know
whether
they're
happy
with
the
changes
we
because
we
address
the
most
of
the
most
of
the
comments.
D
D
So
that's
the
procedure,
and
then
we
have
a
traditionally
way
to
describe
the
I
mean
the
framework.
It
looks
like
how
do
you
I
mean,
inter
crack?
Interconnected
I
mean
interact
with
other
blocks,
so
here
we
have
the
gpim
on
the
top,
and
if
you,
by
the
way
d
here
means
are
derived
from
so,
which
means
that
we
are
we,
the
generic
policy
data
model
can
be
derived
from
the
GPR
em
as
well
as
I
mean
the
ECE
policy
view.
Information
model
also
can
be
derived
by
this
G
time.
D
Then
we're
using
this
tool
to
I
mean
guide
lee
on
the
design
of
the
easy
policy
route
data
model
which
can
be
finally
used.
I
mean
I,
mean
communicated
to
the
network
network
management
or
the
controller
in
other
way,
and
there
we
have
the
resource
or
the
service
models,
and
just
like
I
said
in
last,
I
mean
in
previous
slides.
Then
this
can
be
I
mean
we
can
have
the
on
configurations
eventually
to
the
network
element
to
the
network
and
line.
D
This
figure
actually
was
added,
because
on
things
we
I
mean
proposing
supa
in
I
mean
a
long
time.
People
keep
asking
what's
the
relationship
between
surveys
and
the
policy.
So
actually
we
have
a
wiki,
which
is
a
generated.
I
mean
we
maintained
by
me,
and
there
are
many
q
and
A's
I
guess.
Maybe
this
one
can
be
also
added
into
the
wiki,
so
I,
just
added
this
figure
and
some
materials
into
our
noon.
I
mean
draft
to
describe
the
relationship,
I
mean
yeah,
I
review.
D
What's
the
relationship
between
policy
and
surveys
between
policy
and
resource?
Of
course,
the
service
and
resource
readership
is
out
of
our
scope,
but
I
just
draw
this
line
to
make
everybody
have
a
big
picture
so
here
on
thanks
to
drones,
help
make
the
I
mean
language
more
clear
and,
like
a
poem,
very
beautiful,
so
here
we
have
the
policy
manages
and
the
Canada
justice
service
behavior
as
necessary.
A
please
note
that
here
we
have
a
kind
of
relationship
that
this
policy
and
service
can
have
a
one-to-one
or
12.
D
Multiple
on
relationship
means
that
you
can
using
one
single
policy
to
manipulate
I
mean
to
manage
configure
I
mean
one
or
given
multiple
services,
and
similarly
we
have
policy
manages
and
can
adjust
the
service,
behavior
I'm.
Sorry,
there
must
be
something
wrong
here
and
just
the
resource
behavior
as
necessary.
So
there
is
a
mistake
here:
I'm,
sorry,
so
the
similarly
we
have
a
12
multi
or
one-to-one
relationship
between
policy
and
resource.
D
So
the
last
sentence
is
about
service
and
resource,
so
I,
not
gonna,
read
it
because
it's
out
scope-
and
the
next
slide
shows
you
the
comments
and
next
step.
So
thanks
for
all
the
reviewers
are
we
have
received
many
comments
on
the
mailing
list
or
I
mean
offline
or
face-to-face
discussions.
I
briefly,
I
mean
categories
based
on
comments
into
this.
51
I
mean
this
fight,
so
the
first
thing
is
that
what's
the
relationship
between
I
mean
just
like
what
I
explained.
D
Actually
already
done
this
and
you
can
see
from
these
slides,
the
figures
are
already
polished
and
you
can
also
see
those
in
our
new
draft
and
the
last
one
is
the
only
comments
that
I
haven't
decided.
How
to
do
it
and
I
want
to
ask
the
audience
here.
Is
that
whether
we
should
on
me
talk
about
the
I
mean
how
the
declaratory
policy
to
fit
in,
because
this
is
now
out
of
scope
and
actually
I
receive
these
comments
from
Burt
and
also
from
crush
from
juniper.
D
Yesterday
we
have
a
very
long
discussion
about
this
topic.
I
guess
little.
You
can
explain
so
I'm.
Also
I
really
wants
to
listen
to
cheers
the
ad
and
all
the
audience,
so
whether
we
should,
for
example,
we
should
just
to
keep
silent
on
this
topic,
or
we
should
write
a
small
sentence
or
paragraph
about
this
is
not
in
our
scope,
but
if
there
is
something
to
be
discussed,
how
do
we
do
this?
So
we
are
open
to
your
opinions
and
the
next
step
will
be
oh
I
already
updated.
The
draft
and
I
can
submit
it.
D
I
We
understand
that,
but
that
work
may
actually
benefit
the
working
group
by
the
time
that
they
get
rich
other
than
maybe
do
this
work.
So
it
would
be
good
if
we
can
see
how,
where
you
think
that
those
things
fit
in
the
framework,
so
that,
if
we
do
any
of
that
work,
you
know
we
are
not
doing
something
completely
different
from
what
was
in
the
overall
concept
of
the
policy
at
the
super
working
group.
That
would
be
good
to
have
that's
why
I
made
that
comma.
K
D
C
Yes,
ok!
So
there's
about
10
people
there,
which
is
good
and
next
I,
guess
all
those
people
how
many
would
support
it?
Being
a
working
group
item?
Ok,
that's
about
the
same
group!
Yes,
so
we
will
put
up
as
a
working
group
item
and
run
that
on
the
mailing
list
for
another
couple
of
weeks
before
formally
adopting
it.
The
next
question
is
of
the:
why
not
for
everybody
in
the
room,
how
many
people
are
prepared
to
review
the
document.
C
If
you
all
right,
ok,
so
that's
fun
for
the
document.
Now
the
the
question
of
about
declarative
policy,
the
the
Charter
does
say
that's
out
of
scope,
but
will
has
raised
the
question
of
throwing
in
a
few
paragraphs.
I
think
that's
how
he
put
it
just
to
make
it
a
bit
more
complete
Ben.
Why
could
we
have
an
area
director
comment
on
that?
Please.
G
Binocular
speaking
so
you're
right,
a
charter
says
out
of
scope.
Now
it
depends
how
much
time
and
how
much
a
40
want
to
bring
two
dads.
You
know,
as
you
mentioned
it,
if
this
is
a
couple
of
paragraph
telling,
if
there
is
ever
in
10,
this
is
how
it
works.
This
is
perfectly
fine
right.
If
we're
spending
more
time
on
the
intent
of
document
versus
the
other
one,
then
we
have
a
problem
right.
I
If
I
may
be
a
trainer,
so
a
short
section,
and
it's
okay,
if
you
even
state
explicitly
in
this
document
that
it
has
only
put
here
to
see
where
it
fits
in
the
framework
but
that
we
don't
work
on
it,
I
think
one
box
in
the
in
the
in
the
picture.
That's
in
the
document
would
be
good
also
to
see
where
one
or
two
boxes
in
that
picture,
where
it
fits
in
the
picture
as
well
right,
I'm.
I
C
I'll
just
remind
everybody,
seeing
I
have
the
mic
at
the
moment
that
what
we're
looking
for
mm-hmm
isn't
in
any
other
working
group
is
people
who
have
prepared
not
just
to
say
no.
We
don't
think
this
is
too
good.
All
this
is
much
too
long.
We're
looking
for
people
who
have
will
send
in
text
to
the
editors
so
that
it
can
be
improved.
L
Thank
you
very
much
level,
and
so
what
I
would
like
to
present
now
is
the
problem
that
the
super
working
group
is
working
on.
Actually,
this
problem
statement
has
been
used
in
many
drafts
previously,
so
we
are
also
use
the
parts
of
this
ideas
to
actually
initiate
the
working
group,
but
due
to
the
fact
that
we
have
received
comments
from
from
many
participants
to
actually
make
this
draft
supporting
the
draft
to
show
to
the
audience
what
exactly
super
is
doing
and
what
exactly?
L
What
is
the
problem
does
so
by
solving
that's
why
we
thought
that
it
will
be
good
to
to
also
try
to
make
this
draft
as
a
working
draft.
So
the
authors
have
contributed
to
this.
Internet-Draft
can
be,
can
be
seen
here
on
this
slide,
so
let's
go
to
the
demotivation,
so
the
growth
of
the
variety
and
significance
of
traffic
that
actually
is
forwarded
them
needs
to
be
supported
by
different,
complex
enterprise
and
and
network
operator.
L
Architectures
is
actually
imposing
very
much
complexity
and
the
operational
management
tasks
that
have
to
be
done
in
order
to
maintain
this
kind
of
networks
and,
at
the
same
time,
makes
the
actually
the
initiation
and
deployment
of
new
services
also
quite
difficult,
so
super.
What
actually
super
tries
to
do
is
to
solve
this
type
of
challenges
and
it's
providing
specifying
and
policy
based
management
framework
that
actually
combines
two
main
concepts.
L
So,
let's
go
through
the
status
and
change
changes
from
the
00
version,
as
already
mentioned.
This
draft
actually
is
based
on
the
information
that
has
been
provided
in
previous
drafts.
So
it
replaces
that
is
to
internet-drafts
a
term.
You
can
see
there
and
it's
actually
incorporate
the
super
problem
statement.
It
provides
information
about
the
value
of
the
soup
approach
and
it
gives
also
give
description
and
examples
of
how
how
the
event
condition
action
can
be
applied
for
policy
management
and
then
the
changes
from
the
00
version,
so
this
is
actually
0.
L
So,
let's
go
to
some
details
on
the
on
the
problem,
so
current
service
and
network
operators
need
to
operate
and
the
support
operation
of
networks
that
are
becoming
increasingly
complex
and
they
are
increasing
their
size
and
they
are
using
actually
a
multiple
type
of
technologies,
multiple
paradigms
and
also
a
different
programmatic
control
tools
and
at
the
same
time
they
are
actually
deployed
by
multiple
vendors
and
the
operation
and
management.
Actually
search
networks
introduces
key
challenges
and
you
can
see
them
there
at
the
bottom.
So
actually
the
network
infrastructure
management
becomes
to
be
more
complicated.
L
L
Then
the
second
one
is
the
unified
network
for
structure
policy
management.
So
by
by
doing
that,
we
provide
means
to
operators
to
have
an
unified
way
of
managing
methods
by
use
it
by
using
this
policy
framework
and
and
then
the
third
one
is
real,
and
this
is
an
important
one,
a
real
time,
an
event
based
network
management.
So,
actually,
the
the
network,
the
network
for
structure,
could
be
adopted.
It
could
be
changed
based
on
some
context
that
is
monitored
by
this
policy
at
the
current
moment
in
time.
L
And
then
here
we
have
some
in
the
draft
who
have
four
examples
that
show
how
the
event
condition
actual
policy
is
used.
I'll
go
only
through
the
first
one,
and
this
one
is
about
the
network
service
management
and
we
are
using
as
network
service,
in
this
case
the
LC
VPN,
and
what
you
can
see
there
is
that
the
event
is
shown.
L
It
happens
at
the
moment
that
alarms
and
Aaron
notifications
are
being
received
from
an
LC
VPN
service,
then,
as
condition
under
the
condition
that
this
error
notifications
are
coming
from
from
one
interface
within
a
period
of
time.
And
then
the
action
will
be
that
if,
if
the
error
they
are
rate-
and
that
actually
is
monitored-
exceeds
some
limit,
then
something
will
happen.
L
So
I'll
skip
this
other
three
and
I'm
going
to
the
next
steps.
So
we
receive
comments
balance
on
the
main
linux,
as
I
mentioned
previously.
So
we
receive
comments
on
the
mailing
list
that
having
this
problem
statement
Raftis
is
useful,
because
then
we
can
show
to
the
ordinate
audience
what
what
supports
actually
trying
to
do,
and
in
addition
to
that,
we
receive
comments
that
we
should
bring
back
the
the
gap,
analysis
and
the
related
work,
but
then
use
it
in
d
in
the
appendix
of
the
draft.
L
D
Bill
from
Holly
this
work
actually
on
that
piece
of
comments
is
out
from
me
and
I
do
think
that,
because,
when
we're
doing
this
work
there
long
I
mean
there
is
long
time
ago.
So
maybe
if
you
wanted
to
I
mean,
if
you
want
to
add
the
gap,
analysis
I
mean
in
a
summarized
diversion
and
you
need
to
look
at
look
at
it.
What
her
I
mean,
what
has
technology
is
nowadays
I
mean
not
only
two
to
two
years
ago,
because
those
parts
are
I
mean
he.
D
L
B
J
This
point
in
time,
especially
for
adopt
it
as
a
working
group
item,
is
over
Wisconsin
School
to
go
okay
because
it
was
a
very
useful
tool
while
where
things
are
both
and
trying
to
identify
what
are
the
problems,
the
problem
space
to
work
it,
but,
and
now
it's
it
also.
Is
you
Sadie
it's
a
it's
a
Oh.
J
A
Okay,
thank
you.
George
S
I'd
said
just
a
couple
of
observations.
The
first
is
I've
seen
some
comments
on
the
list
that
it
would
be
nice
to
have
a
problem
statement.
It's
still
a
little
unclear
to
me
is
to
kind
of
what
purpose
this
this
document
is
going
to
serve
because
we're
we're
working
on
the
solution.
Already
we've
got
data
models.
We've
got
the
information
model.
A
There
was
a
comment
that
the
Charter
maybe
wasn't
clear
or
come
to
enough
and-
and
this
document
certainly
provides
a
very
good
deep
sort
of
perspective
of
why
we're
here
and
why
super
was
instantiating,
it's
written
and
it's
available,
and
it's
enshrined
in
that
in
the
data
tracker
anyway.
Do
we
actually
need
to
continue
to
work
and
develop
this
document
and
actually
publish
you
know
as
a
formal,
your
RFC,
because
you
you
want
to
adopt
the
the
document.
So
that's
that's
question
that
I
would
have
and
I
think
we
need
to
ask
the
working
group.
M
J
M
Iratze
here,
people
reproduce
or
whatever
and
websites
vulnerable
to
that
extent,
I
would
recommend
adopting
it
but
asking
the
other
to
take
this
is
slow
down
and
if
some
cases
this
could
be
useful
as
an
introductory
material
for
something
some
other
documents.
That
would
be
my
recommendation.
Frank
Thank.
F
You
Diego,
this
is
joel,
Halpern
I
was
going
to
say
basically
the
same
thing
with
one
refinement.
One
of
the
advantages
of
adopting
it
is
that
we
then
make
sure
that
the
content
reflects
the
working
groups
preferences,
the
working
groups
understandings
right
now
it
is
the
author's
understandings
and
if
somebody
else
has
not
been
involved
here
comes
what
they're
seeing
is
the
authors
understand
if
we
adopt
it
and
we
put
in
a
little
bit
of
the
effort
needed
to
fix
it.
F
A
I'm
just
I'm
cognizant
that
we
have
a
limited
number
of
resources
and
people
participating
in
super
and
I
don't
want
to
dilute
the
effort
by
having
too
many
documents
that
are
working
sort
of
we're
working
on
concurrently.
There's
a
need
to
have
this
document.
That's
going
to
feed
into
some
of
the
you
know
the
milestones,
the
Charter
items
that
we
specifically
stated
when
we
created
the
working
group
I'm
interested
also
to
hit
been
one's
perspective
because
he
Trump's
please
confirm.
N
From
telling
telecom
I
think
this
document
will
provide
some
provide
some
guidance
on
about
how
to
use
soap,
adding
the
network
in
the
future
or
what
kind
of
scenario
would
can
use
case.
So
I
think
that
will
be
very
variable
to
before
I
would
for
our
network,
so
I
hope
that
it
can
be
adopting
the
future.
Okay.
O
That's
probably
true,
so
we
need
to
become
an
applicability
document
or
change
it
from
here's.
A
problem
statement
make
it
something
that
would
be
valuable
that
people
picking
this
up
would
then
understand
how
to
use
it
these
cases
whatever,
so
my
recommendation
would
be
the
change
in
that
life
may.
L
A
So
we
have
an
applica
bility
document.
We
have
a
problem
statement
document.
We
have
a
framework
document
yeah,
that's
that's
a
lot
of
documents.
I
mean
I'd,
be
much
more
comfortable.
If
we
were
to
look
at
you
know
where
we
can
actually
merge
this
effort
and
keep
keep
the
text
but
actually
have
you
know
a
document
to
documents
rather
than
you
know
three
documents
at
this
stage,
plus
the
information
model
plus
the
data
model,
but
as.
Q
Soon,
okiya,
my
statement
goes
actually
in
a
similar
direction.
The
document
title
says
problem
statement,
but
I
heard,
or
there
is
a
need
for
an
all
of
you.
There
is
a
need
to
explain
how
to
use
super.
Both
of
these
does
not
fit
actually.
On
the
problem
statement
in
problem
statement,
I
would
like
to
see
what
the
problem
is.
So
we
need
to
kind
of
decide
what
kind
of
documents
we
need
to
be
able
to
address
what
is
required
it.
There
seems
to
be
some
additional
information
required
which
goes
beyond
problem
statement.
G
But
not
less
so
the
last
three
person
have
been
stressing
the
need
on
stressing
the
need
to
document
how
we
apply
super
and,
in
my
son's
exactly
the
content
of
Napa
kept
these
statements,
which
is
the
Charter
which
says
you
take
one
or
two
use
cases,
and
then
you
explain
our
super
works
for
these
use
cases.
I
believe
that
we
are
passed
for
a
long
time,
lagda
Prem
statements.
There
is
a
working
group
because
there
is
a
problem.
We
know
about
that
right,
so
I
don't
see
the
value
of
actually
publishing
this.
G
A
R
It's
rajesh
kumar
from
juniper
network
and
I
just
want
to
give
background
I
just
started,
ending
up
IDF
and
as
juniper
we're
developing
security
controller
and
I
have
some
interest
in
the
ID
on
us
half
and
looked
at
the
talked
a
lot
of
customers.
So
one
of
the
challenge
which
we
have
seen,
that
is
the
security
policy
configuration
is
a
very
complex
tasks
and
if
you
have
a
multi-vendor
solution
and
virtualized
non-virtual
I
legacy
is
rach
router
firewall.
This
is
a
very
complicated
topic.
R
So
how
do
we
really
make
the
so
that
the
customers
can
really
use
the
system,
whether
we
call
the
controller
management
system
that
does
math
to
be?
But
how
do
you
provide
interfaces
to
the
northbound
side
or
to
the
OSS
BSS
application
or
whatever
you
want
to
call
that
and
make
those
interfaces
so
that
it
does
not
matter
how
the
network
is
bill,
what
the
topology
is
and
which,
where
they
special
function,
physical
function
or
whether
the
function
would
we
realized
that
switches
routers
stuff
like
that?
So
that
is
the
background
to
that.
R
In
our
opinion,
what
we're
trying
to
do
is
there
is
security
controller
which
really
trying
to
abstract
all
that
details,
whether
it's
a
physical
virtual
or
whether
it's
a
which
event
of
the
devices
security
controller
is
going
to
manage
all
the
thing
going
south
one
side.
So
we
are
calling
din
I
to
NSF
NSF
facing
interface
right,
so
NSF
face
interface,
understand
that
that
a
particular
capability
exists
in
a
network
security
function
and
there
could
be
another
layer
of
abstraction
which
would
happen
where
this
NSF
interface
are
generic.
R
Quite
a
lot
of
understanding
of
networking
device
how
the
topology
is
so
the
main
idea
is
how
to
use
work
which
is
done
in
the
sofa
and
to
make
end
customer
or
the
user
like
fixing.
That's
the
whole
idea
behind
this.
So
there
is
a
what
we
are
saying
is
in
the
eye
to
SF
the
client
interface
I
just
explained,
that
is
security
control,
inspector,
the
client
and
what
our
idea
is.
We
don't
really
care
like
like
I
know,
people
have
talked
about
I
just
wanted
to
say
one
line
about
this
user
intent.
R
What
we're
calling
that
I
know!
This
word
has
a
lot
of
different
meaning
to
different
folks.
What
we
mean
by
user
intent,
and
that's
why
I
was
talking
to
bill
earlier.
Is
we
don't
have
to
boil
the
ocean?
What
we
have
to
do
is
we
can
solve
a
simple
problem.
Just
like
and
customer
want
to
program
a
policy
based
on
the
user
group
access,
let's
say
in
any
enterprise
and
they
have
different
Department.
R
You
could
have
legal
department,
you
have
finance
department
and
you
want
to
say
that
users
which
belong
to
finance
department
or
HR
department.
They
cannot
have
application
access
or
the
data
access
in
a
different
department.
I
mean
this
is
a
very
typical
security
policy
of
dribble.
It
applies
that
so
to
us
that
is
in
10.
Do
you
want
to
program
a
security
policy
based
on
figuring
out
hey?
What
is
the
user
IP
address
is
given
instance
of
time
or
where
the
application
is
deployed.
R
What
is
IP
address
the
given
time
and
if
the
application
change
or
the
application
move
is
IP
address,
say
to
the
user?
Can
somebody
has
subtracted
and
reconfigure
the
policy,
so
the
bottom
line
is
what
user
want,
not
what
the
device
capabilities
from
the
CLI
perspective
from
the
five
tuple?
Sixth
of
all
user,
sadies,
hey
I,
want
have
HR
group
I,
don't
know
give
access
to
this
application
group,
so
it
doesn't
mean
that
we
have
to
provide
this
natural
language
processing.
What
we're
saying
is
how
to
model
the
intent
into
the
client
interfaces.
R
So
when
we
talk
about
intent,
that's
what
I
mean
here.
So
the
next
thing
is
like
I,
think
in
the
problem
statements
you
present,
if
that
that
it
should
be
network
topology
unaware
when
clients
say
that
it
does
not
care
whether
that
NSF
is
where
it
is
located
is
how
it
is
broke
and
we
wanted
leverage
super
policy
interface
there.
R
So
these
are
other
user
intent,
modeling
and
the
idea
was
here
is
these
are
the
intent
which
we
think
would
useful
to
create
for
the
northbound
or
the
client
facing
interfaces,
and
if
I
can
use
super
based
policy
to
model
this
thing,
that
would
be
great.
So
some
of
these
thing
is
Mara
data-driven.
So,
as
I
said
earlier,
user
intent
could
remodel
just
hey
Mara
data-driven
needs
to
prime
the
fixed
IP
address,
so
manner
data
could
be
related
to
user's
device
application
locations
and
the
group
definition
could
come
from
anywhere,
sao
paulo.
R
R
I
want
to
use
those
even
to
drive
my
policy
enforcement,
and
the
next
thing
is
what
what
user
want
in
rules
like
I
said
earlier,
he's
going
to
build,
ruled
on
the
building
blocks
of
the
object
which
we
are
going
to
define
like
you
have
like
I
said
there
you
have
groups,
groups
are
the
basically
where
the
policy
will
reapply
it.
What
kind
of
policy
won't
apply?
You
want
to
do
threat
management.
You
want
to
block
botnet
access,
d-does,
Hanley,
marriage.
We
just
give
an
example.
R
What
can
action
user
want
to
take
that
permit
denying
me
drinkers
profile
again,
we
are
not
trying
to
go
through
exhaustively
I'm,
just
giving
how
we
want
to
model
that
interface
and
if
we
can
leverage
super,
that's
the
whole
like
event.
This
and,
of
course,
user
could
say
that
hey
when
I
want
to
talk
to
my
security
controller
I
want
you
to
have
this
content
occasion,
authorization
and
their
operation
requirement
multi-tenancy,
telemetry
notification.
R
So
basically
we
are
trying
to
capture
this
client
interface
requirement
and
how
to
leverage,
if,
if
it
is
possible
to
leverage
soup
us
work
so
I
read
to
us
the
prop.
You
said
that
in
the
draft
the
two
policies
specified
management
policy.
My
understanding
is
and
then
barrick
policy.
The
decision
we
have
their
new,
so
the
very
interpreted
is
managing
policy
is
exactly
what
I
thought.
What
I
want,
where
management
policies
totally
obstructing
is
not
it's
not
a
device-specific
and
that
it
policy
is
more
device
specific.
So
this
is
all
I
have
to
say.
D
Go
back
to
the
architecture
page.
Actually,
a
little
update
is
that
we
had
a
long
discussion
about
this
thicker
and
I.
As
the
author
of
the
framework,
I
cannot
add
at
a
moment,
I
cannot
add
those
the
interface
about
the
user
intent
stuff
into
our
framework.
So
but
beside
that,
those
part
I
mean
except
those
part.
The
other
part
you're,
welcome
to
I,
mean
comments
and
review
our
come
draft
and
and
give
your
comments
class.
Yes,.
