2 Aug 2016
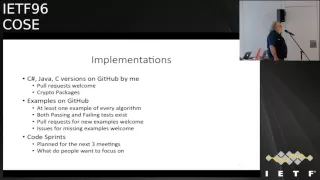
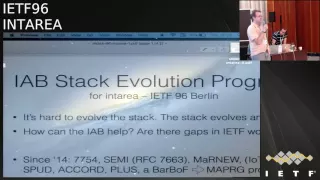
IETF Chair Jari Arkko and Dan York of the Internet Society cover some of the highlights from IETF 96 such as improved security protocols and new approaches to sending Web content over the Internet. They also discuss work underway to develop running code at the IETF Hackathon in Berlin.
- 2 participants
- 4 minutes

21 Jul 2016
Thursday, 21 July 2016, 13:00-13:45, Potsdam I
Description: The threats to our networks and ecosystems are continuously increasing in capability and frequency. Subjectivity in standards and protocol implementation are common attack methods and often quite difficult to prevent or detect. What can we do to both reduce these types of attacks yet build in future proof protections?
Standards based upon “assumed trust” will need to transition to a model of “assumed harm”. How can we establish such a paradigm shift yet maintain performance, flexibly and interoperability?
Speaker: Kevin D. Walker
Biography: Kevin D. Walker is the Security Chief Technology and Strategy Officer for Juniper’s Development and Innovation (JDI) organization. He is responsible for driving the security strategy. He provides the guidance required for JDI to conceive, develop and create momentum for industry-leading security solutions. Working closely with the Security Engineering team, Walker identifies the opportunities for improved security, growth, and innovation to deliver the scalable, reliable, and compliant security architecture needed in today’s security landscape.
Before joining Juniper, Walker was VP and Assistant Chief Information Security Officer (CISO) at Walmart.com. He has served as a Chief Information Security Officer (CISO), Chief Security Strategist and Director of Information Security across a number of notable companies including Intuit, Cisco, Symantec and VERITAS Software. With over twenty-five years in various computer science and information technology disciplines, focusing on enterprise applications, network design, and information security, Walker possesses research and engineering expertise across of range of technologies including networking protocols, securing applications at the atomic level, cryptography, and speech biometrics.
Description: The threats to our networks and ecosystems are continuously increasing in capability and frequency. Subjectivity in standards and protocol implementation are common attack methods and often quite difficult to prevent or detect. What can we do to both reduce these types of attacks yet build in future proof protections?
Standards based upon “assumed trust” will need to transition to a model of “assumed harm”. How can we establish such a paradigm shift yet maintain performance, flexibly and interoperability?
Speaker: Kevin D. Walker
Biography: Kevin D. Walker is the Security Chief Technology and Strategy Officer for Juniper’s Development and Innovation (JDI) organization. He is responsible for driving the security strategy. He provides the guidance required for JDI to conceive, develop and create momentum for industry-leading security solutions. Working closely with the Security Engineering team, Walker identifies the opportunities for improved security, growth, and innovation to deliver the scalable, reliable, and compliant security architecture needed in today’s security landscape.
Before joining Juniper, Walker was VP and Assistant Chief Information Security Officer (CISO) at Walmart.com. He has served as a Chief Information Security Officer (CISO), Chief Security Strategist and Director of Information Security across a number of notable companies including Intuit, Cisco, Symantec and VERITAS Software. With over twenty-five years in various computer science and information technology disciplines, focusing on enterprise applications, network design, and information security, Walker possesses research and engineering expertise across of range of technologies including networking protocols, securing applications at the atomic level, cryptography, and speech biometrics.
- 7 participants
- 1:06 hours